Exercer L'enregistrement Des E-mails. Utilisez Des Outils De Signature électronique Qui Fonctionnent Où Vous êtes.
Obtenez les fonctionnalités de signature électronique puissantes dont vous avez besoin avec la solution en laquelle vous avez confiance
Choisissez le service professionnel conçu pour les professionnels
Configurez l'API de signature électronique facilement
Collaborez mieux ensemble
Exercer l'enregistrement des e-mails, en quelques minutes
Réduisez le délai de clôture
Maintenez les données importantes en sécurité
Découvrez les signatures électroniques airSlate SignNow en action
Solutions airSlate SignNow pour une meilleure efficacité
Les avis de nos utilisateurs parlent d'eux-mêmes






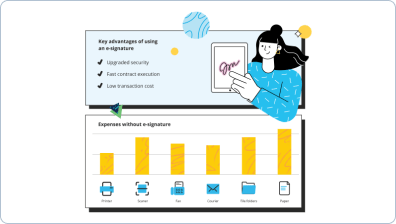
Pourquoi choisir airSlate SignNow
-
Essai gratuit de 7 jours. Choisissez le forfait dont vous avez besoin et essayez-le sans risque.
-
Tarification honnête pour des forfaits complets. airSlate SignNow propose des abonnements sans frais supplémentaires ni frais cachés lors du renouvellement.
-
Sécurité de niveau entreprise. airSlate SignNow vous aide à respecter les normes de sécurité mondiales.

Votre guide étape par étape — excise email record
Exercer l'enregistrement des e-mails. Obtenez la meilleure valeur du système de signature électronique le plus fiable et sécurisé. Améliorez vos transactions électroniques en utilisant airSlate SignNow. Optimisez les flux de travail pour tout, des simples dossiers du personnel aux accords complexes et modèles de vente.
Comprenez comment exercer l'enregistrement des e-mails :
- Téléchargez plusieurs pages depuis votre ordinateur ou stockage cloud.
- Faites glisser et déposez des cases personnalisables (signature, texte, date/heure).
- Modifiez la taille des champs en appuyant dessus et en sélectionnant Ajuster la taille.
- Placez des cases à cocher, des menus déroulants et des groupes de boutons radio.
- Modifiez les signataires et créez la demande pour des matériaux supplémentaires.
- Exercez l'enregistrement des e-mails.
- Incluez la formule où vous souhaitez que le champ apparaisse.
- Ajoutez des remarques et des annotations pour les destinataires n'importe où sur la page.
- Enregistrez toutes les modifications en cliquant simplement sur TERMINÉ.
Connectez des utilisateurs de l'extérieur et de l'intérieur de votre entreprise pour travailler électroniquement sur des documents importants et exercer l'enregistrement des e-mails à tout moment et sur n'importe quel système en utilisant airSlate SignNow. Vous pouvez suivre chaque activité effectuée sur vos documents, recevoir des notifications et un rapport d'audit. Restez concentré sur votre entreprise et vos partenariats clients tout en ayant la certitude que vos données sont précises et sécurisées.
Comment ça marche
Fonctionnalités airSlate SignNow appréciées par les utilisateurs
Découvrez des résultats exceptionnels Exercer l'enregistrement des e-mails. Utilisez des outils de signature électronique qui fonctionnent où vous êtes.
Obtenez des signatures juridiquement contraignantes dès maintenant !
FAQ
-
Comment puis-je déclarer la taxe d'accise ?
Le formulaire 720, la déclaration trimestrielle de taxe d'accise fédérale, est utilisé pour déclarer et payer les taxes d'accise collectées par l'entreprise pour une variété de produits et services. Utilisez l'annexe A pour indiquer le montant de votre responsabilité totale pour les taxes d'accise du trimestre. -
Comment la taxe d'accise est-elle payée ?
Les taxes d'accise sont des taxes payées lors de l'achat d'un bien spécifique, comme l'essence. Les taxes d'accise sont souvent incluses dans le prix du produit. Il existe également des taxes d'accise sur des activités, telles que les paris ou l'utilisation de l'autoroute par les camions. L'un des principaux composants du programme d'accise est le carburant moteur. -
Pourquoi payons-nous la taxe d'accise ?
Les taxes d'accise sont des taxes requises sur certains biens ou services comme le carburant, le tabac et l'alcool. Les taxes d'accise sont principalement des taxes que les entreprises doivent payer, ce qui augmente généralement les prix pour les consommateurs de manière indirecte. -
Comment les taxes d'accise sont-elles collectées ?
Les taxes d'accise sont collectées par t
Ce que disent les utilisateurs actifs — excise email record
Questions fréquemment posées
Comment ajouter une signature électronique à un formulaire ou un contrat ?
Que dois-je faire pour signer électroniquement un PDF ?
Comment puis-je signer un PDF créé à partir d'une image ?
Obtenez plus pour excise email record
- AirSlate SignNow CRM vs. Zoho CRM pour l'enseignement supérieur
- AirSlate SignNow CRM vs. Zoho CRM pour l'industrie de l'assurance
- AirSlate SignNow CRM vs. Zoho CRM pour les services juridiques
- AirSlate SignNow CRM vs. Zoho CRM pour les sciences de la vie
- AirSlate SignNow CRM vs. Zoho CRM pour Hypothèque
- AirSlate SignNow CRM vs. Zoho CRM pour les organisations à but non lucratif
- AirSlate SignNow CRM vs. Zoho CRM pour l'immobilier
- AirSlate SignNow CRM vs. Zoho CRM pour le commerce de détail
Tout savoir sur la signature électronique

Découvrez d'autres excise email record
- Essayez les eSignatures sans couture : télécharger ...
- Explorez votre signature numérique – Questions ...
- Commencez votre parcours de signature électronique : ...
- Découvrez les fonctionnalités populaires des ...
- Explorez les fonctionnalités populaires des ...
- Explorez les fonctionnalités populaires d'eSignature : ...
- Améliorez votre expérience Google : signature ...
- Découvrez les fonctionnalités populaires d'eSignature ...
- Explorez les fonctionnalités populaires des ...
- Découvrez les fonctionnalités populaires d'eSignature ...
- Découvrez les fonctionnalités populaires de la ...
- Profitez de flux de travail eSignature flexibles : ...
- Commencez avec eSignature : capture de signature sur le ...
- Suivez des Instructions Simples : signature manuscrite ...
- Commencez avec eSignature : quelle application puis-je ...
- Explore Online Signature: what are electronic ...
- Explorez la signature en ligne : ce qui constitue une ...
- Explorez la signature en ligne : ce qui constitue une ...
- Explorez la signature en ligne : ce qui constitue une ...
- Explorez la signature en ligne : ce qui compte comme ...













































