SOC Initials Made Easy
Get the powerful eSignature features you need from the solution you trust
Select the pro service created for professionals
Configure eSignature API with ease
Collaborate better together
Soc initials, in minutes
Decrease the closing time
Maintain sensitive data safe
See airSlate SignNow eSignatures in action
airSlate SignNow solutions for better efficiency
Our user reviews speak for themselves






Why choose airSlate SignNow
-
Free 7-day trial. Choose the plan you need and try it risk-free.
-
Honest pricing for full-featured plans. airSlate SignNow offers subscription plans with no overages or hidden fees at renewal.
-
Enterprise-grade security. airSlate SignNow helps you comply with global security standards.

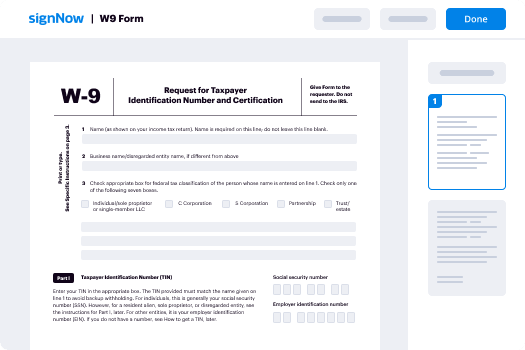
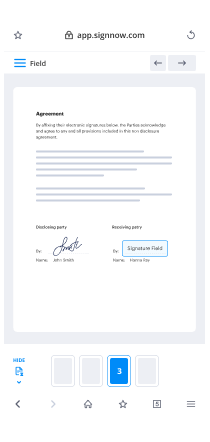
Your step-by-step guide — soc initials
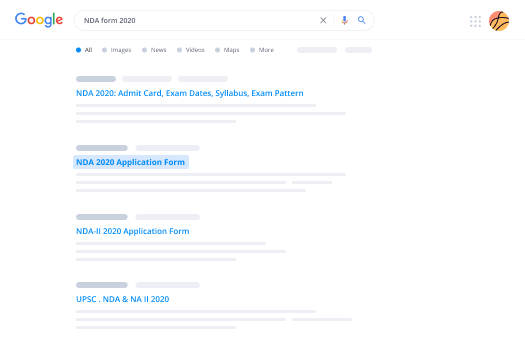
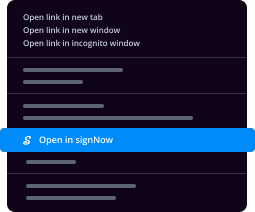
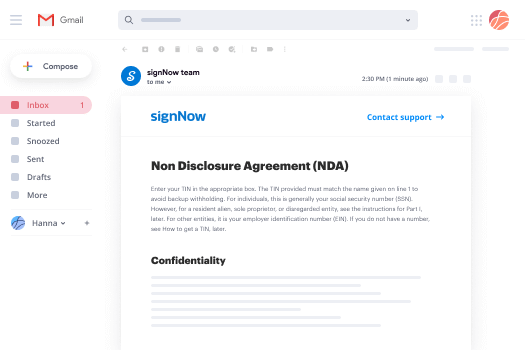
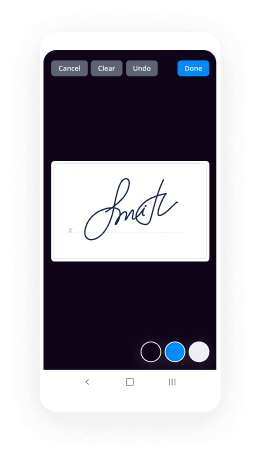
Adopting airSlate SignNow’s eSignature any business can speed up signature workflows and eSign in real-time, supplying a better experience to customers and staff members. Use SOC initials in a couple of simple steps. Our handheld mobile apps make operating on the run feasible, even while offline! Sign signNows from anywhere in the world and close tasks quicker.
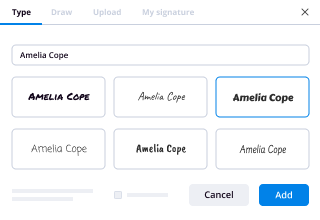
Take a stepwise instruction for using SOC initials:
- Log in to your airSlate SignNow profile.
- Find your record in your folders or upload a new one.
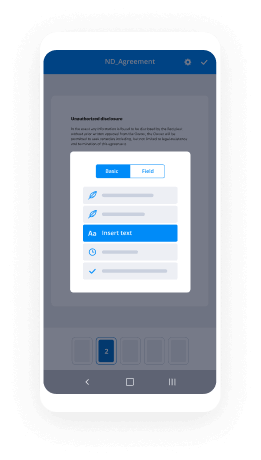
- Open the record adjust using the Tools menu.
- Drag & drop fillable boxes, type text and sign it.
- Add numerous signees using their emails and set up the signing order.
- Specify which users can get an signed version.
- Use Advanced Options to restrict access to the document add an expiry date.
- Tap Save and Close when done.
Furthermore, there are more innovative features available for SOC initials. List users to your collaborative work enviroment, view teams, and track teamwork. Millions of users all over the US and Europe concur that a solution that brings people together in a single cohesive digital location, is exactly what enterprises need to keep workflows working effortlessly. The airSlate SignNow REST API enables you to embed eSignatures into your app, website, CRM or cloud. Try out airSlate SignNow and enjoy quicker, easier and overall more effective eSignature workflows!
How it works
airSlate SignNow features that users love
See exceptional results SOC initials made easy
Get legally-binding signatures now!
FAQs
-
What does SOC stand for in accounting?
A Service Organization Control 1 or Soc 1 (pronounced "sock one") report is written documentation of the internal controls that are likely to be relevant to an audit of a customer's financial statements. -
What is SS in psychology?
SS interval. abbreviation for shock\u2013shock interval. -
What does SOC stand for in electronics?
A distributed antenna system, or DAS, is a network of spatially separated antenna nodes connected to a common source via a transport medium that provides wireless service within a geographic area or structure. -
What does CT stand for in psychology?
Computed tomography (CT), originally known as computed axial tomography (CAT or CT scan) and body section roentgenography, (and also known as computed axial tomography (CAT scan) X-ray computed tomography is a medical imaging method employing tomography where digital geometry processing is used to generate a three- ... -
What does SOC stand for in auditing?
A Service Organization Control 1 or Soc 1 (pronounced "sock one") report is written documentation of the internal controls that are likely to be relevant to an audit of a customer's financial statements. -
What does ur stand for in psychology?
UR stands for Unconditioned Response (psychology) -
What is a soc1?
A SOC 1 Report (System and Organization Controls Report) is a report on Controls at a Service Organization which are relevant to user entities' internal control over financial reporting. ... SSAE 18 Type I Report Background Information. -
What does SOC mean on an application?
SoC stands for system on a chip. This is a chip/integrated circuit that holds many components of a computer\u2014usually the CPU (via a microprocessor or microcontroller), memory, input/output (I/O) ports and secondary storage\u2014on a single substrate, such as silicon. -
What it is SOC 2 compliance?
SOC 2 compliance is a component of the American Institute of CPAs (AICPA)'s Service Organization Control reporting platform. Its goal is to make sure that systems are set up so they assure security, availability, processing integrity, confidentiality, and privacy of customer data. -
What does SOE mean?
A state-owned enterprise (SOE) is a legal entity that is created by a government in order to partake in commercial activities on the government's behalf. It can be either wholly or partially owned by a government and is typically earmarked to participate in specific commercial activities. -
What are the disadvantages to a SoC style chip?
Disadvantages of an SoC Even a single transistor or system damage may prove to be very costly as the complete board has to be replaced, and its servicing is very expensive. Integrating all systems on single chip increases complexity. It is not suitable for power-intensive applications. -
What does SAF stand for?
SAF means "Single Asian Female" -
What is SOC medical term?
Standard of care: 1. A diagnostic and treatment process that a clinician should follow for a certain type of patient, illness, or clinical circumstance. Adjuvant chemotherapy for lung cancer is "a new standard of care, but not necessarily the only standard of care." ( New England Journal of Medicine, 2004)
What active users are saying — soc initials
Related searches to SOC initials made easy
Soc initial
hello and welcome my name is Paul brenell from Hewlett Packard Enterprise and I'm going to walk through a very quick presentation around what an intelligent SOG could look like so without further ado let's crack on with the presentation so here we have a quick illustration of some of the aspects and some of the elements that we would consider to be part of a modern Security Operations environment we can see there's a whole mixture of components and systems and people that would interact with this and of course it will vary according to the level of sophistication the complexity of the infrastructure and additionally the amount of investment that's gone into that environment but in essence we're looking at a number of things that we need to be doing a number of roles that we need to be carrying out and this will all help towards our detection and resolution of and understanding some of the Security's threats that we actually see so let's start off firstly we're going to have some data coming in this the logs and events from the systems the applications from the users the endpoints from virtually any kind of system we need to be collecting those and then we also want to be running that through what we call a real-time correlation engine now that's going to generate some alerts and it's going to generate things that we need to do some investigation on that's when we're gonna get the first level of interaction that our our analysts are going to be making use of so typically those alerts created in real time will be passed along to what we call the sock workflow now typically some form of Q or queuing mechanism that we can hand this information to our security analyst level one so what we also call the L one or level one analysts these are the individuals that would then be looking at that initial set of alerts and information and doing an initial triage on that now we typically work on the basis of something around about three to five minutes is that typical triage process because they're dealing with these alerts in real time they're being received from those logs and events and process part of that real-time correlation engine so we can understand what the context the relevance the importance and the priority is now again is this three to five minute window what we do want to do is understand is a real incident now if it is a real incident we probably want to be handing that on and handing that as part of a further ongoing investigation alternatively if it is something that is relatively simple and straightforward why this is the situation where these level one L is should be able to look at it triage it and go I don't consider this to be a major problem maybe I'll pick it up later when I've got a few more minutes spare but in a prioritization process I need to move on towards more important aspects and the threats that we can see so that's typically the first level of this real-time monitoring of these level 1 analysts are looking at and understanding the incidents as they occur now if something genuinely does occur and those level 1 analysts do identify something that they constitute is an incident that does require and need further investigation that doesn't necessarily mean it's real what we're trying to do is reduce the false positives trying to reduce the amount of effort required in detailed analysis but that's okay because it could be real but we want to class it on to in this particular case our security analysts level 2 as part of an investigation process now of course it will vary according to situation and circumstance and customer and level of sophistication and infrastructure as well but a classic example is where a further detailed level of investigation needs to be carried out on these alerts to ascertain exactly what's gone on what's the importance what's the relevance what do we what's the impact what do we have to understand with regards to users and also we have to have a incident management process in place so they're typically now going to be interacting with systems to look at investigate through and drive through some of our data so you can see here we're doing things like investigation queries we're looking at this what we would consider for example is security data warehouse where we've got this data we can go back through the information understand what's going on I understand the aspects and the elements that are involved the actors and the attackers in the incidence of the compromised indicators and all motley to understand what we consider what we call the blast radius how far does this go so the level to analysts are now carrying out active investigations looking at and through the data asking questions of simple things like what did that particularly user do yesterday what do they do last month and how does that compare as a baseline against the other users are they doing extraordinary things like huge amounts of data in or out of the organization or logging in or out of the applications and systems at very unusual times the context and the data that needs to be looked at is much wider much deeper and normally in some form of comparison type investigation process typically part of an investigation you probably want to be using something like a an investigation tool or an incident management tool which we'll be tracking from an audit point of view which we understanding what what's actually going on what the individuals are doing and making sure that we have a legal chain of custody with regards to what's going on as well now you can see there's another face to this as well where you know we call it a hunt team but it could be a level-3 or you know tier 3 is often used as well this is a separate team where they are taking and some of the information taking some data for example from our level 2 analysts and and using that to drive intelligence-led investigations and hunting activities so this isn't necessarily triggered from an alert it's not necessarily triggered something from a real-time correlation for example but this is something that with intelligence with relevance and context it could come from the level 2 analysts who may have identified some unusual patterns of activity they can carry on doing their investigation but they hand all over some of those intelligence-led aspects to the hunt team and say now you can go ahead and start looking back through that data and with the additional intelligence that you have for example looking at intelligence feeds external data internal data as well and how you can use for example things like analytics to drive some of that aspects of hunting for these unknown threats now the critical thing here which is the unknown aspect what's known and what's unknown yet typically the hunt team is looking for those unknown threats those unknown aspects and those unknown actors that are operating typically within the organization but that's okay because that's what the driven by but when we look back up again for a second and we look at the level one analysts for a second they're typically being driven by known threats and aspects and they have priorities of how they need to handle some of that as well so those known threats are typically driven by the real-time correlation engine and then typically from a level two they are again driven by those alerts but looking back through that data into for example something like a security data warehouse and then typically the hunt team are using analytics based capabilities to drive back through that data on an intelligence led aspect of their role specifically so you can see there's a difference between the known and the unknown and the way that they would interact as part of that but let's take a deeper dig into how some of these operations actually occur and and where would these individuals interact and and how would there be other roles typically within this environment within the Security Operations Center itself so let's take the the gray circle to start with typically we're going to be getting data from technology whether it be from your network from your environments from your servers from your security systems that are generating this data as well whether it's coming from external systems like intelligence-led and threat intelligence data itself we're typically doing some processing on that we're going to be storing a data we're going to be using that data at a correlation engine and this example we're showing it here with the arcs ITSM real-time correlation platform but what we're doing is we're processing that data and bring it together to bring context to what it means for example we want to be able to start asking some questions of things like who did what where did they do it how did they get there and what did they do when they got there so we need to be piecing together lots of these different systems for example it as part of a real-time correlation engine to start answering some of those questions and matching that with a real-time correlation engine to then be able to impose and define what we know from a known based attacks and how they can be then picked up by an alert mechanism and sent to the level one analyst for example so now we've moved on and we've identified that there's a people aspect here so for example we've seen some activity that's been correlated by some known rules as part of this case in here with arcs ITSM real-time correlation platform that's then triggered an alert which is then being sent to the level one analyst as we mentioned before typically they're looking at something like three to five minutes where they're doing some initial triage to understand the priority the context and the relevance of what's going on and whether this needs to be investigated any further if it does need to be investigated any further they can hand that to the level two analyst so now they can start digging into and spending much longer on the investigation and we mention data level ones typically three to five minutes can be long longer that's okay but typically we want to be focused around doing that prioritization and triage but a little too analyst in typically working in conjunction with an incident handler if it is a real incident that we need to understand and deal with there is typically a very fixed process as part of this and of course it varies based on geography based on role based on situation even the organization involved in here as well so in that environment we need to have almost an unlimited amount of time as part of that incident handling process and they need to be involved with other aspects of the business as a whole so for example a great scenario is level one analyst identifies that this usual activity by a particular user whose internal to the organization they conclude that there is genuine activity that is suspicious and it requires further investigation they hand that to the level 2 analyst who then starts and kicks off the whole incident process who then would typically trigger something as part of an incident management process application and involving an incident handler but the incident handler then identifies and says we'll hang on a second this involves a particularly high privileged user within the organization which is impacted by various legal and governance aspects as well it could even for example being somebody who's based in a particular location or geography where they're protected by workers councils and other privacy rules at that point they have to work hand in hand with network system owners and application owners or even within the human resources part of the organization directly to ensure that they have the right aspects of process in place that they we can ensure that we handling this correctly accurately and fairly but notice that typically not the level 1 and level 2 who are focused on the operations aspect of security monitoring and typically as part of the level 2 analyst they'll be identifying things they'll be identifying activity threats and other changes as well where they can see things going on and they will want to hand that for example unknown or previously unknown or unidentified aspects and hand that to what we call an engineer or a platform or content engineer in that place that the individual that's then responsible for creating evolving and adding additional alerts processes correlation rules and other aspects to the platform to further evolve and improve the levels of detection the point here and it have to stress this directly is we don't want the Watchers creating the rules on either level one or level two aspect because it's human psychology that says typically they will make it simpler so they don't get more and more things in their queue to process we want this to be handled by an external person within the group that we can work together as part of a team to ensure that we get to get the best levels of detection that we're trying to deliver as part of this capability so as a quick recap we're going to have technology that's delivering as information log data application information we're then doing some correlation on that in this particular example we're using arcs ITSM correlation platform the level one analyst is identifying and picking up that there's a particular alert has been triggered and doing that initial triage they hand that to the level two typically if this is real and it needs to be escalated further to hand that to an incident handler which is external to the actual Operations Group directly the incident handler can then work in in conjunction with the networking system owners HR and other aspects of the organization to ensure accurate and fair handling of the incident as a whole and then typically we want to have a review process where the level two analysts can feedback further information to the platform engineer or the content engineer where they can further evolve and improve on the levels of detection we trying to deliver as part of this not forgetting we also want to have a business business owner that has an element of part of this process as well so they can identify an overall steer the operations capability is part of this Security Operations Center itself to drive it in the right direction around its levels of capability and its levels of detection going forward so let's just step back a second to one of my previous illustrations here so we can see that there's very much some defined roles as part of an intelligent Security Operations Center we have very specific capabilities there's a lot more roles as well don't get me wrong but we're focusing around the level one analysts the level two analysts and a-hunting they're typically interacting with different components technologies and systems and they do have a levels of integration between themselves but you can see that this is driving three distinct use cases that assisting in the overall detection and response capability and we can see that the level one analysts are typically working in conjunction with the real-time correlation and monitoring platform itself responding to those alerts as quickly as they can to bring the context and do that initial triage the level two analysts are typically working in in addition to the level one analyst but they're working on additional capabilities around asking and being able to answer so much more of those investigation questions what happened what's the impact how does that compare with other activity and they can then carry out and hand off some of that investigation to the incident handling process as well and then finally there's the hunt aspect these are the individuals that go out with intelligence-led activities go hunting for the bad guys hunting for those those actors that are trying to interrupt change or get access to our particular applications and systems now typically they're going to be using an analytics driven capability so we can see there's very much three different roles three different aspects that just illustrates the difference that we would need to be delivering as part of an intelligent Security Operations Center and ultimately this is around delivering and improving on that overall capability we can see and it because organizations shouldn't compare themselves on this and think for example that because they're not further up in a overall capability graph that there's somehow lacking or not delivering or what they need to be delivering that's not fair because some organizations that could be very for example very small have a very high requirement around some of this functionality whereas other organizations which might be dramatically larger are not impacted by some of these aspects directly so therefore don't have that level of sophistication is required so it varies by customer organization location region and so on but typically this is a good illustration of the levels of capability that would typically need as part of an intelligent security operation center we've gone on from just centralizing with love management to a more sophisticated level of data analysis where we're doing correlation some advanced forensics capability and the ability to generate a number of reports and aspects to give us intelligence of what's going on we then need to move to much more sophisticated capability to deliver on much higher fidelity around correlation and being able to understand how we can do that in real time we need to move to a real-time analysis and incident response because that's a big step forward we need to not only just be able to have a real-time correlation engine for example but we need to have the capability that we can respond to that in real time - that means need to do that level one and analysis and contextual understanding of what's going on but additionally we need to have a set of capabilities and individuals that are helped us as part of the incident handling as well now that can take time but it needs to be able to be triggered in real time as the events and as the threats appear and then ultimately what we're doing is driving that forward and being able to deliver on this vision of true security intelligence the ability to to have in-depth analysis being able to do a level of productivity - what we're trying to identify can we get ahead of the threats before they're really there and then ultimately being able to solve some of the more advanced use cases and identify those new threats that's where we start delivering on the capabilities but you can see that there is a number of phases that we need to move to to get to that overall set of capabilities we don't just get there at stage one there's a number of individuals a number of roles and aspects to our security operations environment to get there in the first place anyway that's enough for me I wish to thank you very much for your time and listening thank you
Show more