Reveal Digital Signature Order with airSlate SignNow
Get the powerful eSignature features you need from the company you trust
Select the pro platform made for pros
Configure eSignature API with ease
Work better together
Reveal digital signature order, within a few minutes
Cut the closing time
Maintain important data safe
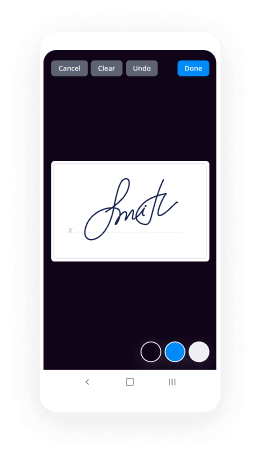
See airSlate SignNow eSignatures in action
airSlate SignNow solutions for better efficiency
Our user reviews speak for themselves






Why choose airSlate SignNow
-
Free 7-day trial. Choose the plan you need and try it risk-free.
-
Honest pricing for full-featured plans. airSlate SignNow offers subscription plans with no overages or hidden fees at renewal.
-
Enterprise-grade security. airSlate SignNow helps you comply with global security standards.

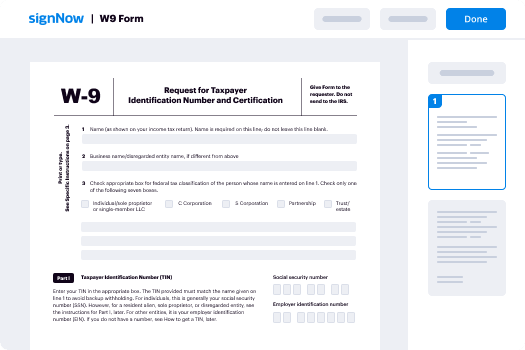
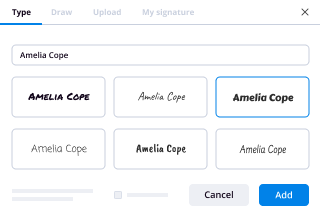
Your step-by-step guide — reveal digital signature order
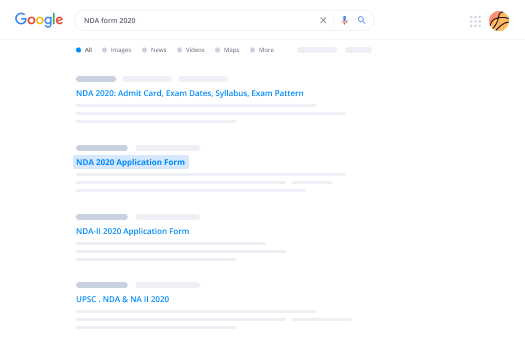
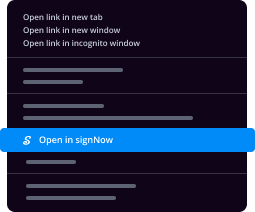
Employing airSlate SignNow’s electronic signature any company can increase signature workflows and sign online in real-time, giving an improved experience to consumers and workers. reveal digital signature order in a couple of easy steps. Our mobile apps make work on the go possible, even while off the internet! eSign contracts from anywhere in the world and close deals quicker.
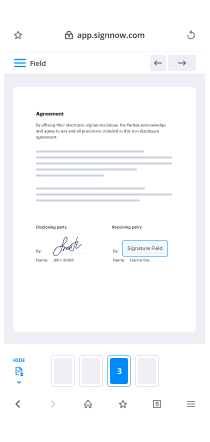
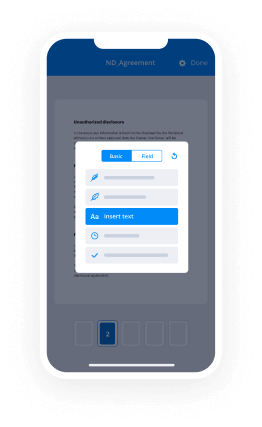
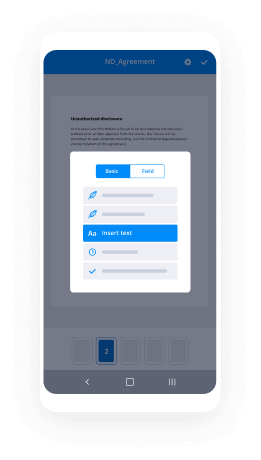
Follow the walk-through instruction to reveal digital signature order:
- Log in to your airSlate SignNow account.
- Find your needed form in your folders or upload a new one.
- Access the template adjust using the Tools list.
- Place fillable areas, add textual content and sign it.
- Add multiple signees via emails configure the signing order.
- Choose which recipients will receive an signed version.
- Use Advanced Options to reduce access to the document and set up an expiration date.
- Click on Save and Close when completed.
Moreover, there are more innovative features open to reveal digital signature order. Add users to your shared digital workplace, browse teams, and monitor teamwork. Numerous users across the US and Europe concur that a solution that brings everything together in a single holistic enviroment, is what companies need to keep workflows functioning efficiently. The airSlate SignNow REST API enables you to embed eSignatures into your application, internet site, CRM or cloud storage. Try out airSlate SignNow and enjoy faster, smoother and overall more effective eSignature workflows!
How it works
airSlate SignNow features that users love
See exceptional results reveal digital signature order with airSlate SignNow
Get legally-binding signatures now!
FAQs
-
How do you decrypt a digital signature?
Suggested clip Hashing Encryption Decryption Digital Signature Signing ... - YouTubeYouTubeStart of suggested clipEnd of suggested clip Hashing Encryption Decryption Digital Signature Signing ... - YouTube -
How do you create a digital signature in cryptography?
To create a digital signature, the signing software creates a one-way hash of the data to be signed. The private key is then used to encrypt the hash. This encrypted hash, plus other information like the hashing algorithm used, is the digital signature. -
How do I create a digital signature using Cryptool?
Suggested clip How to use CrypTool for creating the digital signature for documents ...YouTubeStart of suggested clipEnd of suggested clip How to use CrypTool for creating the digital signature for documents ... -
What is digital signature in cryptography?
Cryptography Digital signatures. ... Digital signature is a cryptographic value that is calculated from the data and a secret key known only by the signer. In real world, the receiver of message needs assurance that the message belongs to the sender and he should not be able to repudiate the origination of that message. -
What is the difference between digital signature and encryption?
As far as I understand in public-key cryptography one encrypt with a public key and decrypt with a private key. ... So, the way digital signature works is that the content of a certificate is hashed and then "signed" with a private key. The signature is verified then with the corresponding public key. -
What is a digital signature and how does PKI create a digital signature?
Digital signatures, like handwritten signatures, are unique to each signer. Digital signature solution providers, such as airSlate SignNow, follow a specific protocol, called PKI. PKI requires the provider to use a mathematical algorithm to generate two long numbers, called keys. One key is public, and one key is private. -
How is a hash function related to a digital signature?
Hashing is one of the core elements of a digital signature system. The process of hashing involves transforming data of any size into a fixed-size output. ... When combined with cryptography, the so-called cryptographic hash functions can be used to generate a hash value (digest) that acts as a unique digital fingerprint. -
What is the difference between a hash and a digital signature?
A hash is used to only verify the message integrity - if a message changes, the hash of a message will change, too. Hashing is not used to authenticate the sender. ... A digital signature typically includes a hash, subsuming hash functionality. -
What are the functions of a digital signature?
Simply put, a digital signature is your electronic fingerprint. It lets you sign a document electronically and it validates the signer. It is a mathematical code that authenticates the document from the sender and ensures the document remains unaltered on signNowing the recipient. -
What are the characteristics of digital signatures?
A common digital signature generally owns characteristics as follows: Creditability: the receiver of the document believes the authenticity of the digital signature on the document and that the signer agrees its contents. Unforgeability: no one can forge the signer's digital signature. -
What is the use of digital signature?
A digital signature is an electronic form of a signature that can be used to authenticate the identity of the sender of a message or the signer of a document, and also ensure that the original content of the message or document that has been sent is unchanged. -
What are three uses for digital signatures?
Uses of digital signatures Digital signatures are used to meet three important goals of information security: integrity, authentication, and non-repudiation. -
What is digital signature and how it works?
Digital Signature is a process that guarantees that the contents of a message have not been altered in transit. When you, the server, digitally sign a document, you add a one-way hash (encryption) of the message content using your public and private key pair. -
How does digital signature look like?
When you click "sign", a unique digital fingerprint (called a hash) of the document is created using a mathematical algorithm. ... The hash is encrypted using the signer's private key. The encrypted hash and the signer's public key are combined into a digital signature, which is appended to the document. -
Why digital certification and its signature is important?
Digital signature is used to verify authenticity, integrity, non-repudiation ,i.e. it is assuring that the message is sent by the known user and not modified, while digital certificate is used to verify the identity of the user, maybe sender or receiver.
What active users are saying — reveal digital signature order
Related searches to reveal digital signature order with airSlate airSlate SignNow
Digital signature alcohol inventory
so the problem is that in real documents and RS a the same signature can be applied to multiple documents what we need is a signature unique to a specific document and since alcohol changes the key for every message let's see if we can use L Kamal for digital signatures so remember to set up an alcohol system Alice announces a public base a and a public modulus n if Alice involved want to communicate Alice chooses a private expert an axe and sends Picon grant aid power X mod n to Bob Bob chooses a private exponent Y and sends Q Congress a to power Y mod n to Alice Alice computes K kagura to Q to the X Bob computes K congruent to Pina the Y and messages M can be encrypted as K M mod n and again Alice can prove her identity by showing she knows acts and she could do this by announcing X but this reveals too much information and so Alice wants to do two things sure that she knows X and tie the X to a specific message m and here's an important consideration because L kemal relies on destroying x and y the private exponents after the communication she can't rely on X or Y after signing the document and this leads to a rather odd situation Alice needs to prove her identity by revealing that at one time she knew the value of X even though she might not know it currently and we might proceed as follows since X is a power we might consider making the message M a power as well as this suggests that a to the M will play a role in alice's signature let's think about that a little more hello Kamal relies on Alice and Bob providing half keys to each other and this suggests we can implement an alcohol signature system by having Alice provide two half signatures s1 s2 that combine to produce a to power M since Alice also has to establish your identity by showing she knows X we might try to send s1 congruent 8 power X and s to congruent to a to power M minus X that way when we multiply s 1 by s 2 we get 8 power M except this doesn't work since Alice already communicated a to power X that's the half key she sent to Bob then Eve can find a to power M minus X simply by solving a to power M congra to s1 s2 mod n so let's think about that a little more remember the security of alikum all relies on a difficulty of solving the DLP suppose Alice chooses a new value of K with s1 congruent a 2 power K mod n Alice could then use her unique knowledge of K and X and the message m to produce the second part of a half key so we know that 8 power M we can write that as a 2 power K times a 2 power M minus K but this doesn't incorporate alice's other exponent X so we might use a to power M congruent to a to power KX times a 2 power M minus KX advil rearrange this a little bit so keep in mind that the things that Bob knows Bob knows a the public base and M the message that Alice is supposed to sign unfortunately Bob can't compute the right-hand side without knowing the value of X and so even if Alice sends him s 1 he can't verify her identity well let's see what else we can do how about instead of multiplying the two keys suppose we exponentiate them as before we'll at s1 be equal to a 2 power K for some random K and what we want is for a 2 power M to be congruent to ass 1 to power s2 or rearranging if we take s 2 to be equal to K inverse M then this expression a to power K to power s 2 becomes and this gives us at s 1 s 2 that will verify the message and now we have something that relies on Alice's unique knowledge of K except it doesn't incorporate X well let's try one more thing so again we'll let s one be a 2 power K and this time let's just consider s 1 2 power s 2 by itself that's going to be a 2 power K 2 power s 2 and s 2 will want that to include K inverse well what that to include em and we'll want that to include X and so we'll let s to be K inverse times the quantity M minus s 1 X where we'll see in a moment why we need that s 1 there and so that means this s 1 2 power s 2 well that's going to be a 2 power K times K inverse M minus s 1x rearranging things a little bit this is the same as a to power M times a to power minus s1 X but remember p alice's half key which she sent out to bob is equal to a 2 power X and so this can be rewritten as a 2 power M P to power minus s1 we'll rearrange that a little bit remember this is s 1/2 power s to Congress 8 power M P to power minus s 1 multiplying by P to power s 1 on both sides gives us and so this expression over here on the left is a to power M now remember s 1 and s 2 rely on this number K that Alice chose this number X that Alice chose to form her half key and the message m and so only Alice can provide s 1 and s 2 that make this true for this particular document and this gives us the el Kamal digital signature scheme Alice has alcohol system with public base a public modulus and and Bob one sir decide message M so Alice picks X and evaluate speak on grant aid power X mod n which is her half key for communication with Bob Alice also picks a new K and evaluates s one concurrent eighth power K mod n allison evaluates k inverse M minus s1 X mod fee of n and this has to be mod fee of n because if you look at where s two shows up its an exponent mod n and remember exponents mod n can be reduced mod fee of n and so for document M with encryption half key P her signed document is going to be s 1 s 2 and to verify this Bob checks first V Concord to P to power s 1 s 1 to power s to mod n and also a 2 power M mod n if V is equal to W then the message is genuine and legitimately signed
Show moreFrequently asked questions
What is needed for an electronic signature?
How do I add signature elements to my PDF so that my recipients can sign it?
How do I eSign a PDF on a PC?
Get more for reveal digital signature order with airSlate SignNow
- Print electronically sign Commercial Sublease Contract
- Prove electronically signed Membership Agreement Template
- Endorse digisign Manufacturing Contract
- Authorize signature service Customer Satisfaction Survey
- Anneal mark Eviction Notice
- Justify esign Product Sales Proposal Template
- Try countersign Web Design Agreement Template
- Add Supply Agreement mark
- Send Design Quote Template signed
- Fax Church Invitation digi-sign
- Seal Summer Camp Physical Form digital sign
- Password Interior Design Proposal Template initial
- Pass Hold Harmless (Indemnity) Agreement signature
- Renew Owner Financing Contract countersignature
- Test Occupational First Aid Patient Assessment digital signature
- Require Cooperative Agreement Template electronically signed
- Comment observer electronically sign
- Boost subscriber signed electronically
- Call for receiver electronic signature
- Void Gardening Contract Template template eSignature
- Adopt Business Separation Agreement template autograph
- Vouch Hogwarts Express Ticket template digital sign
- Establish Texas Bill of Sale template signed electronically
- Clear Car Wash Proposal Template template electronically sign
- Complete Transfer of Pet Ownership template countersignature
- Force Freelance Invoice Template template electronically signing
- Permit RV Bill of Sale template mark
- Customize Manufacturing and Supply Agreement template signed