Sign Certificate Made Easy
Do more online with a globally-trusted eSignature platform
Outstanding signing experience
Trusted reporting and analytics
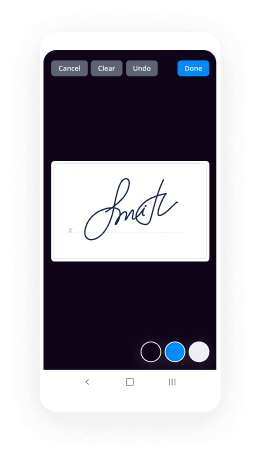
Mobile eSigning in person and remotely
Industry regulations and conformity
Sign certificate, faster than ever
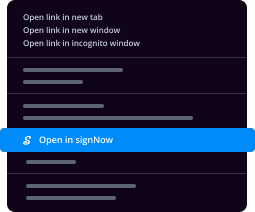
Useful eSignature extensions
See airSlate SignNow eSignatures in action
airSlate SignNow solutions for better efficiency
Our user reviews speak for themselves






Why choose airSlate SignNow
-
Free 7-day trial. Choose the plan you need and try it risk-free.
-
Honest pricing for full-featured plans. airSlate SignNow offers subscription plans with no overages or hidden fees at renewal.
-
Enterprise-grade security. airSlate SignNow helps you comply with global security standards.

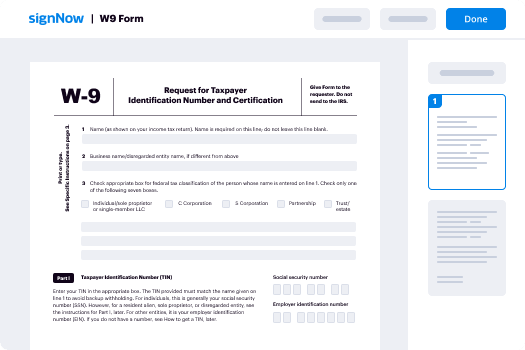
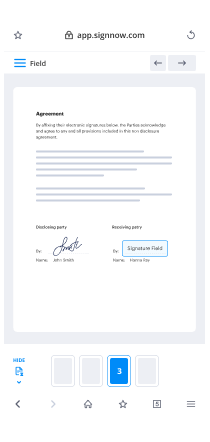
Your step-by-step guide — sign certificate
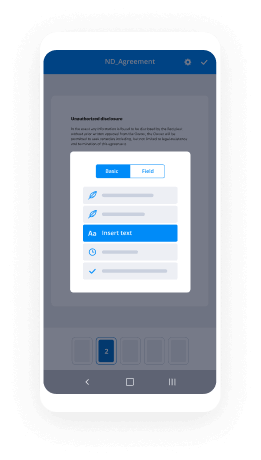
Adopting airSlate SignNow’s electronic signature any company can enhance signature workflows and sign online in real-time, supplying a greater experience to consumers and workers. Use sign certificate in a couple of simple actions. Our mobile-first apps make operating on the run possible, even while off the internet! eSign signNows from any place in the world and make trades quicker.
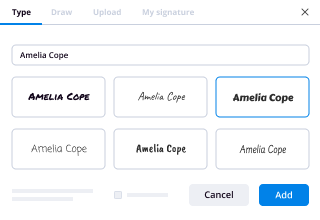
Keep to the walk-through instruction for using sign certificate:
- Log on to your airSlate SignNow profile.
- Locate your document in your folders or import a new one.
- Open the template adjust using the Tools menu.
- Drag & drop fillable boxes, add text and sign it.
- List multiple signers via emails and set the signing sequence.
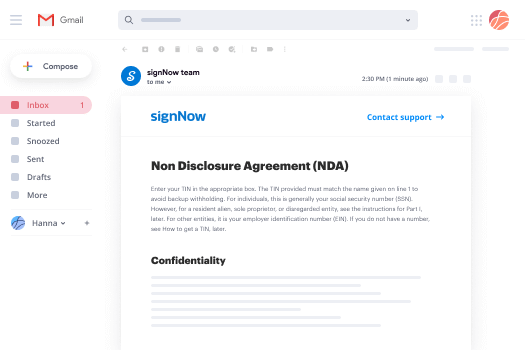
- Specify which users will receive an executed version.
- Use Advanced Options to limit access to the document and set an expiration date.
- Press Save and Close when completed.
In addition, there are more enhanced capabilities open for sign certificate. Add users to your collaborative workspace, browse teams, and monitor collaboration. Numerous customers across the US and Europe agree that a solution that brings everything together in one cohesive digital location, is exactly what organizations need to keep workflows performing easily. The airSlate SignNow REST API allows you to integrate eSignatures into your application, website, CRM or cloud storage. Try out airSlate SignNow and get faster, smoother and overall more efficient eSignature workflows!
How it works
airSlate SignNow features that users love
See exceptional results sign certificate made easy
Get legally-binding signatures now!
What active users are saying — sign certificate
Help Me With Install eSignature in SalesForce
how does HTTP work I'm planning on releasing a couple of new videos on securing micro-services with HTTPS and also about how you can use kubernetes to automatically obtain the TLS certificates required for HTTPS and for that I think it makes sense if everyone understands how HTTPS works this video won't get too technical I've simplified a couple of concepts so it will fit in a shorter video so after the end of this you might not be able to implement all the required algorithms from scratch but you should be able to understand how the common tools that are out there what they do and how you can use them to implement HTTPS protection for your micro services oftentimes I've experienced that developers treat this whole HTTP communication thing as that sort of black box they don't even want to try to understand because it sounds so complicated but it's actually pretty simple and I'd like to show you just how it works with this video so let's start with a couple of prerequisites whenever you hear HTTP and there's cryptography involved it almost sounds very complex and very mathematical but it doesn't really have to be complex at all you just need to trust that public key cryptography and signature works now if you're saying what is public key cryptography and signature it's basically a couple of very simple mathematic functions that only work in one way or that are much easier to compute in one way than in another way but you should trust these two principles you should trust that any message that has been encrypted with Bob's public key and Bob's public key is public it's out there for everyone can only be decrypted with Bob's private key so basically that means only Bob because he's the only owner of his private key can decrypt this message even though it can be publicly distributed and everyone can listen to it but no one can do anything with it because they just see some random bytes so that was the public key cryptography part and then there's also the signature part so anyone who is access to Alice's public key can verify that a message could only have been created by someone with access to Alice's private key so basically this means anyone on the Internet even though they don't know Alice's private key only Alice knows her private key can verify that a message was actually sent by Alice and in the background there's basically just a bit of multiplication and modulus calculation going on but you don't have to worry about that at all just take this as given based on this we can now start with your browser and let's say you want to access youtube.com so the first thing your browser does it tells the internet give me youtube.com this is of course very simplified in a background there'll be DNS requests going on so you can resolve that name to...
Show more