Validate Signed Template with airSlate SignNow
Do more online with a globally-trusted eSignature platform
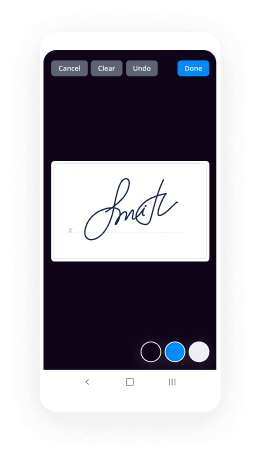
Standout signing experience
Trusted reports and analytics
Mobile eSigning in person and remotely
Industry regulations and compliance
Validate signed template, quicker than ever
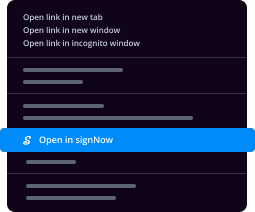
Useful eSignature extensions
See airSlate SignNow eSignatures in action
airSlate SignNow solutions for better efficiency
Our user reviews speak for themselves






Why choose airSlate SignNow
-
Free 7-day trial. Choose the plan you need and try it risk-free.
-
Honest pricing for full-featured plans. airSlate SignNow offers subscription plans with no overages or hidden fees at renewal.
-
Enterprise-grade security. airSlate SignNow helps you comply with global security standards.

Your step-by-step guide — validate signed template
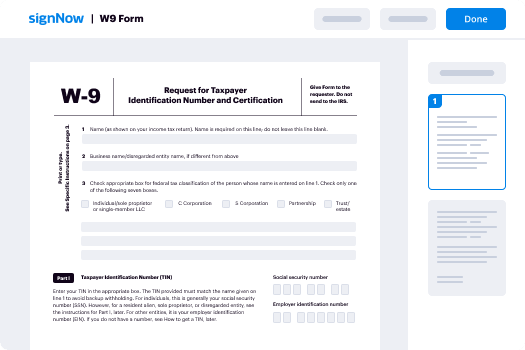
Using airSlate SignNow’s electronic signature any company can speed up signature workflows and sign online in real-time, providing a better experience to consumers and staff members. validate signed template in a couple of easy steps. Our mobile-first apps make operating on the move possible, even while off the internet! Sign documents from any place in the world and close up deals in less time.
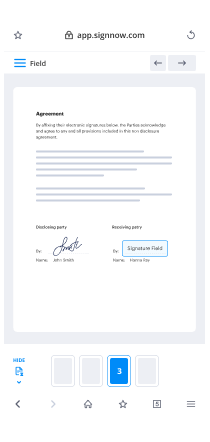
Take a walk-through instruction to validate signed template:
- Sign in to your airSlate SignNow profile.
- Locate your record within your folders or upload a new one.
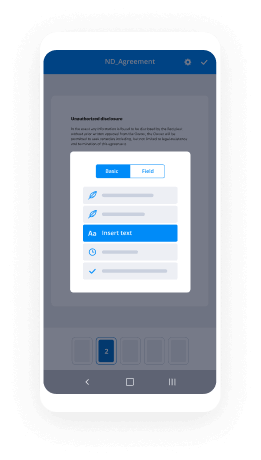
- Open up the template and make edits using the Tools list.
- Drop fillable areas, add text and sign it.
- Include numerous signers using their emails configure the signing sequence.
- Choose which individuals will get an completed doc.
- Use Advanced Options to reduce access to the record and set an expiry date.
- Press Save and Close when finished.
Moreover, there are more enhanced features accessible to validate signed template. Add users to your collaborative work enviroment, view teams, and monitor cooperation. Millions of people across the US and Europe agree that a solution that brings people together in one cohesive enviroment, is what enterprises need to keep workflows performing efficiently. The airSlate SignNow REST API enables you to integrate eSignatures into your app, internet site, CRM or cloud storage. Try out airSlate SignNow and get faster, easier and overall more effective eSignature workflows!
How it works
airSlate SignNow features that users love
See exceptional results validate signed template with airSlate SignNow
Get legally-binding signatures now!
FAQs
-
How can I validate my signature?
Open a PDF document containing a digital signature. Right-click a signature on the page and then select Verify Signature from the shortcut menu. The Validation Status information box shows the results. Click Properties for more information about the signature. -
How do I validate a digital signature in Word?
Open the Word document, Excel spreadsheet or PowerPoint presentation that has a digital signature. Double click the signature line. ... The Signatures pane appears. ... The Signature Details dialog appears. For more certificate information, click View. The Certificate dialog appears. -
How can I validate my digital signature in Aadhar card?
Right click on the 'validity unknown' icon and click on 'Validate Signature' You will get the signature validation status window, click on 'Signature Properties'. Click on 'Show Certificate. ... Verify that there is a certification path named 'NIC sub-CA for NIC 2011, National Informatics centre'. -
How can I validate my Aadhar card signature?
Click on Signature and then click on Show Signature Properties. Open a Tab named \u201cTrust\u201d located in the Upper Bar of options. Click on \u201cAdd to Trusted Certificates.\u201d Tick mark all the Options and click ok. Finally Click Validate Aadhar and done. -
How can I download Aadhar card with valid signature?
Step 1: First, you have to right-click on the validity unknown icon. Step 2: Click on the Validate Signature option in the next step. Step 3: You have to click on the Signature Properties option after getting the signature validation status window. -
How do I validate my signature in PDF?
Open a PDF document containing a digital signature. Right-click a signature on the page and then select Verify Signature from the shortcut menu. The Validation Status information box shows the results. Click Properties for more information about the signature. -
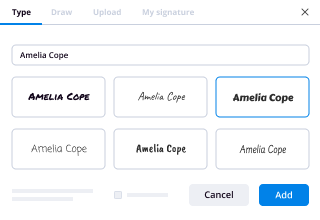
How do I add a signature to a PDF?
Open the PDF file in airSlate SignNow Reader. Click on Fill & Sign in the Tools pane on the right. Click Sign, and then select Add Signature. A popup will open, giving you three options\u2014Type, Draw, and Image. Once you're done, click the Apply button. Drag, resize and position the signature inside your PDF file. -
How do I validate my signature in CCC certificate?
Steps to Validate the Signature. Download the certificate in Internet Explorer only and save the pdf file. \u2022 ... Click on Validate Signature and Close, signature will be validated with Green Checkmark. ... Select Anurag Shah. ... Now click on ? ... Click on show signer's. ... Click on check boxes as shown below and click O. -
How do I turn off signNowature panel?
To remove a digital signature, right-click the signature field and choose Clear Signature. To remove all digital signatures in a PDF, choose Clear All Signature Fields from the options menu in the Signatures panel. -
How do I validate an signNowature?
Open a PDF document containing a digital signature. Right-click a signature on the page and then select Verify Signature from the shortcut menu. The Validation Status information box shows the results. Click Properties for more information about the signature. -
How do I know if a certificate is valid?
Click the padlock. Start by clicking the padlock icon in the address bar for whatever website you're on. Click on Valid. In the pop-up box, click on \u201cValid\u201d under the \u201cCertificate\u201d prompt. Check the Expiration Data. -
How does browser verify certificate?
Your web browser comes installed with the public keys of all of the major certificate authorities. It uses this public key to verify that the web server's certificate was indeed signed by the trusted certificate authority. The certificate contains the domain name and/or ip address of the web server. -
How can I validate my signature in Aadhar card?
Right click on the 'validity unknown' icon and click on 'Validate Signature' You will get the signature validation status window, click on 'Signature Properties'. Click on 'Show Certificate. ... Verify that there is a certification path named 'NIC sub-CA for NIC 2011, National Informatics centre'.
What active users are saying — validate signed template
Validate signed template
hello everyone today I want to talk a little bit about JSON web tokens or JW T's in particular I want to show you an option that I don't think is well known which is the use of public key signature with these tokens so I'm going to start by giving you a brief introduction to PI JWT which is the package that I use when I work with JWT tokens in Python so I'm going to create a virtual environment where I can install PI JWT I'm going to activate it and then pip install PI JWT there we go so I'm going to show you how to create a token in a Python session I'm going to use just the Python console for this and the the function that you use comes from the JWT package and it's JWT and code and this function takes three arguments the first argument is the payload and this is going to be the information that's going to be stored in the token and if you're not familiar with JWT tokens the great thing that they have is that you can store information in them so I'm going to create a dictionary that's going to be my payload in most cases this is a one or more variables that identify the user that owns the token so in this example and sent user ID say 1 2 3 and this is going to be my payload I also need to have a secret key and this is what makes the JWT secure because all tokens come with a cryptographic signature that prevents anybody for making changes to the token so for secret key in this example I'm just going to just type some random characters here we go so that's my secret key for this example if you're using flask or Django you can use the secret key configuration variable for for encoding JW T's that's perfectly fine that's what I usually do when I work with this type of signature so now I'm ready to generate my token so I'm going to call Jacob T encode the first argument is my payload the second argument is my key and the third and final argument is the signature algorithm that I want to use and the vast majority of people here use a logarithm that's called HS 256 so that's what I'm what I'm going to use here the return value of JWT and code is a token that's given as a byte sequence so to make it a little bit more convenient since it's all printable characters I'm going to decode it into a utf-8 string so there we go now I can show my token and that we have the token so the most important thing with these tokens is to not be fooled into thinking that the token is encrypted the token is not encrypted so this this payload that we sent is actually here this is the payload and it's encoded in base64 but this is not encryption anybody that knows a little bit can decode this back into the dictionary and in fact I showed how to do this in a previous video where I showed how to decode flask user sessions and this is actually exactly the same so so remember that this is not encrypted you should not store anything that's sensitive so only information that you don't mind others to see so in case you're curious this part is a header this contains some information that describes the structure of the token and this part is the signature and this is what makes the token secure because if I try to hack this this portion and change for example change the user ID then that is going to invalidate the signature and if I don't have the secret key then I have no way to generate any signature that matches the new content so that that's what makes JWT tokens secure so okay so now I have my token before I move on to decoding I'm going to show you another thing there are other things that you can put in the payload and one that's very interesting is an expiration date so my ex key which is this is predefined it's mentioned in the image ad specification and actually I need to input time to do this so I'm gonna import time so that I can get my current time and here I can say time plus I don't know 120 that will be two minutes so this token will be valid for only for two minutes so let's - let's make this token - and now we have two example tokens so once your server generates a token it needs to return it to the client and then in future calls the client will authenticate to you or to your server using this this token and the way that works is when the server receives the token in it for example in an API call it needs to figure out if the token is valid and for that we use the JWT decode function this function takes the token as the first argument secret key a second argument and the third argument is a list of algorithms that are valid for for this token so this is in case you support more than one algorithm the decode function accepts a list of algorithms that you want to be allowed for this token so in this case I'm only going to use the same HS 256 and when I do call this I get my my payload back now if I use an invalid token so let's say I'm just gonna add an extra character to do this token just to make it different then I get invalid signature if I change the signature same thing I'm gonna get invalid signature and this is what makes this is when I know that the token is invalid and I will not allow the API call whatever the client wants me to do in the server if I cannot validate their token so I think there's probably been more than two minutes so if I try to decode token two which is the one half expiration I get an expired signature error so same thing and this is this is super useful because if you make your tokens life they use the life of the token short then you reduce any risk if that token were to be compromised so this is what most people do and what I want to show you is something different because this this usage of JW T's have a disadvantage and that disadvantage is that to decode a token you need to have access to the secret key and if you have a application that is monolithic so basically have a single process where you have both the token generation and they took in verification then this is usually not a problem but these days a lot of people write applications in a distributed fashion so you have multiple services maybe two or three or if you go full-blown micro services you may have twenty or more so in those situations you may have a service that is in charge of generating tokens and then many of the other services may be receiving those tokens as authentication so if if all those services need to call into the authentication service to validate a token then authentication service becomes a bottleneck so what's ideal is that each service can validate they token without having to make calls into other services so you can do that by having the secret key available to all the services but of course that that's more of a security risk because the more places you have your secret key the more the risk of that key getting compromised any thinking it's compromised then the person who has the key can generate new tokens and that's so all of that to say that in using distributed systems this is not really a great idea so with public key signatures the the benefit it it basically works in the same way but the benefit is that to decode the token you don't need to have the secret key and that's that's the main advantage so I'm going to show you how that works quickly and the first thing you need to do when you work with public key signatures is to install another package cryptography and PI GWT supports all those public key algorithms for signatures but it needs to have cryptography installed for those to be enabled because it depends on the cryptographic algorithms in this package so that's installed and then I'm gonna show you one of the algorithms for public key signatures that's based on RS a cryptography and for our say you need for RSA public key encryption and signing you need to create what's called a key pair which is a combination of a private and a public key so we're gonna have two keys not one and there are a few ways to generate these keys the one that I like is to use I'm gonna clear the screen here ssh-keygen this is a utility that comes with OpenSSH which if you have any anything linux or mac OS related you have on windows if you're not using the the linux support then you will need to find a Windows port and install it but it's also available so I'm going to ask for a key of type RSA and I'm gonna set the length of the key to 4096 bits which is what these days is recommended as a secure key length so this is going to create my public and private keys it's asking me for a name for these keys I'm going to call it JW TP this is gonna go in the current directory because I'm not using any any path names I'm not gonna use a passphrase because it's not useful for this usage so I'm going to leave those empty and now I have let's see I have this file which is my private key and this other file which is the same name with doc pub which is my public key so this file I need to protect with my life basically I need to make sure that nobody has access to this file so this file is not going to go into gate I'm not gonna put it in any source control or anywhere where it basic there's a risk that the people that are not authorized to see it will will have access to to it this file on the other side is perfectly fine to share and I'm just going to show you what it is because it basically it holds no no sensitive information there's absolutely no problem if this file is seen you should actually put it in anywhere anywhere where it's public because anybody who who wants to verify tokens will need to have this file so ok so now we have we have our key pair so let's go back to Python and import JWT I'm gonna set my payload again or I'm gonna use the same thing and then my private key I'm gonna call it private key to make sure that I don't confuse these two keys it's going to be the contents of they are the private files so I'm going to open G grab T key and read the contents into this variable that's that's my my private key so now my token is going to be jail empty and code the payload the private key and the algorithm which is going to be RS 256 this is the algorithm that uses RSA signatures and then this is going to be decoded into coops UTF see if it works utf-8 of course not utf-8 here oh okay there we go so the tokens look more or less the same they're a little bit longer but but yeah otherwise they have the same structure you can you can identify the three components with the the periods that act as separators here's the payload which looks actually identical to the previous token because as I said this is a simple base64 encoding of the payload with no encryption so so this is my token and now just to make sure that that this is clear I'm going to exit my Python session and that will clear any any storage of the private key which I'm not going to use so I'm going to start a new session that's clean and now I'm going to assign I'm gonna copy the token back here and I'm going to use the public key which is actually I don't even need to read it from a file I can just take this and paste it here because this is public doesn't matter and to the coded token I'm going to say in GWT decode and then token the public key and then algorithms it's going to be RS 256 and that gives me my my payload back and this was done without using any secrets so the decoding in this case is completely done in the open anybody can verify the tokens that are generated but nobody can generate the tokens unless you manage to steal my private key the private key that I haven't shown you so so that's the key for this I think it's a great usage of JWT that that many people don't know about so I hope you adopt this and basically make your your service more secure by not exposing your secret key to all those other services that need to decode tokens so anyway if you are interested about more details about this there's a blog article you can see the link to it in the description of this video so you're welcome to check it out and if you have any questions feel free to let me know I'll be happy to answer them thank you
Show moreFrequently asked questions
How do I add an electronic signature to a PDF in Google Chrome?
How can I get someone to sign my PDF?
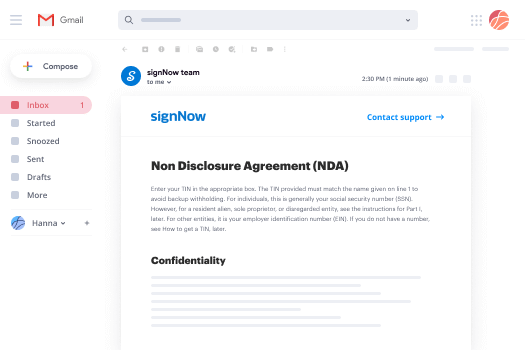
How can I sign an emailed PDF doc online?
Get more for validate signed template with airSlate SignNow
- Print electronically sign Vocabulary Worksheet Template
- Prove electronically signed Budget Proposal
- Endorse digisign Cohabitation Agreement
- Authorize electronically sign House Cleaning Proposal Template
- Anneal mark Go To Market Strategy
- Justify esign Personal Reference Letter
- Try countersign Hourly Invoice
- Add Settlement Agreement esigning
- Send Freelance Graphic Design Contract Template digisign
- Fax Letter of Recommendation for a Teacher Colleague electronic signature
- Seal Trainee Daily Progress Report countersign
- Password IRS Form 1040-ES sign
- Pass Demand For Payment Letter electronically signing
- Renew Florida Condo Lease Agreement eSign
- Test Church Donation Receipt eSignature
- Require Consignment Agreement Template autograph
- Print guest initials
- Champion roomer signatory
- Call for cashier email signature
- Void Photo Licensing Agreement template signature block
- Adopt Deposit Agreement template signature service
- Vouch Prom Ticket template countersign
- Establish Photography Gift Certificate template signatory
- Clear Training Proposal Template template initials
- Complete Landscaping Work Order template eSign
- Force PR (Public Relations) Proposal Template template byline
- Permit Truck Driver Application template esigning
- Customize Affidavit of Death template digisign