SOC Signature Block Made Easy
Upgrade your document workflow with airSlate SignNow
Flexible eSignature workflows
Instant visibility into document status
Easy and fast integration set up
Soc signature block on any device
Advanced Audit Trail
Strict security requirements
See airSlate SignNow eSignatures in action
airSlate SignNow solutions for better efficiency
Our user reviews speak for themselves






Why choose airSlate SignNow
-
Free 7-day trial. Choose the plan you need and try it risk-free.
-
Honest pricing for full-featured plans. airSlate SignNow offers subscription plans with no overages or hidden fees at renewal.
-
Enterprise-grade security. airSlate SignNow helps you comply with global security standards.

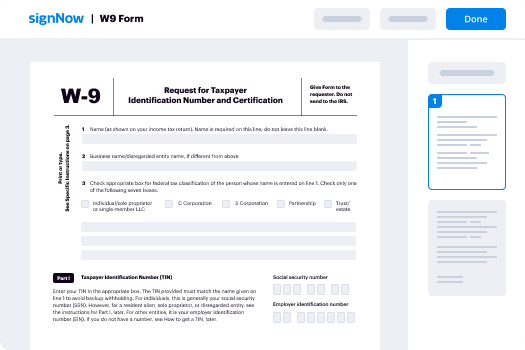
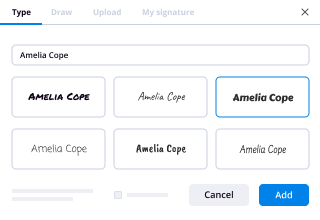
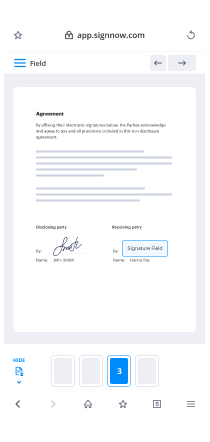
Your step-by-step guide — soc signature block
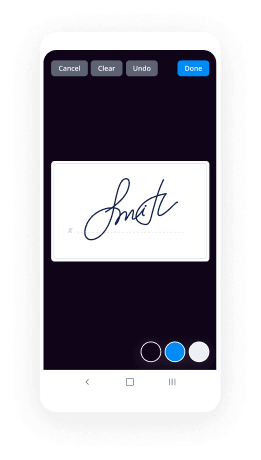
Leveraging airSlate SignNow’s eSignature any organization can speed up signature workflows and sign online in real-time, supplying an improved experience to clients and staff members. Use SOC signature block in a couple of easy steps. Our mobile-first apps make work on the run achievable, even while off-line! eSign documents from anywhere in the world and close trades in no time.
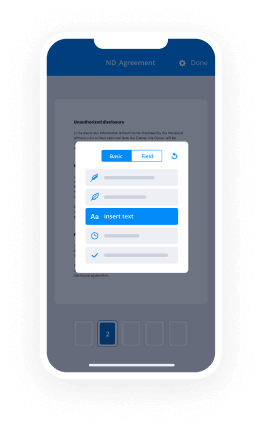
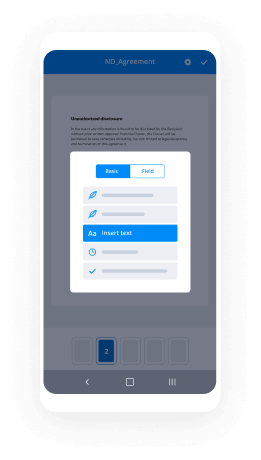
Take a step-by-step guideline for using SOC signature block:
- Log on to your airSlate SignNow profile.
- Locate your document in your folders or upload a new one.
- Access the record and edit content using the Tools list.
- Drop fillable boxes, add text and eSign it.
- Add multiple signees using their emails and set the signing order.
- Specify which users will receive an executed version.
- Use Advanced Options to restrict access to the record add an expiry date.
- Press Save and Close when completed.
Furthermore, there are more advanced features available for SOC signature block. Add users to your common digital workplace, browse teams, and keep track of cooperation. Millions of consumers across the US and Europe recognize that a system that brings people together in one cohesive work area, is what organizations need to keep workflows working easily. The airSlate SignNow REST API allows you to embed eSignatures into your application, website, CRM or cloud storage. Try out airSlate SignNow and get quicker, smoother and overall more effective eSignature workflows!
How it works
airSlate SignNow features that users love
See exceptional results SOC signature block made easy
Get legally-binding signatures now!
FAQs
-
What methods are used for intrusion prevention?
The majority of intrusion prevention systems utilize one of three detection methods: signature-based, statistical anomaly-based, and stateful protocol analysis. -
What are the major aspects of intrusion prevention?
The majority of intrusion prevention systems use one of three detection methods: signature-based, statistical anomaly-based, and stateful protocol analysis. Signature-based detection: Signature-based IDS monitors packets in the network and compares with predetermined attack patterns, known as \u201csignatures\u201d. -
What are intrusion prevention systems?
An Intrusion Prevention System (IPS) is a network security/threat prevention technology that examines network traffic flows to detect and prevent vulnerability exploits. -
What is intrusion detection prevention?
An Intrusion Prevention System (IPS) is a network security/threat prevention technology that examines network traffic flows to detect and prevent vulnerability exploits. -
What is the best intrusion prevention system?
If you only have time for a summary, here is our list of the best IPS's: SolarWinds Security Event Manager (FREE TRIAL) This security tool uses both network-based and host-based intrusion detection methods and takes preventative action. ... Sagan Free intrusion prevention system that mines log files for event data. -
How do intrusion detection systems work?
Intrusion detection systems are used to detect anomalies with the aim of catching hackers before they do real damage to your network. They can be either network- or host-based. ... intrusion detection systems work by either looking for signatures of known attacks or deviations of normal activity. -
How does IPS signature work?
Signature-Based \u2013 In Signature-Based approach, predefined signatures or patterns of well-known network attacks are encoded into the IPS device by its vendors. The predefined patterns are then used to detect an attack by comparing the patterns that an attack contains, against the ones that are stockpiled in IPS. -
What is IPS signature?
A signature is a set of rules that an IDS and an IPS use to detect typical intrusive activity, such as DoS attacks. ... As sensors scan network packets, they use signatures to detect known attacks and respond with predefined actions. -
What does IPS protect against?
An intrusion prevention system (IPS) is a network security technology that monitors network traffic to detect anomalies in traffic flow. IPS security systems intercept network traffic and can quickly prevent malicious activity by dropping packets or resetting connections. -
What is IPS and how does it work?
Intrusion Prevention System (IPS) helps in delivering the secure platform to the network as it proactively responds to any unauthorized threats or unwanted traffic. It has a capability to detect the threat instantly. An Intrusion Prevention System works in in-line mode. -
How does IPS IDS work?
IPS: What is the Difference? Intrusion Detection Systems (IDS) analyze network traffic for signatures that match known cyberattacks. Intrusion Prevention Systems (IPS) also analyzes packets, but can also stop the packet from being delivered based on what kind of attacks it detects \u2014 helping stop the attack. -
How do firewalls prevent intrusion attacks?
Firewalls limit access between networks to prevent intrusion and do not signal an attack from inside the network. An IDS evaluates a suspected intrusion once it has taken place and signals an alarm. An IDS also watches for attacks that originate from within a system. -
Is a firewall an intrusion prevention system?
A firewall is an intrusion detection mechanism. Firewalls are specific to an organization's security policy. The settings of firewalls can be altered to make pertinent modification to the firewall functionality. Firewalls can be configured to bar incoming traffic to POP and SNMP and to enable email access. -
Which type of attack can a firewall not prevent?
Firewall cannot protect you from the following dangers. Malicious use of authorized services: A firewall cannot, for instance, prevent someone from using an authenticated Telnet session to compromise your internal machines or from tunneling an unauthorized protocol through another, authorized protocol. -
What do firewalls block?
A firewall is a system designed to prevent unauthorized access to or from a private network. You can implement a firewall in either hardware or software form, or a combination of both. Firewalls prevent unauthorized internet users from accessing private networks connected to the internet, especially intranets.
What active users are saying — soc signature block
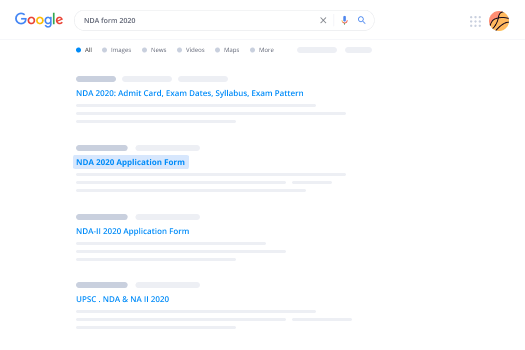
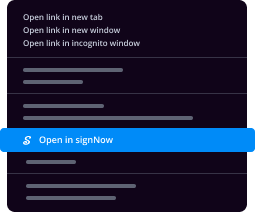
Related searches to SOC signature block made easy
Soc signature block
hello this is Andrew with missing rope calm today we're gonna have a look at the internet security section of the UTM and UTM pro most of this is very similar to what you can do with a USG and you defy but there are some key differences in here that's mostly we're gonna talk about and then also I'll try to highlight the areas where there is an advancement in the feature set with the UTM Pro the first section here is the threat management this is the IDs or IPs this is one of the major reasons why you or I certainly would pick up a UTM or UDM probe versus a USG is it can do sustained much higher throughput using IDs or IPS because it has a much more modern CPU or SOC in it than the usgs do i have it dialed up all the way mostly here to make a point here around how it works I have a DNS query queued up here which should cause a IPS alert to pop up and there we go that's straight out of the unifies documentation around how that stuff works there aren't many differences here between what you can do with the USG versus what you can do to UTM Pro the main thing to take away from this is that if you have an internet connection which is more than 300 megabits per second then you can actually use that bandwidth above its you're gonna make it it's per second with IPS turned on GOP geoip filtering is not new either basically you can block countries using this feature from your from accessing your network to do that is really easy you just kind of pick a country you don't want to receive traffic from like let's go for North Korea and let's block it and then we're done if you want to take country off the list you just unblock it and we're done that's all there is to it for this I assume that this works I don't really have a way to test it though so let's get back to our Internet Security section so DNS filtering is a pretty neat feature because it lets you do the kind of thing that you can do on a USG where you force all of your DNS through a single approved DNS resolver I use PI hole on my networks I'm using pi hole on this network as well but because the us.you diem and UTM probe can't do dnat rules you can't use the device the UTM to force everything through your pie hole and then masquerade and all that other stuff this feature gets really close to that the main difference though is that you can't choose your own DNS provider it uses a DNS provider that they don't disclose with a few different types of filter settings security adult and family if we look at the UTM pro setting up a just tailing the the message log looking for the dns filter let's quickly turn it on I have to turn it off every now and again because there is a bug in the version of the firmware that I'm running which is admittedly a testing version where it a DNS filtering just kind of stops working occasionally so let's tail this and then we'll do a DNS lookup let's see something that nobody would have ever looked at and so here we see a bunch of messages in the log file and it indicates DNS filter and then we look at our destination which is I have a security this is landed security so what we can do or what I did do is I searched for the IP address but I searched for the IP address of the children's our family network and I came up with clean browsing DNS which is this service here which has family filter adult filter security filter so reasonably confident that they're just kind of using the free version of the clean browsing service there are some pluses and minuses to this one you have absolutely no control over what's blacklisted and what's the white listed and it's very much a black box and when this is turned on even if you have a different DNS provider set up you can't use it so as I mentioned before I have a PI whole set up I am using Open DNS to resolve or I have open DNS setup in pile to resolve but Open DNS provides some ways to check to see if you're using Open DNS or not and clearly we can see when we go to their test site we're not using Open DNS even though piehole is a result it we're resolving DNS through the pie hole which is supposed to be using Open DNS is just getting overridden by this black box solution from the ubiquity have turned on here so I don't like that that it doesn't have the flexibility to just kind of use my own or DNS well I would love to do is just DNS filtering to Open DNS after my pie hole is used to block all of the ad spam and trackers and things like that but that's not really an option you do get the ad blocking and track anti tracking stuff through pie hole but it it all goes through this clean browsing DNS resolver and not whatever you want to use which kind of sucks but it is what it is hopefully I mean you can see here there's an alpha feature hopefully this is nowhere near done and they will expand this feature to let you use your own providers and blacklist whitelist all of that sort of thing so hopefully that we will see more of that so I'm gonna turn this off just so it doesn't keep again stuff we go to the deep packet inspection this is an area where if there's been significant improvement versus the USG and the this existent is in the USG but what you couldn't do before is you couldn't so let's say I want to block social network so in the in the USG you just block a category so you block all social networks which maybe you want to do that but I generally don't hear you now can block on an application level so if I want to block Twitter I can do that enable this restriction set it to my restricted group which I have assigned to my land so before I turn this on let's just quickly check to make sure that I can get to twitter twitter loads up no problem so let's turn this on will block the traffic apply and then we'll open up our browser go to Twitter and we can see here that the request will different I'm out I won't be able to resolve Twitter which is brilliant so you have a lot of flexibility now to add a huge amount of different options for all of these different things and if you want to do it at the category level you still can do that so if I want to block all tunneling and proxy servers I just all applications turn it on and I'm done so that's a massive improvement over what you could do with the USG and I'm really pleased to see that and I plan to use this going forward once I can actually use this thing properly the network scanners is another new feature with the UDM or UTM Pro this is not present with the USG basically it sets up we call the honey pots you put them on their network and they listen on a bunch of different ports HTTP HTTP SSH just to name a couple that's documented if you were to hit one of these sites I have one setup per network right now so if you go to the threat management section and honeypot you can see where I've been playing around with the this feature it's kind of a neat thing I don't know how useful it is on a home network but in the enterprise network you would definitely pick up scanners this way while we're here this is one of the things another nice thing that the UDM an EDM Pro do is they note all of the systems on your network which is not new but they can they try to identify the operating system and this is controlled through here with the endpoint scanner that's kind of a niche than anything advanced is where you manage the IPS and IDs signatures both a suppression and you can create white lists I don't tend to create white lists and I'm not sure if that's a just a personal thing I do suppress signatures occasionally mostly the header kind malformed header might tell my lg television has a typo and it's header and so I do suppress that one on the on my USG to manage this the threat management you can either create a whitelist here or you can go to the threat management section via the traffic log here we can see some of those alerts that I was throwing up before we have some options and what we want to do with it we can suppress it which suppresses the signature and then puts an item in the suppression list that we just looked at we can block it which creates firewall rules or we can blacklist or whitelist this traffic I'm going to go ahead and block it so we can see what that does which is after we block it we go back to the firewall section and here we can see the rules that were just created because we chose to to block the traffic if you do that by mistake and you want to on do that you can always just remove it or if you want to make it a little bit a wider definition you have the option to go in and edit the rule and expand it beyond whatever the the scope of the alert that's pretty much all there is to that section hopefully you found this useful if you did go ahead and like the video subscribe to the channel if you have any questions or comments something I didn't address that you want answered just drop that below and I'll get to it as soon as I can thanks
Show more