Add Electronic signature Form iPad
Make the most out of your eSignature workflows with airSlate SignNow
Extensive suite of eSignature tools
Robust integration and API capabilities
Advanced security and compliance
Various collaboration tools
Enjoyable and stress-free signing experience
Extensive support
Send Sign PDF iOS
Keep your eSignature workflows on track
Our user reviews speak for themselves






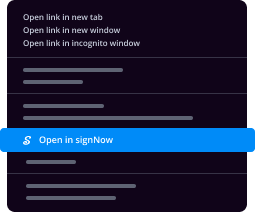
Add Electronic signature Form iPad. Check out by far the most user-helpful knowledge of airSlate SignNow. Handle your entire record handling and discussing program electronically. Range from hand-held, paper-centered and erroneous workflows to programmed, electronic and flawless. You can actually make, supply and signal any files on any device anyplace. Be sure that your important organization cases don't fall overboard.
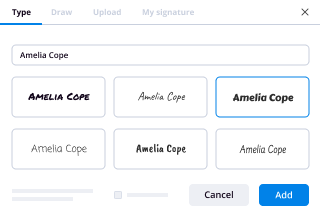
Find out how to Add Electronic signature Form iPad. Stick to the simple manual to get started:
- Build your airSlate SignNow bank account in mouse clicks or log in together with your Facebook or Google profile.
- Take pleasure in the 30-day time free trial offer or pick a costs strategy that's perfect for you.
- Locate any authorized design, create on the web fillable forms and talk about them tightly.
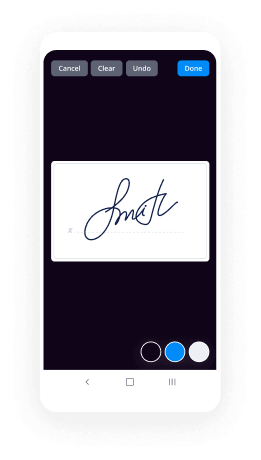
- Use innovative capabilities to Add Electronic signature Form iPad.
- Sign, personalize putting your signature on order and collect in-individual signatures ten times speedier.
- Establish automatic alerts and obtain notices at every step.
Moving your duties into airSlate SignNow is straightforward. What follows is a simple method to Add Electronic signature Form iPad, together with recommendations to help keep your colleagues and lovers for far better collaboration. Encourage your staff with all the best resources to be in addition to enterprise operations. Improve productiveness and range your company speedier.
How it works
Rate your experience
-
Best ROI. Our customers achieve an average 7x ROI within the first six months.
-
Scales with your use cases. From SMBs to mid-market, airSlate SignNow delivers results for businesses of all sizes.
-
Intuitive UI and API. Sign and send documents from your apps in minutes.
A smarter way to work: —how to industry sign banking integrate
FAQs
-
What are the pricing plans for electronic signature applications like Echosign? What alternatives are most suitable for a small
Echosign starts out great, with free, or $15/month for a Pro account. But every time I consider upgrading, I back out because the pricing gets steeply higher per user. To just add a second user means going from paying $15/month for one user to paying $480/year in advance (non-refundable, $20/month per user) or $60/month ($30/user). It is crazy, I actually end up paying 4 times as much just to add a second user, even though there is just a marginal benefit.Echosign definitely must feel there is a network effect to having more users, and greedily tries to capture all of that benefit for themselves. Pricing per user actually increases as you move to larger plans. Per user rates go from $15/month, to $30/month, to $40/month, to $50/month.. -----Delving into this a bit more, it seems like signNow is much like Echosign, but has a better pricing plan for two or more users. It is $25/user for the first two users, and declines to $10/user for 5 users. For 6 users, however, it jumps to $42/user, eventually declining again to $10/user, but adding API access. The plans provide a 20% discount for paying a year in advance.Their technology does not seem to be in any way less advanced than the alternatives. I sent a document with the service, and it seemed to well. Some nice features included recognizing data fields in existing pdf documents, integration with Highrise, Dropbox, and some other services. I didn't notice anything missing compared to echosign.----signNow does not offer a month-to-month option. Users must pay $180/year ($15/month) for the standard service (even though it says $19.99/month on the website)..
-
What is the best alternative to SignNow?
In a world of mobile app and the internet, why are you still collecting signatures on paper? Chasing people for signatures is slow and paper can get lost. SignNow lets you collect signatures and forms quickly and easily from any device. Use of esign app for electronic signatures is 100% safe and legal.There are 2 best alternatives to SignNow -eSignly - eSignly is an electronic signature solution that makes signing simple and fast. You only need to follow 3 steps and you are done -Choose DocumentAdd the name of all the people involved.Drag your signature and drop it where you need and click send.Features provided by eSingly are -In-person signing - Use an electronic signature app on your iPad to take the signatures.Security - All the electronic documents are protected by SSL encryption.Status Notifications - are sent when the document is reviewed.Audit Trail - Record of each party like name, address, IP address is maintained according to the date and time of the activity occurred.Instant verification is done by eSingly to validate the document.It supports all the devices such as Android, MAC, Windows, Linux, Mobile app, windows phone, etc.It works with applications like Dropbox, OneDrive, EverNote, Google Drive, etc.signNow - signNow Basic is the e-signature solution that allows you to easily sign a full range of documents and forms online without installation of any software. it also provides the digital signature app.Key Features of signNow are -It is secure and completely reliable.It offers 24/7 document control.To brand your user’s experience you can add your logo and color palette.Offers services to small, medium and large size enterprises.It also provides the mobile Signature feature.
-
Why are Apple devices so expensive? Are they worth it?
I am typing this answer from a Mid-2012 15″ Retina Display Macbook pro. This laptop since the time it was bought has seldom seen a day it was not switched on and used for 10 hours or more.Never has it felt slow or sluggish or needed an OS reinstall. It has received a major software update every single year that has made the laptop progressively better. When needed, I am able to use Parallels to boot into windows and have it work as well as it does on a Windows laptop. Same holds for Linux too. It has survived more than a few falls and a fair share of abuse.Apple for its part has,Replaced the entire screen when I had a single dead pixelReplaced the entire top case, when I felt the shift key was slightly looseReplaced the entire screen again when there was a recall for potential issue with the anti reflective coatingReplaced the GPU, 4 years after purchase, based on a recallThe only work I paid for was a battery replacement last month after thousands of battery cycles. This constituted replacing the entire top case again, along with a new keyboard and trackpad for a very reasonable $200.While they were at replacing the battery, because the technician felt the ports did not align perfectly (Probably due to a fall that I caused earlier in its life) and he also replaced the entire logic board on the 6 year old laptop, essentially transforming it into a nearly new laptop again.The 6+ year old laptop now functions like new, has a battery backup of 7+ hours and just had the latest Mojave beta installed on it.In contrast to this, a Lenovo - Windows signature laptop that I purchased from a Windows store around the same time, was screwed up when updating form windows 7 to 8. The issue was because of a driver file that was supposed to manage a hybrid HDD and SSD. The store could not help me or replace the computer. I eventually had to spend several weekends fixing it myself. The laptop lasted another year and half before it completely died.To avoid this being brushed aside as a one off case of good fortune with my Macbook pro, let me also add that my business has about 40 computers, with a fair share of both Mac and Windows computers. We have everything ranging from Mac mini’s, iMacs, Macbook Air’s and Macbook Pro’s. They date all the way back to 2012 and the only issue they have ever faced is needing to replace a faulty hard drive in one of the iMacs. On the contrary, the windows laptops and desktops we have used haven’t fared so well and have an average replacement time of 2.5 years.I have also owned 16+ phones over the past 7 years and that includes every generation of iPhone starting from the iPhone 3gs, to the iPhone X that I use now. I have also tried a variety of android phones; usually at least one from each generation and other phones like a windows phone and a blackberry. I have an old iPhone 5 and 5S still lying around, that work pretty well. In fact the 5S is getting the iOS 12 update, almost 5 years after its release. Anytime I have had an issue with an iPhone, it simply involves walking into the apple store and walking out with a replacement device. I cant recall even a single instance where I had to leave the phone and come back later. My Samsung and Sony phones on the other hand have had me ship the phone out for repairs and have made me wait a minimum of 2 weeks to get it back.I also own an iPad (Apple even replaced one of the iPads that I dropped and broke within about a month of purchase, with a new one, simply because they could), Apple watch and airpods. My iPad air has been working flawlessly now for about 4 years and my watch for 3 years or so. The airpods have survived multiple drops and even a short washing cycle.I can’t think of any other brand that has given me the consistent reliability that apple has demonstrated with it’s products, almost across its entire product line. I have also not seen any other brand even come close to offering the quality of service that I have received from Apple over the years.In addition to this, almost every person I know in my personal or professional life, including my own parents have never turned back to an Andriod phone or a windows laptop after being introduced to an iPhone or a Mac. The most commonly cited reason for not turning back is ‘ease of use’. Personally, I am a tech enthusiast and love tinkering around with both hardware and software. I can find my way around most electronic devices very well and even with that background, I do find Apple products to be consistently better designed from a user experience perspective and will certainly prefer and pick an Apple device when I want something that simply works well. I imagine this difference in UX would be even more acute for a less tech savvy user.My experience with apple clearly suggests this; Sure, I may have paid more upfront for some of the Apple products that I have purchased over the years, compared to alternatives. But, when you consider the full cost of ownership, such comparisons become almost meaningless with Apple being the clear winner in terms of cost and most other factors you compare them on, such as performance, user experience or support.While there are several genuine criticisms that stand against Apple and its products, many that you hear on a daily basis such as Apple being expensive, come from people who have never owned or consistently used an Apple product. If you are trying to decide if an apple device is worth it, it would be far more prudent just to try one yourself or at least rely on the collective opinions of people who have used both Apple products and non Apple alternativesPS: Before being labelled an Apple fanboy, let me add that I was a windows only person for the first 21 years of my life. I am a software engineer and a tech enthusiast who loves good technology products irrespective of its brand. Despite what I have said about Apple above, I also own and use Windows laptops, desktops, tablets (Both Windows and other Os’s), Computers running Linux, Game Consoles, Electronics from other manufacturers such as Tv’s, Projectors, Monitors and so on. All devices have been paid for out of my own pocket and there is very little incentive for me to favor Apple, except based on my own purchase and ownership experiences.Edit: Adding a picture as I am seeing comments and messages questioning the authenticity of the answer. Hope this settles it.
-
How do I go about increasing an email marketing list from scratch?
Most businesses wish to increase the size and quality of their email list.You surely are part of this group and so are we.We have therefore decided to carry out research on the best ways to increase the size of an email list.Here is our compilation of the 30 best tricks.PS You probably already know, but do not forget to always ask for permission when you collect email addresses.Tricks to increase the size of your email list:Via your websiteVia your present email contactsOn social mediaWith the help of partners and advertisementOffline and physical storesOn your e-commerce web-siteYour website: The pillar of your email acquisition strategy1. Use a static subscription formThis tip is often used on blogs and at the footer of several web sites. It is a classic way to collect email addresses.A way to improve it is to present the form as the visitor scrolls down your page. In this way, the visitor always sees the subscription section. Two choices: read the content or subscribe! If he likes the content, he can easily subscribe.Kissmetrics seems to have understood the value of highlighting the subscription forms on their article pages and at the footer of all pages.2. Offer free downloadable content in exchange for an email addressNothing better than win-win proposition to acquire new emails.For many companies, quality content is a very valuable currency. In offering premium content in exchange for an email address, a quality list will be generated.For example, Kissmetrics acquires multiple email addresses thanks to their eBook named How to Create an A/B Testing Program That Gets Results which is offered for free.3. Capture email addresses on your home pageYour home page receives the majority of your visitors. This is the face of your business.Do not hesitate to use it by putting in place a subscription offer to a newsletter or a content download on the page. More traffic usually increases the chances of subscriptions.Here is how Cyberimpact does it.4. Organize a webinarWebinars are an excellent way to grow your email list and may even help to convert people who don’t know you.The reason for which they increase your list quickly is because the participants must register for the webinars with their email addresses.The webinars are perceived as having an excellent value, because they are quickly consumed and are usually very educational.If you decide to make webinars, do not forget to promote them. A webinar that is unknown to people, even if it is a good one, does not help much in acquiring emails.Pro tip: Save your webinar and use it later as a subscription offer to your contact list on social media or in your Digital ads.BDC offers several webinars in the section entrepreneur’s tool box which allows them to get the entrepreneur’s email address.Try it, you’ll see!5. Create a useful toolBe useful. Create a tool or an application for your industry.In exchange for its free use, require the email address of the user.Hubspot has had a phenomenal success with its tool Website Grader and it enabled the company to acquire thousands of email addresses.Same scenario for Vircom, a company in Montreal, which has decided to create a tool, Email Security Grader, which checks if your mail server is secure.All is left for you is to find a good tool idea and to create it!6. Use exit pop-upsIf someone has decided to leave your page, there is nothing you can do to bring him back…Not true!By using an exit pop-up it will permit you to get a last chance to convert your visitor into a subscriber.You can offer free contents or other things that might encourage a visitor to give you his email address.If you succeed, it means that you have won a new subscriber who would probably have left your site without ever returning.Social Media Examiner decided to offer their 2016 Social Media Marketing Industry Report7. Set up a gateway or a “welcome mat”A gateway commonly called a “welcome mat” is a trick that allows you to display a call to action in full-size as soon as the visitor gets on your site.You can therefore put forward your content offers or your subscription offers on the newsletter in a way that is clear and obvious.Here is an example of how Wishpond uses it on their website.The “welcome mat” is free tool from SumoMe8. Use pop-upsBe it pop-ups activated by scrolling a page, by the time spent on a page or other criteria, pop-ups are true values when it comes to acquiring new email addresses.iProspect used this strategy on their blog with great success.9. Include a subscription form at the footer of all your blog articlesThis trick is essential if you have a blog.Adding a subscription form or a download form at the footer of your articles will enable readers to easily subscribe especially if they enjoyed your article.A simple trick to put in place, but which works very wellHere is an example from Cyberimpact that demonstrates this technique.10. Hello Bar or smart barA “Hello Bar ” or “Smart Bar ”, depending on the tool used, allows you to display a subscription form at the top of your web site.This allows you to remind your visitors to subscribe to your list, to offer them free content or a newsletter in exchange for their email.It works very well since the form is always visible at the top of your web site and is not too intrusive.Use your existing emails to acquire new emails11. Use your email signatureWith how many people do you communicate by email each week?100? 200?All these people who receive your emails are people likely to be interested in being part of your email list. Facilitate the task by adding a link to a subscription page on your email signature.12. Encourage your current subscribers to recommend a friend.Give your subscribers the opportunity to send your newsletters or your content to their friends by submitting the email address of the latter in a form.When submitted, the content will be sent to their friends and at the same time, subscribe them to your list.Offer a reward for their referal and the effect will be more pronounced.The more your list will grow the more you will be referenced. A systematic growth without any efforts.Social Media13. Pin a tweet containing a call to actionOn Twitter, you have the possibility to pin a Tweet so that it remains static at the top of your page. This tweet will be the first to be seen once visitors go to your profile page.Pin a tweet to invite your supporters to join your email list.14. Facebook cover photoThe perfect location to promote the subscription to your email list!Replace the cover image you are using by a cover image containing a call to action and a link to your subscription page.The URL must be easy to write and retain, because your visitors will have to manually enter it on their browser since the link will not be clickable.15. “Subscribe” buttonFacebook allows you to add an action button on your company’s profile page.Use this opportunity to send your Facebook fans to the subscription page of your email list.It works for Neil Patel therefore could be an interesting option for your business.16. Publications encouraging registrationIt would be easy not to encourage our Facebook/Twitter fans to register to your list, thinking that those are already fans of our company.Instead of leaving them to admire your Facebook/Twitter page, you should encourage them to register in order to continue to promote your content and your brand on other platforms.You can promote downloadable contents using an email, a subscription… It is your choice.Pro tip: regularly publish your subscription offer on your Facebook /Twitter page. After all, not all your fans see all your publications. In publishing them often, you signNow more of them.17. Add a link to your subscription page on LinkedInUse the feature “Add Media” on the experience section of LinkedIn in order to add a link that leads to your subscription page or on your home page.Easy, fast and efficient.18. Use your contentYou remember the tip #3, #4 and #5? Use this same content but this time, promote it on your social platforms.Have you registered your webinar? Make it downloadable on your social platforms by publishing a link to a page that allows users to download your content in exchange for an email.You could do the same thing for an eBook or a free web tool.A content recycled = several new chances to get email addresses.19. Organize a contest on FacebookOrganizing a contest with a tool such as Woobox will allow you to quickly expand your scope.Offer a price which is relevant to your market and not a price which attracts everyone such as gift cards or an iPad. With the latter, you may attract people who are not qualified and this is not your goal.Contests are very popular on Facebook and are naturally very viral. By adding a field to capture emails in the contest participation form, you could acquire several new subscribers for your email list.Pro tip: Do not forget to ask for the consent when collecting email addresses via contests.asdfadsfadsfasdfsadfsdf20. Twitter lead generation cardsPromote subscription to your list by using Twitter Lead Generation Cards.These campaigns are designed to help you collect the email addresses of users who have expressed an interest for your offer, giving Twitter users the possibility to communicate you their email addresses in a way that is fast and secure.By configuring a lead generation card to be included in your tweet, you can easily get a greater number of subscribers on your list.Two clicks will suffice for a potential subscriber to share his coordinates with you.Plus, it is very simple to put in place.21. Facebook Lead AdsPromote the subscription to your email list by using Facebook Lead Ads.When someone clicks on your ad, a form opens and the information about his profile is automatically added to the fields of the form. Another click and the person is subscribed to your list.Quick and effective subscription in two clicks and without entry of data.Partnerships, exchanges and advertisements22. Publish your contentProduce quality content that you will be published on a newsletter or on other web sites that have a complementary market or customers similar to yours.Add in your signature and in the content of your article, a link which allows users to subscribe to your email list.Seems simple but it works!23. Exchange of listsFind a partner and share your lists. You promote the subscription offer or content of your partner to your list, your partner will do the same for you to his list.In this way you have instant access to a hearing relevant to your offerings.For this trick to work, you have to find a partner with customers similar to yours and who is not a competitor.The partner must do the sending to his list and not you doing the sending to his list. Respect the consent.24. Advertisement and bannersBuy or exchange advertisements on the web site or in the newsletter of a partner which has a complementary market or customers similar to yours.Offer your content and your subscriptions offers in the form of banners or in the form of content marketing in order to lead your partner’s visitors to your subscription page.25. Google AdWords and BingCreate an AdWords or Bing announcement which publicizes your content and which when clicked Redirects to a subscription page which contains a form to capture emails.If you choose your keywords well, this trick can be profitable in the medium term. However it can become quite expensive if you don’t manage your costs of acquisition.A very fast way to acquire email addresses.Off-line and physical stores26. Ask for the email addresses of your customersYou have physical locations?Establish a process by which you systematically ask for the email addresses of your customers. The simplest way is to do so is at the time of payment.BestBuy does this each time you make a transaction in their stores.Pro tip: To ensure that all email addresses that you will personally collect have indeed been made with the consent of the client, you could put in place a “double -opt-in” system. Following the collection of the email address, a subscription confirmation-mail is sent to the customer. The latter must click a link in the email in order to confirm his subscription to your list.27. Maximize your paper mills and your business cardsUse your paper mills and your business cards in order to generate new subscribers to your list. Add to them, a link that directs people to your Web site or a subscription page.Similar to the tip of the email signature, but it uses the good old paper!28. Give a conference at an event concerning your industry.In addition to the fact that you will be able to promote your business and your expertise, you could also encourage the people in the room to subscribe to your email list.In your presentation, add a link that leads to a subscription form which will be easy to remember. Also mention it during your presentation.This way people sitting in the audience will be able to subscribe easily.Email acqusition on ecommerce site29. Offer a discount in exchange for an email addressHere is how Electronic for less offers a discount on their web site in exchange for a subscription to their newsletterWho refuses 5% if you were going to buy anyways?Yes, they cut 5% of their margins on the first sale, but in exchange they get an email address with which they can continue the relationship.The key to success in e-commerce: communicate when it matters the most.On the long term, they will easily recover their 5% in additional sales.30. Add a field to capture email in your purchase processSimple, but very effective. You would be surprised at the number of business that dont have this in place.The more upstream you capture the email , the more you will have the chance to communicate with your customer if there is a glitch or a transaction abortion.In my opinion, if you operate a transactional site it is a mandatory tactic.Discount car and truck rentals understood it well.Email acquisition is definitely the key to a successful digital transformation.
-
Can you recommend some good online publications/magazines to keep up to date in technology, IT, software and hardware?
Here you can find a list of the tech news websites which might be helpful:Top 40 best technology news websites – the definitive listI would also add a few blogs to stay updated:10 Best Tech BlogsBesides, a few more resources:VentureBeatVentureBeat gives you the full scoop on news, events, groundbreaking research, and perspective on technology innovation. The site aims to provide deep context to help executives, entrepreneurs, and tech enthusiasts make smart decisions.The Next WebThe Next Web is your source for international technology news, business, and culture. With writers from all seven continents, you can rest assured that if there’s any tech news worth hearing about from the other side of the globe—you’ll hear it from them.The VergeFrom gadgets to startups, apps, and tech culture, The Verge has you covered with in-depth reporting, original features, and editorials.WIREDWIRED’s content shows how technology is changing every aspect of our lives—from culture to business, science to design. The breakthroughs and innovations uncovered by the site lead to new ways of thinking, new connections, and new industries.EngadgetEngadget covers everything new in gadgets and consumer electronics obsessively. Since 2004, the website’s extensively discussed cutting-edge devices and the technology that powers them.GizmodoWith “Everything is Technology” as its motto, Gizmodo features the hottest consumer electronics, gadgets, software, and much more. And it’s all provided with Gawker Media’s signature snark.ReadWriteReadWrite is a blog about the frontiers of technology, from robots, drones, and watches to the people who make and use them.Re/codeRe/code wants to reimagine tech journalism. It’s a tech news, reviews, and analysis site featuring content from the most informed and respected journalists in the field.to5Mac9to5Mac provides breaking coverage for the iPhone, iPad, and all things Mac. You’ll have the 411 on news and reviews for Apple products, apps, and rumors.CNETCNET tracks the latest consumer technology breakthroughs and shows you what’s new, why it matters, and how it can enrich your life.Forbes TechThe technology section of Forbes was created to cover breaking tech news as well as to identify the game changers in our digital world.Tech in AsiaThe startup ecosystem in Asia is rapidly booming, and Tech in Asia has the goal of telling the world the exciting advancements happening there.GigaomWith more than 6.5 million monthly unique visitors, Gigaom offers an intelligent, credible analysis of emerging technologies. The publication’s network of over 200 independent analysts provides new content that bridges the gap between breaking news and long-range research.Hacker NewsHacker News is run by Y Combinator—the seed accelerator that provides money, advice, and connections for new companies. YC has invested in companies like Dropbox, Airbnb, The Muse and Reddit, and its news site focuses on computer science and entrepreneurship.AVCAVC is a popular internet commentary by Fred Wilson, a New York-based venture capitalist and the co-founder of Union Square Ventures. Since September 2003, Wilson has published a post every day—usually on subjects like venture capital, entrepreneurship, or the internet.Andrew Chen’s EssaysAndrew Chen is a writer and entrepreneur focused on mobile products, metrics, and user growth. He advises and has invested in tech startups including Dropbox, Product Hunt, and AngelList. He writes long-form essays on what’s going on in Silicon Valley. Oh, and his blog is regularly read by people like investor Marc Andreessen and co-founder of PayPal, Max Levchin.AlleyWatchWith readers from more than 200 countries, AlleyWatch focuses on the New York technology, startup, and entrepreneurial ecosystem. The site is the destination for startup news, opinions and reviews, and investment and product information.Cdixon BlogCurrently a general partner at venture capital firm Andreessen Horowitz, Chris Dixon has personally invested in startups including Skype, Pinterest, Kickstarter, Foursquare, and Warby Parker. On his blog you’ll find posts on topics including but not limited to startups, venture capital, competition, virtual reality, and e-commerce.
-
What are the best property management systems?
There is no one property management system that is ideal for every use case. It depends on who you are and what you are looking for in the system.For residential property managers:If you are a professional property manager and have full service clients, then I have found the best softwares are Yardi and Appfolio. Yardi is a bit more of a “legacy” system — robust but not as fresh as Appfolio, promoting a great UI/UX (user interface and user experience). If you are a property manager and do not use software, then IMO - you are failing at your business. Software will reduce your overhead costs and help mitigate risks of forgetting lease renewals, late fees, etc.. The cost and time related to the setup can be gruesome, but it is well worth it in the end. You’ll be able to take on more clients and provide them with a much better experience.For residential property owners:The majority of owners across the US (80%) self manage their properties. Most of them do not use software, because it is a relatively new concept for them. From a systems perspective, it will depend on what you are looking to accomplish with your real estate goals.Here is an article that all owners should read to understand what kind of management system they want (passive or involved) and what type of solutions cater to their needs.
-
What are the best ways to manage your visitors?
Visitor Management Techniques and StepsEvery business and organization has visitors. Some just get a few package and food deliveries. Others have customers, vendors and interview candidates streaming in and out all day. How offices manage visitors can be as varied as the organizations themselves. For some, the process of visitor check-in is regimented and formal. For others, handling guests is a fly-by-the-seat-of-the-pants affair.Regardless of the visitor management system, there are certain aspects to the process of handling guests that are common across the board. Most are done so quickly that sometimes very little thought goes into the process at all. Each step, however, is important to the functioning of your organization, the safety of your employees and data, the comfort of the guest and -- most importantly -- the overall efficiency of time spent.In this six-part article about the visitor management process, we’ll break down each step of the process, explain why it is important, and give examples of different methods for effectively accomplishing the end goal - great first impressions, productivity and safety.Visitor Management Step 1: Recognizing Visitors and Making Them ComfortableHave you ever walked into a restaurant or other place of business, looked around and had no idea what you were supposed to do next? No one said hello. No sign directed you to “Order at the Window” or “Please seat yourself.” No directory on the wall pointed you to a visitor desk. Most guests in that situation will do one of three things: 1) they’ll wander around awkwardly and watch what other people do; 2) they’ll ask someone for help; or 3) they’ll turn around and leave.This is an obvious failure of the organization to accomplish the first technique of a strong visitor management process: recognizing that visitors will come to your organization and they will need tools to make the initial moments of that visit comfortable and pleasant. We all know it is easier to remember negative experiences. Visitors who feel confused, lost or unwelcome may never want to return, and even worse, may tell others about their treatment.People have an inherent need to be recognized. The first step of recognizing visitors can be easy as saying, “hello”, having a sign that reads “Welcome Visitors” or a welcome screen that informs visitors of their next step. Not every location needs to roll out the red carpet for visitors, but every location needs to acknowledge the visitors who do walk through the door.Every organization has different ways of recognizing guests, and they range from very hands-on and labor intensive, to reception automation. Some methods can be combined for maximum impact.Using People to Recognize GuestsHistorically, the most common method used by organizations to make guests feel recognized was to use people. There are really three types of personnel employed to greet visitors.Dedicated receptionist: The dedicated receptionist’s primary job is to welcome visitors and perhaps answer incoming phone calls. They often have minimal responsibilities outside of assisting guests. The greeter at Wal-Mart has minimal duties beyond saying hello and checking the occasional receipt. In some locations where security is a concern, the dedicated person might be a security guard or a door-person.Semi-dedicated receptionist: The difference between a dedicated and a semi-dedicated receptionist is one of responsibilities. A semi-dedicated receptionist is stationed near the door and expected to greet guests as part of the job description (or, maybe they forgot to mention that part), but also has other responsibilities. Most administrative assistants fall into this category. They are expected to greet walk-in guests, answer phones, and perform other tasks, like write letters, manage calendars, set up meetings, and sometimes accomplish large projects. It is surprisingly hard to resume these other responsibilities after interruptions.Informal/unrecognized receptionist: This is perhaps the least considered visitor welcome method, but is, unfortunately, a very common one. The unrecognized receptionist is often a junior employee with a functional role - human resources, accounting, office management - a person who has their own list of priorities. But in today’s modern office happens to sit in a desk by the door. Depending on the number of walk-ins every day, unrecognized receptionists find themselves interrupting important tasks to help guests find their way. Whether they tell you or not, the unrecognized receptionist HATES IT. They resent the guests and the interruptions and prefer to just get their own work done.Using people to greet guests has the advantage of bringing a personal touch to the welcome process. A warm smile, and a “how may I help you?” can provide the start to a truly positive experience.On the other hand, using people is expensive. You have the direct cost of a dedicated receptionist who is paid primarily to greet guests. Or, if you prefer, you have the high cost of productivity lost for semi-dedicated and informal receptionists. And in the case where you have a less-than-effective receptionist – one who greets people gruffly because they are tired of being interrupted – the cost could be greater in terms of negative attitudes toward your organization.Un-staffed Ways to Recognize VisitorsVisitors don’t always want or need to talk to a person to feel welcome. Organizations can spare employee time and save money by making effective use of the following methods for greeting guests.Automated receptionists: More and more locations are taking advantage of automation in order to greet and assist guests. It is common to see airport check-in kiosks, visitor registration kiosks, informational kiosks in visitor centers and libraries, self-ordering stations at fast-food restaurants. Even just an automated announcement connected to your door - “Welcome, please turn right and proceed to the counter” - tells visitors they are expected and what they are supposed to do. Modern offices are rapidly adopting visitor check-in apps to create strong impressions and improve efficiency.Signage: Prominent signs bridge important gaps for visitors. Posted directories, plaques that identify visitor check-in locations or information desks, and directional signs all help visitors to feel comfortable.Automated receptionists and signage have the advantage of being relatively permanent, tireless, and available 24 hours a day. The cost is far less than paying a dedicated person. Also, as crazy as it sounds, people don’t always like talking to people. Being able to use a kiosk or signage is often preferable to having to ask someone for directions. Signs and kiosks may not be able to deliver the warmth of a smile, but they can direct visitors to the person most likely to give them that smile.Conclusion: The Best WayYou guessed it, there is no single "best way". Rather, the best option to greet guests varies by organization, but all of the most effective methods ensure that the guest is acknowledged, either by a sign or a smile. Visitors should feel welcome, and confident that they can accomplish what they came to do. Using forethought and planning, you can ensure your organization recognizes visitors as part of your visitor management process.Visitor Management Step 2: Identifying VisitorsWhen visitors arrive in your place of work, how do you find out who they are and what their business is? Identifying visitors is an important step in the visitor management process. Once you have this valuable piece of information you can create a great visitor experience. Not having it though could cause you to steer a guest the wrong direction, or allow someone onto the premise who should not be there.In Part One of this series, we described how important it is to simply greet guests and make them feel comfortable. Once this is accomplished, the next step in the process is to determine who they are, what type of guest they are, and how best to meet their needs.Visitors VaryOrganizations have varying levels for how they need or want to greet guests, and it often depends on the type of business that person has come to accomplish. You might be thinking, “My organization doesn’t have any visitors,” but you’d be wrong. Even the most insular of organizations will have people from outside show up from time to time. Consider the following types of visitors:Task-oriented visitors: These include postal workers and delivery personnel, maintenance workers, building and code inspectors. These are people who arrive with a set task that must be done at your location (e.g. dropping off a pizza, painting an office, checking the smoke detectors). They are often paid (or tipped) per task so they will leave quickly once it is complete.Important guests: Prospective and current clients or donors, prospective and current vendors, management visiting from the head office, contacts from a related firm, etc., are all important guests. Anyone who your organization wants to have an ongoing, positive relationship with needs to have special care taken to ensure they feel welcome and are treated accordingly.Casual visitors: These are visitors who don’t plan to stay long do business, but need to know how to get where they are going. Consider hospitals, who have people stop in to visit patients all the time. Colleges have family visiting students on campus. Friends and family of employees also fall into this category; the manager’s spouse might show up to take her out to lunch.Visitor-visitors: This might seem like a no-brainer, but places like museums, hotels, tourist attractions, restaurants, and retail are designed to draw people in and welcome those who may only ever be there once.Starting the ConversationOnce a visitor walks in the door, how do you find out what they need?If you are employing a full-time receptionist to greet people, the logical next step is to ask the person who they are, and what they are there to accomplish. With a person at the door, a simple, “How may I help you?” will start the conversation, though other questions may be needed. Depending upon the security needs of your organization, you might require a guest to show an I.D., fill out forms, create a and explain their business.What happens if the receptionist is busy on the phone when a guest arrives? Or if you don’t have a dedicated receptionist, and the person nearest the door is engaged in other tasks?People aren’t the only way to ask guests what they need. More and more offices are using iPad receptionists to allow visitors to check in themselves, whether they employ a receptionist or not. If the receptionist is tied up on the phone but can pause long enough to point a guest to an automated reception kiosk, the guest can continue the visitor registration process instead of waiting around. Guests of all kinds don’t like to wait and appreciate the ability to be proactive instead of inactive.A reception application might ask the following questions:Your NameThe name of the person you are meeting, if applicableThe purpose for your visitOnce the information is obtained, the receptionist or the kiosk can either direct the guest to the appropriate location, or contact the appropriate person to come meet the guest.Conclusion: This is Mission-Critical InformationUnless they are lost and only walked in to get directions to somewhere else, every visitor who enters your organization is there for a specific purpose. However the person is greeted, finding out the reason for their visit is mission-critical to successfully moving them along on their journey. Your method for identifying them, whether a person or a digital visitor management system, needs to have the necessary skills to politely and effectively gather this key information. Then, they must be intelligent enough to guide the visitor to their next step.Only after you have successfully identified the visitor and their purpose can both your visitor and your organization continue the tasks that keep you in business.Visitor Management Step 3: Signing InDoes your organization require visitors to sign in upon arrival? Every organization, and even individual offices within, has different guidelinessurrounding guests and whether or not signing guests in is part of their visitor management system.In Parts of this series detailing the visitor management process, we described different ways to greet and identify your guests. Once you’ve identified which type of person or group is standing in your lobby, it is time to determine how much of the check-in process they are required to complete.Whether or not you have visitors sign a paper or digital visitor logbook will depend largely on the rules or customs of your organization, but there are definite benefits to requiring visitors to check in.Security FirstIn today’s modern world, office security is a higher priority than ever before. Schools, government buildings, large firms and factories all have reasons for knowing who is inside their facilities. And while businesses might like to maintain an open-campus type policy when it comes to visitors, that also makes them less secure.Visitors are wild cards. Security best practices require visitors to sign in, which adds a first layer of protection from would-be criminals – people who would harm people or steal data – by causing them to have to think twice about leaving a trail of evidence.Many organizations require employees to wear or carry identification that doubles as electronic access keys for buildings. Visitors might also need visitor badges in order to access areas, or simply for identification.A good, secure sign-in process will require, at a minimum, the following information from guests:First and last nameBusiness or organization they represent (if applicable)Purpose for visitingName of the employee, host or contact person they are visitingTo go above and beyond, some organizations might also require:A visitor photograph taken on site.Signed, or electronically signed non-disclosure agreements or waiversMaking Visitors WelcomeIt might seem slightly counter-intuitive, but having visitors sign in can actually help them feel more welcome. While some visitors may be frustrated by having to jump through hoops, this technique is also a signal that your organization has taken visitors into consideration, and it gives guests the knowledge that they’ve come to the right place. When a guest signs in, they know you are aware of their presence and therefore they are less likely to be left wandering around.Also, if visitor badges are part of the sign-in process, you can train your employees to keep an eye out for those visitors who might need a little extra help. Guests often find themselves lost in an unfamiliar location, especially if your building has a lot of twists, turns and levels. Visitor badges give employees the immediate knowledge that the people wearing them are supposed to be in the building, but may not be familiar with the layout.Who signs in?Not every organization is super-sensitive to security, and maybe not every visitor who comes in will be required to sign in. When thinking about your organization and its security needs, you’ll want to think about what your goals are, and what happens in your visitor management process. In Step Six of this article , we will discuss the benefits of keeping a visitor registration log that includes all guests, but here are some possible questions to consider.Do delivery personnel need to sign in? Will they go beyond the lobby? If not, then signing in may not be necessary. Or, you may require less information for delivery people.How much access will the person have? Could they see or hear sensitive information or encounter semi-dangerous manufacturing equipment? If so, they might need to sign a non-disclosure agreement or a waiver. Such documents can be handled during the sign-in process with an e-signature app.Does your organization want or need to know who is in the building at all times? If yes, then having every person sign in is important. Some organization may not; perhaps you don’t need to know about the visit from an employee’s spouse or the pizza delivery person.Do you have a skilled dedicated receptionist to help visitors find their way? If the answer is no, then an electronic check-in kiosk has the benefit of both signing in visitors and helping to move them along in the process. Otherwise, they may very well be lost from the start.Conclusion – Efficient Sign-In for Happy GuestsWhatever process you choose for signing in guests, visitors will appreciate any steps you take to make the experience easy. Take the time to plan ahead to determine your security needs and how best to make guests feel welcome. An efficient visitor sign-in process shows your guests that they are not just an afterthought, but rather an integrated part of a well-functioning workplace.Visitor Management Step 4: Contacting the HostWhen any visitor arrives at your workplace, they are there to connect with a person. It might be their host for a meeting, one of the people who receives food or package deliveries or someone they need to consult with. Helping the guest and their host connect is a crucial step in any visitor management process. There is nothing worse than walking into a building and talking to ten different people before you find someone who can actually help you. So how can you make this step seamless?First, of course, you have to ensure you are first greeting guests, if necessary. Upon knowing their purpose, you can determine who they came to see; it may be a specific person, a group of people, a department or even security if they are not wanted at your site.What is a host employee’s job? And what are the mechanics of making sure the host knows their guest has arrived in a timely manner?The Responsibilities of a HostWhen we think of a host, we often think of those who hold a dinner party, house guests or even travelers in their home, like Airbnb. The fact is, whenever an employee has someone come to see them at work, that employee is serving as a host. For however long the visitor is at your organization, that employee is the face of your organization. It is their responsibility to leave a good impression.Here are some basic reception etiquette tasks a host can do prior to a guest’s arrival to make sure their visitor has a good experience:Provide crucial information to a visitor, like their name or their department.Communicate vital contact information, like telephone number, email and office number.Inform the guest of which entrance to use and any sign-in requirements your organization has.If possible, determine a meeting spot with the guest in advance and be there prior to the appointed meeting time.If appropriate, preregister the guest with either your human receptionist or visitor registrationThe Mechanics of Connecting Visitors to HostsHow you connect your visitors to your hosts will largely depend on how your reception area is staffed and what the practices of your organization are, but the mechanics are basic. One of the following things has to happen:Reception notifications via a phone call, text, email or instant message - or several of those - is sent to the host, who comes and meets the guest.The visitor is given directions for how to find the host, either by another person or a posted directory and finds the host themselves. This method can have several unfortunate consequences ranging from lost and frustrated guests to unwanted visitors unfettered access to your place of work.The visitor is escorted by another person to their host.Who Makes the Call and Why it’s ImportantWhile the mechanics are simple, there are multiple consequences that could interfere with how work gets done and the impression guests get from your organization. The pros and cons hinge on whose responsibility it is to contact the host:The Receptionist: If you have an obvious reception desk, then the receptionist handles making phone calls, answering questions, giving directions and escorting guests. While this has the benefit of being great customer service, it also requires a very knowledgeable and personable staff member – and it’s expensive. In a busy office, the receptionist might be overwhelmed by people who don’t follow rules or too many people at once. This could leave your desk without staff, and keep guests waiting. It also prevents the receptionist from accomplishing other work, if necessary.The unlucky person by the door: If you are in a modern office or coworking situation, you likely don’t have a designated receptionist. The unfortunate soul who sits near the door may find themselves constantly interrupted by deliveries, salespeople, prospective candidates and more. They then have to stop what they are doing to use a phone, shout across the room (we hope not!) or guide the guest to the person in question, wasting work productivity in the process.A Digital Receptionist: Having a digital visitor check-in kiosk with a visitor management system can be a simple solution for visitors. It can automatically inform the host of a guest’s arrival via the host’s preferred method. A digital system can be set to contact hosts using email, text, phone, Slack or all of the above. This is especially helpful in the case of unexpected guests, like the flower delivery person sent to bring a surprise bouquet. They simply enter the name of the recipient into the system, and the person is contacted – wherever they are – that they have a delivery. One drawback of a digital receptionist is that it can be quite easy for a visitor to walk right past a kioskPerhaps the most fail-safe method of ensuring that guests and hosts get connected is to have a combination of a visitor check-in app supported by live staff for extenuating circumstances.Conclusion – Get Them TogetherReal-time reception notifications connecting visitors with the appropriate host is vital to getting business done. You want your visitors to feel welcomed, and to leave with the impression that your office has its act together. Contacting their host quickly and efficiently allows everyone to get on with the important job of accomplishing the purpose of their visit.Visitor Management Step 5: Checking OutYour visitor has arrived, been greeted, signed in and has been connected with the appropriate host. When their business at your workplace is complete, what happens? Does your guest just walk out the door? Or is your visitor required to check out?Throughout this series, we’ve been exploring the various steps to a good visitor management system and explaining why some easily overlooked steps and processes can important. Perhaps the most overlooked step of visitor management is visitor checkout. Unless you run a medical office or are in the hotel business, most organizations don’t focus on guests checking out; guests just leave. However, there is one very compelling reason to have guests check out: security.Your Secure WorkplaceSecurity means protecting your people, physical assets and your data. When it comes to securing your workplace from the dangers of onsite visitors, you can’t know if a guest has left your premises unless the guest is required to check out. There are multiple security reasons for a visitor to actively check out of the location.Access: If a guest is given any sort of physical access capability (a key, key card or identification) it must be returned at the time of checkout. If the visitor gives it to the host and just leaves the site, then the host is responsible for returning it, and it is more likely to get lost. If the guest has been given electronic key card access, even if they don’t return the card or item, your system should register that they have left and deactivate access connected to the unreturned key card (like that pile of hotel keys you have).Accurate records: Knowing who was in your facility on which days at which times and for how long can be incredibly important if it is ever necessary to investigate a crime. (We’ll discuss in detail why it is important to keep these records in our final installment in this series.)Visual record: If all visitors are required to check out at the same location (a security best practice), it is easy to station a staff person or a security camera to watch for anything unusual. Strange behavior, unusual bulges in pockets and other visual cues can alert staff to theft or other crimes. If the use of a camera is engaged, it can also provide the physical appearance of a person for identification in connection with a crime – whether that person is a suspect or a victim – and can provide a record of their movements and what they were wearing.Visitor Safety: Imagine if a visitor completed their meeting, accidentally wandered into an unused area and either got locked in or had an accident of some sort. If the visitor isn’t required to check out, how would anyone know to look for them? At the end of the day or at shift changes, it is good practice to review a visitor log and see if anyone is still in the building or has stayed far longer than is normal. (A good host will also make sure to walk a visitor who is unfamiliar with the facility to the exit!)Methods for Checking OutHow your visitors check out will largely depend upon how they check in. If a guest is writing their name on a paper visitor logbook upon checking in, then they might be required to write the time at which they check out next to their initial signature. If you have a large volume of guests checking in and out, this may require flipping through a number of pages and isn’t very efficient. Not to mention that every guest can see everyone else that has visited.If you have a staffed reception desk, the receptionist or security guard may check the visitor out, taking any physical objects, like keys or key cards, at that time. The staff person might be required to update the paper or electronic log, or to ask the visitor to do so.Pointing visitors to an iPad receptionist for checkout is probably one of the most efficient ways to have them check out. This maintains easy-to-search electronic records of the visit. It also gives visitors some active role in the check-out process. It is a signal that their business is complete and they can transition to their next task accordingly.See Greetly LiveSummary – Checking Out Completes the CircleLast time you went to an amazing restaurant, did you save room for dessert? Never underestimate the value of a great last impression.Checking out of your facility is quite simply the final step a visitor ought to take before leaving your facility. With the stress of business complete, and all parties mentally recapping the visit or moving onto their next activities, it is easy to skip. Yet this important step in the visitor management process gives your organization a measure of security nearly impossible to achieve without it.Visitor Management Part 6: Keeping a Visitor LogWe all love visitors! It’s a chance to move your business or projects forward, to showcase your work or even to take a respite from those!When putting a process to your visitor management system, when a visitor to your organization has signed in, accomplished something amazing - or maybe just had lunch - with one of your staff, and then signed out... Do you keep the visitor log?Over the course of this series, we’ve discussed all the important steps of having a visitor management process. The final piece of an efficient process occurs almost completely outside the visitor’s experience. While the visitor is aware of signing in and signing out, whether or not you keep a record of visitors is completely at the discretion of your organization. There are definite benefits to keeping a visitor log.Why keep a visitor log?There are some distinct advantages to keeping a visitor log. You never know when you might need to reference the information. Here are some possible reasons and scenarios.Visitor Recall: Some employees meet with LOTS of people: salespeople, job candidates in a low unemployment market, vendors crucial to delivering a great product, potential and current clients, maintenance workers and even key staff from other sites. If they had an unfamiliar walk-in visitor and did not get the name or contact information of that person – or misplaced it – a visitor log can fill in the gap. Categorizing every visitors correctly in your CRM database and following up can be crucial for sales and relationship building.Following Up with Visitors: Perhaps you wish to send a message to certain visitors. For example, if you run a service organization, you might wish to send a survey after visitor departs your facility. The insights and data they provide will allow for continuous improvement. Or, perhaps you hosted a grand opening party or Meetup event. You might wish to recap the event to reinforce the good feelings or cause. With a properly built and maintained visitor log you can automate these tasks.Crime Investigation: If you know exactly when a visitor checked in and out of your facility, it can greatly assist with the investigation of a crime. If even the pizza delivery person must sign in and out, but for some reason spent an hour in your facility on the same day property was stolen, that is suspicious. The crime need not even be committed at your organization. If law enforcement is tracking the movements of a suspect or a victim, as in this case, the information of whether they entered your premises could be vital.Digital vs. PaperMost visitor logs are going to be in one of two forms: a paper log that people sign in and out of, or a digital record.In our increasingly digital world, it is hard to believe that paper logbooks still exist. There are a number of drawbacks to paper visitor records.Bad handwriting can make them impossible to read.Unless closely monitored, it is easier for a person to fake entries, in particular, the check-in and check-out times. It is also easy to bypass altogether.They take up a lot of space.They can’t be sorted by name or otherwise easily searched.Digital visitor logs, especially cloud-based, have several distinct advantages over paper logs.They can be sorted by any field, including name, date, time of check-in or check-out, host name or more. All of the visitor’s info is easy to read.They can be searched quickly and efficiently by computer.They take up only a small amount of digital storage space.They can store other records with the log, like non-disclosure agreements and waivers.The time is logged automatically by the electronic device, and therefore the time cannot be falsified.How Long Should You Store Visitor Log Records?When it comes to keeping organizational records, we often fall into two camps.Throw Everything Out: It frees up a lot of physical and mental space. (There is a reason Marie Kondo is so popular.) However, if you throw out records prematurely, you could find yourself needing them for reference; financial audits are the perfect example.Keeping Everything Forever: This can be beneficial when you need to reference information, assuming the records are kept in an organized system. If, however, you keep everything indefinitely AND your system is disorganized, you might as well just take a bulldozer to your files.As is usually the case, the best scenario is somewhere in the middle: you may have reason to go back in the records two, five or ten years, depending on your organization’s needs.If you are keeping paper records, it is likely they will either be thrown out long before this or filed away in a manner that it is unlikely to be retrieved. Digital records can be automatically archived or deleted after a certain length of time. Even if you choose never to delete the records, they take up so little space that keeping them will be no hassle at all.Wrapping it all upKeeping a visitor log, preferably in digital form, is the final step in a comprehensive visitor management process. A guest is greeted, identified, signs in, meets up with the host and signs out. Then, the log of these visits is filed away to the benefit of all the different parties who might have need of them. It is the final link in the chain of a successful visit and an efficient process.Originally posted by Greetly at What are Visitor Management Techniques and Steps?. Re-posted with permission.
Trusted esignature solution— what our customers are saying
Get legally-binding signatures now!
Related searches to Add Electronic signature Form iPad
Frequently asked questions
How do i add an electronic signature to a word document?
What is the original on an electronic signature document?
Electronic eSign categorized as what occupation?
Get more for Add Electronic signature Form iPad
- How Can I Electronic signature Louisiana Police PPT
- How Can I Electronic signature Louisiana Police PPT
- Can I Electronic signature Louisiana Police PPT
- Can I Electronic signature Louisiana Police PPT
- Can I Electronic signature Louisiana Police PPT
- How To Electronic signature Louisiana Police PPT
- How Do I Electronic signature Louisiana Police PPT
- Help Me With Electronic signature Louisiana Police PPT
Find out other Add Electronic signature Form iPad
- Utah tc 65 2018 2019 form
- California school immunization record hope technology school form
- Ri w 4 form fillable form 2018 2019
- Account identification number form
- Ak 6000 form 2017 2019
- Form 6390 orders and limits federal based credits on an
- Name and ein of alaska taxpayer generating attributes if different from taxpayers filing this return attach additional forms if
- Instructions for form 6395
- Tax forms texas comptroller texasgov
- Form ap 133 texas application for fuels tax texas comptroller
- Alaska corporation net income tax return form
- Instructions for 2017 alaska fishery resource landing tax return form
- Instructions for alaska salmon enhancement tax buyers annual form
- Instructions for form 662sf alaska mining license tax return
- Alaska mining license application form
- Final alaska return form
- Instructions for 2017 alaska regional seafood development tax return form
- Alaska income tax education credit alaska department of revenue form
- Alaska veteran employment tax credit form
- Alaska north slope oil and gas resources boem form