Test Initials Request with airSlate SignNow
Do more on the web with a globally-trusted eSignature platform
Outstanding signing experience
Trusted reporting and analytics
Mobile eSigning in person and remotely
Industry regulations and conformity
Test initials request, faster than ever
Helpful eSignature add-ons
See airSlate SignNow eSignatures in action
airSlate SignNow solutions for better efficiency
Our user reviews speak for themselves






Why choose airSlate SignNow
-
Free 7-day trial. Choose the plan you need and try it risk-free.
-
Honest pricing for full-featured plans. airSlate SignNow offers subscription plans with no overages or hidden fees at renewal.
-
Enterprise-grade security. airSlate SignNow helps you comply with global security standards.

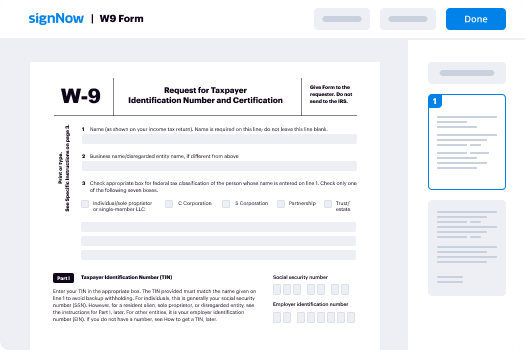
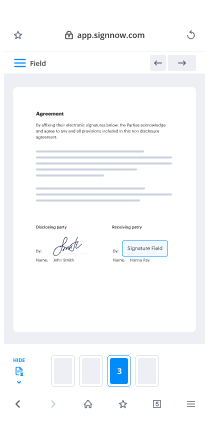
Your step-by-step guide — test initials request
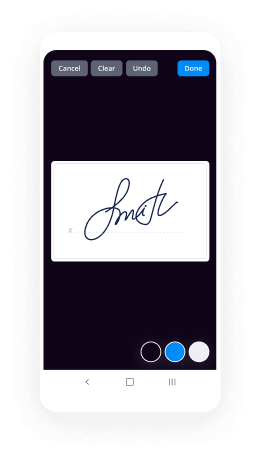
Employing airSlate SignNow’s eSignature any business can enhance signature workflows and sign online in real-time, delivering a better experience to customers and workers. test initials Request in a few easy steps. Our mobile apps make working on the run possible, even while off the internet! Sign signNows from anywhere in the world and complete tasks quicker.
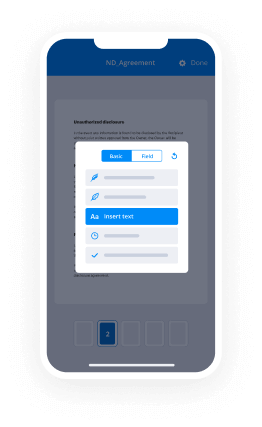
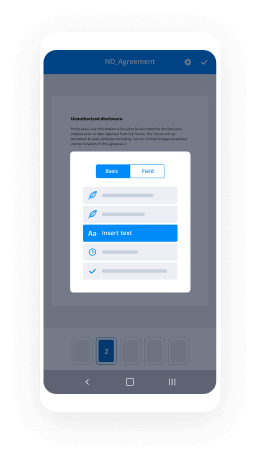
Follow the stepwise guideline to test initials Request:
- Sign in to your airSlate SignNow profile.
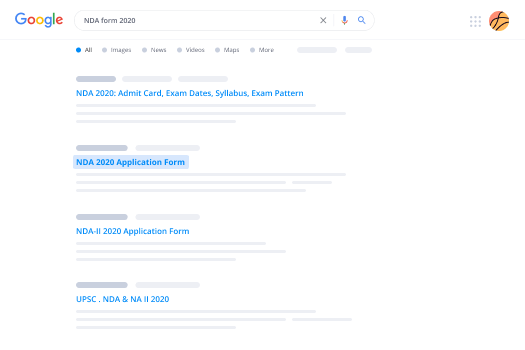
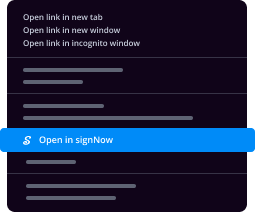
- Locate your record in your folders or import a new one.
- Open the document and make edits using the Tools menu.
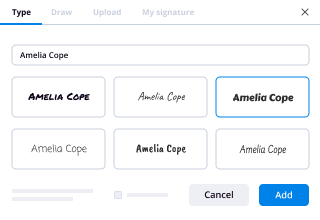
- Place fillable fields, type text and eSign it.
- Add numerous signees via emails and set up the signing order.
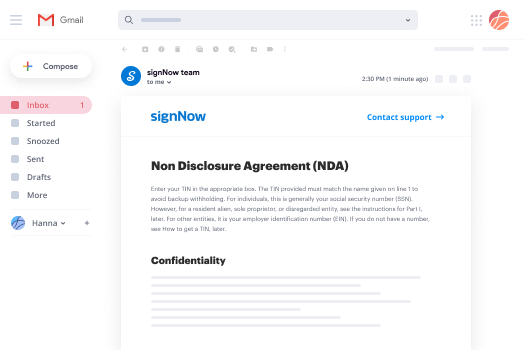
- Specify which users will get an completed version.
- Use Advanced Options to limit access to the template and set up an expiration date.
- Tap Save and Close when done.
Furthermore, there are more enhanced functions open to test initials Request. Include users to your collaborative digital workplace, browse teams, and track teamwork. Numerous users all over the US and Europe recognize that a system that brings everything together in a single unified digital location, is exactly what enterprises need to keep workflows performing efficiently. The airSlate SignNow REST API enables you to embed eSignatures into your application, website, CRM or cloud. Check out airSlate SignNow and get faster, smoother and overall more efficient eSignature workflows!
How it works
airSlate SignNow features that users love
See exceptional results test initials Request with airSlate SignNow
Get legally-binding signatures now!
FAQs
-
What do blood test initials mean?
CBC - Complete Blood Count (test red and white blood cells for overall health and to detect abnormalities) CK - Creatine Phosphokinase (test for muscle damage) CR - Creatinine (part of kidney function test) ESR - Erythrocyte Sedimentation Rate (tests for inflammation) -
What is the abbreviation for thyroid blood test?
The amount of T4 produced by the thyroid gland is controlled by another hormone, which is made in the pituitary gland located at the base of the brain, called thyroid stimulating hormone (abbreviated TSH). -
What does CA stand for in a blood test?
CA stands for cancer antigen. CA 125 is often measured as a blood test. -
What is the correct way to write initials?
Just like with men and women, monograms for children follow the same order of first, last and middle initial, with the last name initial being larger than the other two. However, just as with adults, if the font size of the initials are to be the same, then the order is as such: first, middle and last. -
How do you write a period with initials?
A period should be placed after an initial and after most abbreviations. -
What is the acronym stand for?
Abbreviations and acronyms are shortened forms of words or phrases. An abbreviation is typically a shortened form of words used to represent the whole (such as Dr. or Prof.) while an acronym contains a set of initial letters from a phrase that usually form another word (such as radar or scuba). -
What is your initial name?
The first letter of your name is your initial. ... Initial is something that occurs first or at the beginning. If someone asks you to initial a form, they're asking you to sign by writing your initials on it. -
What is the acronym for have?
HAVE. Home Assistance Volunteer Effort, Inc. ( Aurora, IL) Note: We have 1 other definition for HAVE in our Acronym Attic. Search for HAVE in Online Dictionary Encyclopedia. -
How do you write initials with dots?
Spacing after the periods (dots) is correct. Using periods in abbreviated names is correct, if one is using the full address. However, since many people are referred to by their initials as nicknames in dialog, I think the periods would be eliminated. -
What is an acronym example?
An acronym is a word, name or set of letters created as an abbreviation of a longer phrase or sentence. Usually signNows or words such as 'and' or 'of' are not included in the abbreviation. Examples: NASA = National Aeronautics (and) Space Administration. DIY = Do It Yourself. -
Is FBI an acronym?
The difference between an acronym and initialism is that the abbreviation formed with initialisms is not pronounced as a word, rather you say the individual letters, such as FBI (Federal Bureau of Investigation), CIA (Central Intelligence Agency), and DVD (Digital Video Disk*).
What active users are saying — test initials request
Related searches to test initials Request with airSlate airSlate SignNow
Test initials request
3DES Triple Digital Encryption Standard AAA Authentication, Authorization, and Accounting ABAC Attribute-based Access Control ACL Access Control List AES Advanced Encryption Standard AES256 Advanced Encryption Standards 256bit AH Authentication Header ALE Annualized Loss Expectancy AP Access Point API Application Programming Interface APT Advanced Persistent Threat ARO Annualized Rate of Occurrence ARP Address Resolution Protocol ASLR Address Space Layout Randomization ASP Application Service Provider AUP Acceptable Use Policy AV Antivirus BAC Business Availability Center BCP Business Continuity Planning BIA Business Impact Analysis BIOS Basic Input/Output System BPA Business Partners Agreement BPDU Bridge Protocol Data Unit BYOD Bring Your Own Device CA Certificate Authority CAC Common Access Card CAN Controller Area Network CAPTCHA Completely Automated Public Turing Test to Tell Computers and Humans Apart CAR Corrective Action Report CBC Cipher Block Chaining CCMP Counter-Mode/CBC-Mac Protocol CCTV Closed-circuit Television CER Certificate CERT Computer Emergency Response Team CFB Cipher Feedback CHAP Challenge Handshake Authentication Protocol CIO Chief Information Officer CIRT Computer Incident Response Team CMS Content Management System COOP Continuity of Operations Plan COPE Corporate Owned, Personally Enabled CP Contingency Planning CRC Cyclical Redundancy Check CRL Certificate Revocation List CSO Chief Security Officer CSP Cloud Service Provider CSR Certificate Signing Request CSRF Cross-site Request Forgery CSU Channel Service Unit CTM Counter-Mode CTO Chief Technology Officer CTR CYOD Click-through rate Choose Your Own Device DAC Discretionary Access Control DBA Database Administrator DDoS Distributed Denial of Service DEP Data Execution Prevention DER Distinguished Encoding Rules DES Digital Encryption Standard DHCP Dynamic Host Configuration Protocol DHE Data-Handling Electronics DHE Diffie-Hellman Ephemeral DLL Dynamic Link Library DLP Data Loss Prevention DMZ Demilitarized Zone DNAT Destination Network Address Transaction DNS Domain Name Service (Server) DoS Denial of Service DRP Disaster Recovery Plan DSA Digital Signature Algorithm DSL Digital Subscriber Line DSU Data Service Unit EAP Extensible Authentication Protocol ECB Electronic Code Book ECC Elliptic Curve Cryptography ECDHE Elliptic Curve Diffie-Hellman Ephemeral ECDSA EllipticCurveDigitalSignatureAlgorithm EFS Encrypted File System EMI Electromagnetic Interference EMP Electro Magnetic Pulse ERP Enterprise Resource Planning ESN Electronic Serial Number ESP Encapsulated Security Payload FACL File System Access Control List FDE Full Disk Encryption FRR False Rejection Rate FTP File Transfer Protocol FTPS Secured File Transfer Protocol GCM Galois Counter Mode GPG Gnu Privacy Guard GPO Group Policy Object GPS Global Positioning System GPU Graphic Processing Unit GRE Generic Routing Encapsulation HA High Availability HDD Hard Disk Drive HIDS Host-based Intrusion Detection System HIPS Host-based Intrusion Prevention System HMAC Hashed Message Authentication Code HOTP HMAC-based One-Time Password HSM Hardware Security Module HTML Hypertext Markup Language HTTP Hypertext Transfer Protocol HTTPS Hypertext Transfer Protocol over SSL/TLS HVAC Heating, Ventilation and Air Conditioning IaaS Infrastructure as a Service ICMP Internet Control Message Protocol ICS Industrial Control Systems ID Identification IDEA International Data Encryption Algorithm IDF Intermediate Distribution Frame IdP Identity Provider IDS Intrusion Detection System IEEE InstituteofElectricalandElectronicEngineers IKE Internet Key Exchange IM Instant Messaging IMAP4 Internet Message Access Protocol v4 IoT Internet of Things IP Internet Protocol IPSec Internet Protocol Security IR Incident Response IR Infrared IRC Internet Relay Chat IRP Incident Response Plan ISA Interconnection Security Agreement ISP Internet Service Provider ISSO Information Systems Security Officer ITCP IT Contingency Plan IV Initialization Vector KDC Key Distribution Center KEK Key Encryption Key L2TP Layer 2 Tunneling Protocol LAN Local Area Network LDAP Lightweight Directory Access Protocol LEAP Lightweight Extensible Authentication Protocol MaaS Monitoring as a Service MAC Mandatory Access Control MAC Media Access Control MAC Message Authentication Code MAN Metropolitan Area Network MBR Master Boot Record MD5 Message Digest 5 MDF Main Distribution Frame MFD Multi-function Device MITM Man-in-the-Middle MMS Multimedia Message Service MOA Memorandum of Agreement MOU Memorandum of Understanding MPLS Multi-protocol Label Switching MSCHAP Microsoft Challenge Handshake Authentication Protocol MSP Managed Service Provider MTBF Mean Time Between Failures MTTF Mean Time to Failure MTTR Mean Time to Recover or Mean Time to Repair MTU Maximum Transmission Unit NAC Network Access Control NAT Network Address Translation NDA Non-disclosure Agreement NFC Near Field Communication NIDS Network-based Intrusion Detection System NIPS Network-based Intrusion Prevention System NIST National Institute of Standards & Technology NTFS New Technology File System NTLM New Technology LAN Manager NTP Network Time Protocol OAUTH Open Authorization OCSP Online Certificate Status Protocol OID Object Identifier OS Operating System OTA Over The Air OVAL Open Vulnerability Assessment Language P12 PKCS #12 P2P Peer to Peer PaaS Platform as a Service PAC Proxy Auto Configuration PAM Pluggable Authentication Modules PAP Password Authentication Protocol PAT Port Address Translation PBKDF2 Password-based Key Derivation Function 2 PBX Private Branch Exchange PCAP Packet Capture PEAP Protected Extensible Authentication Protocol PED Personal Electronic Device PEM Privacy-enhanced Electronic Mail PFS Perfect Forward Secrecy PFX Personal Exchange Format PGP Pretty Good Privacy PHI Personal Health Information PII Personally Identifiable Information PIV Personal Identity Verification PKI Public Key Infrastructure POP Post Office Protocol POTS Plain Old Telephone Service PPP Point-to-Point Protocol PPTP Point-to-Point Tunneling Protocol PSK Pre-shared Key PTZ Pan-Tilt-Zoom RA Recovery Agent RA Registration Authority RAD Rapid Application Development RADIUS Remote Authentication Dial-in User Server RAID Redundant Array of Inexpensive Disks RAS Remote Access Server RAT Remote Access Trojan RBAC Role-based Access Control RBAC Rule-based Access Control RC4 Rivest Cipher version 4 RFID Radio Frequency Identifier RIPEMD RACEIntegrityPrimitivesEvaluationMessageDigest ROI Return on Investment RPO Recovery Point Objective RSA Rivest, Shamir, & Adleman RTBH Remotely Triggered Black Hole RTO Recovery Time Objective RTOS Real-time Operating System RTP Real-time Transport Protocol S/MIME Secure/Multipurpose Internet Mail Extensions SaaS Software as a Service SAML Security Assertions Markup Language SAN Storage Area Network SAN Subject Alternative Name SCADA System Control and Data Acquisition SCAP Security Content Automation Protocol SCEP Simple Certificate Enrollment Protocol SCSI Small Computer System Interface SDK Software Development Kit SDLC Software Development Life Cycle SDLM Software Development Life Cycle Methodology SDN Software Defined Network SED Self-encrypting Drive SEH Structured Exception Handler SFTP Secured File Transfer Protocol SHA Secure Hashing Algorithm SHTTP Secure Hypertext Transfer Protocol SIEM Security Information and Event Management SIM Subscriber Identity Module SLA Service Level Agreement SLE Single Loss Expectancy SMS Short Message Service SMTP Simple Mail Transfer Protocol SMTPS Simple Mail Transfer Protocol Secure SNMP Simple Network Management Protocol SOAP Simple Object Access Protocol SoC System on Chip SPIM Spam over Internet Messaging SQL Structured Query Language SRTP Secure Real-Time Protocol SSD Solid State Drive SSH Secure Shell SSL Secure Sockets Layer SSO Single Sign-on STP Shielded Twisted Pair TACACS+ TerminalAccessControllerAccessControlSystemPlus TCP/IP Transmission Control Protocol/Internet Protocol TGT Ticket Granting Ticket TKIP Temporal Key Integrity Protocol TLS Transport Layer Security TOTP Time-based One-time Password TPM Trusted Platform Module TSIG Transaction Signature UAT User Acceptance Testing UAV Unmanned Aerial Vehicle UDP User Datagram Protocol UEFI Unified Extensible Firmware Interface UPS Uninterruptable Power Supply URI Uniform Resource Identifier URL Universal Resource Locator USB Universal Serial Bus USB OTG USB On The Go UTM Unified Threat Management UTP Unshielded Twisted Pair VDE Virtual Desktop Environment VDI Virtual Desktop Infrastructure VLAN Virtual Local Area Network VLSM Variable Length Subnet Masking VM Virtual Machine VoIP Voice over IP VPN Virtual Private Network VTC Video Teleconferencing WAF Web Application Firewall WAP Wireless Access Point WEP Wired Equivalent Privacy WIDS Wireless Intrusion Detection System WIPS Wireless Intrusion Prevention System WORM Write Once Read Many WPA WiFi Protected Access WPA2 WiFi Protected Access 2 WPS WiFi Protected Setup WTLS Wireless TLS XML Extensible Markup Language XOR Exclusive Or XSRF Cross-site Request Forgery XSS Cross-site Scripting
Show moreFrequently asked questions
What is needed for an electronic signature?
How do you sign a PDF doc online?
How do you sign a PDF attachment in an email?
Get more for test initials Request with airSlate SignNow
- Print electronically sign Mother's Day Gift Certificate
- Prove electronically signed Construction Quote Template
- Endorse digisign Restaurant Business Plan Template
- Authorize electronically sign Bonus Plan
- Anneal mark Free Event Ticket
- Justify esign Vacation Rental Short Term Lease Agreement
- Try countersign Laundry Services Proposal Template
- Add Joinder Agreement signatory
- Send Service Receipt Template initials
- Fax Recommendation Letter eSign
- Seal Artist Press Release esigning
- Password Website Standard Terms and Conditions Template digisign
- Pass Tolling Agreement electronic signature
- Renew Bank Loan Agreement countersign
- Test Go To Market Strategy sign
- Require Non-Compete Agreement Template electronically signing
- Comment subscriber signature service
- Champion assignee signature block
- Call for visitor esign
- Void Stock Certificate template electronically signed
- Adopt Investor Rights Agreement template byline
- Vouch Musical Ticket template esigning
- Establish Wedding Photography Quotation template signature block
- Clear Construction Contract Template template signature service
- Complete Discount Voucher template countersign
- Force Bylaws Template template email signature
- Permit Landscape Transforming Appointment Record template signatory
- Customize Construction Contract Agreement template initials