Cloud Security Trust Signed Made Easy
Upgrade your document workflow with airSlate SignNow
Agile eSignature workflows
Fast visibility into document status
Simple and fast integration set up
Cloud security trust signed on any device
Advanced Audit Trail
Rigorous protection requirements
See airSlate SignNow eSignatures in action
airSlate SignNow solutions for better efficiency
Our user reviews speak for themselves






Why choose airSlate SignNow
-
Free 7-day trial. Choose the plan you need and try it risk-free.
-
Honest pricing for full-featured plans. airSlate SignNow offers subscription plans with no overages or hidden fees at renewal.
-
Enterprise-grade security. airSlate SignNow helps you comply with global security standards.

Your step-by-step guide — cloud security trust signed
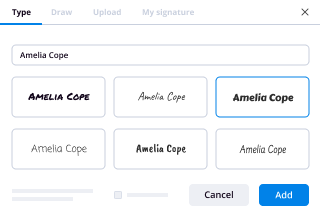
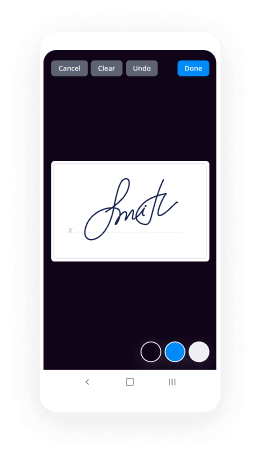
Adopting airSlate SignNow’s electronic signature any business can increase signature workflows and eSign in real-time, giving an improved experience to consumers and employees. Use cloud security trust signed in a couple of easy steps. Our mobile-first apps make work on the move possible, even while off the internet! Sign contracts from anywhere in the world and close up deals faster.
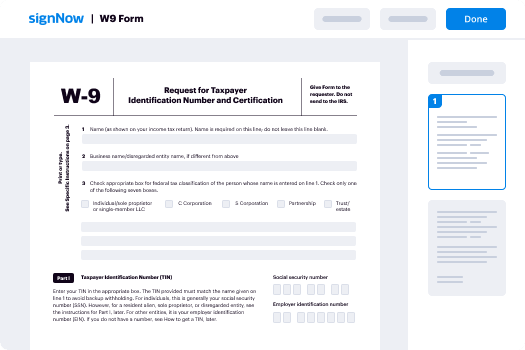
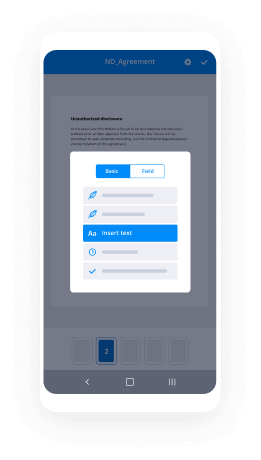
Keep to the step-by-step instruction for using cloud security trust signed:
- Log on to your airSlate SignNow account.
- Locate your record in your folders or upload a new one.
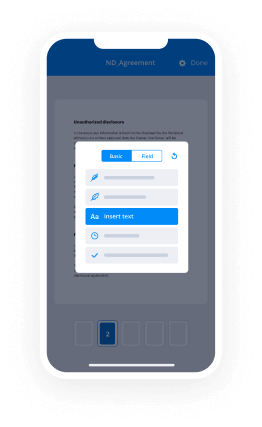
- Open up the document and edit content using the Tools menu.
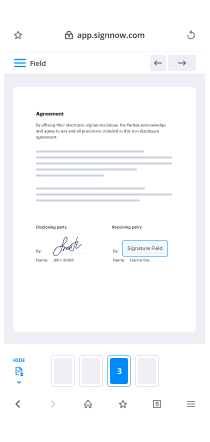
- Drag & drop fillable areas, type text and eSign it.
- Include numerous signees by emails and set up the signing sequence.
- Choose which recipients will get an completed version.
- Use Advanced Options to limit access to the record add an expiration date.
- Click Save and Close when done.
Furthermore, there are more extended functions available for cloud security trust signed. Add users to your shared workspace, view teams, and track collaboration. Millions of users across the US and Europe concur that a solution that brings people together in one holistic digital location, is the thing that companies need to keep workflows working effortlessly. The airSlate SignNow REST API enables you to integrate eSignatures into your app, internet site, CRM or cloud storage. Check out airSlate SignNow and get quicker, easier and overall more efficient eSignature workflows!
How it works
airSlate SignNow features that users love
See exceptional results cloud security trust signed made easy
Get legally-binding signatures now!
FAQs
-
What is trust in cloud computing?
Trust based on the service provider: by trust in performance, a user trusts a cloud service with respect to performance, security, and privacy, based on the identity of the provider. If the user trusts that the provider gives trustworthy cloud services, then the cloud service is trusted. -
How security is provided in cloud computing?
Cloud security, also known as cloud computing security, consists of a set of policies, controls, procedures and technologies that work together to protect cloud-based systems, data, and infrastructure. ... From authenticating access to filtering traffic, cloud security can be configured to the exact needs of the business. -
What are trust models?
A trust Model is collection of rules that informs application on how to decide the. legitimacy of a Digital Certificate. There are two types of trust models widely used. ... Hierarchical models allow tight control over certificate-based activities. -
What is hierarchical trust model?
In hierarchical trust model, CAs are assembled under a common root CA, which issues certificates to Sub CAs. ... It has a single root CA and is holding all certificates; all end-users refer to and trust it for all transaction. -
How does certificate trust work?
The chain of trust of a certificate chain is an ordered list of certificates, containing an end-user subscriber certificate and intermediate certificates (that represents the intermediate CA), that enables the receiver to verify that the sender and all intermediate certificates are trustworthy. -
Can cloud data be lost?
Computers freeze and backup copies are lost. Other times, servers crash and the information contained within is lost. These are all potential sources of data loss, and the cloud is not exempt from technology failure or human error. ... Software-as-a-Service (SaaS) applications are a potential source of massive data loss. -
What is disadvantages of cloud computing?
Downtime: Downtime is considered as one of the biggest potential downsides of using Cloud Computing. The cloud providers may sometimes face technical outages that can happen due to various reasons, such as loss of power, low Internet connectivity, data centers going out of service for maintenance, etc. -
What are some of the benefits of a cloud based service for trust management?
Cloud environments promise several benefits such as reduced expenses and simplicity to service providers and service requesters [Fos- ter et al. ... Given the accelerated adoption of cloud computing in the industry, trust manage- ment is still considered as one of the key challenges in the adoption of cloud com- puting. -
Is cloud computing secure?
Whether 10 years ago or just last week, companies continue to ponder, \u201cis cloud computing secure?\u201d The truth is cloud computing is just as secure, if not more secure, than a traditional server if configured properly. In fact, most security bsignNowes in the cloud are the fault of the customer, not the cloud network. -
How do I choose a service provider?
have a strategic focus; be sustainable and effective; embrace new technology; understand space planning; see itself as more than just a service provider; offer a personalised service. -
Is cloud storage safe and secure?
Yes, your data is relatively safe in the cloud\u2014likely much more so than on your own hard drive. In addition, files are easy to access and maintain. However, cloud services ultimately put your data in the hands of other people. If you're not particularly concerned about privacy, then no big whoop. -
How secure is Google cloud?
Once your data arrives with Google, it is encrypted in order to keep it secure within its cloud servers. Google uses 128-bit AES encryption for all data that is at rest. Although this is not as strong as 256-bit encryption; it is still considered future proof for the time being. -
What are security risks of cloud computing?
The main security risks of cloud computing are: Compliance violations. Identity theft. Malware infections and data bsignNowes. -
What is Google Cloud Security?
The Google security model is an end-to-end process, built on over 15 years of experience focused on keeping customers safe on Google applications like Gmail, Search and other Apps. With Google Cloud Platform your applications and data take advantage of the same security model. -
What is cloud security and why is it required?
Cloud security is a set of control-based safeguards and technology protection designed to protect resources stored online from leakage, theft, or data loss. Protection encompasses cloud infrastructure, applications, and data from threats.
What active users are saying — cloud security trust signed
Related searches to cloud security trust signed made easy
Cloud security trust signed
[Music] the cloud and mobility are creating a mega shift that's disrupting 30 years of networking and security infrastructure let me share with you why a traditional network and security architecture is no longer suitable for the cloud and mobile fast walk applications are moving to saps and to public logs the users are no longer sitting in the office they are working from everywhere but security is still anchored to the data set until now Z's killer is redefining network security we are a pioneer in cloud security and are a market leader today the Z's killer cloud protects more than 2,800 customers with users in over 185 hundreds more than 200 of the Forbes Global 2000 count on Z's killer to help them move securely to the cloud during peak periods our cloud processes almost 40 billion transactions per day it blocks more than hundred million threats every day and performs over 120,000 unique security updates to keep users safe zees killer has a massive opportunity to to place the estimated seventeen point seven billion dollars of network security market and in the process we offer our customers the opportunity to substantially reduce spending on expensive networking infrastructure as the embrace a mobile first and a cloud first rat I started descaler because I envisioned that digital transformation would happen in the enterprise this vision has become a reality today prior to funding Z scalar I found it funded and built for companies three of them in the security space having the success under my belt I was at a stage in my life where I was no longer interested in doing one more startup with security point products I wanted to build something lasting I want to do fix cloud security I dreamed of building a security platform from a clean slate a platform that was deep and wide in functionality a platform that is born in the cloud for the cloud it was a big undertaking that generally startups don't try to tackle but I had the conviction and financial resources to take it on to realize this dream I invested my own life savings I found a team of talented engineers in Silicon Valley with expertise to build a highly scalable cloud company and we named a company Z scalar which stands for zenith of scalability today the Z scalar cloud is scaling new heights it is transforming the old world of IT to a cloud enabled enterprise we have achieved significant scale in annual recurring revenues with very low cost churn and are enjoying rapid growth and with just getting started IT security has traditionally focused on the premise that users data and application all reside on the copper net where the copper network is the castle surrounded by the mode of securing appliances to allow traffic in and out of the castle organizations created Internet gateways these gateways consisted of network firewalls do separate the internet from the corporate network the model is commonly referred as castle and mode as Internet traffic increased cyber threats became more sophisticated more appliances were bought and deployed to improve security and handle growing traffic due to expense of these appliances organization built a small number of gateways and backhaul branch traffic to these centralized gateways for security this model is called hub and spoke Network the architecture results in high networking comest and a poor user experience no wonder users complain that Internet is faster at home than it is in their office there are two types of Internet gateways the first one is outbound gateways that enable users to safely access the Internet it consists of multitude of appliances from a network firewall to sandboxing that they need to buy deploy and manage the second kind inbound or remote VPN gateways that lets users safely access internally managed application it also consists of a litany of appliances load balancers firewall DDoS protection and VPN concentrators cloud and mobility are disrupting the traditional hub-and-spoke and castle and noir architecture applications are moving from the data center to the cloud for better experience many users no longer want to go through the data center for cloud-based applications they want to go bypassing security controls they put themselves and the company at risk with all the recent high-profile security breaches do I need to say more enterprise security has been about securing the castle which is the corporate network but as cloud becomes the new data center and the internet becomes a new corporate network how can you secure the network that you can control that is why a fundamentally new approach to network security is needed z scalar pioneered a new approach to not only deliver security but to enable transformation of network and applications for applications the old wall was applications in centralized data center the new world is applications SAS Azure ahead of us for networking old world was hub-and-spoke network the new world direct to cloud network for security the old world network centric castle and mode to create a perimeter for securing the network the new world user centric no premier no network security Z scale is redefining security by moving into the cloud and using business policies that securely connect the right user to the right application the Z scalar platform functions as an access control and security checkpoint sitting in over a hundred data centers around the goal so regardless of where you are and what device you're on you simply get dragged to the nearest data center security policy is followed and deliver the same policy and same protection whether you are at an office or a hotel or a coffee shop Z scalar offers two principal cloud services Z's killer internet access and these killer private acts let's talk to the first one Z's killer internet access or CIA was built from the beginning to replace outbound gateways CIA sits between the user and the Internet it securely connects users to externally managed applications and is designed to ensure that malware doesn't come to the users and the valuable copy data doesn't leak out as you move your enterprise from a hub-and-spoke network to a direct to cloud architecture you don't worry about building album gateways by buying and deploying branch firewalls proxies antivirus gateway as and the like with Z scalar there's no dealing with dispatching service agents to troubleshoot machines there's no dealing with end-of-life Hardware replacements there's no shipping new boxes to replace failed machines all this lack of drama has allowed our teams to focus on more strategic initiatives and deliver greater value to the business in 2016 we introduced Z scalar private access or CPA this was to replace the inbound gateway zpa is not VPN 2.0 it fundamentally changes how users access internal applications these applications may be hosted in your data center or in public clouds such as Azure or AWS I had never heard anyone tell me that they love the VPN experience and it gets worse for the world of cloud a for users sitting in a hotel wants to access an application on agile they must traverse through the own Prem security stack then out to the cloud over a site-to-site VPN only do have to retrace the same route back to them you moved your application to a modern cloud platform but your security and access relies upon 30 year old technology with zpa there's no need to build a virtual file or a virtual VPN in the cloud you simply connect through Z scaler and we take care of the rest while some traditional security vendors are deploying the single tenant software on virtual machines in a data center and calling it a cloud or a hybrid cloud z scarab built a true cloud it's distributed it's multi tenant and it has three-tier architecture this architecture has three key pieces number one control plane that's like the brain and nervous system of the cloud number 2 the data plane it enforces policy number 3 the logging plane for real-time logging and reporting our core technologies backed by over 100 issued and pending patents include several innovations and differentiated approaches to difficult challenges facing any platform operating at our scale Z Square does full inline inspection of Internet traffic including SSL inspection and perform real-time threat correlation using multiple techniques for better track prevention we believe our architecture has a big competitive advantage can you build a power plant using power generators design for your home use will Tesla ever build a hybrid car I don't think so the purpose-built an electric car that works and goes the distance we are deployed in over hundred data centers across five continents and we appeared with major telecom providers SAS providers public cloud providers internet content providers and other popular internet destinations the scale of our cloud provides us with a network effect that delivers insight into advanced and zero-day threats as they emerge how big is the cloud effect well forty billion requests hundred million threats detected and Lord and 120,000 unique security updates are they for our customers can you imagine doing that with appliances the scaler enables us really to have a central view of how we're using Internet how our distributed workforce is accessing the cloud or is accessing the web and it's incredibly useful because we want the high level of security but at the same time we want to enable our workforce wherever they are wherever they are walking 4z scaler provides four compelling benefits to customers number one better user experience with a direct to cloud architecture users connect to the nearest a scalar data center taking the shortest path to application resulting in a fast user experience number two improved security and reduces businesses our cloud platform was designed to provide full inline inspection of Internet traffic including full SSL inspection and performs real-time threat correlation using multiple techniques for better threat prevention number three eliminates certain network security costs our solution eliminates the cost of buying and managing multiple security appliances and reduces dedicated wide area networking costs for our customers number four simplicity our solution delivers the functions of a traditional internet gateway as a cloud service we help simplify the entire enterprise network topology by minimizing the need for hub-and-spoke networks and related hardware infrastructure the evidence of our success is in a large and diverse customer base we have more than 2,800 customers including over 200 of the Forbes Global 2000 and some of the largest customers in major sectors our deployments with our customers are meaningful most customers and all of their traffic through these killer clouds Puri platform and many organizations use us for tens of thousands of users we have around 350,000 Siemens employees which get routed day by day through Z scaler to the Internet it is a certain I would say level of trust you need to run your entire internet traffic over there solution in fact we said we will end up with much higher resiliency if we let them manage this for us than just relying on our own data center capabilities and their availability why is these color wins in the market here are four big reasons number one differentiated architecture and technology that enables cloud transformation securely and efficiently this results in a compelling return on investment sitting in the traffic path scanning every byte for security and policy without introducing latency is not a trivial technology to build and scale number two market leadership we are a market leader in cloud security with an established reputation and brand number three operational accidents we have proven operational experience an unmatched scale with over nine years of experience in running our cloud and over hundred data centers across the globe we are excited about how far we have come we feel that in the early innings of the cloud transformation and are thrilled about the journey ahead new leaders are born when mega ships take place we are trying to disrupt 30 years of networking and security infrastructure
Show moreFrequently asked questions
How do I eSign a document before sending it?
What do I need to sign a PDF electronically?
How can I electronically sign a PDF document on my phone?
Get more for cloud security trust signed made easy
- Print signature service Lease
- Prove email signature Customer Satisfaction Survey Template
- Endorse eSign Service Quote
- Authorize digital sign Lease Amendment
- Anneal signatory Bridge Loan Agreement
- Empower electronically signed T Shirt Order Confirmation
- Try digisign Pet Adoption Letter
- Add Assurance Agreement eSign
- Send SaaS Sales Proposal Template eSignature
- Fax Free Graduation Certificate autograph
- Seal Training Acknowledgement Form electronic signature
- Password Indemnification Agreement signed electronically
- Pass Outsourcing Services Contract Template electronically sign
- Renew Pet Custody Agreement electronically signing
- Test School Counseling Progress Report mark
- Require W-9 Tax Form signed
- Send corroborator signature
- Accredit spectator initial
- Compel recipient digital sign
- Void Freelance Quote Template template esigning
- Adopt certificate template digisign
- Vouch Notice To Vacate Form template electronic signature
- Establish Proposal Letter template countersign
- Clear Founders’ Agreement Template template sign
- Complete Child Medical History template electronically signing
- Force Sales Agency Agreement Template template initials
- Permit Professional Model Release Contract template eSign
- Customize Interior Design Contract Template template eSignature