Consent Time Field with airSlate SignNow
Get the powerful eSignature capabilities you need from the solution you trust
Choose the pro service made for professionals
Set up eSignature API quickly
Collaborate better together
Consent time field, in minutes
Reduce your closing time
Keep sensitive data safe
See airSlate SignNow eSignatures in action
airSlate SignNow solutions for better efficiency
Our user reviews speak for themselves






Why choose airSlate SignNow
-
Free 7-day trial. Choose the plan you need and try it risk-free.
-
Honest pricing for full-featured plans. airSlate SignNow offers subscription plans with no overages or hidden fees at renewal.
-
Enterprise-grade security. airSlate SignNow helps you comply with global security standards.

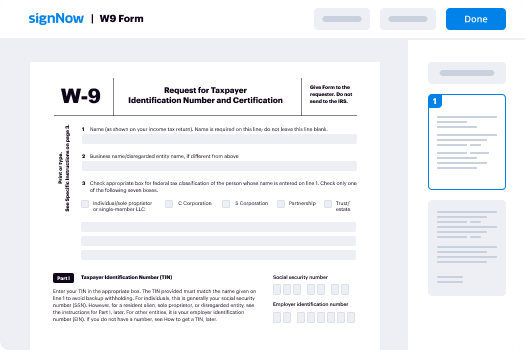
Your step-by-step guide — consent time field
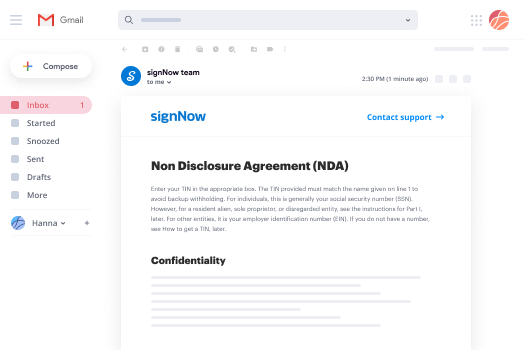
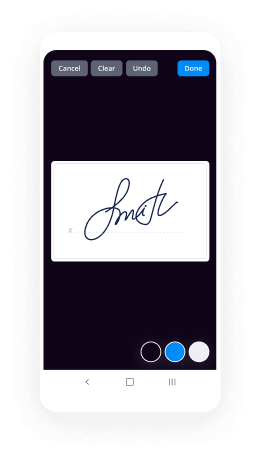
Employing airSlate SignNow’s electronic signature any company can accelerate signature workflows and eSign in real-time, supplying an improved experience to clients and workers. consent time field in a few simple actions. Our handheld mobile apps make work on the run achievable, even while off the internet! eSign documents from any place worldwide and close tasks faster.
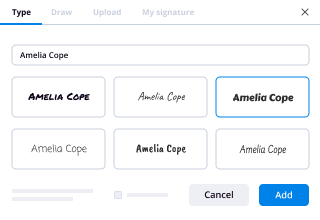
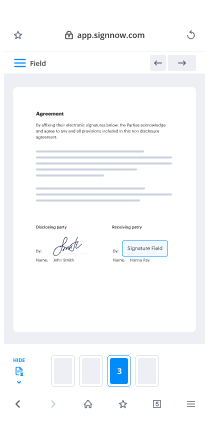
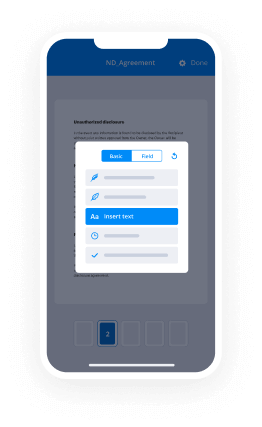
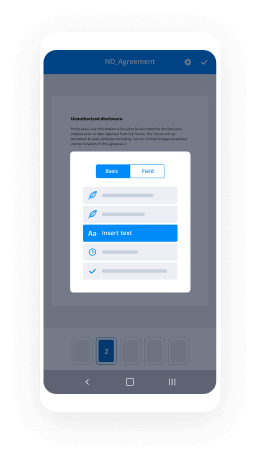
Take a walk-through guide to consent time field:
- Log on to your airSlate SignNow account.
- Locate your needed form in your folders or upload a new one.
- Open up the record and make edits using the Tools menu.
- Drag & drop fillable areas, type textual content and eSign it.
- Include several signers by emails and set up the signing order.
- Specify which recipients can get an completed version.
- Use Advanced Options to limit access to the document and set up an expiration date.
- Press Save and Close when done.
In addition, there are more innovative functions accessible to consent time field. Add users to your collaborative workspace, view teams, and track teamwork. Millions of users all over the US and Europe recognize that a solution that brings people together in one unified enviroment, is the thing that enterprises need to keep workflows working easily. The airSlate SignNow REST API enables you to integrate eSignatures into your application, internet site, CRM or cloud. Check out airSlate SignNow and enjoy faster, easier and overall more efficient eSignature workflows!
How it works
airSlate SignNow features that users love
See exceptional results consent time field with airSlate SignNow
Get legally-binding signatures now!
FAQs
-
How do you get consent from participants?
Obtaining consent involves informing the subject about his or her rights, the purpose of the study, the procedures to be undergone, and the potential risks and benefits of participation. Subjects in the study must participate willingly. Vulnerable populations (i.e. prisoners, children, pregnant women, etc.) -
What are the basic elements of informed consent?
A statement that the study involves research, an explanation of the purposes of the research and the expected duration of the subject's participation, a description of the procedures to be followed, and identification of any products which are experimental. -
What are the 4 types of consent?
Types of consent include implied consent, expressed consent, informed consent and unanimous consent. -
How do you get consent?
Clear. Consent is clear and unambiguous. ... Ongoing. You should have permission for every activity at every stage of a sexual encounter. ... Coherent. Every participant in sexual activity must be capable of granting their consent. ... Voluntary. Consent should be given freely and willingly. -
What is the importance of informed consent for research?
Defining Informed Consent It is that important. Informed consent provides participants with sufficiently detailed information on the study so that they can make an informed, voluntary and rational decision to participate. This includes: The purpose of the study. -
What type of consent must a first aider use to treat unconscious patient?
Whether you are a bystander or a professional who renders aid, an unresponsive patient has "given" implied consent just by virtue of being unconscious. The idea is that a reasonable person would give consent for treatment in that situation if they were able. -
Who signs informed consent?
Important Note: The California Medical Experiment Act requires attestation that the consent form is signed and dated by a person other than the participant or the participant's guardian or legally-authorized representative who can attest that the requirements for informed consent has been met. -
What should be included in a consent form?
A statement that the study involves research, an explanation of the purposes of the research, the expected duration of a subject's participation, a description of the procedures to be followed, and if applicable identification of any experimental procedures. -
What is consent in research ethics?
Consent. Consent is the central act in research ethics, as set out in the 1947 Nuremberg Code. ... 'Research subjects must be informed fully about the purpose, methods and intended possible uses of the research, what their participation in the research entails and what risks, if any, are involved. -
What is included in a consent form?
A statement that the study involves research, an explanation of the purposes of the research, the expected duration of a subject's participation, a description of the procedures to be followed, and if applicable identification of any experimental procedures. -
How long is written consent valid?
Some facilities say signed informed consent forms are valid for 30 days, or the duration of the patient's hospital stay. Others state that a patient's informed consent is active until a patient revokes it, or the patient's condition changes. -
How do you write a research consent form?
Provide the title of the research project, the researcher(s) name, supervisor's name (for 2. student research), the Unit in which the researcher is based and the name of the governing institution. State that the PIS has been read and the participant has had the opportunity to ask 3. questions of the researcher. -
Why is consent to treatment important?
Patient-informed consent means patients understand the risks, alternatives and possible benefits of any treatment they receive. ... This is important since even treatments which are meant to help a patient come with risks, and it is essential for patients to accept those risks when getting care. -
What is informed consent and what does it mean?
Medical Definition of Informed consent Informed consent: The process by which a patient learns about and understands the purpose, benefits, and potential risks of a medical or surgical intervention, including clinical trials, and then agrees to receive the treatment or participate in the trial. -
Who can give consent on behalf of a patient?
What may not be as clear is who can give consent for treatment. An adult 18 years of age and older can give consent for his or her own treatment, unless they have a guardian who is designated to provide consent for the individual.
What active users are saying — consent time field
Related searches to consent time field with airSlate airSlate SignNow
Consent time field
good afternoon everyone I am excited that a lot of you guys came to join us today I know it's sort of the tail end of cis and this serve the last push but um for those of you that don't know me so my name is Remy Lyle I'm a regional Solutions Architect with ping which basically means that I get to solve our customers problem and I'm on the front lines along with the rest of my team and I've been in the identity space for the last 12 years as a PS person developer POC are architects occasionally support engineer support doesn't answer your tickets so yeah so today we're going to talk about what we're seeing in the field as far as content management and just some design patterns everything but I'll expand on that so um so just a little bit of intro I think that very recently we're hearing a lot of buzz with consent management especially around you know gdpr what's interesting is that I think if you especially for those of us that have been in the industry for a while and identity and access management traditionally when somebody says I am we tend to think you know user provisioning we tend to think you know role based access authorization single sign-on Federation proofing but not really so much around you know controlling the data and you know giving users control about what attributes they can see but there's definitely a lot of you know sort of buzz around it you know there's a lot of blogs and vendors are writing about it analysts are writing about it um we decided though that for this talk to make things a little bit more interesting is you know what is the field actually seeing if any of you know Steve show who's the chief product officer at Payne he loves the field we kind of he looks to us a lot of times to help drive the direction of where you know the strategy is going for our products because from a practical level that's where things are actually happening right so I think that you know there's a lot of you know you right about it there's a lot of you know sort of theoretical talk at the high level and you know the open standards group and all that but at the end of the day you know the people that are out in the field you know what is what is actually being deployed what is practically you know how our customers kind of seeing everything so Pam thought it would be a good idea to kind of get the the field perspective and you know having spent you know my entire career in the field thought that we could kind of talk about it so just so you guys know the design patterns that we'll talk about is not just you know my own experience but it's actually a collection of the different interactions that you know ping customers have had or that are you know are essays at paying have had with our customers so you know water you know the approach we took is you know if somebody were to design you know content management system completely vendor agnostic you know what are some design patterns that you should be considering when you're you know thinking about putting together consent management in the perspective of identity management so you know what our customers actually asking for how are they actually defining consent and that's what we'll talk to you guys about today so this is a fun first question well what is consent I think the thing that I found most interesting right off the bat is I asked this question to just five people and I got five completely different answers at the heart of it all I mean it there's there's many different types of consent right so there's consent as far as you know I am you know I am jeido at mydomain.com and I consent to give my mail to a point out me you know I let them do you know view my email calendar you know sort of more granular attribute scopes basis as far as consent goes and then you also have the more all-encompassing you know Terms of Service and it's funny because not a lot of people even pay him actually when her and I were kind of going through this even view sort of Terms of Service as a form of consent but in many ways it is consent right the user is saying hey I agree to whatever this long verbage that you have in front of me that says you know I have to give you my firstborn and give up my data and all that good stuff right so it you know it's a different definition for everybody and I think the thing that I find most interesting is that consent management itself is not something new right I mean health care has been doing it for a really long time you know I you know fill out a consent form I you know write that you know hey I'm participate too you know I agreed to participate in this research but I think where it's really new for us is you know kind of embedding that within the user profile and you know including that within identity management and allowing users to not only update their first name or last name or address but as part of that also you know have the ability to you know granular granularly control their data so it's getting there it's maturing but uh again kind of the you know sort of varies right now for what how customers are defining it so the first design pattern that we see is that it really is its own object type even for the implementations that we've done we tend to wrap consent if you look at you know how the user data is actually stored it's actually part of the user object but in many ways it really is its own independent object type so it's very similar to roles and that you know within within my user object you know I can have a role but you know within my user object I can have all the different consents that I have but what's interesting is that you know similar to roles it has its own metadata right so you know how did I you know what is the description of this metadata how did I use it what's the version of this and it really has its own life cycle which I'll go over in the next slide and there's a workflow component that's part of that because similar to roles you have to have a crud layer on top of it so how do you create consent how do you update it how do you manage it and then how do you you know remove it or revoke it typically we see it stored as as a JSON object and the other thing that's really interesting to me about consent is it can live beyond the identity so if you think of consent for example you know between the you know a husband and wife or legally legal relationships right even though the identity might physically no longer be there their consent lives on right and you know you still have to honor that in many ways so there's you know there's legal relationships there's real estate relationships so to me it's a really interesting identity related object because you know unlike you know roles that sort of you know die with the identity consent is unique in the sense that it can really live beyond the identity which is something that's pretty unique to it from a life cycle perspective pretty straightforward this is you know how we envision or how we've been seeing consent you know manage so you have the creation of the consent and then you have a management of that and then you have either you know a user revoking that consent or perhaps the consent expires right which are two different use cases and then obviously you have an option to renew and then you want to make sure that you're auditing and logging consent as part of that um one thing to consider is you know it's funny because again it this kind of goes back to the fact that you know consent management with an identity management is still maturing but you know when you say you do consent management you have to consider things like well how you know how often am i collecting this consent so there's there's a timer on it that's in many ways similar to a password object right in the sense that okay if a user collect you know if a user agrees you know to this specific thing you know how long is that valid for and then you know I have to have a timer on that from an implementation perspective because you know at the end of 12 months or at the end of six months I want to make sure that I either you know ask him again to renew or you know I you know I collect their consent again or maybe they just revoke it another interesting thing is specifically maybe more closely related to Terms of Service you know our users agreeing to you know your the latest version of your consent you know what if you have minor change in wording you know how do you how do you handle that and so with that this is actually an example schema that we used for consent that we actually used out in the field the only thing I would say I sort of modified for this presentation is I separated out the consent as its own actual object but you'll notice that within you know the consent object itself you know what is we you know we gave it a you RN type identifier I just gave it a little bit of a description the consent manifestation is you know if for example if you look at the what this consent is it's - you know a consent for a user - you know hey you can you know send me newsletters via email so perhaps for you know in terms of service you could say well this is you know Terms of Service and it manifests itself as a term service that the user agreed to or if it's for example more on the OAuth you know scope attribute level then maybe the ID is the actual attribute that you're using that you're you know having the user agree to share but maybe it's an application that will actually receive that you know that specific attribute you know is this required true or false and I think again what's interesting about this is that you know while this is you know kind of loosely the schema that we've been seeing implemented for our own content management implementations for customers there's plenty of variations to this and I was trying to find you know okay what's sort of common between all of them right and then from from a user data perspective you know we want to store well how did we collect this consent you know what is the timestamp when does this expire you know did they opt in to this or did they opt out so um again this is the you know schema that we followed but there's definitely variations of this from customer to customer that we found in the field the other interesting point is if you look at for example some of the open standards work that are out there you know Kent era is putting together or has put together the consent receipt specification and the idea behind that is you know you get a receipt when you you know and you agree to something kind of similar to how you would receive you know receive from you know purchase or something like that but again it comes down to the fact that you know different businesses define consent differently and again there's the question of you know is there enough commonality for a schema to be use as I mentioned I mean this is in the field kind of has worked for us but I think over time I'm sure a lot of very smart people will come together and say you know what I think we should all be using the same you know naming conventions and standards and all that and the format for this but so far nothing yet so from the field we sort of at least for you know from our team's perspective this is what we've you know managed to put together the other thing that definitely customers are asking us for is consent transparency they want to provide their their users or their constituents with an with the ability to self-service manage the consents I think right now it's pretty prevalent still that there's a lot of consents that are given during registration but then there's really not an opportunity to to modify that from a user perspective and I think definitely with gdpr there's a lot of shift and making sure that as part of the profile management UI that consent is taken into in consider in consideration as part of that it's important for a lot of our customers and this is something that we see in all our fees is that you know whatever solution we go with that we provide user is the ability to cook those consents at any time because you know obviously for our customers it would could potentially lead to fines and penalties you know frustrated users and threats to privacy the interesting question here though is how granular you're allowing your users to change consents because and I actually have a graph of this later on you know are are we making consent so granular that it becomes you know physically hard for users to manage that right like are we really expecting our users to log into their profile management and keep up with all the consents that they've given and make sure that oh I really don't want this or that so I think it's important to consider the UI that we're building and yes we want to give users control over their data but at the same time we don't want to make it overwhelming so that they tend not to you know you know go to go to that port or at all or you know decide to serve shy away from the the power that we're giving them from our perspective this is an example of a UI that that we put together as you can see it's pretty simple even though we're storing all that metadata in the backend we're simplifying it from a front-end from a user perspective or just saying hey did you grant this to delivery Co you know these were the attributes that you provided this is the description of that so again kind of UI has to be taken into consideration as far as transparency from an opt-out perspective this is another requirement that a lot of we're we're seeing out a lot in the field we want to make sure that there is an enforcement of the opt-out whether this is you know allowing users to revoke their consent or letting an expiration period expire one thing that I found interesting about this this pattern is that there's there's a lot of focus on this in the RFPs that we see you know everybody's so caught up in make sure that whatever the system you're designing you're honoring the opt-out but it's interesting because you know opt-in I think is just as important right and we'll talk about that in a minute but from an opt-out perspective like who are really enforces consent you know in the implementations that we've done and any kind of the design that we've done we add a governance layer on top of the data for consent and then that from an identity provider perspective we provide the opportunity to enforce consent but from an application side the applications that are receiving the consent we really don't have any guarantee that they are you know that they're enforcing this consent our governance layer you know utilizes you know zackham oh so that we can apply that fine-grain access control and what's interesting is that I actually had this idea of consent governance right so if you if you look at traditional identity and access management today we have you know we have the idea of access governance but and you know the whole theory behind that is that you know you have systems that go back and check to see well you know did does you know is this person really supposed to have this access you've granted it now we're sort of doing an audit to make sure that you you granted you know the right access but what about consent and how do you address you know conflicts that arise from that just so again that's something to consider when designing your consent management system so this is an implementation example a design example so if you notice here we have a policy that we wrote we said you know if the client ID is you know marketing engine and the user isn't opting in we want to make sure that we exclude emails so if we look at the actual response you'll notice that depending so this is the same data call but depending on the users preference right so if you notice at the top part the user said no I don't want in there for the data the JSON data that we give back to the application actually doesn't include the email address right but if we say yes the user is opted to this then you actually see the email so again from a identity provider perspective when we're providing that data to the requesting application we are honoring the users consent but that's not to say that you know the service provider might not have saved email from a previous session right so that's the whole concept between you know who really enforced it we can design systems so that we you know we provide the data of how the user you know has has preferred their data to be shared but ultimately you know it could also not be guaranteed here's some examples of design design for for opt-out you eyes just to give you guys kind of more concrete example so on the on the upper right-hand side I just left from here guys prospective users can say hey I want to remove my consent and then from the other perspective you know we have a you know a similar UI where we say okay for this client you know do you want to revoke you know sharing your if there were scopes there you know sharing the information with the specific client so kind of coming back to that opt-in comment that I was making so there's definitely a lot of requests from from our customers to enforce opt-out but really opt-in is just as important um some clients you know kind of view this is like well if I have different tiers of opting in you know that allows me to have you know more effective campaign targeting you know I know that you know this user is more engaged than another user and for them that could you know potentially translate into you know more engagement and you know having those you know paying attention to those users because you know that you know they're actually you know more qualified leads or engagement than you know some of the other customers that may not want to opt into as many things the other thing to consider in this from a design pattern perspective is that making sure that users actually understand what they're opting into so from a consent management perspective UI is is really important right you want to make sure that whatever you are providing your users that it's something that isn't you know cumbersome that it isn't you know something that's overwhelming for them that you sort of try and simplify it as much as you can so that they understand you know what it is that they're that they're opting into and this is key to you know a successful you know consent management system another design pattern that we found is that you know you want to model your consent data close to your customer data if you think about for example a healthcare example right we need to know if James consented for this application to share her data maybe it's a life-threatening situation right so you know you really have to model your consent data close to your customer data the other assumption and that we found in kind of designing consent is that you we return the result of the consent as adjacent object but can we make that assumption that you know all applications can consume the JSON object what what do you do for legacy applications right I kind of liken this to the whole idea of authentication in the sense that you can ask authentication system if you know if I give you a username and password you just tell me yes or no did I pass that right or do I give you similar to a sam'l assertion do I give you more data and do I add more attributes to that response the rather than just saying yes this users authenticated you also want to try to take into consideration you know the principle of least privilege so what you know minimum amount of metadata is needed for the application to make decisions and again I'd be nice for that for there to be ability to export the consent data if need to be for applications to consume from an architectural perspective you'll notice that the way we've modeled this in the field is that we have the user data and to consent data so that's serve our data layer and then there has to be a governance layer on top of that that enforces that consent that we talked about and then the interaction between the applications you know is again through the use of a JSON object but again there's a consideration of will do the applications to just need a yes or no or do they actually need more metadata the other interesting thing is from a complexity perspective the number of parties that are involved in your consent management actually dictates how complex your system is going to be I I'm just gonna skip to the four party consent so this is the scenario let's say that you know my husband passed away and I his wife need to be able to access his 401 K but I'm using Google as my identity provider which is logging into let's say Wells Fargo and Wells Fargo is contouring that contracting that out to John Edwards right so there's four parties that are involved in order for me as the wife to get to the John Edward you know 401k and what's interesting about this and I don't know that this is something that we've considered as identity management professionals is how you know from a proofing perspective what do we do about proving people's relationships right how do I know that what do we do as part of this process to prove that you know I'm really the wife or somebody's my attorney or somebody is my you know my legal agent or somebody's my legal guardian how do we model that from a practical perspective so there's definitely an interesting question there and consents I'll just skip to a couple slides here so you'll notice here is an example schema that we came up with for consent delegation so at the top part we're adding a flag on the consent object itself that says hey are we allowing this content to be delegated yes or no presuming I'm sort of making the assumption that the delegated user is residing within the same identity provider but you know here we're adding the ID for the actual delegated user but obviously you know it can be really complex quickly depending on the number of parties that you have in your consent management system this diagram I am also very fun of this because this kind of shows that the more fine-grained your consents are that dictates you know how easy your user interface is gonna be for from a design perspective but at the same time you know that you're providing better privacy controls you know providing the fine-grained consents so it's finding that sort of nice balance in the middle where you know the user interface is pretty easy to understand but you're still providing enough privacy controls for your users yes and just making sure from a logging perspective that you there's a question of when you when you were in your revoke consents you know do you remove that row or do you actually just add a new entry that says hey we just revoke this but not actually delete it from your data and last slide design pattern takeaways consent is its own object type you know separate your meta data objects from your consent records provide a easy-to-understand UI for users to manage consent and force your opt in opt outs typically there's a governance layer as part of that implement your consent data close to your user data and again the more parties that you have in your consent the more complex it gets and just making sure that you're aware of your auditing requirements and with that I am gonna open the floor for any questions yes yes so you mentioned jacquimo in one of the slides do you also model a model your consent requirements as policies yeah and okay and how do you what's the communication between the PDP m i'm assuming the PDP decides okay is consent required or not do you have like a consent decision on top of the authorization decision that you're returning but what it does is when it pulls these are information right the sample policies on that governance layer and so we can specify and then it has a connection out to like i know and then when a request goes in we can map out to a Vacaville policy on our governance layer site that says if climate is this that this is the type of data that we should be so the governance layer and the data layer actually very tightly coupled okay so there is no separation of a decision engine and an enforce or they're basically the same thing for for consent okay okay make sure Phillip has is thanks for me [Applause]
Show moreFrequently asked questions
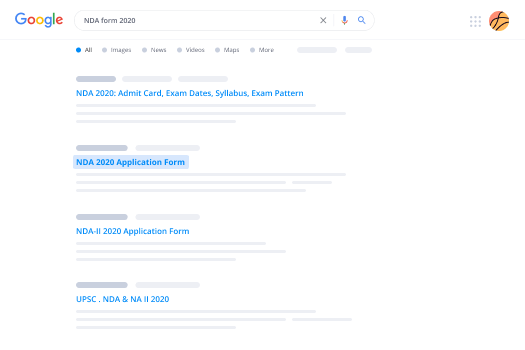
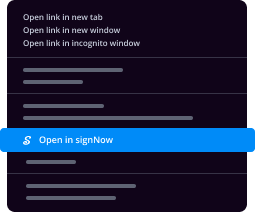
How do I add an electronic signature to a PDF in Google Chrome?
What do I need to sign a PDF file?
How do I create a PDF for someone to sign?
Get more for consent time field with airSlate SignNow
- Drawn sign
- Prove electronically signed Revocation of Power of Attorney
- Endorse digisign Mobile app Development Proposal Template
- Authorize electronically sign Intellectual Property Assignment Agreement Template
- Anneal mark Letter of Recommendation for Student
- Justify esign Simple Invoice
- Try countersign Affidavit of Title
- Add Security Agreement signature
- Send Sales Contract Template email signature
- Fax Letter of Recommendation for Scholarship signatory
- Seal Event Press Release electronically signed
- Password Event Sponsorship Proposal Template byline
- Pass Construction Contract Agreement esigning
- Renew Time and Materials Contract signature block
- Test Delivery Receipt signature service
- Require Construction Proposal and Agreement Template countersign
- Print beneficiary esign
- Champion person digi-sign
- Call for client signed
- Void Affiliate Agreement template countersignature
- Adopt Earn Out Agreement template digital signature
- Vouch Travel Information template electronically signed
- Establish Massage Gift Certificate template digi-sign
- Clear Consulting Contract Template template esign
- Complete Freelance Web Development Request template signature block
- Force Network Installation Proposal template initial
- Permit Video Release Consent Letter template signature
- Customize Leave of Absence Agreement template email signature