Use Advanced Threat Protection and Sign
Do more online with a globally-trusted eSignature platform
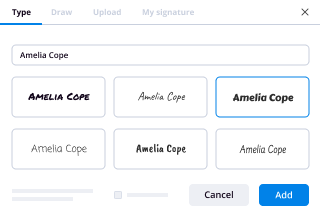
Standout signing experience
Robust reports and analytics
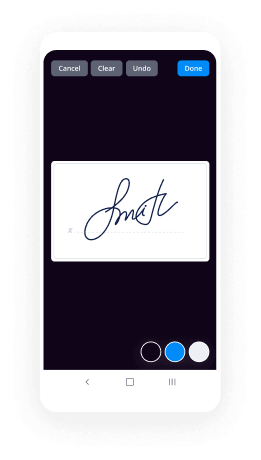
Mobile eSigning in person and remotely
Industry polices and conformity
Use advanced threat protection and sign, faster than ever
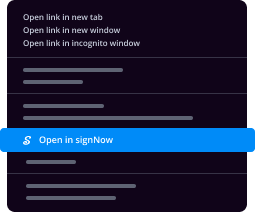
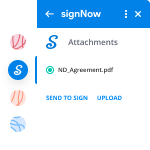
Handy eSignature add-ons
See airSlate SignNow eSignatures in action
airSlate SignNow solutions for better efficiency
Our user reviews speak for themselves






Why choose airSlate SignNow
-
Free 7-day trial. Choose the plan you need and try it risk-free.
-
Honest pricing for full-featured plans. airSlate SignNow offers subscription plans with no overages or hidden fees at renewal.
-
Enterprise-grade security. airSlate SignNow helps you comply with global security standards.

Improve your everyday workflows with the use advanced threat protection and sign feature
Most of the PDF editors readily available on the market offer you basic tools that aren't really helpful for serious eSignature workflows. Just about every program has the ability to add text and shapes. Start using a tool that boasts a professional use advanced threat protection and sign option. Get the flexibility you need for improving your organization’s document management. airSlate SignNow is a comprehensive solution with all the capabilities required for streamlined corporate eSignature workflows.
How to use the use advanced threat protection and sign function in airSlate SignNow:
- Complete your registration. Start with the Free trial button and sign up using your email or your Facebook/Google profile.
- Upload a document. Use the appropriate button near the logo in the upper-left corner and find a file on your device.
- Prepare your sample for reusing. Select More > Make Template to be able to use the form multiple times.
- Get the fillable document. Find the form in the Templates folder and open it. Click Settings > Magic fields to make it faster or request extra text, attachments, stamps and signatures by using tools in the left toolbar.
- Prepare the doc for signing. Double-check the document and open the Edit Signers menu from the left toolbar to assign fields and define a signing order (if required).
- Collect eSignatures. Click Save and Close to leave the editor. Pick the record, choose your preferred way of sending it for signing from the right sidebar, and follow the instructions in the pop-ups. Don't forget about Advanced options if something should be more strict.
- Save the template. Click More > Download to save the PDF file to your device or download it from your email when it's signed.
You can find everything you need for your efficient workflows, starting from the use advanced threat protection and sign feature up to automatic cloud integrations or additional data safety in airSlate SignNow. So don't waste your time. Check out an entirely new approach to document processing!
How it works
airSlate SignNow features that users love
See exceptional results mcafee advanced threat defense
Get legally-binding signatures now!
FAQs microsoft advanced threat protection pricing
-
What is advanced threat protection?
Windows Defender Advanced Threat Protection (ATP) is a Microsoft security product that is designed to help enterprise-class organizations detect and respond to security threats. ATP is a preventative and post-detection, investigative response feature to Windows Defender. -
What is Microsoft advanced threat protection?
Microsoft Office 365 Advanced Threat Protection (ATP) is a cloud-based email filtering service that helps protect your organization against unknown malware and viruses by providing robust zero-day protection, and includes features to safeguard your organization from harmful links in real time. -
What is azure advanced threat protection?
Azure Advanced Threat Protection (ATP) is a cloud-based security solution that leverages your on-premises Active Directory signals to identify, detect, and investigate advanced threats, compromised identities, and malicious insider actions directed at your organization. -
How do I turn off advanced threat protection?
According to the information in this official article, we can turn them off by signing in to https://outlook.live.com. Then select Settings > Premium > Security. There's a toggle under Advanced Security that you can use to turn off Safelinks. Note that turning off Safelinks will only affect future messages you receive. -
How do I set Office 365 advanced threat protection?
Suggested clip How to configure Advanced Threat Protection in Office 365 - YouTubeYouTubeStart of suggested clipEnd of suggested clip How to configure Advanced Threat Protection in Office 365 - YouTube -
What is Sophos advanced threat protection?
Advanced Threat Protection analyzes all network traffic (DNS requests, HTTP requests, or IP packets in general). It also incorporates Intrusion Prevention and Antivirus data if the respective features are activated. Go to Advanced Threat > Advanced Threat Protection. -
What is advanced threat detection?
A Definition of Advanced Threat Detection Advanced threat detection solutions are designed to detect attacks that employ advanced malware and persistent remote access in attempt to steal sensitive corporate data over a length of time. -
What is threat detection and response?
Definition of Threat Detection and Response (TDR) Threat detection and response is about utilizing big data analytics to find threats across large and disparate data sets. The objective is to find anomalies, analyze their threat level, and determine what mitigative action(s) may be required in response. -
What is McAfee advanced threat defense?
Detect advanced malware McAfee® Advanced Threat Defense enables organizations to detect advanced, evasive malware and convert threat information into immediate action and protection. -
How does Microsoft advanced threat protection work?
Microsoft Office 365 Advanced Threat Protection (ATP) is a cloud-based email filtering service that helps protect your organization against unknown malware and viruses by providing robust zero-day protection, and includes features to safeguard your organization from harmful links in real time.
What active users are saying — office 365 advanced threat protection plan 1 pricing
Related searches to exchange online advanced threat protection price
Frequently asked questions
How do you generate a document and apply an electronic signature to it?
How do I add an electronic signature to a Word document?
How can I type my name in the sign field in a PDF?
The ins and outs of eSignature



Find out other advanced threat protection definition
- ESignature Legality for Startup Business Plan in United ...
- ESignature legality for Startup Business Plan in UAE
- Unlock eSignature Legality for Business Letter in ...
- Unlocking eSignature Legality for Business Letters in ...
- ESignature Legality for Business Letter in Australia - ...
- ESignature Legality for Business Letter in European ...
- ESignature Legality for Business Letter in India - ...
- ESignature Legality for Business Letter in Canada - ...
- Unlocking the Power of eSignature Legality for Business ...
- ESignature Legality for Operational Budget in Mexico
- Unlocking eSignature Legality for Business Letters in ...
- Achieve eSignature Legality for Operational Budget in ...
- ESignature Legality for Operational Budget in United ...
- ESignature Legality for Operational Budget in European ...
- ESignature Legality for Operational Budget in Canada - ...
- Maximizing eSignature Legality for Operational Budget ...
- ESignature legality for Operational Budget in UAE
- ESignature Legality for Operational Budget in United ...
- Ensure eSignature Legality for Invoices for Goods in ...
- ESignature Legality for Invoice for Goods in Australia ...