Verify Digital Signature Order with airSlate SignNow
Improve your document workflow with airSlate SignNow
Versatile eSignature workflows
Fast visibility into document status
Easy and fast integration set up
Verify digital signature order on any device
Advanced Audit Trail
Strict security standards
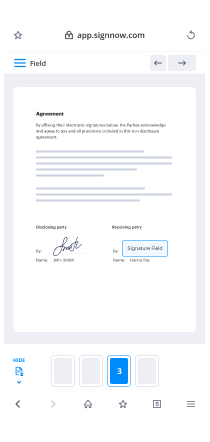
See airSlate SignNow eSignatures in action
airSlate SignNow solutions for better efficiency
Our user reviews speak for themselves






Why choose airSlate SignNow
-
Free 7-day trial. Choose the plan you need and try it risk-free.
-
Honest pricing for full-featured plans. airSlate SignNow offers subscription plans with no overages or hidden fees at renewal.
-
Enterprise-grade security. airSlate SignNow helps you comply with global security standards.

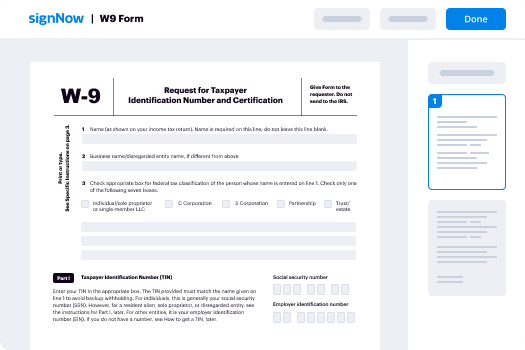
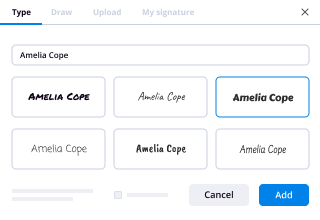
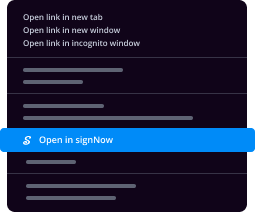
Your step-by-step guide — verify digital signature order
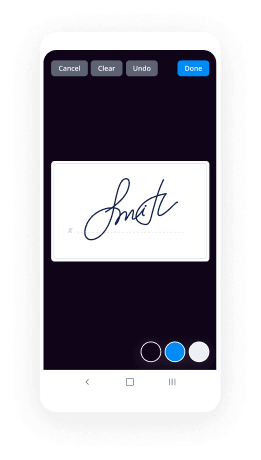
Using airSlate SignNow’s eSignature any business can speed up signature workflows and sign online in real-time, supplying a greater experience to clients and staff members. verify digital signature order in a couple of simple steps. Our handheld mobile apps make work on the go feasible, even while off-line! Sign contracts from anywhere in the world and close up deals quicker.
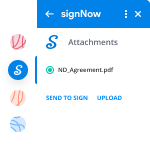
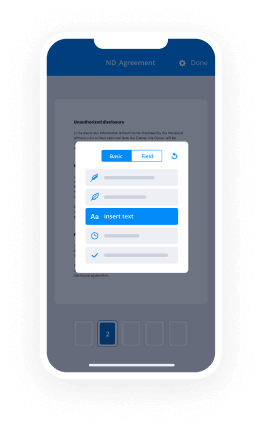
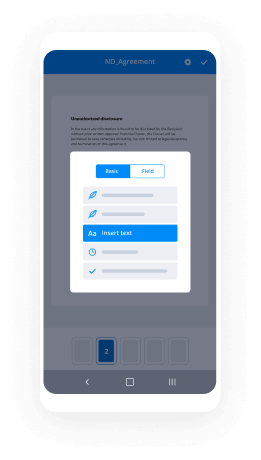
Keep to the walk-through guide to verify digital signature order:
- Log on to your airSlate SignNow profile.
- Locate your needed form in your folders or upload a new one.
- the document adjust using the Tools list.
- Drop fillable areas, type textual content and eSign it.
- List numerous signers via emails and set up the signing sequence.
- Indicate which users can get an executed doc.
- Use Advanced Options to reduce access to the document and set an expiration date.
- Click on Save and Close when done.
Moreover, there are more innovative features available to verify digital signature order. List users to your common work enviroment, view teams, and track collaboration. Numerous users across the US and Europe recognize that a solution that brings people together in a single unified digital location, is the thing that companies need to keep workflows functioning smoothly. The airSlate SignNow REST API allows you to embed eSignatures into your app, website, CRM or cloud storage. Check out airSlate SignNow and enjoy quicker, smoother and overall more effective eSignature workflows!
How it works
airSlate SignNow features that users love
See exceptional results verify digital signature order with airSlate SignNow
Get legally-binding signatures now!
FAQs
-
How do you verify a digital signature?
Open a PDF document containing a digital signature. Right-click a signature on the page and then select Verify Signature from the shortcut menu. The Validation Status information box shows the results. Click Properties for more information about the signature. -
How is digital signature computed and verified?
The computed hash is encrypted by the private key of sender resulting in the digital signature. The digital signature is sent along with the original file for its verification by the receiver. ... Sender decrypts the digital signature by using the public key of the sender to get the hash sent by the sender. -
How digital signature is created and verified?
Digital signatures are typically made in a two-step process. ... Thus, when a signature is verified by the public key, it decrypts to a hash matching the message. That hash can only be decrypted using the public key if it were encrypted with the private signing key. Public keys are created by the keypair owner. -
How is digital certificate verified?
Digital certificates are issued by trusted parties, called certificate authorities, to verify the identity of an entity, such as a client or server. ... The CA checks your signature using your public key and performs some level of verification of your identity (this varies with different CAs). -
How do I verify a signature on airSlate SignNow PDF?
Open the Preferences dialog box. Under Categories, select Signatures. For Verification, click More. To automatically validate all signatures in a PDF when you open the document, select Verify Signatures When The Document Is Opened. -
Does airSlate SignNow verify identity?
airSlate SignNow ID Verification is fully integrated with airSlate SignNow eSignature, enabling customers to securely verify signers' identities prior to accessing the agreement. ... After a successful verification, the signer can view the agreement and sign as usual. -
How digital signatures are generated and verified?
Signature Verification Algorithms : Verifier receives Digital Signature along with the data. It then uses Verification algorithm to process on the digital signature and the public key (verification key) and generates some value. It also applies the same hash function on the received data and generates a hash value. -
Can digital signature be forged?
With digital signatures, forgery is next to impossible \u2013 much more difficult than forging a handwritten signature. First, a digital signature is more of a process than just affixing a signature. ... If the results are the same, the signature is valid; if they are different, the signature is not valid. -
Can digital signature be misused?
Yeah it can be misused but which shall rarely happen. Only people who knows you and your documentation ( for which you use digital signature ) can misuse. But there is NO BIG deal in it. If someone receives a document which is signed by 'your' digital signature. -
What is digital forgery?
Digital forgery (or digital tampering) is the process of manipulating documents or images for the intent of financial, social or political gain. This airSlate SignNow provides a brief introduction to the digital forgery.
What active users are saying — verify digital signature order
Related searches to verify digital signature order with airSlate airSlate SignNow
Validate Electronic Signature Document Later
hi there welcome to the CBT Nuggets micro nugget this is the second in a short series we're doing called the malware hunter this episode is called verifying digital signatures my name is Tim Worner and I'm a cbt nuggets trainer why are digital signatures important in hunting malware well by way of background friends first we need to remember that digitally signing code and by code we're talking about executable code exe files as well as dynamic link library assemblies that contain code etc that by developers purchasing a code signing certificate from a reputable certification Authority and then signing their code they're giving us the consumer of their software authentication and integrity authentication means we have faith or actually it's more than faith it's trust that the person or entity that's given us some executable code or from whom we've purchased that code is who they say they are and integrity means that not a single bit of that executable code has been modified in between it being on their servers or wherever we downloaded it and our own systems that's key we don't want to be in the situation where we have legitimate software XYZ and instead of downloading it from the vendors site which is always the recommendation we download it from another site and little do we know that that codes been modified or transformed into ABC and when we install it the program installs just fine seems to work just fine little did we know that that modification installed some piece of malware on our system and who knows what is happening from there do you see what I mean so digitally signing code to me is a no-brainer that any software developer needs to do digital signatures in code signing are related they relate to public key cryptography here's what happens in a nutshell a developer creates a hash of their code module they run their module through a known hashing algorithm and then encrypts that hash with a private key this is a digital signature as it's called in public key crypto the private key is private to the owner of the account owner of the certificate on the other hand users who download your software receive a copy of the digital certificate the users public key the shared component that fits finger and glove with the corresponding private key and the downloader actually it's not the person but the operating system will use that public key to decrypt the hash and then compute the hash based on the code module and if the code has been tampered with even as little as a single bit difference then when we run the hash on the client side we're going to get a completely different number and that's going to fail the integrity check you see now then how can we translate that geek speek into something that a male where hunter can understand as you know we're focusing on the microsoft technet...
Show more