Sign Alaska RFP Secure
Make the most out of your eSignature workflows with airSlate SignNow
Extensive suite of eSignature tools
Discover the easiest way to Sign Alaska RFP Secure with our powerful tools that go beyond eSignature. Sign documents and collect data, signatures, and payments from other parties from a single solution.
Robust integration and API capabilities
Enable the airSlate SignNow API and supercharge your workspace systems with eSignature tools. Streamline data routing and record updates with out-of-the-box integrations.
Advanced security and compliance
Set up your eSignature workflows while staying compliant with major eSignature, data protection, and eCommerce laws. Use airSlate SignNow to make every interaction with a document secure and compliant.
Various collaboration tools
Make communication and interaction within your team more transparent and effective. Accomplish more with minimal efforts on your side and add value to the business.
Enjoyable and stress-free signing experience
Delight your partners and employees with a straightforward way of signing documents. Make document approval flexible and precise.
Extensive support
Explore a range of video tutorials and guides on how to Sign Alaska RFP Secure. Get all the help you need from our dedicated support team.
Document type sign rfp alaska secure
Keep your eSignature workflows on track
Make the signing process more streamlined and uniform
Take control of every aspect of the document execution process. eSign, send out for signature, manage, route, and save your documents in a single secure solution.
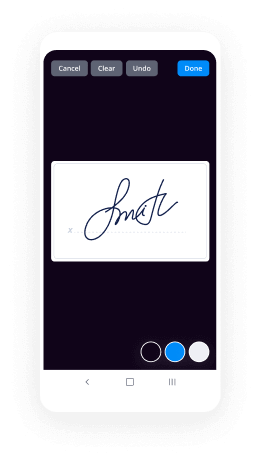
Add and collect signatures from anywhere
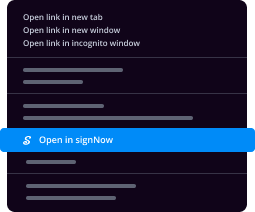
Let your customers and your team stay connected even when offline. Access airSlate SignNow to Sign Alaska RFP Secure from any platform or device: your laptop, mobile phone, or tablet.
Ensure error-free results with reusable templates
Templatize frequently used documents to save time and reduce the risk of common errors when sending out copies for signing.
Stay compliant and secure when eSigning
Use airSlate SignNow to Sign Alaska RFP Secure and ensure the integrity and security of your data at every step of the document execution cycle.
Enjoy the ease of setup and onboarding process
Have your eSignature workflow up and running in minutes. Take advantage of numerous detailed guides and tutorials, or contact our dedicated support team to make the most out of the airSlate SignNow functionality.
Benefit from integrations and API for maximum efficiency
Integrate with a rich selection of productivity and data storage tools. Create a more encrypted and seamless signing experience with the airSlate SignNow API.
Collect signatures
24x
faster
Reduce costs by
$30
per document
Save up to
40h
per employee / month
Our user reviews speak for themselves






Wondering about Sign RFP Alaska Secure? Nothing can be more comfortable with airSlate SignNow. Its an award-winning platform for your company that is easy to embed to your existing business infrastructure. It plays perfectly with preferable modern software and requires a short set up time. You can check the powerful solution to create complex eSignature workflows with no coding.
Sign RFP Alaska Secure - step-by-step guidance:
- Sign up if you have no account yet. You can also log in with your social account - Google or Facebook.
- Get started with a 30-day free trial for newcomers or check airSlate SignNow pricing plans.
- Create your customized forms or use ready-to-use templates. The feature-rich PDF editor is always at your fingertips.
- Invite your teammates and create an unlimited number of teams. Collaborate in a single shared workspace.
- Easily understand Sign RFP Alaska Secure feature by self serve on our website or use the customer support.
- Create document signing links and share them with your clients. Now you can collect signatures ten times faster.
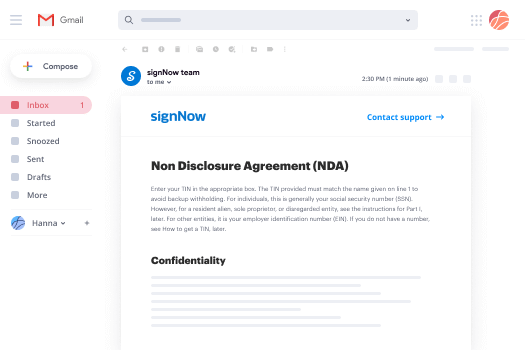
- Get instant email notifications about any user action.
- Try out the free mobile application to be in touch on the go.
Improve your experience with airSlate SignNow. Creating your account, you get everything needed to close deals faster, enhance business performance, make your teammates and partners happier. Try out the advanced feature - Sign RFP Alaska Secure. Make sure it's the best solution for the company, customers, and each individual.
How it works
Find a template or upload your own
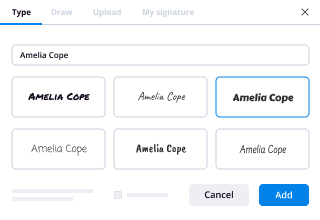
Customize and eSign it in just a few clicks
Send your signed PDF to recipients for signing
Rate your experience
-
Best ROI. Our customers achieve an average 7x ROI within the first six months.
-
Scales with your use cases. From SMBs to mid-market, airSlate SignNow delivers results for businesses of all sizes.
-
Intuitive UI and API. Sign and send documents from your apps in minutes.
A smarter way to work: —how to industry sign banking integrate
Trusted esignature solution— what our customers are saying
be ready to get more
Get legally-binding signatures now!
Related searches to Sign Alaska RFP Secure
Frequently asked questions
How do you make a document that has an electronic signature?
How do you make this information that was not in a digital format a computer-readable document for the user? "
"So the question is not only how can you get to an individual from an individual, but how can you get to an individual with a group of individuals. How do you get from one location and say let's go to this location and say let's go to that location. How do you get from, you know, some of the more traditional forms of information that you are used to seeing in a document or other forms. The ability to do that in a digital medium has been a huge challenge. I think we've done it, but there's some work that we have to do on the security side of that. And of course, there's the question of how do you protect it from being read by people that you're not intending to be able to actually read it? "
When asked to describe what he means by a "user-centric" approach to security, Bensley responds that "you're still in a situation where you are still talking about a lot of the security that is done by individuals, but we've done a very good job of making it a user-centric process. You're not going to be able to create a document or something on your own that you can give to an individual. You can't just open and copy over and then give it to somebody else. You still have to do the work of the document being created in the first place and the work of the document being delivered in a secure manner."
How do i insert an electronic signature into a word document?
How do I sign a text file with a text editor?
How do I convert an .rtf, .otf, or .woff file to a proper .doc format?
How do I edit an .doc file using an application like MS Word?
How do I save an .doc or .rtf file in Adobe Illustrator format?
Can I import a .doc, .rtf, or .otf file in Microsoft Publisher?
How do I convert WordPerfect (.doc), MS Word (.doc), OpenOffice/LibreOffice/Adobe Acrobat (.odt).
How do I import a file using MS Outlook?
How do I import a Microsoft Office Document?
I'm having trouble saving a document (how do I find a particular document in the archive? what does that mean? what does it mean to add something to a file or folder in Exchange?
I'm having problems saving documents in Microsoft Office, is there any way I can export or save these documents? If so, what settings would make the file most helpful to me?
I'm having problems saving a file in Microsoft Office (Exchange). Is it possible to find out how a file is saved?
I'm trying to get a document to print but cannot find the printer I want to use. How do I set up the printer and find it on the network?
Do you have a tool that shows me which Exchange servers can access the Exchange Online folder structure?
What are the differences between the Exchange 2003, Exchange 2004, Exchange 2007, Exchange 2010 and Exchange 2013? Can you describe the differences between the three Exchange Server versions?
If an Exchange user has multiple email addresses, how can I change their email...
How do you put an electronic signature on a pdf?
The pdf must also be compressed using GZIP or any other compression method. The format of the pdf is specified with its filename in the metadata. For a more detailed description of the format of this file refer to the Wikipedia.
What is this file about?
The metadata is a simple format used to describe the content of a file. It consists of a file name (in case the file is a zip archive), a header section, a body (the actual content of the file), and a final section in which a description is written or the filename and the name of the author are appended. The metadata may consist of one or many lines, with each line containing a header row, a body column, and a description. The description line may also contain a line that is terminated by a semicolon.
The metadata is used in the following formats:
The header section defines the format of a document and is written in standard Unicode (Unicode ) or ASCII format (Unicode ).
The body is the actual content of the file. This could be an actual text-file, an image, a video with audio (MPEG audio and MPEG-1 Audio Layer 3), or anything else with data content that might be described. The header section contains a series of text fields with values. For each field there is a corresponding value that can be used to write a description of the contents of the file (which includes the metadata).
The description is an optional line that can be used to describe the contents of the file. It starts with a semicolon and is delimited by ano...
Get more for Sign Alaska RFP Secure
- Sign Virginia Postnuptial Agreement Template Free
- Sign Virginia Postnuptial Agreement Template Myself
- Sign Virginia Postnuptial Agreement Template Secure
- Sign Connecticut Divorce Settlement Agreement Template Easy
- Sign Virginia Postnuptial Agreement Template Fast
- Sign Virginia Postnuptial Agreement Template Simple
- Sign Virginia Postnuptial Agreement Template Easy
- Sign Connecticut Divorce Settlement Agreement Template Safe
Find out other Sign Alaska RFP Secure
- Printable snap application form
- Solicitud de inscripcin de sociedades mercantiles ante la superintendencia de administracin tributaria y el registro form
- Drill and ceremony performance test sheet t228
- Lausd form 8239
- W w x x x x form
- Rev 0112 application for registration as a potential smartdrivinginstructortraining co form
- Employee reimbursement form
- Form 604 fair political practices commission state of california sbcvote
- Noc form for passport
- Veba montana form
- Sxcran 233354234 form
- History of guardians brotherhood form
- Longarm quilting intake form
- Icici claim form 91896254
- Image of form to fill to apply for credit card
- Uf college of pharmacy physical form
- W w x x x x 74421950 form
- Application to add a father on a state of michigan michigan form
- Skills worksheet critical thinking analogies answer key form
- Dom 302 medicaid ms form