Redline Requisition with airSlate SignNow
Get the robust eSignature capabilities you need from the solution you trust
Select the pro service designed for pros
Configure eSignature API quickly
Work better together
Redline requisition, in minutes
Decrease the closing time
Keep important data safe
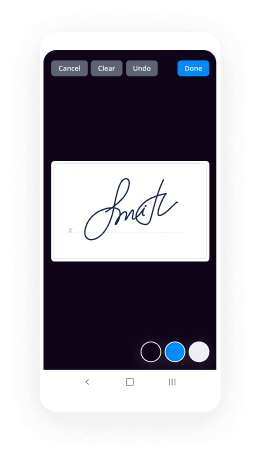
See airSlate SignNow eSignatures in action
airSlate SignNow solutions for better efficiency
Our user reviews speak for themselves






Why choose airSlate SignNow
-
Free 7-day trial. Choose the plan you need and try it risk-free.
-
Honest pricing for full-featured plans. airSlate SignNow offers subscription plans with no overages or hidden fees at renewal.
-
Enterprise-grade security. airSlate SignNow helps you comply with global security standards.

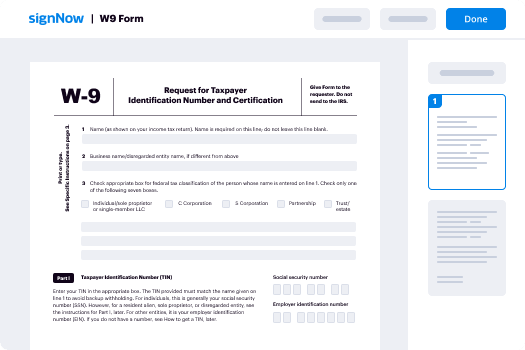
Your step-by-step guide — redline requisition
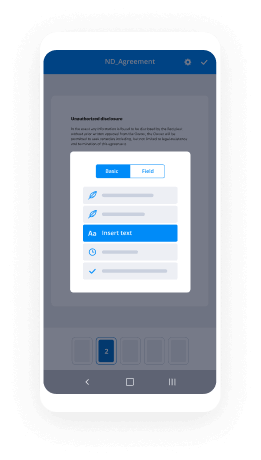
Leveraging airSlate SignNow’s electronic signature any company can speed up signature workflows and eSign in real-time, giving an improved experience to consumers and staff members. redline requisition in a couple of simple steps. Our mobile apps make operating on the run achievable, even while off-line! eSign documents from any place worldwide and close up tasks quicker.
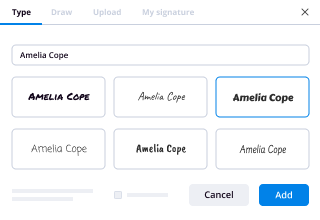
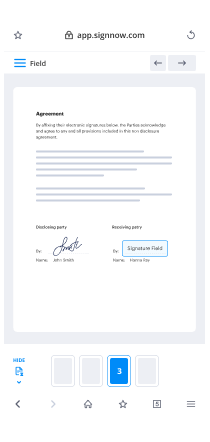
Follow the step-by-step guideline to redline requisition:
- Log on to your airSlate SignNow profile.
- Find your record within your folders or upload a new one.
- the template and edit content using the Tools list.
- Drop fillable boxes, type textual content and sign it.
- Add several signers via emails configure the signing sequence.
- Specify which individuals can get an executed copy.
- Use Advanced Options to reduce access to the record add an expiration date.
- Tap Save and Close when done.
Additionally, there are more innovative capabilities available to redline requisition. Add users to your collaborative digital workplace, view teams, and monitor collaboration. Millions of consumers all over the US and Europe agree that a solution that brings people together in a single cohesive workspace, is the thing that businesses need to keep workflows performing easily. The airSlate SignNow REST API allows you to embed eSignatures into your app, internet site, CRM or cloud storage. Try out airSlate SignNow and enjoy quicker, easier and overall more efficient eSignature workflows!
How it works
airSlate SignNow features that users love
See exceptional results redline requisition with airSlate SignNow
Get legally-binding signatures now!
FAQs
-
How do you run a redline?
In the toolbar at the top of the screen, click the "Review" tab. This tab contains tools to help with spell checking and editing, including the "Track Changes" feature. Click the "Track Changes" button to enable Track Changes. This feature places a red line in the margins next to any edited text. -
What does it mean to redline a contract?
Redlining a contract is the process of editing a draft. The draft might have been provided by opposing counsel, or it might be an old contract you are using as a template. Redlining requires that you go back and forth with the other side to hammer out the details of your agreement. -
How do you make a red liner?
Know Your Redlining Software. ... Never Create a Redlining over another Redline while doing Contract Changes & Terms. ... Avoid Reading Triple Redlining. ... If in Doubt over another Party's Redline, Run Yours. ... Do not Rely on \u201cTrack Changes\u201d ... Very Few Changes. -
What is a redline in legal terms?
Legal Definition of redlining 1 : the illegal practice of refusing to offer credit or insurance in a particular community on a discriminatory basis (as because of the race or ethnicity of its residents) \u2014 compare reverse redlining. 2 : the practice of showing changes to a draft of a document by marking with red lines. -
What does Redline mean in cars?
Redline refers to the maximum engine speed at which an internal combustion engine or traction motor and its components are designed to operate without causing damage to the components themselves or other parts of the engine. -
What is a redline copy?
"Redlining" is a form of editing in which red ink is used to indicate removal or addition of text in Microsoft Word. You can redline a Microsoft Word document by using Microsoft Word's built-in "Track Changes" feature, or you can manually redline the document with font color changes and strike-throughs. -
How do you redline in Word?
Suggested clip How to Redline in Microsoft Word in OSX - YouTubeYouTubeStart of suggested clipEnd of suggested clip How to Redline in Microsoft Word in OSX - YouTube -
Can you strikethrough on airSlate SignNow?
Now, with airSlate SignNow LINE, you can easily do so. Prepare you document for sending as you normally would: Upload your document, set the signing order and click next. ... After clicking the LINE button, you'll be able to click anywhere on the document and drag strikethrough lines where necessary. -
Can I edit a PDF in airSlate SignNow?
You can use airSlate SignNow to quickly scroll through an interactive, fillable PDF and to fill in all necessary fields. ... In the airSlate SignNow library, highlight the form and then choose Sign and Send. At the Apply Form Fields prompt, choose Apply, which allows you to edit the fields in the PDF. -
How do I edit a template in airSlate SignNow?
Under the templates menu, click on \u201cMy Templates.\u201d Find the template you wish to edit, and open it. In the first screen, it is possible to change the name, the description, and who the template is shared with. The document that will be signed can also be swapped out with a different document, such as a newer version. -
Can you edit document in airSlate SignNow?
Tap My Docs or Transaction Rooms and navigate to the document you wish to edit. Tap the document, then tap the Share icon. Tap the preferred application to edit the document. Edit the document as desired. -
Can airSlate SignNow edit pdfs?
Thanks to airSlate SignNow, you can now easily add and edit form fields on PDF files to collect important signer information. ... With airSlate SignNow, you can: Upload a PDF document and make edits from any smartphone or mobile device. -
What does allow to edit mean in airSlate SignNow?
"This option allows recipients to make changes to the document with the document markup feature. If a recipient selects Markup Document and makes a change, all signers on the document must initial their approval of these changes, and a full audit trail is maintained in airSlate SignNow" All Answers. -
Can you white out on airSlate SignNow?
Using the airSlate SignNow Document Markup feature, recipients can make changes to an airSlate SignNow document. Recipients can use the markup tool to: "White out", or cover up, document text to show deletions. Cover up text and add new text over the old text. -
How do I turn on Redline in Word?
What is the method to turn on the red squiggly line that appears in Microsoft Word? - Quora. Go to File > Options > Proofing and then make sure the Check spelling as you type option is selected. In the document, Word will pick up incorrect spelling. You can also press the F7 key to perform a spell check.
What active users are saying — redline requisition
Related searches to redline requisition with airSlate airSlate SignNow
Redline requisition
hello uni Vanier welcome to my introductory video on how to install and use redline in this video I will cover what rayline does how do you get it how do you install it how do you use it and why you should use it hope you like the video thanks for watching okay so what is redline redline is fires premiere free endpoint security tool as a leading company in cyber security I wanted to learn their tool as it provides host investigative capabilities to detect malicious activity and compromise systems through memory and file analysis through that it helps develop a threat assessment profile for users one thing to note is that redline used to be a tool originally called mandiant which is also the name of a private company founded in 2004 by Kevin mania mandiant originally provided incident response services in the event of a data security breach prior to being acquired by fire I in 2014 of January a mandiant was partnered with fire I who often identified a security breach then teamed up with mandiant to investigate who the hackers were okay so what can Red Line do in order to find out what the tool can do we're going to visit Fry's website and go to the resources page for the software and read the description so open up a browser and in the URL bar type in WWF IRI calm and on the home page when I go to the resources tab and under free tools and apps click the free software downloads link that should take us to the software page if we scroll down you will see that feride does provide a variety of analysis tools out the one that we're learning today is redline so we're going to click on the red line here and that should take you to the redline page on this page fireEye explains what red lines features are basically redline is a easy to use GUI interface that makes it easier for users to analyze collective data to help identify malicious activity through memory and file analysis with red line you can thoroughly audit and collect all learning processes and drivers from memory file system metadata registry data event logs network information services tasks and a web history it can also analyze and vu imported audit data including the ability to filter results around a given time frame using red lines timeline functionality with the time wrinkle and time crunch features the third feature list that it can streamline memory analysis with the proven workflow for analyzing malware based on relative priority lastly it can perform indicators of compromise or IOC analysis supplied with the set of i/o sees the red line portable agent is automatically configured to gather the data required to perform the IOC analysis and an IOC hit result review if we scroll to the bottom of this page you can see that red line is currently at one point to zero point to version as of June a 2018 and in this version rely introduces support for large file and registry audits our red line also has been improved to address issues related to efficiency and memory management let's move on to downloading red line so scroll back up to the top of the page again and on this page it is required that you complete this form in order in order to download red line once you've completed form click the download now button and that should download red line I've already downloaded it but once you've finished the download it should go to your downloads folder and it should be called red line - one point to zero point two which is the current version I am installing as of today March 24 2009 teen go ahead and right click on it and click install and click Next accept the EULA agreement and I'm just going to choose just me because I don't want anyone else using it other than me if you click on this cost you will see that redline only use this 349 megabytes of disk space which is not that much I'll go ahead and click OK here choose the install path that you want I'm just gonna do it to the default path here click Next and click Next again to initiate the installation should have took too long and let it install and there we have it it is installed okay now that relining is installed how do we use it the cool thing of our line is once you install it it also gives you a user installation guide which can be found in the installation directory of wherever you installed a redline for me within a C Drive Program Files x86 and we're gonna go to redline here we go and indeed redline folder there's a file called redline user guide we're gonna double-click to open that and it does provide information about redline installation instructions redline collectors which we'll go over briefly analysis session creation analysis data investigation use cases and best practices rely licenses support glossary and index going back to the redline collectors I wanted to show that redline has three types of collectors it has the standard collector which is basically a basic collection configuration to collect that out the one that you really want to use that is most important and recommended is the comprehensive collector which does everything the standard collector does and more we'll go over this s we use red line and then indicators of compromised search collectors or ioc search collector this one basically you use you want to look for any critic compromise and match select a tank here's a kind of revised data so we're going to minimize that and to launch redline open up your Windows Start bar and type in redline or you can launch it from the installation path as well and here we are okay so real eye opens up with two options collect data and analyze data collection data lets you create a static collector a comprehensive collector or an IOC search collector and analyze data let's see you analyze the data from is saved and image file or a previous analysis now we don't have anything to analyze yet so the first things we need to do is collect data I'll first do the static collector to show you what the differences between the standard and comprehensive but basically we want to collect data I'm sorry creating the collector does is it creates a collection package onto a USB flash drive or storage media that you can insert into the targeted or infected machine we're on the collector and it'll run and look for any malicious activity and save it into a report file which then you would analyze the report file and review any malicious review the file for any malicious activity so first things first let's click the extended collector and in the start your NASA session window you always want to make sure that acquire memory images always checks it's very important that you check this because you want to review in acquired memory data so that you can be analyzed for any malicious activity click on edit your script a new window opens called view and edit your script and you see there are five tabs memory disk system Network another now for the standard collector all this checked is is process listing Jarvis enumeration who detection and acquired memory image under the memory tab and of course under each of these options here you see sub options for what to collect on you can select more of these for a more comprehensive scan or a collection if you want if you go over to the disk tab you see that nothing is checked under system only one option is checked machine in OS Information Network nothing is checked and other nothing is checked again this is a basic standard collection if you want you can select these options if you want a more comprehensive scan but again when it cats out of that and go back to the comprehensive collector check the same checkbox and click out of your script and you can see that this is a way more comprehensive collection method than the standard collector package because under the disk tab there are options way more options that are checked to collect that on of course nothing under sha-256 or sha-1 or strings is checked we can click those to check it I'm just gonna click on everything here to collect all the data on this current machine normally we would do this on a target or effective machine but I don't have one so we're gonna do it on this machine for the purpose of this tutorial click okay and under the savior collector - this is where you choose the media device you want to install the collector package on so we're gonna click browse and I have a flash drive already in place it has already created a file but I'm going to delete this just to show you yes okay we're going to select the flash drive now you can see that you cannot save the collector file to the root of your flash drive there has to be a directory door for you to say at the flat save the collector - so in order to do that I'm going to click browse and we're gonna recreate the folder I just created earlier so collector package ok we're gonna select that folder it's selected now and the red error message went away so click OK that'll create the portable collector and gives you collector instructions on how to run a collector so basically step one your collector package is created and save to the location you specified and step two on the machine you want to audit we're on the Iran Red Line audit dot bat script preferably from the removable media the script will run the collector as you configured it and say the results to folder name sessions analysis session 1 and every time you run that run red line on it that bad it will create a new analysis session folder called analysis session - now section 3 etc and then when the question is finished you want to transfer the results back to the analysis machine which is this machine which we're also gonna be running the analysis on I'm Charlie collector on and then double click the analysis session that man's file locating the analysis session folder okay so let's go ahead and do that we're going to go to the flash drives here we're going to double-click on click or package and inside the collector package folder there are a few files saw including the father we need to run which is the run red line audit top at we're going to right click on that and expect it oops right click and you can see that there are a few lines of code here that is ran to collect the data that we configured to run now there are a few other JavaScript files vbscript files as well as the x64 and x86 folders which includes an ex h ET exe file that is a fireEye agent application that is used when does run read online run red line audits that file is executed to acquire the data so we're just gonna run this file it will pop it really fast and this takes about an hour so we'll let that run and there it goes it's collecting I think I ran too okay we only want to run run so here we go we'll come back in an hour okay so the collection finally finished it took a lot longer than an hour and so you can see I did finish 11:59 a.m. the next day or today if you right-click on audits folder and go to properties you can see that the collection collected six point nine eight gigabytes of data and that's just because we did the comprehensive collection if we did a standard and chose less options it would have been a lot less but with the comprehensive scan we're doing a lot more and it all depends on your system as well so what I went ahead and did was click on the analysis session one mandiant analysis file and that automatically loaded it didn't a red line and it is now creating a new analysis session this process can take a while I did start the story earlier just to get it going and we'll come back to the video when it's done alright so the analysis session is created it brings you to a start your investigation page showing the system formation and four options to choose from and then the left-hand side you see an analysis data which is all the collected information you configured earlier in the comprehensive scan to collect so the first option here is reviewing a triage collection from a checks this is fireEye's and point their prevention platform which is a commercial product that works with red line the second option which we will choose is the I am investigating a host based on an external investigative lead third is I am reviewing a web history data and fourth I want to search my data with a set of any cares of compromise which we don't have or nor are we doing a web history data so we're gonna go ahead and proceed with clicking the I am I'm investigating host based on external investigative lead this takes you to a detail window was showing you the timestamp field and summary of the next task as it's run you can see the timeline configuration we're going to leave default and then under the analysis data pane shows all the collected information on system information processes hierarchical processes file system registry and so on I'm not going to show my system information because it provides a private information about my system but basically this shows you the Machine information operating system and the BIOS we're going to go ahead and click on processes the processes show the process name of all the processes in the system as well as the PID the path the arguments user name start time and so on and then we're gonna go over the file system the file system has useful information that we also want to look at the file system shows the basically all the information collected on your C Drive or any drives that you might have on the target system looking at the processes I'm sorry file system I went to my desktop and we're just gonna click one of these links here one of these paths there to view information on the path okay so it that took a while but basically the path well I'm sorry the item when the desktop will show you the metadata the hashes time stamps user information file path parts PE info advanced being for the digital signature and exports information I'm a lot of useful information here if you want to look at what application is on the desktop or what items are on the desktop and then also the registry the registry shows all the registry keys on the system you can see the path the type the text value you in the username associated with a registry key how when he was last modified and the security hash we're gonna go over to Windows services and here you can see all these services that are running on the machine by the descriptive name the description the path and any arguments for the service when I skip assistance and go over to users this was very useful in the sense that you want to you know how many users are on the machine and who uses the machine whether the account is disabled locked out and if the path if a password is required this definitely show some vulnerabilities here especially if users don't have a password we'll take a look at the event logs to show all the events logged on the system as well there's a lot of useful information there red line clicks that you can look at unfortunately I wasn't browsing anything or downloading anything there for us to use the browser URL history or file download history options you know but it's a really good tool and you know why you should use it well don't limit yourself to just one set of tools so it's always good to have no different type of analysis tools red line is very easy to use GUI based tool that doesn't involve any command line the downside of it is that it only Anna analyzes window systems and doesn't do Mac or Linux systems maybe not yet but this whole process really didn't take me a lot of time to download and learn it took some playing with but overall the program does collect and provide a lot of useful information I hope this information was helpful and useful to you and thanks for watching
Show more