eSign Radix-64 Made Easy
Improve your document workflow with airSlate SignNow
Agile eSignature workflows
Instant visibility into document status
Easy and fast integration set up
E sign radix 64 on any device
Detailed Audit Trail
Rigorous protection standards
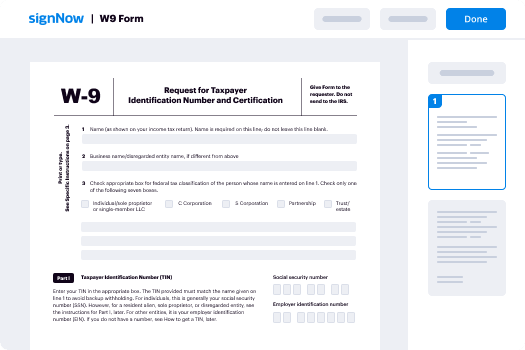
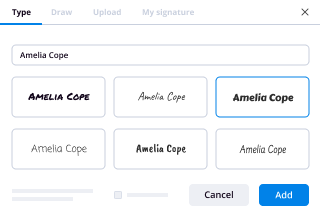
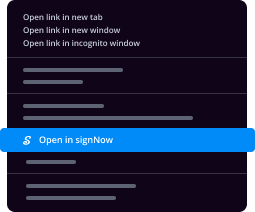
See airSlate SignNow eSignatures in action
airSlate SignNow solutions for better efficiency
Our user reviews speak for themselves






Why choose airSlate SignNow
-
Free 7-day trial. Choose the plan you need and try it risk-free.
-
Honest pricing for full-featured plans. airSlate SignNow offers subscription plans with no overages or hidden fees at renewal.
-
Enterprise-grade security. airSlate SignNow helps you comply with global security standards.

Your step-by-step guide — e sign radix 64
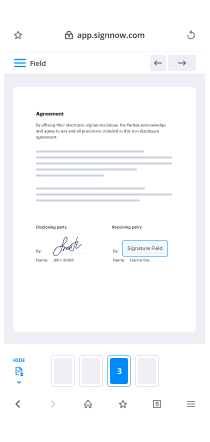
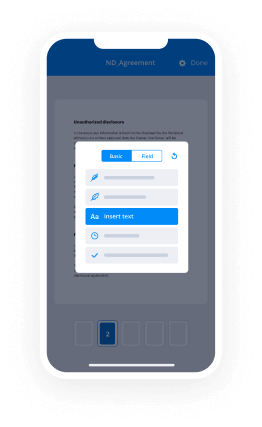
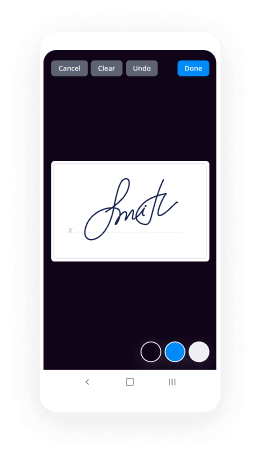
Leveraging airSlate SignNow’s electronic signature any organization can increase signature workflows and sign online in real-time, giving an improved experience to customers and employees. Use eSign Radix-64 in a few easy steps. Our mobile-first apps make operating on the move possible, even while offline! Sign documents from anywhere in the world and make tasks in no time.
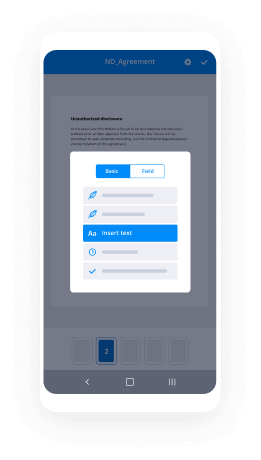
Keep to the stepwise guide for using eSign Radix-64:
- Sign in to your airSlate SignNow account.
- Locate your document in your folders or upload a new one.
- Open up the template and edit content using the Tools list.
- Drag & drop fillable fields, type text and eSign it.
- Add multiple signers via emails configure the signing sequence.
- Indicate which recipients will get an completed copy.
- Use Advanced Options to reduce access to the document and set up an expiry date.
- Click on Save and Close when completed.
In addition, there are more advanced capabilities accessible for eSign Radix-64. List users to your shared workspace, browse teams, and monitor collaboration. Millions of people across the US and Europe concur that a solution that brings everything together in a single holistic digital location, is exactly what organizations need to keep workflows functioning easily. The airSlate SignNow REST API allows you to integrate eSignatures into your application, website, CRM or cloud. Check out airSlate SignNow and enjoy quicker, easier and overall more productive eSignature workflows!
How it works
airSlate SignNow features that users love
See exceptional results eSign Radix-64 made easy
Get legally-binding signatures now!
FAQs
-
What is Radix 64 text encoding?
Radix 64 or base 64 is a binary-to-text encoding system that is designed to allow binary data to be represented in ASCII string format. This is an educational project accepts a string from a user and Radix 64 encodes it. -
Is base64 an encryption?
7 Answers. Base64 is not encryption -- it's an encoding. It's a way of representing binary data using only printable (text) characters. -
What is base 64 encoding used for?
Base64 is most commonly used to encode binary data (for example, images, or sound files) for embedding into HTML, CSS, EML, and other text documents. In addition, Base64 is used to encode data that may be unsupported or damaged during transfer, storage, or output. -
Why does PGP generate a signature before applying compression?
The signature is generated before compression for two reasons: (a) It is preferable to sign an uncompressed message so it is free of the need for a compression algorithm for later verification. ... Message encryption is applied after compression to strengthen cryptographic security. -
Why does base64 end with ==?
A more complete answer is that a base64 encoded string doesn't always end with a = , it will only end with one or two = if they are required to pad the string out to the proper length. 2- As a short answer : The 65th character ("=" sign) is used only as a complement in the final process of encoding a message. -
What is the purpose of base64 encoding?
Base64 is a way to encode binary data into an ASCII character set known to pretty much every computer system, in order to transmit the data without loss or modification of the contents itself. For example, mail systems cannot deal with binary data because they expect ASCII (textual) data. -
How long is a base64 encoded string?
Length of data Base64 uses 4 ascii characters to encode 24-bits (3 bytes) of data. To encode, it splits up the three bytes into 4 6-bit numbers. A 6-bit number can represent 64 possible value. -
How many base 64 bits does it take to encode the three letters ABC?
The three-letter string ABC can be interpreted as a 24-bit string that looks like this: We've added these blue lines just to show where the bytes are broken out. To interpret that as base64, you need to break it into groups of 6 bits. 6 bits have a total of 64 combinations, so you need 64 characters to encode it. -
What is a base 64 decoder?
The \u201cBase64 Decode Online\u201d is a free decoder for decoding online Base64 to text or binary. In other words, it is a tool that converts Base64 to original data. This online decoder is as smart as it is simple. Its superpower is the ability to automatically detect the encoding standard. -
How do I find base64 encoding?
The length of a Base64-encoded string is always a multiple of 4. Only these characters are used by the encryption: \u201cA\u201d to \u201cZ\u201d, \u201ca\u201d to \u201cz\u201d, \u201c0\u201d to \u201c9\u201d, \u201c+\u201d and \u201c/\u201d The end of a string can be padded up to two times using the \u201c=\u201d-character (this character is allowed in the end only)
What active users are saying — e sign radix 64
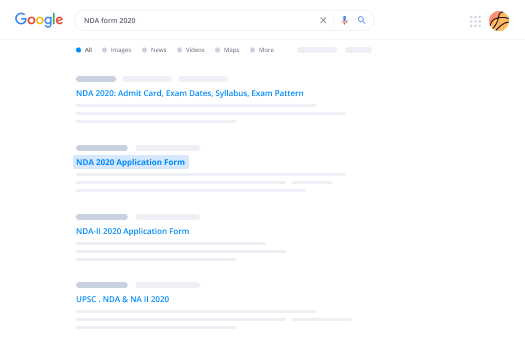
Related searches to eSign Radix-64 made easy
E sign radix 64
next we will move on to the next topic PGP operation email compatibility what actually email compatibility when BGP is used at least part of the block to be transmitted is encrypted if only the signature service is used then the message digest is encrypted for example with the sender's private key if the confidential service is used the message plus signature are encrypted it may be in one time a symmetric key thus part of all of these resulting block consists of a stream of arbitrary 8-bit however many electronic mail systems only permit the use of blocks consisting or containing of AXI discs to accommodate this restriction pgb provides the service of service of converting the raw 8-bit binary string to yet stream up a printable ASCII characters the scheme used it for this purposes radix 64 version conversion each group of three octet of binary data is mapped into four ASCII characters this format also offends CRC to detect the transmission error the use of radish 64 expands and message by 33% [Music] fortunately the session key and signature portions of this messages are relatively compact and the plaintext messages have been compressed in fact the compression should be more than enough to compensate further at a 64 X function for example if you're going to see an average compression rate ratio maybe 2.0 using a zip if we ignore the relatively small signature and key components the typical overall effect of compression and expansion finally X would be 1.33 in 2.5 m 3x that maybe 0.66 5x thus there is still an overall compression of M about 1/3 so one noteworthy aspect of this radix 64 algorithm is it's blindly converts the input stream of red X 64 format regardless of content even if the input happens to be ASCII text thus if a message is signed but not encrypted and the conversions applied to the n-type block the output will be untreatable to the casual observer which provides a certain level of confidentiality as an option PGP can be configured to convert to radix 64 former only the signature portion of the sign the plaintext message this enables the human recipient to read the message without using PGP PGP would be still have to be used to verify the signature for example the we will see about the particular operation the speaker the relationship among the four services so for what we discussed this could inhibit us and so with it on the transmission generic transmission diagram which is going to be illustrated or it's it's completely stated over here let's see how it's going to be to the operation a bun on transmission a signature is going to be generated using an ash core of the uncompressed to pine text then the bind text plus signature if present is compressed for example a file which is going to be given over there and whenever your signature is going to be required then it can generate the signature and there is going to be concatenated with the file and that is going to became compressed if no signature is required just simply this file is couldn't be get compress Dorothy next if the content shallot is required the block is encrypted and prepared with the public key encrypted symmetric encryption key finally the entire block is converted to ready 16 example for the compression after the compression the data if conference shot is going to be required then we can do the encryption process to provide the confidentiality for this particular operation with the public key with the public key under shared key otherwise if no confidential is going to require stratum it's going to be given for the converter radix 64 this is going to be the operation which is going to be there in the generic transmission diagram we will see a port on the reception end in the reception end once the incoming block is first converted into back from radix 64 format to binary then if message is going to be encrypted then the receptor need to decrypt the information if it is not encrypted then straight away the information may be get taken for the decompression if the message is encrypted then we have to go for the decryption process the decryption process is going to be done with the private key of the user with the particular public key then we have to get the data over here if the message is the resultant block is then be compressed if the message is sign the the receptor recovers the transmitter ash code and compares its to its own calculation of the hash code otherwise straight away that decompressed data will be taken over here this is a generic reception diagram which is going to be present in the particular email compatibility let us discuss about the fifth parameter service of the particular PGP operation segmentation another constraint of the Zeeman is that that is usually a maximum message length and PGP automatically blocks an encrypted message into segments of an appropriate length on the reception the segment's must be reassembled before the decryption process so such a way this PGP is going to be kept operate able under the services as we have come across with this particular thing authentication confidentiality authentication and confidentiality both together and email compatibility sorry compression email compatibility and finally the segmentation process these are the file services which have been provided for the PGP operation let me see the summary of PGP services under the function a digital signature is may be used over there or message encryption compression and email compatibility the algorithm which is going to be used over there the digital signature is going to be T SSR sha on RSA sha and which is going to be providing an ash code of message is created using this SH algorithm the encryption process may be and DSS or RSA which is with the helper position as private key and which includes the message of the message encryption the algorithm it is going to use over there is nothing but C ast 128-bit our IDE or triple key encryption dip triple tree decryption is going to be get used over the with the diffie-hellman RSM so here the description is nothing but the message is encrypted using the particular caste 128 the hi DEA or Triple DES with one time session key generated by the Cinda the center key is encrypted using a DV Hellman or an RSA with the recipients public key and it includes a message the compression method which is going to be used over is nothing but zip xored IP zip compression method so a message may be compressed for storage or transmission using the zip the knee mail compatibility is nothing but we are going to use an ordered x64 conversion method which is going to provide the transparency for email applications as encrypted messages may be converted to en asking strings using in reading 64 conversion such a way we have come to an conclusion summary of this particular video in this particular video we have come across with an introduction about electronic mail security we have entered into we have seen about the pretty good privacy protocol the notations which have been used in the critical privacy and operational descriptions nothing but the services provided by the PGP the five different services authentication confidentiality compression email compatibility and finally segmentation and we are come across with transmission and reception of a message in the PGP in the email compatibility and finally we conclude with the summary of PGP services hope that this video may would be helpful for you people to understand about the PGP operation the pretty good privacy operation which have been used in the email security if you have any queries kindly we can post the chorus to me thank you for watching this video thank you
Show moreFrequently asked questions
How do I eSign a document before sending it?
How can I easily get an electronic signature created in Word?
How do I put an electronic signature on a PDF file?
Get more for eSign Radix-64 made easy
- Print signature service Agency Agreement Template
- Prove email signature Artist Press Release
- Endorse eSign CCW Certificate Award
- Authorize digital sign Free Florida Room Rental Agreement
- Anneal signatory Credit Agreement
- Empower electronically signed ID Card Template for Parents
- Try digisign Award Application
- Add Property Management Service Agreement digi-sign
- Send Event Management Proposal Template esign
- Fax Perfect Attendance Award signature block
- Seal Teacher Resignation Letter signature
- Password Joint Venture Agreement email signature
- Pass Wedding Photography Contract Template signatory
- Renew Prenuptial Agreement electronically signed
- Test Management Report byline
- Require 1040 Form esigning
- Send eyewitness sign
- Accredit watcher countersign
- Compel awardee signature service
- Void Photography Quote Template template digital sign
- Adopt report template initial
- Vouch Washington State Rental Agreement template signature
- Establish New Client Onboarding Checklist template countersignature
- Clear Graphic Design Proposal and Agreement Template template digital signature
- Complete Employee Medical History template electronically signed
- Force Separation Agreement Template template signed
- Permit Car Service Receipt template digi-sign
- Customize Residential Roofing Contract Template template esign