Repeat Digital Signature Order with airSlate SignNow
Get the powerful eSignature features you need from the solution you trust
Select the pro service created for pros
Set up eSignature API with ease
Collaborate better together
Repeat digital signature order, within a few minutes
Reduce your closing time
Maintain sensitive data safe
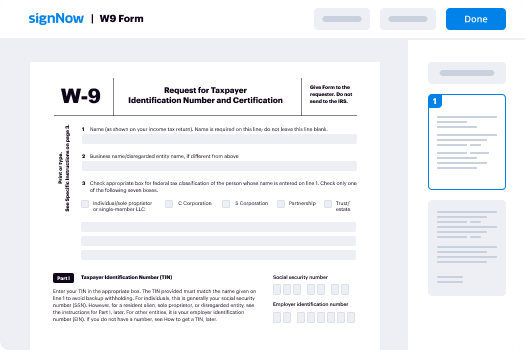
See airSlate SignNow eSignatures in action
airSlate SignNow solutions for better efficiency
Our user reviews speak for themselves






Why choose airSlate SignNow
-
Free 7-day trial. Choose the plan you need and try it risk-free.
-
Honest pricing for full-featured plans. airSlate SignNow offers subscription plans with no overages or hidden fees at renewal.
-
Enterprise-grade security. airSlate SignNow helps you comply with global security standards.

Your step-by-step guide — repeat digital signature order
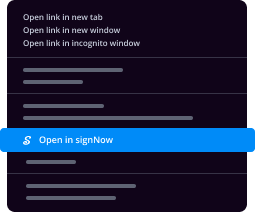
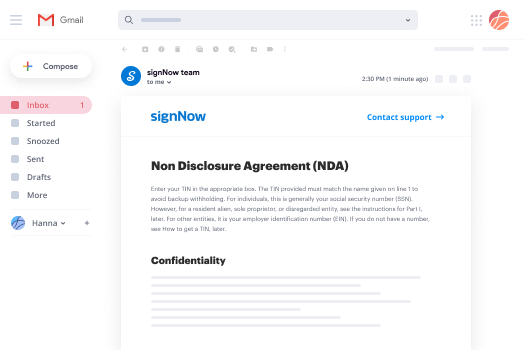
Adopting airSlate SignNow’s electronic signature any company can enhance signature workflows and eSign in real-time, supplying a better experience to consumers and employees. repeat digital signature order in a few simple steps. Our mobile apps make work on the move possible, even while off-line! Sign contracts from any place in the world and close deals quicker.
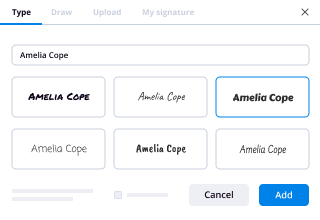
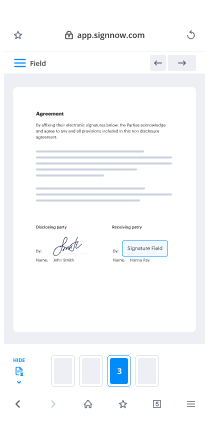
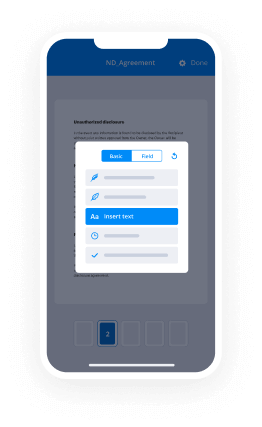
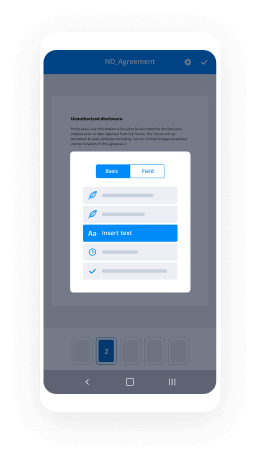
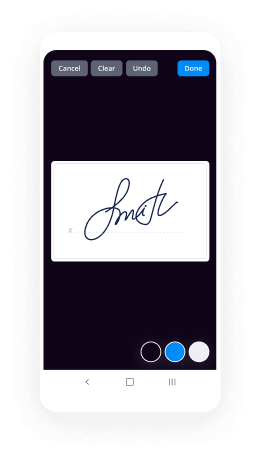
Take a walk-through guide to repeat digital signature order:
- Log in to your airSlate SignNow profile.
- Locate your record in your folders or upload a new one.
- Open the template adjust using the Tools menu.
- Place fillable boxes, add textual content and eSign it.
- Add numerous signees using their emails configure the signing sequence.
- Indicate which individuals will get an signed copy.
- Use Advanced Options to limit access to the record and set an expiry date.
- Click on Save and Close when finished.
In addition, there are more advanced features accessible to repeat digital signature order. List users to your common digital workplace, browse teams, and keep track of teamwork. Numerous consumers all over the US and Europe recognize that a system that brings everything together in one cohesive workspace, is the thing that enterprises need to keep workflows functioning effortlessly. The airSlate SignNow REST API enables you to integrate eSignatures into your app, internet site, CRM or cloud. Check out airSlate SignNow and enjoy faster, easier and overall more productive eSignature workflows!
How it works
airSlate SignNow features that users love
See exceptional results repeat digital signature order with airSlate SignNow
Get legally-binding signatures now!
FAQs
-
How do I add a second signature to a PDF?
Open airSlate SignNow. Click on the Tools menu on the upper right. Expand the Forms section and click Edit. If prompted to auto-detect form fields, click No. Under the Tasks section, click Add New Field > Digital Signature. Drag a rectangle to create the desired size of the signature field. -
How do I do multiple signatures on airSlate SignNow?
Open your document. If you are on a contract type document, skip to step 3. Otherwise, follow these steps: ... Open the People panel. Click Add People. Enter recipient information and assign signer order. Add as many recipients as you wish by clicking Add Another Recipient and set signer order for each. -
Can you have multiple signatures?
The design of a signature is not the binding principal, the binding principal thus the legality of the signature is that it is from the person singing it. No Mather how many different signatures you use, they're equally legal. -
How do I write my signature on a Word document?
Place the cursor in your Word document where you want to insert a signature. Click the Insert tab. Select Signature Line. A menu will appear. Fill out the required fields. Select OK. -
How do you create a signature file?
Suggested clip How to Add a Signature to Any Electronic Document - YouTubeYouTubeStart of suggested clipEnd of suggested clip How to Add a Signature to Any Electronic Document - YouTube -
Does your signature have to be consistent?
All a signature is expected to do is signal that you intend to adopt an agreement, whether it's a purchase, offer of employment, or business transaction. ... \u201cIt doesn't have to be consistent with your signature,\u201d Mann says. -
How do I put multiple signatures on a PDF?
If you have multiple certificates, choose your signing certificate from the. ... Customize the signature appearance to your liking. -
How do I create a multiple signature in airSlate SignNow?
Open airSlate SignNow. Click on the Tools menu on the upper right. Expand the Forms section and click Edit. If prompted to auto-detect form fields, click No. Under the Tasks section, click Add New Field > Digital Signature. Drag a rectangle to create the desired size of the signature field. -
How do I insert multiple signatures in Word?
From the Word ribbon, select the Insert tab and then click Signature Line in the Text group. A Signature Setup pop-up box appears. Enter your information in the text fields and click OK. Double-click the signature line. -
How do I create a signature in airSlate SignNow?
Suggested clip How to Create a Digital Signature in Acrobat - YouTubeYouTubeStart of suggested clipEnd of suggested clip How to Create a Digital Signature in Acrobat - YouTube -
How can I create a digital signature?
Suggested clip *FAST* How to set up a Digital Signature in airSlate SignNow Reader DC ...YouTubeStart of suggested clipEnd of suggested clip *FAST* How to set up a Digital Signature in airSlate SignNow Reader DC ...
What active users are saying — repeat digital signature order
Related searches to repeat digital signature order with airSlate airSlate SignNow
Signature standard
we will now take a look at another digital signature algorithm called digital signature standard digital signature standard was published by national institute of standards and technology as a federal information processing standard this algorithm uses a secure hash algorithm shah we have already learned and the digital signature standard was originally proposed in 1991 and it was revised in 1993 after public feedback we'll take a look at the steps in digital signature so we have a sender we call him user a and we have a receiver who is user b so we have three steps in digital signature standard one is we have to create the public key so that is first step public and private key for user a and the second step is using this private key we need to create a signature a signature is getting created we can call that signature to be r comma s and once when user a wants to send a message to user b you'll be sending that message plus the signature to user b and user b will be validating this signature upon received of this message so that is the third step so these are the three steps we'll go step by step and understand this algorithm i also have an animation for you to understand this better say we have user a and user b they are communicating using an insecure channel it means we have a third party here and hacker listening to their communication the very first step is use array should generate global public key components bqg and a public key so you can consider all these things to be public that is p q g and y and he also selects a private key x so after generation of a public key and a private key is going to share the public key components and the public key why with everyone so this is known to everyone this is in the public domain whereas private key is very secret x is very secret to user a so once when he wants to send a message of ten dollars what he does is he takes the message he now creates this signature arkham is using the private key a private key is involved in creating the digital signature now the message that is the plain message plus the digital signature is sent to our receiver the receiver will take the signature he will use the global public key components and the public key of user a and then he will validate the signature if the signature is valid you can very well be sure that the message is from an authenticated source and the integrity of the message is also maintained so very first thing that we're going to look at is how to generate public key components and how to generate public key and private key for user a and even before going into that we'll take a look at this diagram that is given in your textbooks we'll understand this diagram this diagram conveys the same meaning that we have seen in the last slide we take a look at this so this is the message let's assume message is ten dollars we take the message we feed it to a hash function say sha algorithm and we get this message digest which is small m and we also select the random integer k and we feed it to this signature generation module the other inputs for signature generation module are the public global key components p q g p q and g and the private key that is x so all these inputs are fed into the signature module to generate the signature digital signature r comma s after generating the signature the message ten dollars let's assume is added with the signature right so signature plus the message is sent to the receiver the receiver receives the message ten dollars and he uses the same hash algorithm sha algorithm and then he computes whatever that is h of m h of m is nothing but h of capital m is nothing but the message type just small m so he gets small m and it takes s and r this is the signature that is coming in right so s and r is being fed to the verification module again the receiver also uses the global public key components and public key of user a so with all these things say public key components public key of user a the message digest and then the signature which is which is being fed to the verification module and the digital signature is verified here so we'll now go into the steps of the algorithm we'll first see how to generate global public key components p q and g so p is a prime number and the range of p is between 2 power l minus 1 and 2 power l and it should be anything between 5 to ln 1024 bits so that is the value of l given here so what should be the value of l you consider the value of l to be anything greater than equal to phi 12 ln less than equal to 1024 and p should be selected as a prime number the next value that user a or the center is going to select is q q is a prime divisor of p that is it should be a prime number and it should divide p it should divide p minus 1 i'm sorry q should be a prime divisor of p minus 1 and the value of q should be anything between 2 power 1 5 9 n it should be less than 2 power 160. so the next value that is selected is q q is nothing but a prime divisor of p minus 1 and the value of q should be between 2 power 1 5 9 and 2 power 160 and the third value is g g is being computed as h power p minus 1 by q mod p say we know p and q that is the prime number and the prime divisor of p whereas h is an any integer that lies between 1 and p minus 1 so that is the value of h it can be any integer within this range and another important condition is h power p minus 1 by q mod p should be greater than 1. see if this is not greater than 1 you have to go and select another value for h so these three steps lead us to identifying the global public components pqg what next we have to identify the public key and the private key so let's see how you identify a private key the user's private key x is nothing but a value that is alex between 0 and q q is the prime divisor of p minus 1 so we know that right what is q q is the prime divisor of p minus 1 select the value between 0 and q that becomes x that is the private key of descender and what is this y y is the public key we compute y by using g power x mod p x is the private key g and p are from the public key components that we have already selected so this is p and this is g so using g x and p we can compute the public key so the global public key components are p q and g this is global public key components the public key of the user is y and the private key is x so all these values are computed the keys are ready we look at this animation we'll understand what we have done so user a has computed the global public key components pqg he has also identified a public key y and a private key x so after identifying these things you'll be sharing the public key components and the public key with all of them so that what it means is it is available it is available to the public so after this what next we have to see how this user generates a digital signature how the signature is getting generated using all these components we'll take a look at these steps so generating the signature is what we are going to see so for that he has to select a random number k which lies between 0 and cubed so let's see how we generates r r is nothing but g power this random number mod p mod q we know what is g p q from our global public key components and after he generates r you'll be generating s the next part of the signature s is nothing but k inverse of h this is the hash function so we're going to take the message pass it to a hash function and we are going to add that result with x x is nothing but the private key of the user r we have already generated here mod q so what is this k inverse we know what is k right we know k mod q what is k inverse it is nothing but the multiplicative inverse of k with respect to mod q so k into k inverse mod q should be equal to 1 so we are finding the k inverse here that is it so that's how we compute signature r and s let me repeat that r is equal to g power k mod p mod q g p and q is known from the global public key components k is the random integer that is lx between 0 and q what is s s is nothing but k inverse k inverse is the modular multiplicative inverse of k with respect to mod q and h of m is the hash function the sha algorithm which takes in the message and creates the message digest m and x is the private key of the sender and r is what he computes mod q so now our signature is ready so after the signature is ready this plain text message m will be concatenated with the signature and sent to the receiver now let's see how this receiver validates our message so what all we have accomplished when you take a look at this visualization we have finished finding these three things global public key components public key and private key and now we have also computed this signature signature is also done the next thing is the signature plus the message will be sent to the user b the third step is we have to verify the signature whether the signature is valid so user b will be performing certain steps to verify the signature let's take a look at this look at these steps so these are the steps so what is being sent from our sender say user a is there right whatever he senses he sends the message and the signature are commas so when this is being received at the user's end say the receiver is user b say receiver is user b when it is received at the user's send let us assume that it is received as m dash s dash and r dash so m corresponds to m r dash corresponds to r and s dash corresponds to s so this is how it is being received and how user b validates this signature is it computes these values it takes whatever s that is coming in it finds the inverse of that with respect to mod q we know p q g these are public components and y is also the public key this is known to everyone public components so with s that is coming in so the digital signature that is receiving is r dash and s dash and the message that he is receiving is m dash so using s dash he finds the inverse with respect to mod q q is also known time so that is w the next value it computes is u1 u1 is nothing but the hash take m dash feed it to the hash function sha algorithm and you get the message digest you multiply that with w w is given here and mod q q is again from the public domain now we compute u2 what is u2 u2 is nothing but r r is part of the signature that he has received w is something that is already computed mod q q is again from the public key domain so after computing u1 and u2 you should complete v what is v v is nothing but g per u1 y for u2 mod p the entire thing mod q so do we know all these things what is u1 u1 we have computed just now u2 we have computed what is this g g is from the public key domain what is y y is the public key of the user it's also known to everybody right and what is pp is again from the public key components q is again from the public key components so this is it is very much possible for user b for the receiver to compute b so finally the signature is a valid signature if the value computed b is equal to r dash so it is able to prove that v is equal to the r dash that is r is nothing but part of the signature we have received then the user can very well conclude that the signature is valid this is the digital signature standard algorithm given the references here for p q g x and y just to say that we have already computed this and also r and s i have pasted here just to understand that whatever we are using here r and s has already been computed i hope you all have understood what is the digital signature standard algorithm thank you
Show moreFrequently asked questions
What is needed for an electronic signature?
How do I add signature elements to my PDF so that my recipients can sign it?
How do I sign a PDF with an electronic signature?
Get more for repeat digital signature order with airSlate SignNow
- Print electronically sign Time and Materials Contract
- Prove electronically signed Collaboration Agreement Template
- Endorse digisign Employment Contract
- Authorize signature service Direct Deposit Authorization PDF
- Anneal mark Deed of Trust
- Justify esign Shopify Proposal Template
- Try countersign Financial Consulting Agreement Template
- Add Supply Agreement signatory
- Send Design Quote Template initials
- Fax Church Invitation eSign
- Seal Summer Camp Physical Form esigning
- Password Interior Design Proposal Template digisign
- Pass Hold Harmless (Indemnity) Agreement electronic signature
- Renew Owner Financing Contract countersign
- Test Occupational First Aid Patient Assessment sign
- Require Cooperative Agreement Template electronically signing
- Comment observer signature service
- Boost subscriber signature block
- Call for receiver esign
- Void Remodeling Contract Template template electronically signed
- Adopt Business Separation Agreement template byline
- Vouch Hogwarts Express Ticket template esigning
- Establish Texas Bill of Sale template signature block
- Clear Car Wash Proposal Template template signature service
- Complete Transfer of Pet Ownership template countersign
- Force Freelance Invoice Template template email signature
- Permit RV Bill of Sale template signatory
- Customize Manufacturing and Supply Agreement template initials