Repeat Signed Request with airSlate SignNow
Get the robust eSignature capabilities you need from the solution you trust
Choose the pro service created for pros
Configure eSignature API with ease
Work better together
Repeat signed request, within minutes
Decrease the closing time
Maintain important data safe
See airSlate SignNow eSignatures in action
airSlate SignNow solutions for better efficiency
Our user reviews speak for themselves






Why choose airSlate SignNow
-
Free 7-day trial. Choose the plan you need and try it risk-free.
-
Honest pricing for full-featured plans. airSlate SignNow offers subscription plans with no overages or hidden fees at renewal.
-
Enterprise-grade security. airSlate SignNow helps you comply with global security standards.

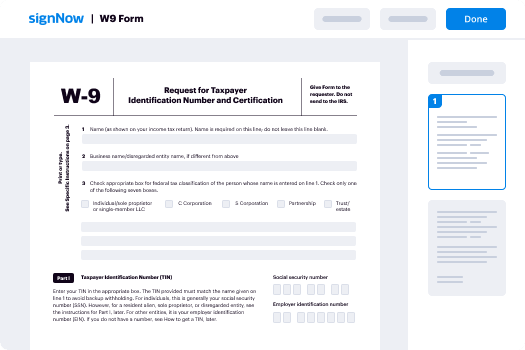
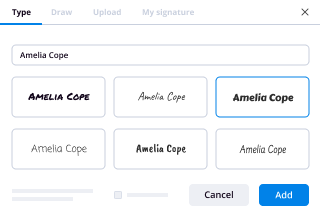
Your step-by-step guide — repeat signed request
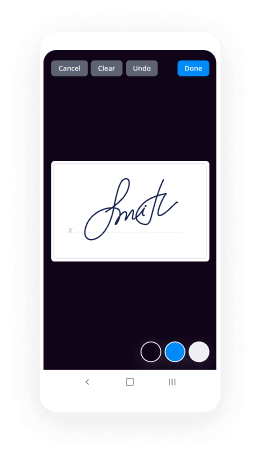
Adopting airSlate SignNow’s eSignature any organization can speed up signature workflows and sign online in real-time, providing a greater experience to clients and employees. repeat signed Request in a few simple actions. Our handheld mobile apps make operating on the run possible, even while off-line! Sign documents from any place worldwide and make deals in no time.
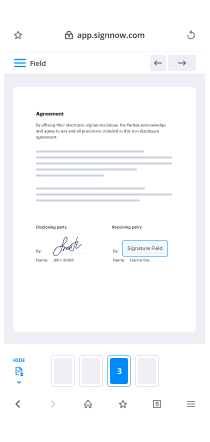
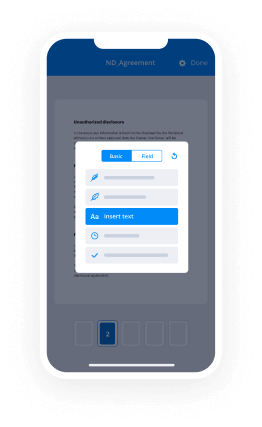
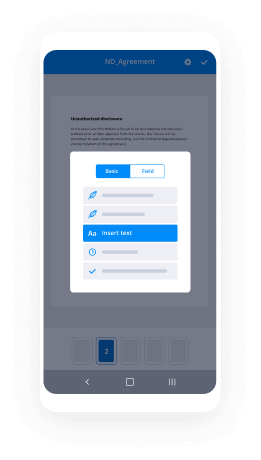
Take a walk-through guideline to repeat signed Request:
- Log in to your airSlate SignNow profile.
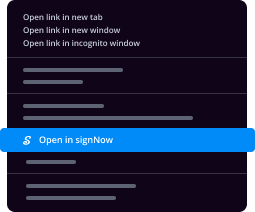
- Locate your needed form within your folders or import a new one.
- Open the document adjust using the Tools list.
- Drag & drop fillable fields, type text and sign it.
- List numerous signers via emails configure the signing sequence.
- Choose which individuals will receive an signed copy.
- Use Advanced Options to reduce access to the record and set an expiry date.
- Click Save and Close when done.
Moreover, there are more innovative tools accessible to repeat signed Request. List users to your collaborative work enviroment, view teams, and keep track of cooperation. Millions of people across the US and Europe recognize that a system that brings everything together in one holistic work area, is what organizations need to keep workflows working easily. The airSlate SignNow REST API enables you to embed eSignatures into your app, website, CRM or cloud. Check out airSlate SignNow and get quicker, smoother and overall more effective eSignature workflows!
How it works
airSlate SignNow features that users love
See exceptional results repeat signed Request with airSlate SignNow
Get legally-binding signatures now!
FAQs
-
What is signed request?
Signing Requests. OAuth defines a method for validating the authenticity of HTTP requests. This method is called Signing Requests. Instead of sending full credentials (specifically passwords), OAuth uses digital signatures with each request. -
How do I sign AWS requests?
Task 1: Create a Canonical Request for Signature Version 4. ... Task 2: Create a String to Sign for Signature Version 4. ... Task 3: Calculate the Signature for AWS Signature Version 4. ... Task 4: Add the Signature to the HTTP Request. -
What is aws4?
aws4. A small utility to sign vanilla Node. js http(s) request options using Amazon's AWS Signature Version 4. ... It also provides defaults for a number of core AWS headers and request parameters, making it very easy to query AWS services, or build out a fully-featured AWS library. -
What is API signing?
The signing key is your API account's percent-encoded secret key which should be kept secret. Note that you should never explicitly transfer it and noone should ask you to type it anywhere. This key should be \u201cknown\u201d by your application only. -
How do I use Amazon API?
On the Amazon Associates page, under Tools, choose Product Advertising API. You can also use the table at the bottom of this page to locate the Product Advertising API URL for your locale. Choose Sign Up Now. Use the primary or secondary email address in your Associates account to sign in. -
How do I sign an API request?
Sort request parameters alphabetically (e.g. foo=1, bar=2, baz=3 sorts to bar=2, baz=3, foo=1) Concatenate in order your API secret key and request name-value pairs (e.g. SECRETbar2baz3foo1) Calculate the signature as the MD5 hash of this string. -
How do I use sign request?
Suggested clip How To Get Documents Signed Online Using airSlate SignNow - YouTubeYouTubeStart of suggested clipEnd of suggested clip How To Get Documents Signed Online Using airSlate SignNow - YouTube -
How do I create an AWS signature?
Use the canonical request and additional metadata to create a string for signing. Derive a signing key from your AWS secret access key. Then use the signing key, and the string from the previous step, to create a signature. Add the resulting signature to the HTTP request in a header or as a query string parameter. -
What is a canonical request?
Overview. A canonical request is a string that represents a specific HTTP request to Cloud Storage. You use a canonical request along with a cryptographic key, such as an RSA key, to create a signature that is then included in the actual request as authentication. -
What is Oauth_nonce?
The oauth_nonce parameter is a unique token your application should generate for each unique request. Twitter will use this value to determine whether a request has been submitted multiple times. -
What is token secret?
A value used by the Consumer to gain access to the Protected Resources on behalf of the User, instead of using the User's Service Provider credentials. Token Secret: A secret used by the Consumer to establish ownership of a given Token. -
What is a token request?
Token Request. 16.3. While the device is waiting for the user to complete the authorization flow on their own computer or phone, the device meanwhile begins polling the token endpoint to request an access token. The device makes a POST request with the device_code at the rate specified by interval . -
What does access token mean?
An access token is an object that describes the security context of a process or thread. The information in a token includes the identity and privileges of the user account associated with the process or thread. -
How is a token generated?
Most importantly, tokens are machine-generated. The user arrives at the target domain. They enter their login credentials. The server verifies the match and lets them in. The user is authenticated to access that domain.
What active users are saying — repeat signed request
Make signed request
hello everyone my name is Barbour Magida I'm a software engineer in this short lecture series I will walk you through the process of creating sign requests to API gateway the technologies which I will use are typescript nor GS angular framework serverless framework AWS lambda and a Tobias API gateway at the end of this lecture series you would be able to answer the following questions how to create sign requests to API gateway how to create lambdas in AWS console how to create API is using AWS API gateway console how to create lambdas using serverless framework how to deploy an API using several s and how to create a basic angular application so let's start learning I will start by discussing the theory behind Amazon API gateway sign request then I will go to the AWS console and create API is and lambdas and give demos of different kind of services so let's start so this is the content which I will discuss in this lecture series so installed with with the API gateway sign request I'll give a brief introduction and then I will give different kind of steps how to generate the sign API gateway requests then I'll discuss the architecture of services which I will use in my demo and I will give a brief description of the application and the workflow which would be used for the sign API requests then I will go to AWS lambda console and create lambda functions then after that I'll go to API gateway console and then I'll create API is there and then I'll integrate lambda functions of it those api's furthermore I will demonstrate sign request in postman then I'll use a front-end angular application to demonstrate the sign request so here in this step I will create the angular application and then for creation of the authorization header I will use typescript nodejs and then I've used from a server last framework to deploy that API into AWS then I'll demonstrate the sign request in angular application so what are the API gateways sign requests so whenever you send a request to API gateway you basically sign the request so that AWS can identify who has sent this request so for the identification you actually create a digital signature of this request using the secret key and the access key and then that digital signature is part of the header of the request and then you send it to API gateway so let's understand this using this example for example here we have an application and we want to hit the API gateway and retrieve some item from that so whenever we send this request so we wanna sign this request so that means like we we want to create a digital signature of this request so this digital signature would be created using the secret key the access key this method and some of the parameter from the URL that is like canonical URI canonical query parameters hostname and Amazon date there is a specific format of that so then you create a hash using some cryptographic function and then you add that hash into the authorization header of this request and then you send this request to API gateway once API gate may receive that request so it recalculates that hash and then compare the hash which is sending the authorization header if both are same then the except then the request is accepted otherwise it is rejected I hope it will not too much confusing if it is so don't worry I will explain it again and again so the AWS documentation has divided design requests into different steps so I will go over different steps so here are these steps so first is to create a canonical request then create a string to sign then calculate the signature and finally add the authorization header to the request so let's go to each step in the next slides so in the first step the creation of the canonical request so basically whenever an HTTP request is sent to API gate where this is something like that so it has a method then it has a URL that has a hostname and then the query parameters then header like different kind of headers so if we want to convert it to the canonical request so how would we do that so in the AWS documentation they have given some pseudo code so the canonical request basically that is equal to HTTP request method that is in this case the GAT one and then the next line and then canonical URI the canonical URI is basically the part after comm and before this question mark so if there is any a path there so we added here in the canonical URI in this case it is empty so but we will use the forward slash / hair and the canonical query string is basically everything after the canonical URI that is a starting from action until our hair so the canonical headers those are all the headers which are included in the request so in this case those are host content type and XML on date and the sign headers are basically the strings of the titles like the host content type and XML on date but in the lower cases and those are separated by semicolons and at the end the the hash is created of the payload if any payload is included in the request then we create a hash using some cryptographic hash function and this is the example canonical request so here we have this method named get then this one is the canonical URI this one is a canonical query string this is canonical headers and this one is the sign headers and this one is hash and finally we create the hash of whole of the canonical requests using the hash function which would be used in the next step so the second step is create a string to sign so this is the pseudocode for string to sign that will use the algorithm the request date and time credential scope and the hash canonical request which is basically created in the previous step so here is the example so the algorithm is a WS 4-h Mac sha-256 in this case the request date and time is in this format and the credential scope it has a date region service name and AWS for request which is the basically signature version for and then at the end the hash canonical request which is created in the previous step so the next step is calculate the signature for calculating the signature we create the hash of different parameters so we will start from the secret key and then using the secret key we'll calculate the date then using both of date and secret key we calculate the region then we calculate service using all of the above and at the end we calculate signing using the K service region and date and secret and finally for a signature we use this string to sign and drive signing key so and finally we get this hash for the signature and in the fourth step we add all of the above information in the authorization header so this is the pseudocode for that so authorization here we add the algorithm name then the credential we use access key ID then the credential scope and the sign header we use all of the sign headers and at the end we add the signature over here which we calculated in the previous step so this is the example of the authorization header so it has this algorithm AWS for H max sha-256 for the credential access key ID and then selected credential scope date the region service name AWS for request and then for the sign headers like all of the header titles in small cases separated using the semicolon and at the end signature is added there so in the next slide I will discuss the architecture of this application that I would use for API gave me a sign request so I will use the angular application on the front end that that basically will call the API gateway it will send a HTTP requests and the API gateway is integrated with with two lambda functions both are written in OGS so there would be one get request that will interact with the get item lambda function and there is another request that would be the post request that we integrate with the save item lambda function so whenever we call the get item so first there would be another API so that would be the authorization API and the angular application will call that API and then get the header using another lambda function so then whenever this authorization header is returned then this authorization header is used as a header of this get item request and the same thing is done with this save item
Show moreFrequently asked questions
What is needed for an electronic signature?
How do I sign and scan a PDF?
What counts as an electronic signature?
Get more for repeat signed Request with airSlate SignNow
- Print electronically sign Certificate of Liability Insurance
- Prove electronically signed Software Sales Proposal Template
- Endorse digisign Advertising Agency Agreement Template
- Authorize electronically sign Service Agreement
- Anneal mark Client Supply Order Invoice
- Justify esign Employment Verification Letter
- Try countersign Event Marketing Proposal Template
- Add Insuring Agreement autograph
- Send Housekeeping Contract Template digital sign
- Fax Promotion Acceptance Letter initial
- Seal Concert Press Release electronically sign
- Password Severance Agreement Template countersignature
- Pass Purchase Order digital signature
- Renew Real Estate for Sale by Owner signed
- Test Creative Brief digi-sign
- Require Intellectual Property Sale Agreement Template esign
- Comment undersigned mark
- Champion awardee electronically signing
- Call for patron sign
- Void Privacy Policy template electronic signature
- Adopt Funding Agreement template signed electronically
- Vouch Concert Ticket template electronically sign
- Establish Simple Medical History template electronically signing
- Clear Construction Proposal Template template mark
- Complete Foster Application template signed
- Force Articles of Incorporation Template template eSignature
- Permit Gala Reservation Confirmation Letter template autograph
- Customize Bill of Sale template digital sign