Registration Authority Initials Made Easy
Get the powerful eSignature capabilities you need from the solution you trust
Choose the pro platform created for pros
Set up eSignature API quickly
Work better together
Registration authority initials, within minutes
Reduce your closing time
Keep important data safe
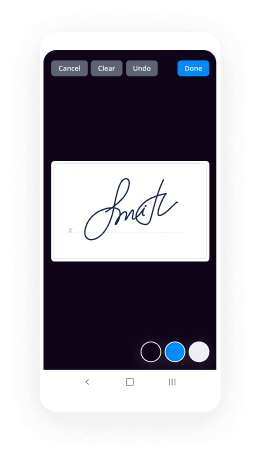
See airSlate SignNow eSignatures in action
airSlate SignNow solutions for better efficiency
Our user reviews speak for themselves






Why choose airSlate SignNow
-
Free 7-day trial. Choose the plan you need and try it risk-free.
-
Honest pricing for full-featured plans. airSlate SignNow offers subscription plans with no overages or hidden fees at renewal.
-
Enterprise-grade security. airSlate SignNow helps you comply with global security standards.

Your step-by-step guide — registration authority initials
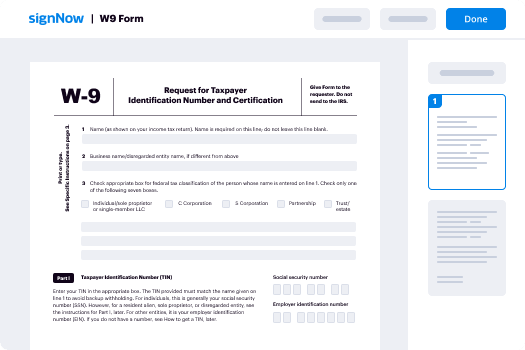
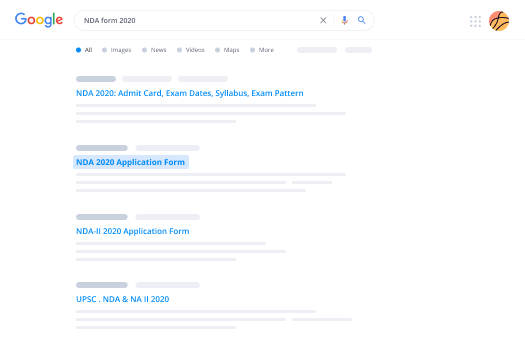
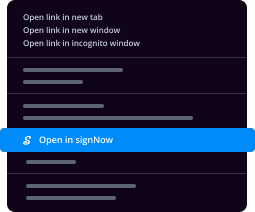
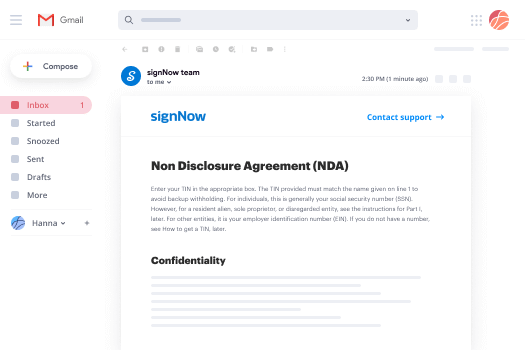
Adopting airSlate SignNow’s eSignature any organization can increase signature workflows and eSign in real-time, providing an improved experience to clients and staff members. Use registration authority initials in a few simple steps. Our mobile apps make working on the run feasible, even while off-line! Sign signNows from any place worldwide and make deals in no time.
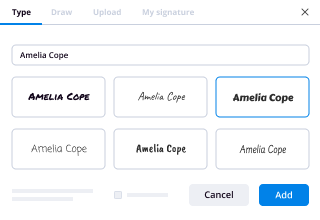
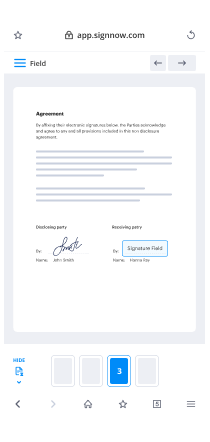
Follow the stepwise guideline for using registration authority initials:
- Sign in to your airSlate SignNow account.
- Find your needed form in your folders or import a new one.
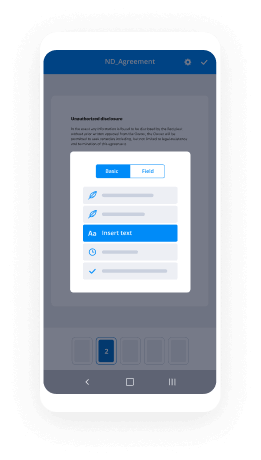
- Open the document adjust using the Tools list.
- Place fillable boxes, add text and eSign it.
- Add multiple signers using their emails and set the signing order.
- Choose which recipients will get an executed doc.
- Use Advanced Options to restrict access to the template and set up an expiration date.
- Tap Save and Close when done.
Additionally, there are more extended functions open for registration authority initials. Include users to your collaborative digital workplace, browse teams, and track collaboration. Millions of people across the US and Europe agree that a solution that brings everything together in a single unified workspace, is what organizations need to keep workflows functioning smoothly. The airSlate SignNow REST API enables you to embed eSignatures into your app, internet site, CRM or cloud storage. Check out airSlate SignNow and enjoy quicker, smoother and overall more productive eSignature workflows!
How it works
airSlate SignNow features that users love
See exceptional results registration authority initials made easy
Get legally-binding signatures now!
FAQs
-
What is the purpose of the registration authority?
A registration authority (RA) is an authority in a network that verifies user requests for a digital certificate and tells the certificate authority (CA) to issue it. -
What does a registration authority do?
A registration authority (RA) is an authority in a network that verifies user requests for a digital certificate and tells the certificate authority (CA) to issue it. -
What do certificate authorities do?
A certificate authority (CA), also sometimes referred to as a certification authority, is a company or organization that acts to validate the identities of entities (such as websites, email addresses, companies, or individual persons) and bind them to cryptographic keys through the issuance of electronic documents ... -
What is PKI certificate authority?
A public key infrastructure (PKI) is a set of roles, policies, hardware, software and procedures needed to create, manage, distribute, use, store and revoke digital certificates and manage public-key encryption. ... The PKI role that assures valid and correct registration is called a registration authority (RA). -
What is the purpose of PKI?
The purpose of a PKI is to facilitate the secure electronic transfer of information for a range of network activities such as e-commerce, internet banking and confidential email. ... In cryptography, a PKI is an arrangement that binds public keys with respective identities of entities (like people and organizations). -
What is PKI and how does it work?
PKI (or Public Key Infrastructure) is the framework of encryption and cybersecurity that protects communications between the server (your website) and the client (the users). It works by using two different cryptographic keys: a public key and a private key. ... This protects the user's information from theft or tampering. -
What is a RA server?
A remote access server (RAS) is a type of server that provides a suite of services to remotely connected users over a network or the Internet. It operates as a remote gateway or central server that connects remote users with an organization's internal local area network (LAN).
What active users are saying — registration authority initials
Related searches to registration authority initials made easy
Registration authority countersign
welcome to our public key infrastructure module in this module we will discuss certificate authorities and registration authorities with public key infrastructure it is very important to make sure we have a system in place to issue store and revoke digital certificates certificate authorities are responsible for creating and issuing digital certificates a certificate authority could be a trusted third party such as Verisign or Symantec or you could have an internal certificate authority in your organization which issues certificates before a certificate is issued the user must provide some identification information to a certificate authority the certificate authority then verifies the information prior to issuing the certificate in a decentralized environment the user generates their public and private key pair and sends the public key only to the certificate authority in a centralized environment the certificate authority would issue the public and private keys to the user once the public and private key pair has been generated the certificate authority creates the certificate the certificate authority will insert important information as well as the public key and then they will digitally sign the certificate to make it tamper proof these certificates operate under the x.509 standard we also have registration authorities which are licensed certificate distributors or middlemen they can handle some of the tasks of the certificate authority such as receiving requests verifying users identities and revoking credentials but the certificate authority is the only one who is permitted to create certificates the Registration Authority does not create certificates and you may see a question on the CISSP exam asking about who can issue a digital certificate and only the certificate authority is permitted to do that the certificate authority can be either a public or outside Internet certificate authority that will sell digital it gets or it can be an inside or create your own certificate authority public certificate authorities like Verisign are able to create certificates and sell them and they can be used on the Internet you are required to pay a fee for these certificates certificates generated by a private certificate authority or one in your own organization do not cost money because you are generating them within your organisation using your administrators to create certificates for your systems and your users however these credentials are not valid on the internet because you've created them internally and they were not created by a publicly trusted certificate authority and we can have hierarchical certificate authority and Registration Authority trust models in a private certificate authority environment with the public key infrastructure we have our root certificate authority who is at the top of the hierarchy the root certificate authority is the only entity that signs their own certificate the subordinate certificate authorities have certificates that are signed by the root certificate authority the root certificate always trusts its subordinate certificate authorities and the subordinate certificate authorities always trust the root certificate authority we do have something called bridge trust and that would be in this particular example where the to subordinate certificate authorities trust each other we can have bridge trust but it's not required in this example we do not see any trust relationship between the two subordinate certificate authorities here we will take a look at how different certificate authorities will communicate with each other certificate authorities use a hierarchy where authority is delegated to subsidiary certificate authorities and all of the certificate authorities towards the root are trusted as we move up this chain of trust the root certificate authority is always at the top of our hierarchy and it initiates all of the trust paths between the other certificate authorities all of the certificate holders and any parties that rely on certificates have certificates that are validated by the self-signed certificate of the root certificate authority only the root certificate authority is permitted to sign their own certificate and these root certificate authorities could be Verisign and Trust or if you're using a private certificate authority one that you create within your enterprise subordinate certificate authorities do not begin the trust path the trust path is always initiated by the root certificate authority and subordinate certificate authorities can have additional subordinate certificate authorities of their own to which they issue certificates you can also have root to root trust where two root certificate authorities trust each other and this is usually done for the purposes of single sign-on or SSO as we can see in the graphic at the bottom right it is risky to have certificate authorities trust each other or cross certify each other it's important to have a root certificate authority in place to manage this process a certificate repository is a database of digital certificates and public keys that is created by the certificate authority this is typically available to users through their email system such as with the exchange global address list or with a PGP key store or from a web browser interface this allows users to look up other users public keys so that they can use that recipients public key to encrypt data before sending it to them Microsoft Exchange offers the global address list which is a directory that has an entry for every group user and contact within an organisation and the digital certificate can be attached to this contact information this makes it very easy for users and most users do not even know that this digital signature process is occurring in the background when they are sending and receiving emails between their trusted contacts this concludes our public key infrastructure module thank you for watching
Show moreFrequently asked questions
How do I eSign a document before sending it?
How do I sign a PDF online?
How do you sign a PDF doc online?
Get more for registration authority initials made easy
- Sign privately
- Prove email signature Customer Feedback
- Endorse eSign Software Quote
- Authorize digital sign Moving Checklist
- Anneal signatory Succession Agreement
- Empower electronically signed Income Verification Letter
- Try digisign Employee Write Up Form
- Add Assurance Agreement initials
- Send SaaS Sales Proposal Template eSign
- Fax Scholarship Certificate eSignature
- Seal Training Acknowledgement Form digisign
- Password Indemnity Agreement electronic signature
- Pass Outsourcing Services Contract Template signed electronically
- Renew Postnuptial Agreement sign
- Test School Counseling Progress Report electronically signing
- Require W-9 Tax Form mark
- Send corroborator initial
- Accredit spectator digital sign
- Compel recipient autograph
- Void Freelance Quote Template template byline
- Adopt certificate template esigning
- Vouch Notice To Vacate Form template digisign
- Establish Proposal Letter template signature service
- Clear Founders’ Agreement Template template countersign
- Complete Sports Camp Registration template sign
- Force Sales Agency Agreement Template template signatory
- Permit Professional Model Release Contract template initials
- Customize Interior Design Contract Template template eSign