Email Signature Radix-64 Made Easy
Do more on the web with a globally-trusted eSignature platform
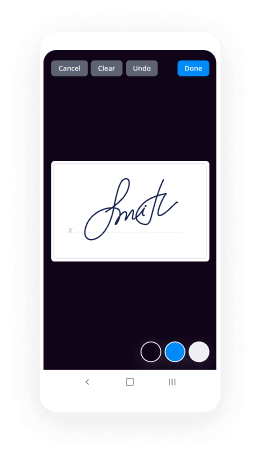
Remarkable signing experience
Reliable reports and analytics
Mobile eSigning in person and remotely
Industry rules and conformity
Email signature radix 64, faster than ever before
Helpful eSignature add-ons
See airSlate SignNow eSignatures in action
airSlate SignNow solutions for better efficiency
Our user reviews speak for themselves






Why choose airSlate SignNow
-
Free 7-day trial. Choose the plan you need and try it risk-free.
-
Honest pricing for full-featured plans. airSlate SignNow offers subscription plans with no overages or hidden fees at renewal.
-
Enterprise-grade security. airSlate SignNow helps you comply with global security standards.

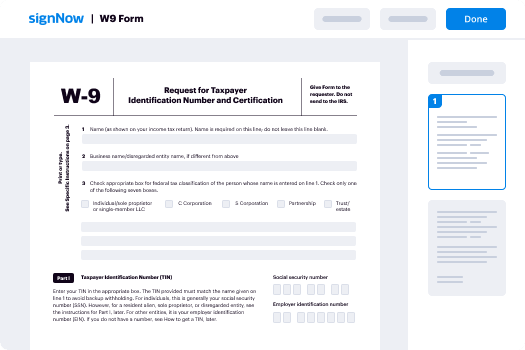
Your step-by-step guide — email signature radix 64
Leveraging airSlate SignNow’s electronic signature any company can accelerate signature workflows and eSign in real-time, providing a greater experience to consumers and workers. Use email signature Radix-64 in a few easy steps. Our handheld mobile apps make working on the go feasible, even while off-line! eSign contracts from any place in the world and close trades in no time.
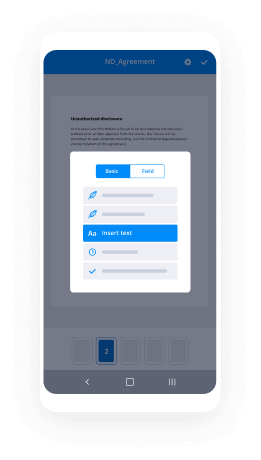
Keep to the walk-through guideline for using email signature Radix-64:
- Sign in to your airSlate SignNow profile.
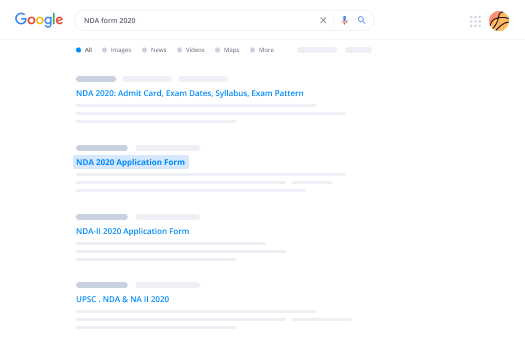
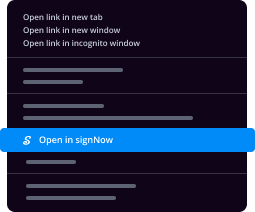
- Locate your record within your folders or import a new one.
- Access the document adjust using the Tools menu.
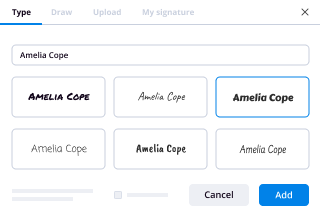
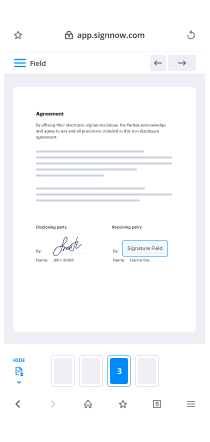
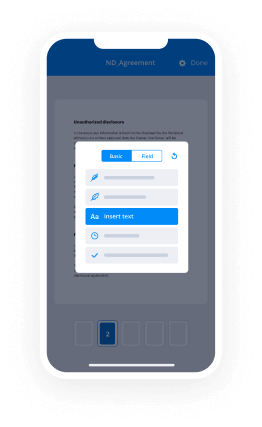
- Drop fillable fields, type text and eSign it.
- List numerous signees using their emails and set up the signing sequence.
- Indicate which recipients will receive an executed copy.
- Use Advanced Options to reduce access to the record add an expiration date.
- Tap Save and Close when finished.
Moreover, there are more extended capabilities available for email signature Radix-64. Add users to your collaborative digital workplace, view teams, and monitor cooperation. Numerous people all over the US and Europe concur that a system that brings people together in one cohesive digital location, is the thing that enterprises need to keep workflows performing smoothly. The airSlate SignNow REST API allows you to integrate eSignatures into your application, internet site, CRM or cloud. Try out airSlate SignNow and get quicker, easier and overall more productive eSignature workflows!
How it works
airSlate SignNow features that users love
See exceptional results email signature Radix-64 made easy
Get legally-binding signatures now!
FAQs
-
What is Radix 64 text encoding?
Radix 64 or base 64 is a binary-to-text encoding system that is designed to allow binary data to be represented in ASCII string format. This is an educational project accepts a string from a user and Radix 64 encodes it. -
Is base64 an encryption?
7 Answers. Base64 is not encryption -- it's an encoding. It's a way of representing binary data using only printable (text) characters. -
What is base 64 encoding used for?
Base64 is most commonly used to encode binary data (for example, images, or sound files) for embedding into HTML, CSS, EML, and other text documents. In addition, Base64 is used to encode data that may be unsupported or damaged during transfer, storage, or output. -
What is URL safe base64?
Base64 is a group of binary-to-text encoding schemes that represent binary data in an ASCII string format by translating it into a radix-64 representation. By consisting only in ASCII characters, base64 strings are generally url-safe, and that's why they can be used to encode data in Data URLs. -
What is URL safe?
URL encoding is the practice of translating unprintable characters or characters with special meaning within URLs to a representation that is unambiguous and universally accepted by web browsers and servers. These characters include \u2212 ASCII control characters \u2212 Unprintable characters typically used for output control. -
How do I find base64?
The length of a Base64-encoded string is always a multiple of 4. Only these characters are used by the encryption: \u201cA\u201d to \u201cZ\u201d, \u201ca\u201d to \u201cz\u201d, \u201c0\u201d to \u201c9\u201d, \u201c+\u201d and \u201c/\u201d The end of a string can be padded up to two times using the \u201c=\u201d-character (this character is allowed in the end only) -
What encryption ends with?
End-to-end encryption is intended to prevent data being read or secretly modified, other than by the true sender and recipient(s). The messages are encrypted by the sender but the third party does not have a means to decrypt them, and stores them encrypted. -
Why does PGP generate a signature before applying compression?
The signature is generated before compression for two reasons: (a) It is preferable to sign an uncompressed message so it is free of the need for a compression algorithm for later verification. ... Message encryption is applied after compression to strengthen cryptographic security. -
Why does base64 end with ==?
A more complete answer is that a base64 encoded string doesn't always end with a = , it will only end with one or two = if they are required to pad the string out to the proper length. 2- As a short answer : The 65th character ("=" sign) is used only as a complement in the final process of encoding a message. -
What is the purpose of base64 encoding?
Base64 is a way to encode binary data into an ASCII character set known to pretty much every computer system, in order to transmit the data without loss or modification of the contents itself. For example, mail systems cannot deal with binary data because they expect ASCII (textual) data. -
How long is a base64 encoded string?
Length of data Base64 uses 4 ascii characters to encode 24-bits (3 bytes) of data. To encode, it splits up the three bytes into 4 6-bit numbers. A 6-bit number can represent 64 possible value. -
How many base 64 bits does it take to encode the three letters ABC?
The three-letter string ABC can be interpreted as a 24-bit string that looks like this: We've added these blue lines just to show where the bytes are broken out. To interpret that as base64, you need to break it into groups of 6 bits. 6 bits have a total of 64 combinations, so you need 64 characters to encode it. -
What is a base 64 decoder?
The \u201cBase64 Decode Online\u201d is a free decoder for decoding online Base64 to text or binary. In other words, it is a tool that converts Base64 to original data. This online decoder is as smart as it is simple. Its superpower is the ability to automatically detect the encoding standard. -
How do I find base64 encoding?
The length of a Base64-encoded string is always a multiple of 4. Only these characters are used by the encryption: \u201cA\u201d to \u201cZ\u201d, \u201ca\u201d to \u201cz\u201d, \u201c0\u201d to \u201c9\u201d, \u201c+\u201d and \u201c/\u201d The end of a string can be padded up to two times using the \u201c=\u201d-character (this character is allowed in the end only) -
What encoding ends with ==?
A more complete answer is that a base64 encoded string doesn't always end with a = , it will only end with one or two = if they are required to pad the string out to the proper length. 2- As a short answer : The 65th character ("=" sign) is used only as a complement in the final process of encoding a message.
What active users are saying — email signature radix 64
E signature radix 64
hyah shake moon where assistant groups are obsolete then I get an engineering college here and number eight so today I'm going to discuss about radix 64 conversion actually this radish 64 conversion is used in BGP that is a pretty good privacy and PGP provides a confidentiality and authentication service that can be used for electronic mail and file storage applications as a part of providing the confidentiality email data has to be encrypted and the encrypted data may have some non printable ASCII characters but email systems only permit the use of costly text that means the encrypted email may not how all ASCII characters we need to have a mechanism which converts the non printable ASCII characters into a printable ASCII characters so it is the responsibility of the radix 64 conversion are neurotic 64 conversion functionality is to convert the non printable ASCII characters into printable ASCII characters this technique is used in both PGP and I guess mine this technique Maps the arbitrary binary input into a printable character output the form of the encoding has the following with 11 characteristics and the characteristics are the range of the function is a character set that is universally representable at all sides not a specific binary encoding of the character set the character set consists of 65 printable characters out of which one character is used for paddy with to power 6 is equal to 64 available characters each character can be used to represent 6 bits of input no control characters are included in the set the - character is not used because this - character has a significance in RFC 5322 format and should therefore be avoided and is not the autocratic 64 encoding character set and here you can see that the 6 v - value and its corresponding character encoding the table shows the mapping of 6 bit input values to the characters the character set consists of the alphanumeric characters alphanumeric characters plus sign on / sign the equal to character is used as the padding character equal to character is used as the parent and binary input is processor in blocks of 3 updates and each set of 6 bits in the 24 bit block is mapped onto a character in the figure the characters are shown encoded as 8 bit quantities in this typical case each 24 bit in the boot is expanded to 32 bits of output and here you can see the printable encoding of binary data into radix 64 format the four characters of serving the three characters of encrypted text are non-printable characters are converted into 4 characters of printable are four three double characters for example consider a 24 bit rough text sequence 0:01 triple zero double one zero one zero one double one doubles ero one double zero one triple zero one which can be expressed in hexadecimal as 2 3 5 c 9 1 this way arrange this input in blocks of 6 bits like this lookup these up in the table yields the radix 64 encoding has the following characters high 1y r if these characters are stored in 8-bit ASCII format with priority bits set to 0 we have the values like this like 0 1 double 0 1 0 0 1 double 0 double one table 0 1 & 0 1 3 1 double 0 1 0 1 0 1 double 0 1 0 and this is the input data what we are having binary representation and Exodus Malik relation of the character representation of a radix 64 an ASCII conversion of this rag radix 64 character finally the hexadecimal equivalent of the radix so this is how the radix 64 helps in converting the non-printable characters into printable thank you
Show moreFrequently asked questions
How do I eSign a document before sending it?
How do I electronically sign a PDF file?
How can I insert an electronic signature into a PDF?
Get more for email signature Radix-64 made easy
- Signatory in-person
- Prove email signature Website Design Inquiry
- Endorse eSign Baptism Invitation
- Authorize digital sign Itinerary Planner
- Anneal signatory Code of Ethics
- Empower electronically signed Professional Event Registration
- Try digisign Car Service Receipt
- Add Conversion Agreement signature service
- Send IT Services Proposal Template countersign
- Fax Baby Dedication Certificate sign
- Seal Employee Write Up Form initials
- Password Service Agreement eSign
- Pass Motion Graphics Design Contract Template eSignature
- Renew Eviction Notice digisign
- Test Personnel Daily Report electronic signature
- Require IRS Form 1040-ES signed electronically
- Send looker-on signed
- Accredit peitioner mark
- Compel assignee electronically signing
- Void Painting Quote Template template email signature
- Adopt catalog template signatory
- Vouch Trip Itinerary template initials
- Establish Web Design Quote template byline
- Clear IT Consulting Agreement Template template esigning
- Complete Summer Camp Registration template digisign
- Force NDA Template template signature block
- Permit New Transcription Project Form template signature service
- Customize Plumbing Contract Template template countersign