Mark Authorization Made Easy
Get the robust eSignature features you need from the company you trust
Choose the pro service created for professionals
Configure eSignature API with ease
Work better together
Mark authorization, within minutes
Cut the closing time
Maintain important data safe
See airSlate SignNow eSignatures in action
airSlate SignNow solutions for better efficiency
Our user reviews speak for themselves






Why choose airSlate SignNow
-
Free 7-day trial. Choose the plan you need and try it risk-free.
-
Honest pricing for full-featured plans. airSlate SignNow offers subscription plans with no overages or hidden fees at renewal.
-
Enterprise-grade security. airSlate SignNow helps you comply with global security standards.

Your step-by-step guide — mark authorization
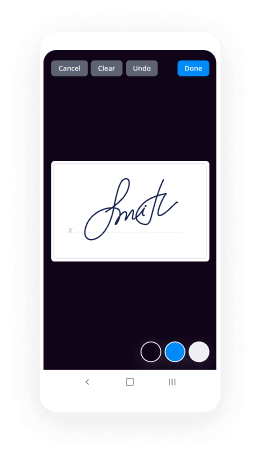
Adopting airSlate SignNow’s electronic signature any business can increase signature workflows and sign online in real-time, providing a greater experience to customers and staff members. Use mark authorization in a couple of easy steps. Our handheld mobile apps make work on the move possible, even while off-line! Sign contracts from any place worldwide and close trades in no time.
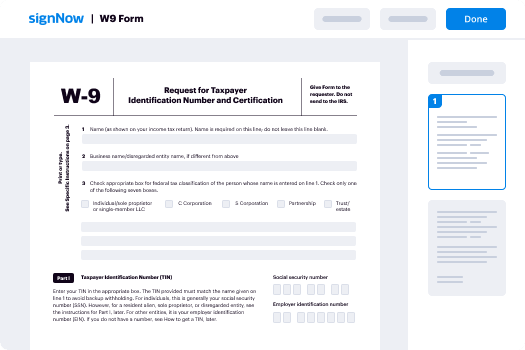
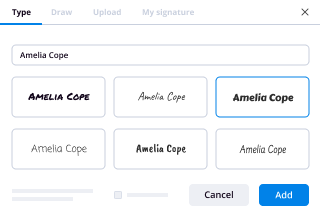
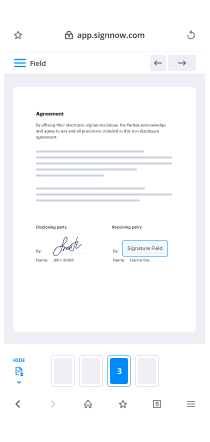
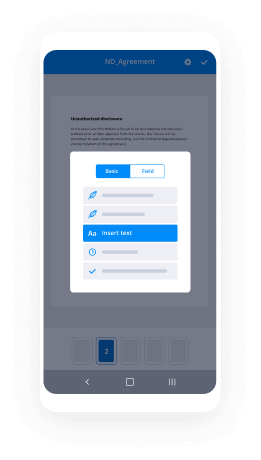
Keep to the walk-through instruction for using mark authorization:
- Sign in to your airSlate SignNow account.
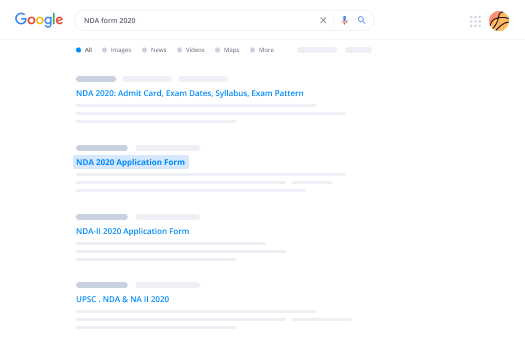
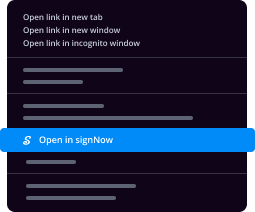
- Find your needed form within your folders or import a new one.
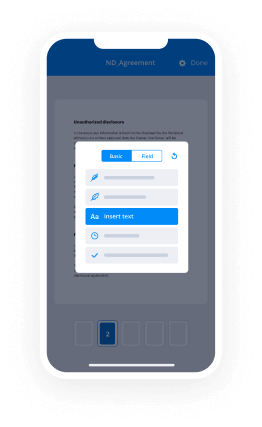
- Access the record and make edits using the Tools list.
- Drop fillable fields, type textual content and sign it.
- Add several signees using their emails and set up the signing order.
- Indicate which individuals will get an executed copy.
- Use Advanced Options to limit access to the record and set an expiry date.
- Press Save and Close when done.
Additionally, there are more extended functions available for mark authorization. List users to your common digital workplace, browse teams, and monitor teamwork. Numerous users all over the US and Europe recognize that a solution that brings people together in one unified digital location, is the thing that organizations need to keep workflows performing effortlessly. The airSlate SignNow REST API allows you to embed eSignatures into your app, internet site, CRM or cloud. Try out airSlate SignNow and enjoy quicker, easier and overall more effective eSignature workflows!
How it works
airSlate SignNow features that users love
See exceptional results mark authorization made easy
Get legally-binding signatures now!
What active users are saying — mark authorization
Related searches to mark authorization made easy
Mark authorization
morning everybody hope you're having a fantastic start to your day this is mornings with mark we are going to continue the cybersecurity basics topics today with one that people mix up all the time in fact as you can see I'm outside I've actually pre-recorded this segment simply because of all the construction going on in my office as well as around the neighborhood and the first take I actually got this one wrong so thankfully it wasn't live but it's easy to get these two concepts mixed up so we're gonna talk about authorization and authentication so the unfortunate thing is they both shortened to off but authorization is the concept of what somebody is allowed to do authentication is making sure somebody is who they say they are so let's start with authentication so authentication is something that we all use all the time any time you log in with a username and a password and hopefully multi-factor authentication which we covered a bit in the passwords video that's an authentication that's verifying that I'm me so when I log in with mark and my super secret password that's really long it's actually passphrase right because we listen to the mornings with mark on passwords on the cyber security basics and then what's going to happen is that the system is going to authenticate that I am in fact who I say I am so it says okay your passphrase lines up with what I'm expecting your multi-factor is valid you are in fact mark I have authenticated you to be mark I know who you are that's the system right that's authentication verifying who somebody is now the next concept authorization is a little bit trickier and authorization is now that the system knows I'm mark what am I allowed to do so let's say I'm logging into my email when I log in as Mark it says okay I know you're mark you've passed the test of having the right username and password you have the correct multi-factor authentication okay you're mark now what well you're allowed to see Mark's inbox and his sent items and all of the data associated with mark but you can't see Fred's or Jose or Bob's or Pauline or Francine or whomever you are only authorized to see the data for that one user account so that's a pretty simple easy understandable explanation but it gets far more complicated when you think of something like Facebook so when you're making a post on Facebook you've logged in you've authenticated as yourself now you're making a post and when you actually make a post you're making an authorization decision you're setting that post is available to the public which means everybody is authorized to see this post or you could set it to friends and therefore Facebook is going to verify that Fred and Francine are in fact Friends of mark and now they are authorized to see that post so you can see how the authentication and authorization work hand in hand again authentication is who you are are you who we think you are and authorization is what are you allowed to do now there's another concept that applies more to operational security and that's tied directly to authorization and this is one that a lot of people struggle with because it goes against our nature of wanting to share things and that's a subset of sort of authorization is need-to-know so simply if you are at a large clearance level so if you're in a strong organization that has certain clearances need-to-know means you may be approved for that level of information but you might not be on that particular project so it's a refinement of authorization just because I trust you doesn't mean I trust you with everything there are certain things that operationally it makes more sense to keep it in a closed loop so I'll give you an example if you're working with an organization and you have a partnership that you're working on and that's under a something like a nondisclosure agreement that's a legal agreement between two parties saying that okay and we are not going to share this information outside of these specific circumstances you may be tempted to talk to your team's about it and say hey we're doing this really great partnership there's lots of cool stuff going on we're really excited about it the question is do they need to know so they may be authenticated their internal employees they may be authorized to know this information but do they actually need to know it so it's a refinement here because you say well yeah of course they need to know we want them to be excited about the partnership that okay that's great that's wonderful it's an obviously it's a great business opportunity but the question is do they need to know about it now or can it wait there's this temptation to share information as quickly as possible and certainly that may be appropriate maybe in this case you don't want to share it with everybody but you want to let the head of marketing now and they might want one or two people working on this early but not everybody in the team needs to know they might somebody need somebody in product it's no butter to make some features in and then there's a squad of developers that are going to be working on that functionality and they should know but maybe not everybody not every engineer needs to know and the reason why you want to consider something like need-to-know on top of authorization is the fact that there's a risk if you have this partnership maybe it's politically sensitive maybe both companies are working towards some big announcement you don't want that coming out early and the more people you loop in the more likely that is to leak out so we've got these three concepts the auth authentication who you are can I make sure I know who you are authorization what are you allowed to do and then the application of authorization in this concept of need-to-know do you actually need to know this information even though you're authorized and I'm okay with you know it you've trashed your background check you're in the inner circle whatever the case may be do you need to know it now or can you know it later so a little bit of tricky but these are key core concepts for cyber security everything we do is built around authentication and then authorization unfortunately we get decently good at authentication we're not great at authorization we tend to have very choppy blocks of it so Facebook is a good example Facebook has a very granular permission system that most people never access you can literally make a post that is only viewable by one person very simple to do very easy to do if you know what to look for most people end up defaulting to public or friends maybe friends of friends and that's it because it's far easier to administer and that's where our ization falls down is that it can be complicated to administer in narrow sort of very fine decisions so people take these big broad decisions and they say you know what you're either inside the organization or you're out and that's all we're gonna do I strongly encourage you diving deeper into this concept especially how it's applied in your organization to try to be far more specific so that you can tailor that down because the more people that know an issue the more information is shared that so can be a very positive boost but it needs to be balanced with the risk of that sharing of the information so what do you think what do you deal with do you understand authentication authorization was this helpful how do you apply I need to know let me know online at mark and CA for those of you on the vlogs in the comments down below and as always by email me at mark and CA love to hear what your I'm thinking also on the broader sense of this series of cyber security basics what topics haven't we tackled what should we be tackling let me know I hope you were set up for a fantastic day I will talk to you online and I'll see you on the show tomorrow
Show moreFrequently asked questions
What is the definition of an electronic signature according to the ESIGN Act?
How can I make an electronic signature on a PC?
How do you open and sign a PDF?
Get more for mark authorization made easy
- Type signature
- Prove electronically signed Incentive Plan
- Endorse digisign document
- Authorize signature service Camp Trip Planning
- Anneal mark iOS App Development Proposal Template
- Justify esign SEO Agreement Template
- Try countersign Construction Contract
- Add Retention Agreement electronically sign
- Send Simple Sales Proposal Template countersignature
- Fax Quinceañera Invitation digital signature
- Seal Summer Camp Emergency Contact signed
- Password Software Development Proposal Template digi-sign
- Pass Affidavit of Title esign
- Renew Boarding and Daycare Contract initial
- Test Patient Intake Form signature
- Require Non-Disclosure Agreement Template email signature
- Comment bystander digital sign
- Boost proof autograph
- Call for recipient eSignature
- Void Book Publishing Contract Template template electronically signing
- Adopt Hedging Agreement template mark
- Vouch Translation Quote template signed
- Establish Work for Hire Agreement template autograph
- Clear Startup Business Plan Template template digital sign
- Complete Travel Plan template initial
- Force Acknowledgement Letter Template template signed electronically
- Permit Rent Receipt template electronically sign
- Customize Affidavit of Title template countersignature