Countersign on Mobile Made Easy
Improve your document workflow with airSlate SignNow
Flexible eSignature workflows
Instant visibility into document status
Easy and fast integration set up
Countersign on mobile on any device
Advanced Audit Trail
Strict security requirements
See airSlate SignNow eSignatures in action
airSlate SignNow solutions for better efficiency
Our user reviews speak for themselves






Why choose airSlate SignNow
-
Free 7-day trial. Choose the plan you need and try it risk-free.
-
Honest pricing for full-featured plans. airSlate SignNow offers subscription plans with no overages or hidden fees at renewal.
-
Enterprise-grade security. airSlate SignNow helps you comply with global security standards.

Your step-by-step guide — countersign on mobile
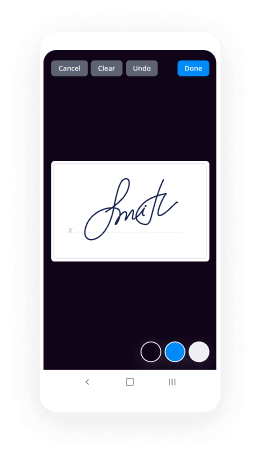
Using airSlate SignNow’s eSignature any organization can increase signature workflows and sign online in real-time, supplying a greater experience to customers and employees. Use countersign on mobile in a couple of easy steps. Our handheld mobile apps make operating on the run possible, even while off-line! Sign contracts from any place worldwide and complete deals in no time.
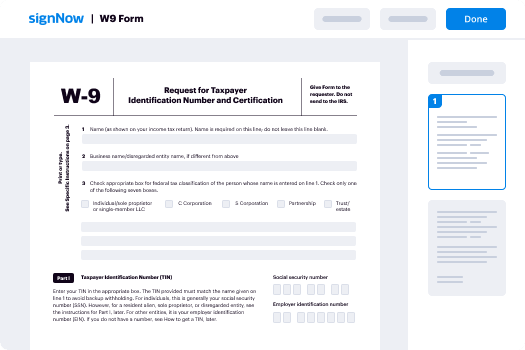
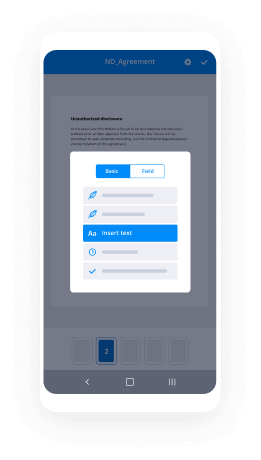
Follow the walk-through instruction for using countersign on mobile:
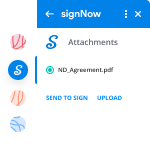
- Log on to your airSlate SignNow account.
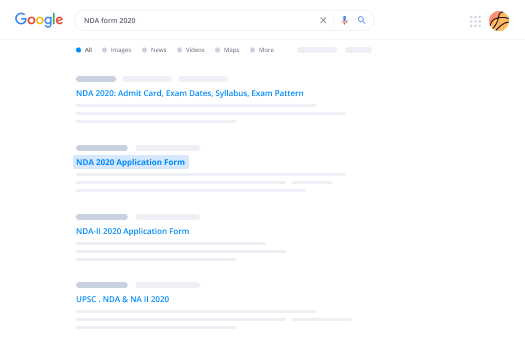
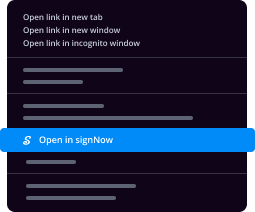
- Locate your document in your folders or upload a new one.
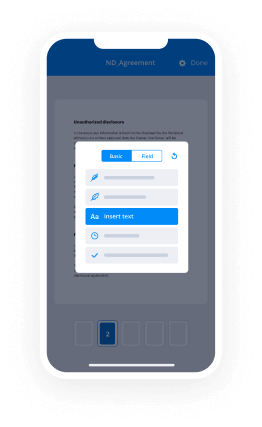
- Open the document and edit content using the Tools list.
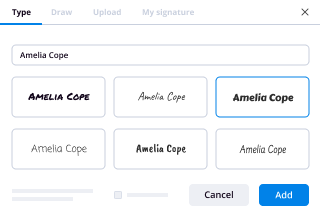
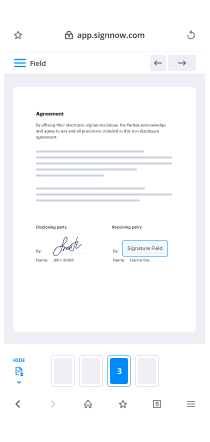
- Drop fillable fields, type textual content and sign it.
- List numerous signers via emails and set up the signing sequence.
- Specify which individuals will get an completed version.
- Use Advanced Options to restrict access to the template add an expiry date.
- Click Save and Close when done.
In addition, there are more advanced capabilities available for countersign on mobile. Include users to your shared digital workplace, view teams, and monitor collaboration. Numerous users across the US and Europe concur that a solution that brings people together in one unified enviroment, is the thing that enterprises need to keep workflows working effortlessly. The airSlate SignNow REST API enables you to integrate eSignatures into your application, internet site, CRM or cloud. Check out airSlate SignNow and get faster, easier and overall more efficient eSignature workflows!
How it works
airSlate SignNow features that users love
See exceptional results countersign on mobile made easy
Get legally-binding signatures now!
FAQs
-
What is countersign on transfer certificate?
countersignature of the Transfer Certificates from one CBSE affiliated school to another be done. away with, which has also been approved by the Governing Body of the Board at its meeting. held on 06.8.2014. Following steps should be adhered to by the Head of the Institution while. -
How do you countersign?
Suggested clip How to Countersign the Application Form and Photo - YouTubeYouTubeStart of suggested clipEnd of suggested clip How to Countersign the Application Form and Photo - YouTube -
How do you countersign a contract?
To countersign, head into the job or lead and under contract click the arrow down and then OPEN. This will open the contract in a sign-able tab where you can countersign it. -
How do you countersign a passport photo?
He or she must write the following on the reverse of one of the two photographs you have. 'I airSlate SignNow that this is a true likeness of [title and full name of adult or child who is getting the passport]. ' They must then sign and date the photo underneath the statement. -
How do you countersign a PDF?
Open your PDF document. Switch to Edit Mode by selecting the Edit icon in the toolbar. Click the Signature icon . In the Sign PDF dialog box, choose to Include "X" or to Include Sign Line. -
Do you need someone to countersign passport?
You'll need to get someone else to sign your application form and passport photo if you need the following: First adult passport; First child passport; ... Renewal of a passport if your appearance has changed and you can't be recognised from your existing passport. -
How do you countersign a document?
A countersignature is undertaken to airSlate SignNow that the action or provisions in the document have been approved by both the signer and the other party in question. When two parties sign a contract, the first party will sign, then the second party will countersign to confirm their agreement with the contract. -
What is a countersign contract?
Countersign (legal) From Wikipedia, the free encyclopedia. Countersigning means writing a second signature onto a document. For example, a contract or other official document signed by the representative of a company may be countersigned by his supervisor to verify the authority of the representative. -
Can my manager countersign my passport?
Yes a store manager can countersign your passport. There is a long list of people who can countersign your passport application. Main thing is they are a person of good standing in the community, so any professional, a manager, your boss, NHS worker, policeman or fireman. -
How do you sign an agreement?
Make Sure the Contract You're Signing Is the Contract You Agreed to Sign. ... Date the Contract. ... Make Sure Both Parties Sign the Contract. ... Make Sure Any Last Minute Changes to the Contract Are Initialed. ... The Parties Must Sign the Contract in Their Correct Capacity. ... Make Sure the Other Party Has Authority to Sign the Contract. -
How do you write a countersign letter?
Understanding Countersignatures The first party reads the document and signs it if they agree to the terms of the agreement, the second party then countersigns the document by providing their signature confirming their agreement with the terms of the contract. -
Can you sign a document on your phone?
Here's how to sign digital documents with airSlate SignNow: Step 1: Download and install the Android or iOS version of the airSlate SignNow app onto your mobile device. Step 2: Launch airSlate SignNow and tap the document icon to open a document. Step 3: Choose to import a document from e-mail, Dropbox, or take a photo of a document. -
Who can countersign a passport photo?
Who can countersign a passport form? ... They must have known the person applying (or the adult who signed the form if the passport is for a child under 16) for at least 2 years. They must be able to identify the person applying such as being a friend, neighbour or colleague (not just someone who knows them professionally) -
How can I create a signature?
Suggested clip How to design your own amazing signature - YouTubeYouTubeStart of suggested clipEnd of suggested clip How to design your own amazing signature - YouTube -
Do you need to sign your passport?
The passport must contain a signature to be valid for travel, customers should sign their passport as soon as they receive it. Customers will need to sign above the pre-printed line above the page which shows their personal details such as their name and date of birth.
What active users are saying — countersign on mobile
Countersign on mobile
welcome everyone thanks for coming yeah this is a talk on secure mobile with mobile device management my name is Mike Hatfield and I'm lead engineer of the mobile team at alfresco we have three mobile groups at alfresco we do we have a team writing iOS applications we have an Android him can deliver them and one of the apps we delivered earlier in the year was alfresco for good which is in the app store now and that's our solution for mobile device management and i'll be talking a little bit more about that and showing a demo of that later on first i wanted to cover security overview of mobile in general and how problems are starting to arise in the enterprise talk a little bit about BYOD and what is MDM and then move on to good technology and alfresco solution so those of you with phones and I'm guessing it's everyone in this room know that there's various options for securing the mouth of the box ranging from four digit pins to swipe patterns on Android complex passwords and obviously more recently and in the news quite a lot fingerprint access and these are great to a certain extent they tend to stop the casual hacker they'll probably give you enough time if you lose your device to change passwords and things like that but they're not an enterprise solution to security the other common thing you're finding all the app stores are apps that have locks themselves so there'll be a custom user interface ranging from copying the devices pin entry code to passwords to swipe entries these without fail give you a false sense of security and I'll go into a little bit more detail about that in a couple of minutes there are very simple ways of hacking these apps so please don't put any confidential information into them the other problem with mobile phones is that they used an awful lot for password resets and for your personal device for two-factor authentication if you lose the phone often it's a scramble to reset all your passwords before someone gets hold of it and does that for you or uses the device to authorize a two-factor authentication do it themselves so this is another problem that mobile vendors are having at the moment and it hits enterprises when people leave iPads on aeroplanes phones in taxis you name it so just thinking about the these apps that offer secret photo storage store your passwords and credit cards and just to be clear I'm not talking about apps like 1password and keep pass here that are very professionally developed and have proper security teams behind them these are the one man in his bedroom apps very much build as secure storage store your dodgy photos so that if your wife gets your phones you can't see them kind of thing that's fine to a certain extent depending on your models and often they go to huge lens to add fake security user interfaces to the begin to the front of these apps there's one I found that has a mimics the Android swipe interface and if you get it wrong it will take a photo using the front facing camera and log where you are and who you are the idea being you can go in and see who's trying to break into your phone all very nice as a technical solution all very useless there's an app called phone view there are other apps out there I think there's one called I explore and there's some windows variations and what it lets you do is quite legitimately go in and browse a mobile devices file system so you can go in even non jailbroken devices you can go in and look inside the sandboxes of apps and it's legitimate in that you can use it to back up photos back up messages emails and back up those sand boxes but it's also a great hacking tool because people assume that the data is safe especially in these these apps from the App Store so all you need is a hacking tool that's actually provided with every mobile phone that comes out the shop and there it is that's your hacking tool once you've got phone view I tested all 14 I think there's 14 14 of these apps from the App Store so that you don't have to and I put photos into them and went through all the password sequences and the secure storage and everything else connected them to phone of you and without fail every single one of them I could pull those photos off no problem at all there's no encryption within those apps whatsoever so the security is very much very very thin layer of UI on top there's no security in that at whatsoever that was more of a don't trust this app don't think that that's a quick solution let's think about a typical enterprise and it's may reflect where your company looks like certainly reflects what our company looks like what tends to happen is that a security guy will arrive IT guy and he'll build his Network and make sure that all the desktops are locked down and the servers are all well inside the firewall and no one can get in from the outside so he does some penetration testing they can't get in he's happy so he goes away and he lets the users in and the users are happy because they're inside the firewall they can go there office documents a nice and secure on the servers their desktops are locked down everyone's happy this was true up until a few years ago when this happened BYOD or bring your own device all of a sudden people have got hugely powerful computers connected computer is in their pockets and they're walking around your firewall with them and often the devices will be allowed onto your networks through one way or another whether it's USB cable into the laptop whether it's access to the Wi-Fi networks or through an SD card and this is a real problem for security and enterprise and people are just starting to realize that it needs a proper solution so it's slightly unfair to pick out dropbox because it is a is a very useful app in its place but there is what we like to call the Dropbox problem and the Dropbox problem is this you've got your enterprise with the lockdown desktop servers desktops and servers and your users are all suddenly buying these shiny new mobile phones and bringing them into the office and connecting them to your Wi-Fi and often they'll beat down the IT guy so you can get connected because they might be mobile and it's just easier to work that way and they can have their documents on the road the problem is they then install apps like Dropbox Dropbox gives you very very easy ways of sharing documents to anyone and anyone whether they've got dropbox or not whether they're inside your enterprise or not i'm sure most people here probably heard of if not installed dropbox and you may even use it daily how many secure documents do you put in dropbox looks at every chunk it chunks the content and it reads the content of every single document that gets uploaded so that they can do they can reduce the amount of storage they need they do data deduplication on your confidential documents to say no and here's the problem as soon as the documents go on to the mobile and to the mobile devices they're not in your enterprise anymore they're in dropbox e servers and this is the dropbox problem you've lost control of your confidential documents suddenly they're out in the cloud and all your security is now dependent on how secure drop boxes and I'm not I'm not going to judge whether they're secure or not I'm sure they've got some very good security teams but the point is it's not in your control anymore so this creates a couple of risks first risk is uncontrolled copies let's say you have an employee they want to get a document it might be confidential medical documents to a hospital they think what's the easiest way of doing this well I'm not allowed to email them because I sort of frowned upon but hey look I can I've got access to dropbox so I'm going to talk to the medical team and they've got access to dropbox as well so here oh I secure documents and we can just share them over Dropbox the problem is that copy at the top that remains in the dropbox servers and anecdotal evidence would stay there it remains there even if you manually delete it for this deduplication effort that they do so here's your business risk number one is that you've got uncontrolled copies of your confidential documents floating around in the internet and the cloud the other problem is loss of ownership so the link between your confidential documents in this situation is between the user and their device and Dropbox your IT security teams are nowhere in that link the problem comes when this guy turns up I don't know if this works in your work in the UK I need to swap it for America so suddenly this guy's been fired you can consider his device to be rogue he's gone out the building he owns the device he owns the dropbox accounts he's got ownership of your documents and you haven't a huge business risk that you've lost ownership for those documents it's all very negative I don't mean it to be it's kind of pointing out the risks let's talk about MDM MDM is mobile device management and their aims to help with data control and protection and thereby reducing also reduces support costs and also reduce business risks the data control and protection that's done by centralizing access to the content within the MDM system on the app so if your device gets lost if your user gets fired centrally you can disable access to all that content this would also reduce support costs because you can provision those users remotely as well so you can provision and support your users remotely through these MDM technologies you can set which servers they want to talk to you can limit their access to those servers and you're also reducing business risks by doing that because you can immediately cut off access to your confidential content when that device or user is compromised various MDM vendors out there and we've been talking to all of them some of the bigger ones a good technology Symantec obviously well known for their desktop antivirus software Citrix and MobileIron and they all attack all the MDM problem in slightly different ways and they've all got their own proprietary ecosystems that enable data to flow between apps securely and talk securely back to your servers and whereas there are some standards for MDM guess what they don't follow them they're all proprietary having said that that also does mean you're not limited to using just one if there's certain apps or services on one vendor and you need some services on another vendor as far as I know they will sit very happily together on the same device and they'll be separated from each other and still remain secure the approaches these companies take are also very very different good technology going at a very very low level in your application and take control of all your data and all your networking MobileIron are more of an optional component so you can actually wear as it's not possible to ship a nap on the good platform without saying you must use good technology with this app you can do that for mobile I on the mobile line code in your app remains dormant until it finds another MobileIron app on your device so there's some very different ways that people have come to solve these problems let's talk a bit more about good technology so good technology have a lot of rules that we must follow as app developers and app vendors all data must be encrypted now they enforce this by I said getting into your app at a very low level and they will they'll enforce that any networking goes over their code and their servers and any data is stored in their secure system on the device the advantage of any of networking going through good servers is that you don't need any inbound firewall rules for your mobile users this is something that we've configured for our own access we use alfresco for good on their own devices and we have a 4.2 server alfresco server internally at al fresco that normally you need to access a VPN you need to be on a VPN to access it nine times out of ten you launch the app and you forget if you're using the none MDM version of the apps you have to come out connect the VPN go back in with the good technology solution the desert proxy server that talks to good that allows these mobile devices to come in once they've been authenticated and to check that they haven't been locked out and they can talk directly to our internal servers there's no way of accessing the of accessing our internal server of the internet except via this secure good system and no firewall rules were required for that in fact the proxy server that we have set up doesn't even have an Internet address good also determines that you must follow best practices and this is very much to combat against this the phone view at problem that I talked about earlier so no temporary files which actually calls this a bit of a problem during the development of our out because there are certain certain features of iOS that generate temporary files themselves and we work together with good to make sure that they were cleaned up as soon as possible so the time that you could possibly access those was so minimal that it was unfeasible for them to be to be a problem no keychain access this was an interesting one if you jailbreak your iphone meaning you can run apps that aren't on the App Store and you have much wider access the keychain suddenly becomes unsecure the keychain is where your passwords and usernames are stored for services there's a key k'naan on max as well and it's whenever something prompts to save your password that's where it goes if you jailbreak a phone you can get hold of that keychain copy it onto a desktop PC and run cracking tools on it and it's anecdotally not that secure I'm not a security expert so I don't know but I believe its it falls over fairly quickly the other thing good mandate is that no data must be sent to third-party apps as a little asterisk by this so it's two caveats the first one is no third party apps and less they're inside the good ecosystem themselves and what that means is if you look on the app store for an app like so like the alfresco out like a good reader smart office they're often two versions on there there's a paid full version except alfresco so we don't charge you and there's a free version with a little good padlock symbol on it and the difference is the you need to approach good and provision that app for your users if it's got the little padlock that means that those apps on your device because they all sit on the good SDK they can talk securely to each other so that no point is your content unencrypted as it's going between the apps it's very secure way of providing services like PDF annotation we don't need to develop that in the alfresco for good app because we can allow good reader to open a document annotate it and send it back securely and there's no chance of that document being compromised the other thing good technology mandate is that all code must be audited by an external security company called Vera code and we had to go through this process a number of times through the development of the app in the end what we've we've got is the iOS SDK 1.1 and objective-c missed that the SDK uses have passed some very very stringent security checks on the code so we were very pleased to to have that against the code what it means is you're not leaking temporary files you're not storing passwords somewhere you're not doing stuff in clear text so it's a good validation anyway as well as being required by good technology so our fresco for good this is the icon you need to look for any app store so we we conform to all the things that good needs with a secure connection so we can connect in without VPNs secure storage everything is in a secure encrypted blob in the sandbox you can't pull those files off and policy enforcement which means that our IT department can prevent an ipad on iphone from accessing that content if it's been left in an airplane seat or it's falling out of your pocket or an employee's left through whatever circumstances I'm going to give you a quick demo because there are certain parts to this that require internet access and everything else and it's the the actual management is inside our firewall I've done this five videos it's also some of these processes a bit slow so I've sped it up a bit the first stage is provisioning a user this is good is very enterprise-e hitting in kind of a good in a bad way the app that web app isn't going to win any awards for for looking night or ease of use but this is your management interface what I'll do is expand that and what i'm doing here is for my user I'm provisioning an app for me what that does is that's talking back to the good servers and it's asking for secure key and there it is ending in 7 j 2 and the system has will email me that and say here you go here's a provisioning key you can install any of the apps you like as long as your company has provisioned them so you need to approach good and have an agreement with them about which apps you can use and that's the financial part that's why the apps are free in the App Store because you have a financial agreement with good instead of Apple Apple kind of tolerate this really short I think about two so that provisioning ki will then let me as a user provision an app on an iOS device and it's a one time use key so I get an email and then I have to type that number into the login box and I certainly didn't intend to do that live so I recorded it earlier and it looks a little bit like this so I launch the app and this is the first thing you see is set up you need to enter email address I'm entering the code I'm not that good at I pity sped up about three times by the way and then it goes through a whole load of activation process to make sure that I can actually use that my profiler said that I need to set a password we've done down the rules for our internal demo and then I'm into the app and I've already been provisioned with a server so let me just pause that a second my policy that my IT admin had set up in the good provisioning portal determined which alfresco server I can connect to so I haven't had to type in HTTP TS alfresco com think worry about port numbers worry about contexts all I know is I've got a server called summit demo server and that's what I'm connected to that's what I need an email address and username and password for and that's what I'm logging into here mom and then we're in a normal share instance and this is the alfresco for good app it looks an awful lot like the 10 out that was a deliberate decision we can reuse the assets and that's familiar to people who are familiar with the nun secured app and you can see it's just normal browsing we do have the addition of thumbnails in this version I can access content as I normally would but here's the difference if I try to send that highly secure content somewhere else to an app that's not in the good ecosystem I get this problem I get action not available your security policy only allows you to send documents to other good dynamics apps that's a policy decision that my IT admin has made and that was me trying to send that photo to iPhoto and that would have been leaving the good dynamics ecosystem and losing control of that document so the app prevents you from doing that but is it secure well I did the same test on our app that I did with those other apps from the App Store so this is phone view and what I'm doing is I'm going into the apps folder finding alfresco for good and then just having a browse around in the usual areas so there's nothing in the documents folder but there's lots of other folders around including some interesting-looking containers and things with good names and everything else but no where are those raw PNG's or JPEGs that I could find with the other apps very very quickly but because I know iOS one thing I do know is that it stores a snapshot when you background the app so I'm going to pull that off to look for confidential information and we cover that case too is back yet so whenever you background this app and this is something for those of you who are using iOS 7 will notice with the new task switcher you get the icons across the bottom and screenshots of the app if we did just back rounded the app you might have some very confidential information on there and iOS or automatically screenshots that and you're very easily to pull that off as just a picture and there you go so we put a security cover over that when we detect the app is about to be snapshot it so how do we help with lost management well so this is the interface that the IT admin gets and you can see that so this is the the ipad I just registered and I have some actions against it one of those is I can see the history of that device so i can see the compliance was enforced i can prevent jailbroken devices from even having this app running so compliance was enforced that was all fine the application policy that's the one that tells me which I'll Frisco server to use that was all fine and security was enforced so there's not been anything strange going on there so we've got security auditing as well through the system now let's say I left this down in the bar at hotel left his iPad I'll call my IT guy and say don't know where my iPad is please lock the device please lock the the app so go in here and lock it and then very shortly afterwards even if the apps live the good system will send a message that will lock out the app you cannot get in you cannot all the keys to that secure storage are also been revoked at this point so you cannot even get into the content that was in there before and again that's a policy decision you can choose to not have that but basically the only way of getting into this out and getting that content now is to talk to the admin and saying I have the device physically in my control give me a new key to get in that's in DM I'm going to hand over now to Peter he's going to talk about some solutions they've got for android I'll take questions at the end if you don't mind solving our don't to eat too much into into Peter's time thank you thank you Mike good afternoon my name is Peter culero and I'm a solution architect from an assault so lakiya and I should be standing here with mr. Thomas facil with a project manager from settle I'm but unfortunately couldn't make it today so I few of these few of his notes to read off of first let me start with obligatory words about the companies involved so talents Lakhia is a BNP Paribas personal finance company operating in a Slovak market of 5 million people for the last 13 years and today they have delivered about 1.2 million personal loans mostly in cooperation with the retail partners such as ikea it employs about 200 employees in there too to log to local offices and each year it brings and archives about 1.6 million sheets of paper which is roughly equivalent to 23 s anna soft is a system integrator and a software development house specializing in deployment of highly secure and customized solutions for banking manufacturing logistics and public sectors for the last five years an assault has been focusing on implementation of papers document systems within these sectors and thus it was tasked by settlin to deploy document management and later assign project both of these projects were set alarms answer to global BNP Paribas initiative simple and efficient initiative which is part of the business plan for BNP Paribas for the next three years the goal of the initiative to improve operating efficiency and simplified the way BMP group functions the initiative set forth by the headquarters in France targeted reduction of internal costs and inefficiencies and settlin has located their number one in efficiency to be within their case management back of his process and the root of the problem within the process is of course paper lots of it actually about one ton of paper in personal personal finance contracts that gets printed and archived in settling Slovakia each year to be more specific the problem was really a set of multiple issues all associated with paper number one problem was that the complete customer files were getting lost or damaged usually on some messy desk or during transfer to another office and the loss of the files was costing company money in unrecovered loans the number two problem was that slow document routing of paper was causing too long to too long go over processing the loan approval for further retail partners so the retail partners really sold the money after they saw the goods about five days later and last but not least handling of paper documents was costing a lot of money on contract printing postage and archiving so how did we go about the solution we started of course with alfresco repository we proposed digital document workflow in the most intensive back-office process of case management case management routing meaning that most of the person alone cases were to be scanned at our some metadata to and an extorting of fresco the case management process was implemented as a set of rules and workflows and it took about 12 months from the beginning of the project when certain decided to start including analysis installation integration to the settle on legacy systems and we had offers go up and running we also had to build a custom document capture to scan existing case a customer dossiers into the system and this was mostly due to the reasons of maximal optimization to basically save few clicks which made a big difference when you have to scan tens of thousands of files or those years so with our fresco and scanning stations up and running we checked off the first two major problems personal own folders were now being routed between back office in digital form only while expenses associated with with lost and damaged files were eliminated also the process became a lot more auditable and not so slow anymore unfortunately paper documents were still being printed in the form of long contracts for n consumers to feel and sign in other words problems with printing and mailing and archiving remained and not only that but we actually added slew of issues associated with scanning all of these problems and bottlenecks early state around solely for the purpose of signing a document and maybe feeling a few checkboxes on so this is really not that simple and efficient yet so our solution part 2 tablets only one year after alfresco enterprise has been deployed between settlin handwritten electronic signature project design started with the goal to dematerialize those paper contracts and forms the goal of ECM project was to give customers an option to sign personal loan electronically at the point of sale and just as we hoped but ninety percent of consumers prefer this option to the old ways and this adoption cleared away for implementing the getting rid of paper with in the case management process Easton project had few but very important business requirements most of them came from legal department and IT department if legal department it not requirement number one was to was for customers to sign what they see meaning they didn't want customers to sign document that retail person is looking at but rather what they're looking at also they wanted them to be still able to disagree with paragraphs within the contract this meant really that the signing experience had to be as false as closely possible as to the original paper form I did IT department had two major requirements and those were don't touch retail pcs meaning we didn't have to we could not install any software or hardware with in retail partners and this was all so this would be nightmare from a maintenance point of view where you have to manage some kind of a software on an unmanaged environment also they didn't want any more servers within their server rooms so standard document signing solutions we're out of questions and of course the whole solution had to be enterprise-grade secure so how do we build such a self-contained black box solution that would have to meet all those set of requirements simple like this now even the goal of even though the goal of the settle and Eastern project was just to build a signing solutions signing electronic document arm and the application had to be really very simple to use by the end users required no training this was really no easy task and it required merging a lot of different new technologies together so we started with android samsung based android tablets with a pen at special and enabled layer just refer to as I spin and of course we had to use a fresco mobile sdk for all the CMS connectivity to office capacitor II we use multiple Samsung SDKs some supporting S Pen some security features and we also used our partners softpro sign doc SDK to provide support for biometric signature that we need it and last but not least we used our own honest of signatures SDK which merges all these technologies together and makes working with complicated technology a little bit simpler and now this SDK is actually a part of our solution that we can offer to partners that would like to implement similar solutions so this was our a complete solution it included alfresco enterprise with the workflow processes in the repository and project assign the solution how dematerialized the forms but it wasn't quite complete and the missing part is really not the angry birds here after the settlin has decided that they would own and manage all the tablets provided to the retail partners they did not want any third-party software running and definitely not angry birds on the tablets so this business requirement really meant only one thing and that's mobile device management after deployment of al fresco and development of mobile application allowing biometric handwritten signature of digital documents we have deployed our samsung only mobile device management which we have used for other projects and even though our MDM is definitely not feature is equivalent to generic ambien solutions we're only mostly focus on single-use devices where device such as this standard mass-produced device becomes one application only embedded device you've used for the bond application that we had this in this case it was assigned and get to the end where we actually managed to solve the problem using multiple technologies and settle em has this way optimize its most inefficient back-office process which was riddled with paper associated problems and meanwhile settle and retail partners are benefiting from much faster time to finance after they have sold the goods and last but not least consumers don't have to worry about filing at home yet another important piece of paper instead they have a permanent access to the original contract digital copy that I have signed it in Saddam's portal so getting rid of paper and moving towards through paperless office was a win-win-win solution for all of them the investment into a fresco and Eastern projects did not only lower paper associated costs it gave settlin real competitive advantage in the crowded personal finance market space and did i mention that settle on now saves every year small forest of 23s thanks to the documents that never have to be printed thank you and I didn't have time for any demo so in case somebody wants to see that sir telling live I can show them offline thanks and if anybody has any questions yeah just quick one with the the alfresco for good iOS app and if you take a normal screen shot will it also obscure it so if you take a screenshot of the app using the normal pressing of all the weird buttons and stuff okay it does that as well yeah I believe they can prevent that in iOS 7 I don't think I was sick printing from doing that and there's nothing stopping you're using a digital camera yeah taking a picture of the screen either so there a certain length you can you have to stop at ya okay thanks very much come in hi I'm are you wrestle from soccer ball I'm wondering if your company do the sorry if your company does not involve in to bring your own device which is the case of our company is there any interest of using the container for example provided by good i understand it could be useful for remote wipe and so on but for the sdk / to know that you may use into your own application is it useful what well as far as i understand them the sdk part of MDM solution is useful for your personal devices because you don't have to need VPN and so on but if you have a mobile phone with the parent certificate and so on nvm solution could be useful to manage use the devices of your employees but if you are building internal applications do you have any interest of using the sdk as well yes and so the moment we do we don't have the MDM solution in the SDK itself its application based solution and it works works in tandem with device wide MDM that samsung and google and apples they provide so there's lots and layers and it's all very much on a case-by-case basis as to what the best solution is and where that MDM solution goes and how when that sits in the sdk and not sure I answers your question completely and if you want to catch up afterwards are going to put in technical detail better for matter thank you I give
Show moreFrequently asked questions
How do I eSign a document before sending it?
What is the difference between an in-person signature and an electronic signature?
What counts as an electronic signature?
Get more for countersign on mobile made easy
- Print signature service Insuring Agreement
- Prove email signature Medical School Letter of Recommendation
- Endorse eSign DJ Invoice
- Authorize digital sign Purchase Order
- Anneal signatory blank
- Empower electronically signed Customer Product Setup Order
- Try digisign Wine Tasting Invitation
- Add Donation Agreement mark
- Send Sponsorship Proposal Template signed
- Fax Volunteer Certificate digi-sign
- Seal Pet Adoption Letter digital sign
- Password Consulting Agreement initial
- Pass Interior Design Contract Template signature
- Renew Pet Care Agreement countersignature
- Test Client Progress Report digital signature
- Require Exclusive Distribution Agreement Template electronically signed
- Send beholder signature service
- Accredit onlooker signature block
- Order petitioner esign
- Void Construction Quote Template template eSignature
- Adopt mnda template autograph
- Vouch Virginia Lease Agreement template digital sign
- Establish Software Proposal template signed electronically
- Clear Letter of Intent Template template electronically sign
- Complete Personal Medical History template countersignature
- Force Escrow Agreement Template template electronically signing
- Permit Vehicle Service Order template mark
- Customize Bartending Services Contract Template template signed