Signature Protocol Made Easy
Do more online with a globally-trusted eSignature platform
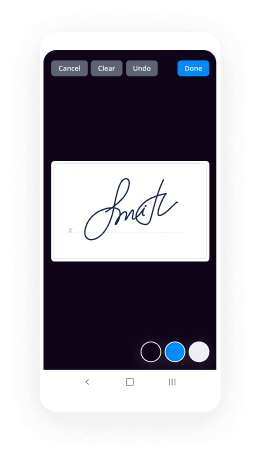
Outstanding signing experience
Reliable reports and analytics
Mobile eSigning in person and remotely
Industry regulations and conformity
Signature protocol, faster than ever
Handy eSignature add-ons
See airSlate SignNow eSignatures in action
airSlate SignNow solutions for better efficiency
Our user reviews speak for themselves






Why choose airSlate SignNow
-
Free 7-day trial. Choose the plan you need and try it risk-free.
-
Honest pricing for full-featured plans. airSlate SignNow offers subscription plans with no overages or hidden fees at renewal.
-
Enterprise-grade security. airSlate SignNow helps you comply with global security standards.

Your step-by-step guide — signature protocol
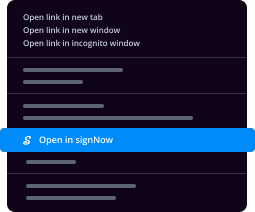
Adopting airSlate SignNow’s eSignature any business can accelerate signature workflows and sign online in real-time, giving a greater experience to consumers and workers. Use signature protocol in a couple of simple actions. Our mobile apps make work on the run achievable, even while off-line! eSign documents from anywhere in the world and make deals faster.
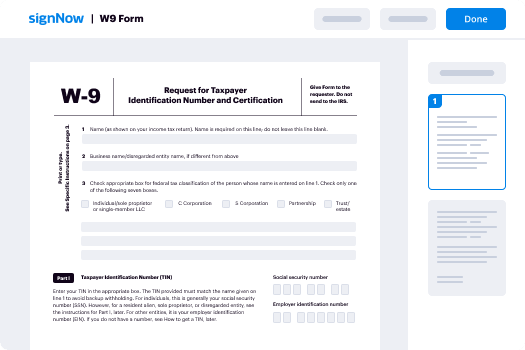
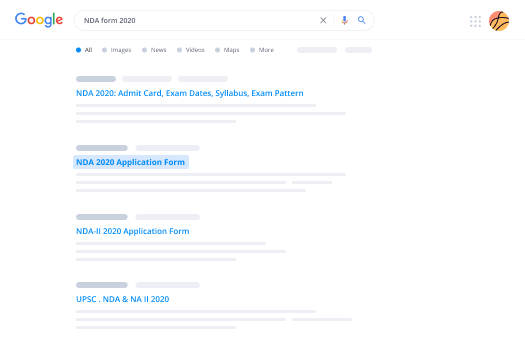
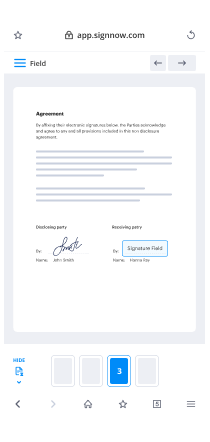
Take a step-by-step guide for using signature protocol:
- Log in to your airSlate SignNow account.
- Locate your document within your folders or upload a new one.
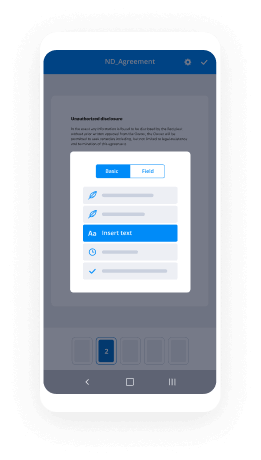
- Open up the template and edit content using the Tools list.
- Place fillable areas, type textual content and eSign it.
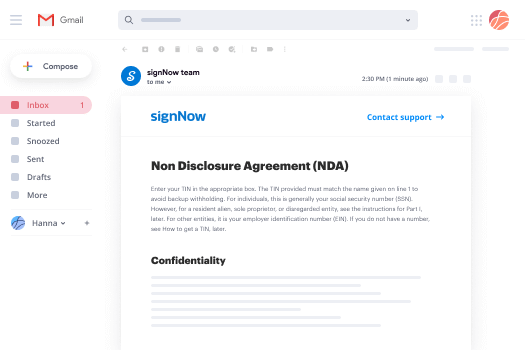
- Add numerous signers via emails configure the signing order.
- Indicate which users will receive an executed doc.
- Use Advanced Options to limit access to the template and set an expiry date.
- Click Save and Close when finished.
Furthermore, there are more extended functions accessible for signature protocol. List users to your shared work enviroment, browse teams, and monitor cooperation. Millions of customers across the US and Europe concur that a system that brings people together in one cohesive workspace, is what organizations need to keep workflows performing smoothly. The airSlate SignNow REST API allows you to integrate eSignatures into your app, internet site, CRM or cloud storage. Check out airSlate SignNow and get quicker, easier and overall more effective eSignature workflows!
How it works
airSlate SignNow features that users love
See exceptional results signature protocol made easy
Get legally-binding signatures now!
FAQs
-
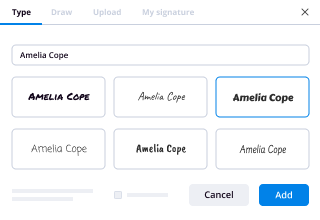
How do you sign a digital signature?
Go to our eSign tool. Upload the document you wish to sign. Place a signature, and optionally add text to your document. Click 'Apply' -
How do I sign a digital signature in airSlate SignNow?
Choose the Fill & Sign tool from the airSlate SignNow dashboard and open the document you need to sign. Click the Sign tool, then Add Digital Signature. Please note that digital signatures must be enabled by your airSlate SignNow administrator. Select cloud-based digitial ID certificate, then click Apply. -
How do I create a digital signature?
Click the link. ... Agree to electronic signing. ... Click each tag and follow the instructions to add your digital signature. Verify your identity and follow the instructions to add your digital signature. -
How can I write my name in signature form?
Suggested clip The Best Signature Examples with 10 Techniques | How to Draw ...YouTubeStart of suggested clipEnd of suggested clip The Best Signature Examples with 10 Techniques | How to Draw ... -
How do you create an electronic signature?
Android: Use airSlate SignNow Fill & Sign It can also capture pictures of airSlate SignNow documents with your camera so you can sign them electronically. After installing the app, you can open PDF documents in the app and tap the signature button to sign them. -
How do I create a free electronic signature?
Create an airSlate SignNow account. It only takes a few seconds. Upload your document to your account. ... Select who needs to sign your document. ... Prepare the document for signature. ... Sign the document or send it out for signature. -
How do I insert a signature in Excel 2013?
Step 1: Open your spreadsheet in Excel 2013. Step 2: Click the Insert tab at the top of the window. Step 3: Click the Signature Line button in the Text section of the ribbon. Step 4: Fill in each of the lines on this window that you wish to include with the signature line, then click the OK button. -
How do I create a multiple digital signature in Excel?
Click the File tab. Click Info. Under Permissions, click Protect Document, Protect Workbook or Protect Presentation. Click Add a Digital Signature. Read the Word, Excel, or PowerPoint message, and then click OK. In the Sign dialog box, in the Purpose for signing this document box, type the purpose. Click Sign. -
How do you create an electronic signature on a Mac?
In the Mail app on your Mac, choose Mail > Preferences, then click Signatures. In the left column, select the email account where you want to use the signature. ... Click the Add button below the middle column. In the middle column, type a name for the signature. ... In the right column (the preview), create your signature. -
How do I insert a signature in Excel 2010?
Suggested clip Microsoft Excel 2010: Add Digital Signature - YouTubeYouTubeStart of suggested clipEnd of suggested clip Microsoft Excel 2010: Add Digital Signature - YouTube -
How do I sign my RSA message?
RSA Digital Signatures To sign a message m, just apply the RSA function with the private key to produce a signature s; to verify, apply the RSA function with the public key to the signature, and check that the result equals the expected message. That's the textbook description of RSA signatures. -
How do you sign a message with a private key?
So: To generate a signature, make a hash from the plaintext, encrypt it with your private key, include it alongside the plaintext. To verify a signature, make a hash from the plaintext, decrypt the signature with the sender's public key, check that both hashes are the same. -
How long is RSA signature?
PKCS#1, "the" RSA standard, describes how a signature should be encoded, and it is a sequence of bytes with big-endian unsigned encoding, always of the size of the modulus. This means that for a 2048-bit modulus, all signatures have length exactly 256 bytes, never more, never less. -
How does RSA key fob work?
The RSA SecurID authentication mechanism consists of a "token" \u2014 either hardware (e.g. a key fob) or software (a soft token) \u2014 which is assigned to a computer user and which creates an authentication code at fixed intervals (usually 60 seconds) using a built-in clock and the card's factory-encoded almost random key ( ... -
How is RSA encryption calculated?
Select primes p=11, q=3. n = pq = 11.3 = 33. phi = (p-1)(q-1) = 10.2 = 20. Choose e=3. Check gcd(e, p-1) = gcd(3, 10) = 1 (i.e. 3 and 10 have no common factors except 1), ... Compute d such that ed \u2261 1 (mod phi) i.e. compute d = (1/e) mod phi = (1/3) mod 20. ... Public key = (n, e) = (33, 3)
What active users are saying — signature protocol
Related searches to signature protocol made easy
How To Use eSignature in ERP
hello this is Sun welcome back today my topic is digital signature a [Music] detail signature is equivalent to a handwritten signature it is an electronic verification of the sender a digital signature serves three purposes one authentication a digital signature gives the receiver reason to believe the message was created and assigned by the claimed sender two now repudiation with a digital signature the center cannot deny having sent the message later on three integrity a digital signature ensures that the message was not altered intended digital signatures are commonly used for software distribution financial transaction and other kisses with important detect forgery and a temporary digital signatures are very popular with email users let me demonstrate how digital signature works here is the scenario Bob is ascending a memo to Alice with his digital signature keep in mind digital signature uses a symmetric cryptography which means public key algorithm is employed first Bob generates two kids public key and a private key Bob keeps the private key and give Alice the receiver the public key after creating a memo Bob generates a digest by a hash in his mammal using some hash on rhythm table then encrypts the digest with his primary key this encrypted digest is the digital signature for the mammal Bob sends both of the memo and a digital signature to Alice notice here the memo is not encrypted we only focus on digital signature we Alice receives them she will do two things one Alice decrypts the digital signature using Bob's public key and she gets a digest if she cannot decrypt the digital signature then she knows it did not come from Bob because only Bob's public key is able to decrypt the digests generated with his primary key - once Alice gets the digest she will check the integrity of the memo here is what she does Alice hashes the memo with the same hash algorithm Bob used and computes the result to the digest she received if the are equal Alice can be confident that the memo has not changed since Bob signed the memo if the digest are not equal Alice will know the memo has changed in transit last I want to point out one common confusion about the digital signature using digital signature does not equipped the message itself in this example both is ascending in the plaintiffs mammal to Alice if he wanted to encrypt his memo he would have to use Alice's public key which is another story in another video thank you very much and see you next time [Music]
Show more