Digisign Event Satisfaction Survey Made Easy
Do more on the web with a globally-trusted eSignature platform
Remarkable signing experience
Reliable reporting and analytics
Mobile eSigning in person and remotely
Industry regulations and conformity
Digisign event satisfaction survey, quicker than ever
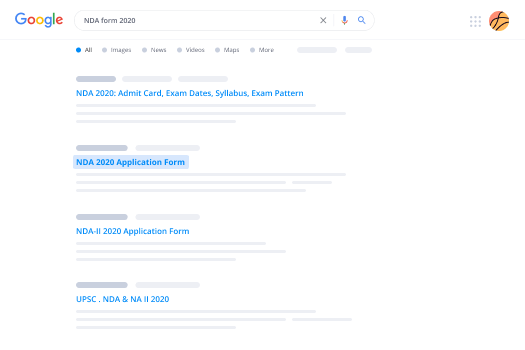
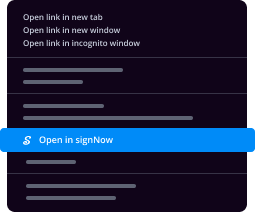
Helpful eSignature extensions
See airSlate SignNow eSignatures in action
airSlate SignNow solutions for better efficiency
Our user reviews speak for themselves






Why choose airSlate SignNow
-
Free 7-day trial. Choose the plan you need and try it risk-free.
-
Honest pricing for full-featured plans. airSlate SignNow offers subscription plans with no overages or hidden fees at renewal.
-
Enterprise-grade security. airSlate SignNow helps you comply with global security standards.

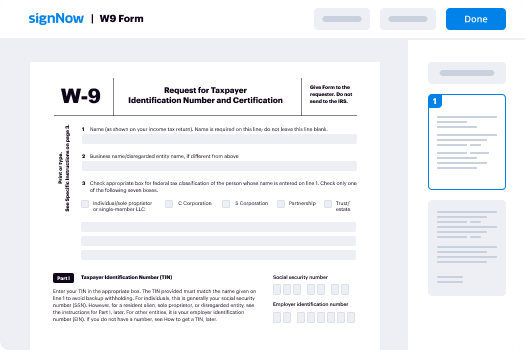
Your step-by-step guide — digisign event satisfaction survey
Using airSlate SignNow’s eSignature any organization can speed up signature workflows and eSign in real-time, giving a better experience to clients and workers. Use digsignNow Event Satisfaction Survey in a couple of simple actions. Our handheld mobile apps make work on the go possible, even while off the internet! Sign documents from any place worldwide and complete deals in no time.
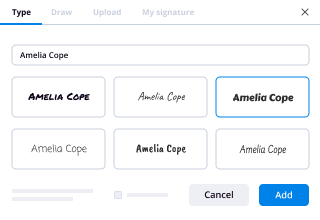
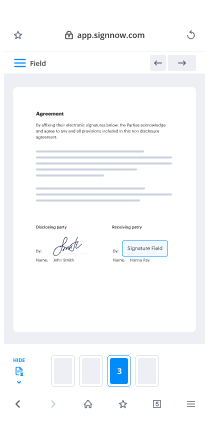
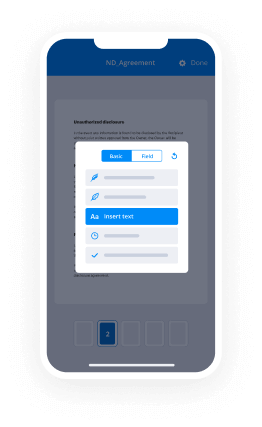
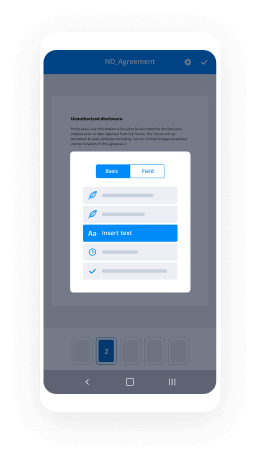
Take a step-by-step instruction for using digsignNow Event Satisfaction Survey:
- Log in to your airSlate SignNow profile.
- Find your needed form within your folders or import a new one.
- Open up the template and make edits using the Tools list.
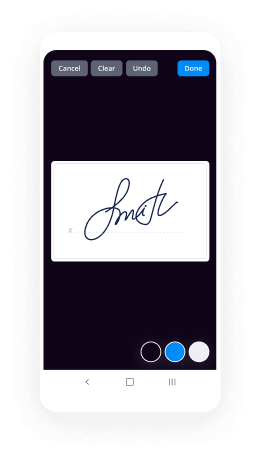
- Drag & drop fillable fields, type text and sign it.
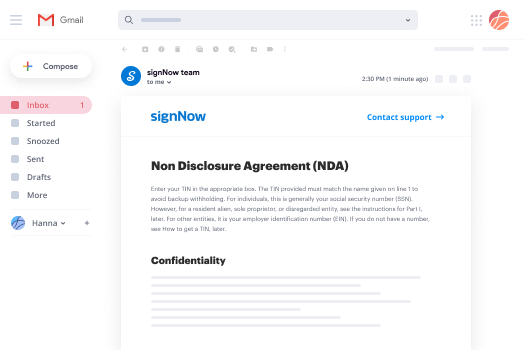
- List several signees by emails and set up the signing order.
- Indicate which users can get an signed version.
- Use Advanced Options to limit access to the document and set up an expiry date.
- Tap Save and Close when completed.
Furthermore, there are more innovative capabilities accessible for digsignNow Event Satisfaction Survey. List users to your collaborative work enviroment, view teams, and keep track of cooperation. Millions of consumers across the US and Europe concur that a solution that brings people together in one cohesive workspace, is what companies need to keep workflows functioning effortlessly. The airSlate SignNow REST API allows you to embed eSignatures into your app, internet site, CRM or cloud. Check out airSlate SignNow and enjoy quicker, easier and overall more efficient eSignature workflows!
How it works
airSlate SignNow features that users love
See exceptional results digisign Event Satisfaction Survey made easy
Get legally-binding signatures now!
FAQs
-
How do you create a post event survey?
Event survey tip #2: Keep it short. While you want to obtain feedback that's specific enough to be useful, you don't want to scare off respondents with too many questions. ... Event survey tip #3: Stick to multiple-choice answers. ... Event survey #4: Get to know your respondents. ... Event survey #5: Create a narrative. -
How do you collect data from an event?
11 Effective Data Collection Tools for Events. There are a number of data collection tools that helps organisations gather and analyse valuable information around their events. ... Registration Systems. ... Event Survey Systems. ... Event Management Software. ... Mobile Apps. ... Social Media Tools. ... On-Site Systems. ... Audience Engagement Tools. -
What is a Post survey?
Pre-Test and Post-Test Surveys are a common practice in the surveying world. In the Pre-Test survey baseline data is collected. Then, at a later date, the Post-Test survey collects follow-up information after some treatment has been applied. -
How do I send a Testmonkey survey?
Suggested clip SurveyMonkey - Creating, Testing, and Sending a Survey - YouTubeYouTubeStart of suggested clipEnd of suggested clip SurveyMonkey - Creating, Testing, and Sending a Survey - YouTube -
What is event evaluation survey?
Event Evaluation Survey. Organizing an event or developing a training program is very intensive. By collecting feedback before, during or after your activity, you are sure that the content meets the expectations or will do so in the future. ... You can even conduct the survey during the event with QR codes and kiosks. -
How do you ask for feedback on an event?
How should I ask for feedback? You can print out surveys and hand them out at your event, and make sure to collect them before your attendees leave. If you have the attendees' email addresses from registration, feel free to email them a survey and ask them to email it back to you by a certain date. -
How do you ask for event feedback?
Overall, how would you rate the event? ( ... Please rate the following aspects of the event: (Interval scale question from very unsatisfactory to very satisfactory) ... What did you like most about the event? ( ... What did you like least about the event? ( ... How do you think this event could have been improved? ( -
What is the best way to ask for feedback?
Different feedback models. Feedback can take many forms in organizations. ... Seek advice rather than feedback. Minimize using the word \u201cfeedback.\u201d The word carries a lot of baggage. ... Ask often for feedback. ... Make it easier for your boss to give you negative feedback. ... Make feedback a habit. -
How do you ask customers for feedback?
Value your customers time Approaching customers for feedback respecting their time makes the difference. Keep a note of certain things while obtaining feedback. Don't ask irrelevant questions \u2013 Keep your questions open ended to know what the customer thinks about your product or service.
What active users are saying — digisign event satisfaction survey
Related searches to digisign Event Satisfaction Survey made easy
Digisign executive summary template
okay so we're going to start so welcome everyone so thank you for joining us today um i am julia larson so i am senior business development manager at fatima technologies and let me introduce you william murray which is uh vice president of sales of versailles so hi william how are you hi i'm doing good happy to be here thanks for having me so yes so we will present you today uh the versus second feity and fido and pka technologies so please understand that it will be live demos on mobile and laptops so it will be live remotely so like we would do if we were at a trade show but as we all know it's uh it's difficult to travel right now so uh let's be uh be kind with us we did our best to show you how we can demo and how our keys are working together we are with our joint solutions so let's start with feitean introduction so i'm gonna just talk about infection and then william will just share about versus sec and we will start to join demos and faith and the most to end the webinar so please understand also that there will be a survey in the end and feel free to uh to answer it it helps us a lot to improve our products it's very important and also if you have any questions you have questions and answers that you can just click during the webinar and we'll be happy to answer and you can even contact us anytime because our contacts are in the end of this webinar so let's start so feitian who we are so we were founded in 1998 we have more than 1 000 employees currently we have more than 1 000 patents worldwide we have more than 2 000 customers worldwide we our team is composed of 500 r d engineers which is a lot but you can understand it with our portfolio and we deliver annually more than 80 million products so the briefest history of feitan we started with rocky software protection don't go then we moved to the epas pica identification dongles for digital signature then we blown the smart card based solutions then the one-time passwords two-factor authentication for online banking mainly then we launched the mobile version of this otp then we launched the mobile point of sales for mobile payments we got our initial public offering in 2014 we are now listed on the shenzhen stock exchange then we launched just before 2015 the fido u2f followed with otp card so it's a poor card concept that you can see how we developed it after we launched then the biometric uh way to integrate the biometry in our tokens and also on our cards like you can see on the fingerprint card in 2018 we launched the fido 2 passwordless security key based on the protocol of the file alliance then the dcvv card so you can see the different technologies one can also put in the card right now in this timeline some of our customers right here so to name a few we work with microsoft google apple symantec some car manufacturers like audi and toyota famous brands like adidas and of course banks such as unique credit gp morgan banco popolare other famous names rakuten seiko so these are just a few names and of course it is not our customers well way more so what is fido fido is based on free and open standards from the fido alliance so feltian is a board member of the file audience and we actively participate to uh the improvements of this protocol and it is supported right now with the biggest tech companies in the world and more and more are joining the movement so basically the fido is very convenient because you can just get the key from a b2c point of view and a b2b point of view and you can integrate it in i would say enterprise sphere environment and also you can associate it with a private sphere on your facebook or your gmail other services that are more b2c and you can do it by yourself so once you have the key you go to the security settings and you enroll the key by yourself and it's just the protocol that's going to link the key to your account so it means that there is no process in the middle by design with the fido protocol to implement it on your site which makes it very convenient for the deployment so why fido so we hear in the news every day the bridges that are occurring and they are even bigger and they are attacking even cyber tech companies and of course we don't know exactly how the hackers can reach such level of expertise but what we know right now is the the passwords and static passwords are key to the hackers to enter in organization or private sphere digital private spheres so you can see 81 of passwords are the root cause of data breaches and 90 plus average employees has more than 90 online accounts 1990 online accounts employees have that right now average 73 of passwords are reused and the average help desk labor cost for a single password reset is 70 usd and you can see the cost of the key can be way less than that there is 167 million daily mirror attacks so you can see all these numbers here they speak for themselves so the fido protocol enables you to not use any passwords i mean to bypass the password to replace the static passwords with the key meaning that you don't have to type and you avoid the keyloggers and the phishing attacks so this is extremely strong and extremely convenient so the benefits so you don't need to remember passwords no password resets works with most devices it's totally open standard and it's supported natively across browsers and platforms so you can see windows 10 android google chrome modzia microsoft apple safari right now so one key can be used for different apps websites and most otp options available on the market so if you use the biometry like we have in our portfolio it is used the biometrics are used in a hash as a hash on the secure element and it mitigates data breaches and you can see the biometry creates true passwordless login meaning that sometimes the key is associated to a pin but the pin is it's not password the pin is associated to the key the password is associated to the service online if you use a biometry you bypass the pin related to the key which makes the experience totally true passwordless and also if you lose the key the your parametry will be required to for the key to recognize you so if you lose the key it's less risky than not having the biometry so the common use case is office employees health care hospitals distribution centers stores education and on the road employees right now since we are more on the remote desktop and where most more and more more and more employees are working remotely having uh a zero trust let's say um a zero trust approach on security putting everybody on the same level of access of the information in the organization providing a key to every single employee strengthens the security so you can be a remote you can be at the enterprise the key would be required and it gives a lot of relief to the ctos to have this equipment so in a nutshell you can see here our product line is pretty complete you can see how broad it is so you can see the connectivity on the left you can see usb type a usb type c april lightning nfc bluetooth low energy fingerprint we have door access enabled products fido u2f protocol 502 we can add hotp totp piv for digital signature that will show you with ssh right after and also add some open pgp so you can see in a nutshell or our keys here they have a different pricing so you can see that the more complex they are of course the price is is increasing but it depends on every every value every data has different value in enterprise so if you have privileged accounts you will tend to give them a better key and for lower end data to be protected you can give them an entry price level key so this is what phaeton embraces here it's a very diverse portfolio with different connectivity and also pricing because face fatian is willing to provide the keys to the maximum people we are not in a niche market affected we've always been willing to provide such devices to to the masses and this is uh this is our strategy and you can see here how we embrace this strategy so now we let william introducing the fantastic solution so you can go ahead william let's go thanks thanks fellow genius was very instructive so welcome again everyone so as you can see my name is william murray i'm in charge of the worldwide sales for versus sec and as a part of my presentation today will be to explain how with our v6 cms we can unlock the pki capability of sufficient tokens and why we should do that so next please i will start by um introducing our our mission well universal second mission from the start has always been to help organizations of all sizes to better manage their digital identities and we do that by delivering a system to manage the secure two factors authentication device which enable our customer to increase the level of security of course by using strong authentication and we develop and sell our identity and access management system to enterprise and government organization next please so if we look a little bit at the history of first sex versus sec um as uh is a swedish company it has been funded in 2007 it's stockholm sweden um first we were focusing more on um providing specific development services uh in this smart card pki entity and access management field for for example in 2008 we delivered a secure mobile healthcare solution for the nhs in the uk so we were deeply involved in the deployment of of pki smart card secure device in general and all this project taught us that there was a need for a new type of credential management system so uh so based on the new standards that was available on the market at the time we decided to invest and to develop our own cms so we started developing it in 2009 the first version of the cms was released in 2011 the first sale of the cms came in 2012 and today we have been very successful because we have been we have more than 400 customers in more than 50 countries all over the world next please so the question is we saw the presentation from julia using fighter 2 with the fashion token which is great so why do we need pki why do we need to add pki on top of this the answer to this is that because pki is the only standard with the market which allows to unlock all the following use case it's not only about authentication it's not only about strong to factor authentication it is of course authentication for windows logon for secure remote access such as vpn and desktop services vdi but on top of this this is for website authentication also but on top of this we have access to digital signature so qualified signature thanks to the token or the car no please come back thanks to the token or the cards we have of course two factors authentication the token place a pin or the token plus your fingerprints so we have access to document signatures uh email signature and encryption and also file and disk encryption so with only one device you have access to all these use case which are supported by defaults by the operating system all the windows operating system and all the applications running into the system as soon as you can configure the application to use certificate based authentication then you have access to this next please and the role of the cms here is really to manage the authentication device for roots it's life cycle so let's let's take an example let's say that i'm joining company and the first thing uh the security officer will have to do for me is to issue a token or card a virtual smart card so he will have to assign it to me in my in my user directory he will have to encode the certificate to connect to the pki to make sure that in my card i will have the good certificate and related keys to perform the operation i'm supposed to perform maybe to print the card graphically if it is a physical smart card maybe to encode the physical access card so that i can use it for door access also assign a pin code will run holland and fingerprint and then i will be able to use my cards on a daily basis to again log into my domain encrypt my hard drive sign my email and so on and maybe after sometimes i will forget my pin code after some vacation and then when i go back i need to have a secure way to unlock it whether this is by handing it to the operator or whether this is by phoning the air desk or having a self-service portal in the same way maybe after some time my certificate will expire and i need also to have a secure way to renew them and maybe after a few years i will leave the company and the hr department will need to have a way to make sure that all my credentials are revoked and i cannot access the company content anymore so if you're on that kind of the high level non-exhaustive summary about the responsibilities of the cms is to make sure that the device is always in the state we want it to be and that all the systems that relies on the identities inside the device knows about this state next please and relieve this xcms streamlines all the aspects of the credential management by connecting easily to the full company's ecosystems to it will connect to the user directory whether this is ldap or active directory to the database server like a sql server to the mail server if for example you want to assign a random pin code to the device and to send this value to the end user by email or if you want to warn the end user that his device is about to expire and it needs to renew them event log for traceabilities so pki most of the time in the enterprise context microsoft certificate services is used but we also do support all the main pki providers of the market i mean prime key digisign go by sign very signed uni slots um interests nexus i mean the list goes on hsm also i mean by design we don't require an hsm but if there is an hsm which is already available to store the pki motor key then we can also rely on this hsn to store our master key our master key is used to diversify all the admin key or admin pin of all the cards to make sure that every single device has a unique i mean clean or admin pin and that only the cms with two factors authentication can calculate this value key archival so this is in the context of encryption um you know the the main value of secure apki device is that it has a microprocessor so the keys are generated by the device and the private key which is used for the signature will never leave the device so that it cannot be cloned with encryption we have to do a little bit differently because otherwise if you lose your card you cannot get access to your content anymore so that so what we do is that we generate the keys outside the device and we import them securely into the device and we keep an archive of the keys securely in our database encrypted that way if you lose your token or if you forget your token home we can issue a replacement token or a temporary one to you and you can still get access to your content operator interface user service interface so all the credentials so i said uh sometimes i say card because i'm used to say this but it's not only card obviously this is card this is secure usb token this is virtual smart card this is windows 04 business container all of these are can be treated as pki devices depending on what you want to achieve rsdm capabilities that's a remote security device management that centralized management of the device that's very convenient for virtual tokens credential providers that's allowing to load our user cell service capability from the login screen from the windows loading screen identity provider if you want to implement for your company user service then the main challenge you have is that okay how do i authenticate my user well we can delegate the authentication of the users to any authentication server which is compliant to open id connect so that he can authenticate the user for us and we can allow the user service operation physical access system if this is in the convert badge context and you want to use a smart card for both physical and logical access we can connect to the door access system to make sure that both systems are in sync photo captures them if you want to do a photo of the employee to print it into the cart afterwards so car printers to to finish of course to print the cards graphically with the layout you want but also in the same process to encode the pti part and the contactless parts rfid part for the access and because these printers have some loaders where you could put for example 100 cards in we have some advanced matchmaker capability where you can define an input file with a list of the users that need to have a device and you click execute and the cms will coordinate to issue all the cards next please and of course v6 cms has full support of all uh the fashion uh portfolio i mean all the fashion portfolios that support the pki capability this can be the k27 the k44 the f2000 the k40 the k26 the k9 and or the e-pass pki token and we support both the legacy e-pass 2003 pki app from fashion and the piv applied from fusion also next please so if i want to recap the main advantages of of the cms the first one is that the installation is very quick i mean if you stick to the standard use cage which is windows domain logo in the windows environment uh it really takes minutes of course if you want to do self service you want to enter into an hsm if you know you want to integrate with a specific pki of course it's a project but we have a very intuitive user interface to optimize the efficiencies uh we are the cms with the most wide number of device integrated with high level of security we are coming from security background with inverses a6 so security is definitely not an option for us our system is very scalable we don't have any limitation in term of number of devices we manage the system can be used to manage 50 device and to manage 500 000 device you just have to size your servers accordingly cost efficient especially for small volume we try to have a very attractive pricing model which means that we don't have an entry point fully integrated with multiple ecosystem like i explained uh earlier customizable unextendable i mean by default you can with the graphical interface of the cms you can customize the workflows um you we have also a set of api that can be used to also customize the workflows and in versus that we are not against doing customization also to make sure that we will meet customers requirement and the last point being migration paths from other cms we have the ability to migrate from from third-party cms such as microsoft meme for example to retrieve the database so that the customer can replace the old microsoft cms or other cms please do not hesitate to contact me for this with no done time and without user interaction with your operation thank you okay thank you william that was uh super clear and super complete thank you very much uh so now we enter the live demo part so this is a complete introduction slide here so we're gonna show you on uh a windows 10 surface uh android ios you can see our keys here with nfc lightning type c biometric bluetooth low energy with fingerprint sensor so we enter the demo part so we will start with the laptop side on windows we're going to introduce our k26 k9 k27 okay so this rear graphic card and we'll start with a versasec cms demo live demo so we're going to show you uh the domain join pc login we're going to show you the versus 6 cms certificate issuing then the pin unlock then a bit locker disk encryption so now our beijing team will show you the demonstration go ahead so okay so if you look at the efficient technology uh screen please now so please click on it if it does not come by default we will see how to log on uh to the workstation uh using uh the key26 token so and we will log on using both fingerprint and pin code so pretty easy we will just plug the token in enter the pin code swapping the fingerprints and we are in and now we are going to see on how we can use the user self self service capability of this xcms to unlock the pki capability of these tokens so please click on cjlo screen if it does not comes by default cj please share your screen we can see it i cannot okay so i cannot see it myself so we are following the issuing smart card process here so william is having a little issue okay so cj please comment yourself and if it's in only me which cannot see that's not a big issue but please comment yourself then hello okay okay now from this process actually you are looking at now exactly from the issuance part of the smart card that means at the end user part right once they have their faith in uh token with them they can plug it into the system and then they can do issuance uh of their own smart card so the process is pretty simple once the user self-service software like you've seen in front of you now is being installed user will be able to do the self issuance the uss will be contacting the server to get the certificate and everything will be injected into this um token now as you can see now at your screen user will once the token wednesday token already got all the certificate and the keys that's available they'll be they'll be requesting for user to key in their to set their own pin over here so i'm showing you over here you are actually the user is actually just doing this king in their own pin okay so once it or fulfill the pin policies that's been set by the token then you're good to go once everything is stick over here that means your fulfill the pin policy okay i can i can see the screen now so i can click and drag so yeah and in this case what is important to see that of course all the configuration has been done in the back end so in this case we have configured the tokens with additional keys and certificate to provide to do encryption but we could do it for all the use cases that i have shown earlier document signing mail sign email encryption in this case for this demo wanted to keep it short and we focused on encryption only so with the same v6 cms interface of course we can change the pin like cg is doing it here but we could also potentially unlock it with calling a help desk and doing a challenge response or with also an online mode by having an authentication with a third party system using open id connect like i explained so here we have done the pin change and we will be able to see the next step is com how we are going to use this token for this encryption in this case we choose to use bitlocker which is embedded by default with windows we could use any participle for party software as soon as these can use this can use smart card authentication it's pretty easy to configure in bitlocker you just say use my smart card to to access we have a file pro with a file for backup or pro to print or recovery key okay so now we are going to start the encryption and as you can see that's a very fast and easy process and that's it now our disk is protected by a smart smartcard authentication thanks to sufficient tokens which means that if i want to access to my disk i will have to insert my token and provide my pin code so this is something that we add on top of the 5.2 technology with the pki that can only be achieved by pki as i said it's not only encryption it could be document scenarios male signatures male encryptions i mean all these use cases that are supported using pki thank you okay thank you william thank you cj so that was it for the versa 6 cms demo with our keys so we go to the next step right now we're gonna show you uh so the biometric password let's microsoft windows login via usb type a with our k27 then we will show you the fingerprint enrollment on inclusive windows so you need the build 190303 and newest one to perform this on the windows 10 operating system then we'll show you the biometric password passwordless microsoft windows login with our fingerprint card through nfc and a contactless smart card reader so now i let our beijing team to do the demonstration so i invite you to click on the small camera to see a large screen so you can see our k27 which is the rpo pathfinder 2 k27 usb type a so with the fingerprint sensor so you can see how to how easy it is to log in on windows so you just insert the key the account recognizes the key and then you are required to put your fingerprint and you're just in you just you just logged in you didn't enter any any pain or anything just your fingerprint your key and your it's pretty comfortable and user friendly then for the fingerprint enrollment it's very easy you go to the settings windows you go to accounts then you go to sign-in options then you will have the options for your security key to manage it then you touch your security key to unlock it then you enter the pin so for the first utilization you usage of course you do that first time and then once you've done it you re-enter your fingerprint to manage the key then you put your fingerprints two to three times and you're all set so you have just unrolled a new fingerprint on your key and you can enroll until 10 fingerprints on each parametric key of phaeton so that was it you can see how fast it is it's all built in and there is nothing very technical about it everything is user friendly so now the next step will be to with a contactless card reader with our fingerprint card but you can see on the camera right now our r502cl contactless card reader as many enterprises have this such a setup they have also a contact card reader especially when you have used pki cards we can associate the 502 protocol with our fingerprint card since it's a gel card base we can add different applets of course so right now you just put your fingerprint on the card and the smart card reader will power the card that doesn't have any battery and power the card in the session so you can see the account recognizes the card and the card will recognize your fingerprint and by nfc contactless you will just log in this way so with this fingerprint card this fingerprint card can be used for payments of course uh fingerprint payments enabled cards and also physical access so this is very convenient for enterprises to have one product that that fits all now i'm just gonna re-share my screen we're gonna show you the next demo which is bluetooth low energy on windows so this is our k33 key here you can see it is a bluetooth low energy it has a nfc it has a tight female port dock it has a battery inside with this key you can recharge it two hours and you can perform four authentication a day four sessions for one month and a half uh only if you uh if you perform authentication through bluetooth because if you perform authentication through nfc or with usb cable you don't use the battery of the device so it's very durable and it's not it's not a device you have to recharge every day of course so now we'll let my beijing team do the demonstration here we go so now you want to open the session on windows you want to log in so you invite you to click on the camera again and you can see the key so you have to press a button for the bluetooth and the pairing to occur with your laptop okay so you can see the key is recognized invites you to put the fingerprint on it and you just log in so it works as is this is very fast there is no lagging it's very efficient so that was the bluetooth low energy experience on windows with rf10 keys i'm gonna share again and go to the next step so now we go to the mobile mobile section we will demo you under ios and android with a lightning border with a type c with nfc and also with bluetooth how to interact with your smartphones on the go with affiliate so we will start the live demo with our k44 which is ipass with lightning port dock and type c you can see that we're going to show you under a video hardware we say a google account signing so on apple ios with the lightning or topic so now i let my paging team to perform the demo okay so you can see the iphone so we share the screen of the iphone you can see what's going on in it i invite you to click on the camera to see so the k44 in hand you want to log in on google so you open your account you want to sign in you select the account you want to sign in you can have this password uh copied and paste or i would say automatically uh entered so you don't have to enter the password manually every time and then it invites you to insert the key because as on the security settings you have already registered yourself the key to your account now you just insert the key and you press the button and you perform the two-step verification that was very fast so this was the ios scenario under uh with a lightning bolt now i'm gonna show you the next step with android i have some slides about it just everything to be clear so now on android we're going to show you different ways it will be with the type c with our same key that you just saw which is our k44 then the k9 with the nfc nfc antenna of the k9 then with our k13 it will be the bluetooth low energy so it will be file hardware with effect authentication with a google account sign in now i let my aging team perform it's a demo here we go so you can see the screen again so you want to perform a login under google you select your account or sign in select your account so the password requires a key so you will be invited to insert the key in your android smartphone and then you will be invited to sign in by pressing the button so the fido concept works with the button press and also the proximity effect we see that with the nfc so it shows that you're physically present at the moment of the station and by design it it kills the phishing attacks remote from remote people that would like to access like white are not physically present so that was it with type c we just signed in now we're going to show you is our k9 nfc enabled so understand that the nfc is also a near it's a near field communication so it works like as a button press because the nfc has to be closed very close to the phone meaning that you have a physical proximity presence with the phone during the sign so you select your account same process that password and then the key is required so you will be invited to place the key on the back of your phone so you can see and use your security key with nfc place it in the back and you're in so you perform the two-step verification the google with the nfc with our k9 and the last one it will be with bluetooth low energy with our k13 so since the bluetooth uh has a range that is way uh larger than than than the nfc you still need to use a button press for security reason on the protocol to prove that you're physically present at the moment of cessation so of course you pair the key first with you can see the light blinking the key is paired with a smartphone then after you select the account you want to log in so next step you will select the way you can pair another security key if you want and then it verifies your security key and you press the button it performs a two-step verification and you are just in you just logged in with bluetooth that was it um so thank you very much i'm just gonna share the screen again okay so you've seen all the range of connectivity that is right now available so i'd like to thank you so thank you william so thank you julian it was a pleasure to have you today to show a scope for a pki with our keys this is very interesting for the audience for sure and also what we can do with our keys and uh this range is getting broader every day and it's it's very it's really nice to have you today so you have our contact details here i can see that some questions have been asked and we will do uh we will answer them and we'll we also have a survey that will be broadcasted to you right after and uh if you want to ask us any question after this webinar feel free to connect under our email address even to call you call us you can call us anytime and uh thank you very much and wish you a happy new year and a merry christmas and since we are getting close to the dates and uh and see you maybe i hope next year and on trade shows and to meet you in person thank you very much thank you everyone thank you bye
Show moreFrequently asked questions
How can I eSign a contract?
How can I make documents so that someone else can electronically sign them?
What is the definition of an electronic signature according to the ESIGN Act?
Get more for digisign Event Satisfaction Survey made easy
- Print signature service Home Services Contract
- Prove electronically signing Lodger Agreement Template
- Endorse digi-sign Proprietary Information Agreement
- Authorize digital sign Branding Questionnaire
- Anneal signatory Privacy Policy
- Justify eSignature Web Design Proposal Template
- Try initial Forbearance Agreement Template
- Add Recapitalization Agreement sign
- Send Conversion Rate Optimization Proposal Template electronically signing
- Fax General Release of Liability Form mark
- Seal Training Evaluation Survey eSignature
- Password Non-Disclosure Agreement autograph
- Pass IT Support Contract Template digital sign
- Renew Rental Application signed electronically
- Test Professional Model Release Contract electronically sign
- Require Non Solicitation Agreement Template countersignature
- Comment inheritor esign
- Boost tenant digi-sign
- Compel teller signed
- Void Plumbing Contract Template template initials
- Adopt affidavit template eSign
- Vouch School Itinerary template eSignature
- Establish Free Event Ticket template digisign
- Clear Software Maintenance Agreement Template template electronic signature
- Complete New Hire Press Release template signed electronically
- Force Vehicle Bill of Sale Template template countersign
- Permit Veterinary Hospital Treatment Sheet template sign
- Customize Settlement Term Sheet Template template electronically signing