SOC-2 Signature Service Made Easy
Upgrade your document workflow with airSlate SignNow
Agile eSignature workflows
Fast visibility into document status
Easy and fast integration set up
Soc 2 signature service on any device
Advanced Audit Trail
Rigorous protection standards
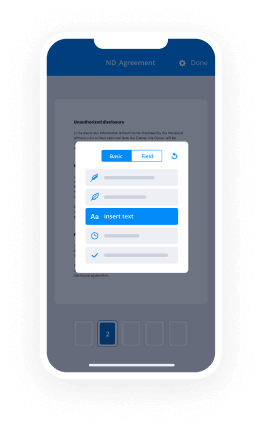
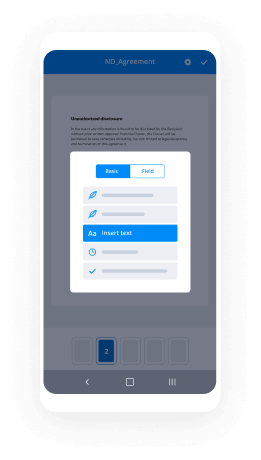
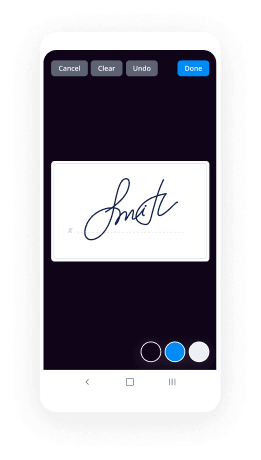
See airSlate SignNow eSignatures in action
airSlate SignNow solutions for better efficiency
Our user reviews speak for themselves






Why choose airSlate SignNow
-
Free 7-day trial. Choose the plan you need and try it risk-free.
-
Honest pricing for full-featured plans. airSlate SignNow offers subscription plans with no overages or hidden fees at renewal.
-
Enterprise-grade security. airSlate SignNow helps you comply with global security standards.

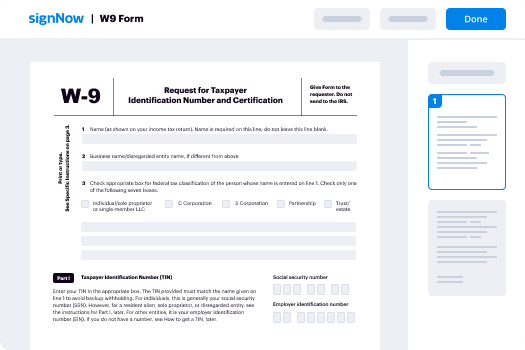
Your step-by-step guide — soc 2 signature service
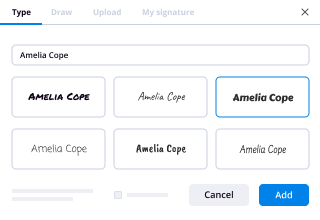
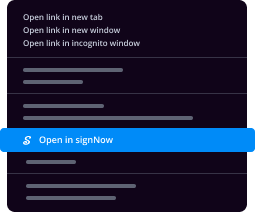
Leveraging airSlate SignNow’s eSignature any business can speed up signature workflows and sign online in real-time, providing an improved experience to customers and workers. Use SOC-2 signature service in a couple of simple actions. Our mobile apps make working on the move feasible, even while off-line! eSign signNows from anywhere in the world and close tasks in no time.
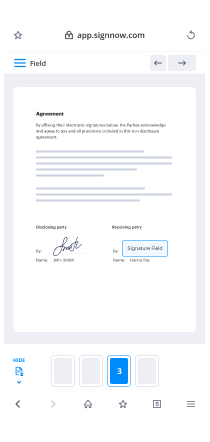
Follow the stepwise guideline for using SOC-2 signature service:
- Log in to your airSlate SignNow account.
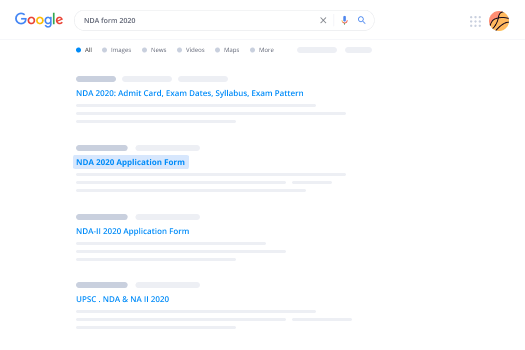
- Find your record within your folders or upload a new one.
- Access the template adjust using the Tools menu.
- Drag & drop fillable fields, type text and eSign it.
- List several signers via emails and set the signing sequence.
- Specify which users will receive an completed doc.
- Use Advanced Options to limit access to the record add an expiration date.
- Press Save and Close when done.
Additionally, there are more extended features open for SOC-2 signature service. Include users to your common digital workplace, browse teams, and track teamwork. Millions of people all over the US and Europe agree that a solution that brings everything together in a single unified enviroment, is exactly what organizations need to keep workflows working efficiently. The airSlate SignNow REST API allows you to embed eSignatures into your app, website, CRM or cloud. Try out airSlate SignNow and get quicker, easier and overall more productive eSignature workflows!
How it works
airSlate SignNow features that users love
See exceptional results SOC-2 signature service made easy
Get legally-binding signatures now!
FAQs
-
What is SOC 2 Type 2 certification?
The Service Organization Control (SOC) 2 Type II examination demonstrates that an independent accounting and auditing firm has reviewed and examined an organization's control objectives and activities, and tested those controls to ensure that they are operating effectively. -
What does SOC 1 Compliance mean?
A Service Organization Control 1 or Soc 1 (pronounced "sock one") report is written documentation of the internal controls that are likely to be relevant to an audit of a customer's financial statements. -
What is included in a SOC 2 report?
There are five Trust Services Principles, or criteria, that comprise a SOC 2 report: Security, Availability, Processing Integrity, Confidentiality and Privacy. ... The SOC II audit is simply the auditor's opinion on how that organization's controls fit the requirements. -
What is the difference between SOC 2 Type 1 and Type 2?
There are many other similarities between SOC 2 Type I and SOC 2 Type II reports, but the key difference is that a SOC 2 Type I report is an attestation of controls at a service organization at a specific point in time, whereas a SOC 2 Type II report is an attestation of controls at a service organization over a ... -
What is the difference between a SOC 1 and SOC 2?
A SOC 2 report, similar to a SOC 1 report, evaluates internal controls, policies, and procedures. However, the difference is that a SOC 2 reports on controls that directly relate to the security, availability, processing integrity, confidentiality, and privacy at a service organization. -
What is the difference between SOC 1 SOC 2 and SOC 3?
A SOC 3 report, just like a SOC 2, is based on the Trust Services Principles, but there's a major difference between these types of reports: restricted use. A SOC 3 report can be freely distributed, whereas a SOC 1 or SOC 2 can only be read by the user organizations that rely on your services. -
What is soc2?
Soc 2, pronounced "sock two" and more formally known as Service Organization Control 2, reports on various organizational controls related to security, availability, processing integrity, confidentiality or privacy. -
What is SOC 2 Type 2 audit?
A SOC 2 audit, or Service Organization Control 2, is an audit of a service organization's non-financial reporting controls as they relate to the Trust Services Criteria \u2013 the security, availability, processing integrity, confidentiality, and privacy of a system. -
What is soc1 and SOC 2 compliance?
Summary. A SOC 1 report is designed to address internal controls over financial reporting while a SOC 2 report addresses a service organization's controls that are relevant to their operations and compliance. One or both could be right for your organization. -
What is a SOC 2 assessment?
What is SOC 2? In 2011, the American Institute of Certified Public Accountants (AICPA) created a series of Service Organization Control (SOC) assessments. ... A SOC 2 is an attestation report that provides controls assurance over a defined set of the service provider's systems. -
What is a Type 2 SOC 1 report?
SOC 1 Type 2. A SOC 1 Type 2 report is an internal controls report specifically intended to meet the needs of the OneLogin customers' management and their auditors, as they evaluate the effect of the OneLogin controls on their own internal controls for financial reporting. -
How do I get SOC 2 compliant?
Step 1: Bring in Credible Outside Auditors. ... Step 2: Select Security Criteria for Auditing. ... Step 3: Building a Roadmap to SOC 2 Compliance. ... Step 4: The Formal Audit. ... Step 5: The Road Ahead \u2014 Certification and Re-Certification. -
What is the difference between SOC 2 and SOC 3?
The short answer is, SOC 2 and SOC 3 reports are both attestation examinations that are conducted in accordance with the SSAE 18 standard, specifically sections AT-C 105 and 205, governed by the AICPA. The main difference is a SOC 2 is a restricted use report and a SOC 3 is a general use report. -
Do I need a SOC 2 report?
SOC 2 requirements are mandatory for all engaged, technology-based service organizations that store client information in the cloud. Such businesses include those that provide SaaS and other cloud services while also using the cloud to store each respective, engaged client's information. -
How long is a SOC 1 report valid?
The opinion stated in a SOC 1 report is valid for twelve months following the date the SOC 1 report was issued. -
What is the difference between SOC 2 and ISO 27001?
Differences : The main difference between SOC 2 and ISO27001 is that SOC 2 is focused mostly on proving the security controls that protect customer data have been implemented, whereas ISO27001 also wants you to prove you have an operational Information Security Management System (ISMS) in place to manage your InfoSec ... -
What does a SOC 1 mean?
A Service Organization Control 1 or Soc 1 (pronounced "sock one") report is written documentation of the internal controls that are likely to be relevant to an audit of a customer's financial statements. -
What is the difference between a SOC 1 and a SOC 2?
Summary. A SOC 1 report is designed to address internal controls over financial reporting while a SOC 2 report addresses a service organization's controls that are relevant to their operations and compliance. One or both could be right for your organization. -
What is the purpose of a SOC 2 report?
SOC 2 Report \u2013 Trust Services Criteria. ... The SOC 2 report focuses on a business's non-financial reporting controls as they relate to security, availability, processing integrity, confidentiality, and privacy of a system, as opposed to SOC 1/SSAE 18 which is focused on the financial reporting controls.
What active users are saying — soc 2 signature service
Related searches to SOC-2 signature service made easy
Soc countersignature
the original standard was known as SAS 70 statement on auditing standards which in 2011 was replaced by sock to service organizational controls - this was developed in America and by the American Institute of Certified Public Accountants sagt who defines the criteria for managing customers data based on the five service principles security availability processing integrity confidentiality and privacy unlike PCI DSS which has very rigid security control requirements - reports are unique to each organization these are in line with specific business practices Eve designs its own controls to comply with one or more of the trust principles first is security the security principle refers to the protection of system resources against unauthorized access access controls help prevent potential system abuse theft or unauthorized removal of data misuse of software and improper alteration or disclosure of information IT security tools such as network and web application firewalls two-factor authentication and intrusion detection software are useful in preventing security breaches that can lead to unauthorized access of systems and data the next ons availability the availability principle refers to the accessibility of the managed service as stipulated by the contract or service level agreements SLA z' as such the minimum acceptable performance level for systems availability is set by both parties this principle doesn't address sips system functionality and usability but does involve security related criteria that may affect availability monitoring network performance and availability site failover security incidents handling are critical in this context you then get processing integrity the processing integrity principle addresses whether or not a system achieves its purpose does it deliver the right data at the right price at the right time accordingly data processing must be complete valid accurate timely and authorized however processing integrity does not necessarily imply beta Integra if data contains error prior to be an input into the system detecting them is not usually the responsibility of the processing entity monitoring of data processing coupled with Quality Assurance procedures can help ensure processing integrity confidentiality data is considered confidential if access and disclosure is restricted to a specific set of people or people within the organization examples may include data that's only intended for company personnel or its business plans or intellectual property it might be financial data encryption is an important control for protecting confidentiality during transmission network and application firewalls together with rigorous access controls can be used to safeguard information being processed or stored on a computer system and finally privacy the privacy principle addresses the system's collection use retention disclosure and disposal of personal information in conformity with an organization's privacy policy as well as within the criteria that's set by sock to the process to becoming Socrates certified is quite a long and arduous process our audit actually lasted six months it starts with the order - looking at your principles your procedures to see how they're carried out on a day to day basis and whether they conform with these standards that have been laid out the audit will then go on and to the point where during your final audit they're actually looking at your live system they want to connect into your cloud they want to see the Reax s certain people within your company have two firewalls two networking equipment so they really go into depth and make sure that not only your paper works up to scratch but so is the infrastructure that you'll be hosting the data being socked to certified for hive managed hosting is really a big thing a lot like in the UK where ISO 27001 is the gold standard in information security in the u.s. that sock to but I think customers can take a huge amount of comfort from a company that is socked to certified because as I said before it's not just looking at your policies and procedures it's looking at your day-to-day running of your company it's looking at your staff it's looking at your security and physical security items that you have within your building and then it's also looking on the infrastructure that the date has held on so it's an all-encompassing certification another point about hive managed hosting being socked to certified can be looked at like this data centers are incredibly secure just to gain physical access to them is very very difficult you've got to have biometric scanners you have ID cards pre-arranged appointment you might have to be escorted and this is just again physical access they hold the access of data just as securely you'll find that the Tier three enhanced data centers are all stocked to an ISO 27001 certified so as the man in the middle as the company that's providing the managed hosting services surely hive should hold these same accreditations so the customer knows that the the way the data center handles security so does hive so I think sock two sits beautifully along ISO 27001 because it covers all of the information security basis that customers need but also it's a big demonstration to your customers to say that we take this seriously it doesn't matter whether you're in the US or Europe or the rest of the world high vantage hosting takes the security of customers data and indeed their own data really seriously and that's really important to us so if you've got any questions on how hive sock 2 certification can help you your company and your data give us a call drop us an email
Show moreFrequently asked questions
How do I eSign a document before sending it?
How do I sign a paper, scan it, and upload it to my computer as a PDF?
How can I use my phone to sign a PDF?
Get more for SOC-2 signature service made easy
- Print electronically sign HIPAA Business Associate Agreement
- Prove electronically signed 1040EZ Form
- Endorse digisign attachment
- Authorize signature service Boy Scout Camp Physical Form
- Anneal mark Sales Receipt Template
- Justify esign Vehicle Bill of Sale Template
- Try countersign Digital Marketing Proposal Template
- Add Collateral Agreement electronically signed
- Send Real Estate Development Proposal Template byline
- Fax Restaurant Reservation esigning
- Seal Art Camp Registration signature block
- Password Service Quote Template signature service
- Pass Affiliate Agreement countersign
- Renew Professional Physical Therapy signatory
- Test Professional Medical History initials
- Require Distributor Agreement Template eSign
- Comment corroborator email signature
- Boost viewer signature
- Call for beneficiary initial
- Void Painting Contract Template template digi-sign
- Adopt Timeshare Agreement template esign
- Vouch Insurance Quote template signature block
- Establish Pet Adoption Application template signature
- Clear Salon Business Plan Template template email signature
- Complete Travel Planning Registration template signatory
- Force Service Proposal Template template digital signature
- Permit Church Donation Receipt template electronically signed
- Customize Affiliate Agreement template byline