Submit eSign Presentation Secure
Make the most out of your eSignature workflows with airSlate SignNow
Extensive suite of eSignature tools
Robust integration and API capabilities
Advanced security and compliance
Various collaboration tools
Enjoyable and stress-free signing experience
Extensive support
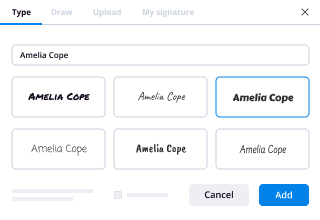
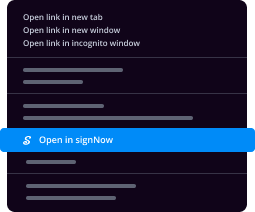
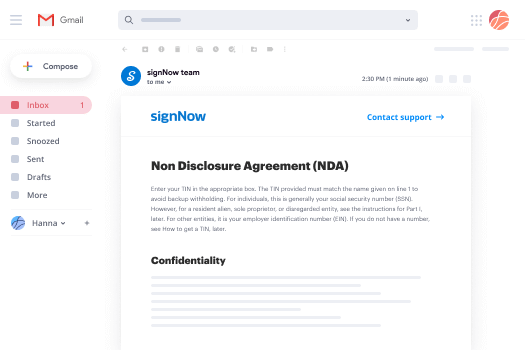
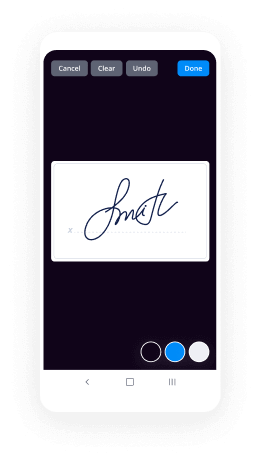
How To Add Sign in eSignPay
Keep your eSignature workflows on track
Our user reviews speak for themselves






Submit eSign Presentation Secure. Discover probably the most end user-warm and friendly experience with airSlate SignNow. Manage your whole document finalizing and expressing method electronically. Range from hand held, papers-dependent and erroneous workflows to automatic, digital and perfect. You can actually create, supply and indicator any papers on any system anywhere. Be sure that your essential organization cases don't slip over the top.
Learn how to Submit eSign Presentation Secure. Adhere to the straightforward manual to get started:
- Design your airSlate SignNow account in click throughs or log on with your Facebook or Google bank account.
- Benefit from the 30-day free trial version or go with a costs plan that's great for you.
- Locate any authorized format, construct on the web fillable kinds and discuss them tightly.
- Use innovative capabilities to Submit eSign Presentation Secure.
- Signal, personalize signing order and acquire in-person signatures ten times speedier.
- Established automatic alerts and obtain notifications at every phase.
Relocating your jobs into airSlate SignNow is simple. What adheres to is a simple method to Submit eSign Presentation Secure, as well as ideas and also hardwearing . colleagues and companions for much better cooperation. Inspire your staff with the finest resources to stay in addition to organization operations. Improve efficiency and range your business speedier.
How it works
Rate your experience
-
Best ROI. Our customers achieve an average 7x ROI within the first six months.
-
Scales with your use cases. From SMBs to mid-market, airSlate SignNow delivers results for businesses of all sizes.
-
Intuitive UI and API. Sign and send documents from your apps in minutes.
A smarter way to work: —how to industry sign banking integrate
FAQs
-
Is airSlate SignNow eSign secure?
Are airSlate SignNow electronic signatures secure? Yes. At airSlate SignNow, the security of your digital experiences is our priority. Industry-standard security practices are deeply ingrained into our internal culture, software development, and service operations processes.
-
Is airSlate SignNow secure?
Is airSlate SignNow secure? Yes. At airSlate SignNow, the security of your digital experiences is our priority. Industry standard security practices are deeply ingrained into our internal culture, software development, as well as service operations processes.
-
Is airSlate SignNow Esign secure?
Are airSlate SignNow electronic signatures secure? Yes. At airSlate SignNow, the security of your digital experiences is our priority. Industry-standard security practices are deeply ingrained into our internal culture, software development, and service operations processes.
-
Is airSlate SignNow eSign secure?
Are airSlate SignNow electronic signatures secure? Yes. At airSlate SignNow, the security of your digital experiences is our priority. Industry-standard security practices are deeply ingrained into our internal culture, software development, and service operations processes.
-
Is airSlate SignNow secure?
Is airSlate SignNow secure? Yes. At airSlate SignNow, the security of your digital experiences is our priority. Industry standard security practices are deeply ingrained into our internal culture, software development, as well as service operations processes.
-
Is airSlate SignNow Esign secure?
Are airSlate SignNow electronic signatures secure? Yes. At airSlate SignNow, the security of your digital experiences is our priority. Industry-standard security practices are deeply ingrained into our internal culture, software development, and service operations processes.
-
Was Donald Trump, Jr. set up?
I think there are two ways to answer this question — what’s likely, and what’s possible.I think what is likely, is that Don Jr. was not set up for anything except failure — meaning that there was no malicious plan to screw him over, he just did it to himself by lacking competence in what he was trying to do.But that’s not the only possibility.There is an argument that can be made that Jared Kushner set him up. Bear with me for a minute while I present it.It basically goes like this — Jared Kushner and Don Jr. were both present at the meeting with the Russians, thus having first-hand knowledge of its content and participants.[1] They also both knew about the intent of the meeting (collusion with the Russian government to support Trump and undermine Clinton) because it’s explicitly stated in the emails they both received. [2]Kushner failed to disclose that meeting — or literally any other foreign contact — on his SF-86 form (this is the form that federal government employees submit for their security clearances). [3] He later amended his SF-86 form two times to disclose that meeting and over 100 foreign contacts.[4]His explanation for why he initially omitted these meetings — from a document that includes a sworn statement under penalty of felony criminal charges that the information within is complete to the best of your knowledge — is that a member of his staff “prematurely” submitted the form in error. [5] As I can personally verify, having gone through the SF-86 process for my own clearance, that’s not really a possibility unless you accidentally clicked the wrong button 28 times in a row, accidentally e-signed it, and accidentally gave your legal medical release as well. (It’s a VERY long form, with a lot of confirmations).[6] So as anyone whose ever gotten a security clearance can tell you, that explanation is bogus. Now, if you forget to disclose a meeting or two on that form, or you got a date or name wrong — not unusual for very experienced applicants, or people in senior positions in certain fields — you can amend the form to include the names you missed. It’s unusual to do that more than once, or as widely as Kushner did.Now, here’s where it gets really interesting. Look at the timeline —June 9, 2016, is the meeting with the Russians.January 18, 2017: Kushner files his initial SF-86 which fails to disclose the foreign contacts. Kushner allegedly notifies the FBI “the next day” that he would fill in the missing information later. [7]April 6, 2017: New York Times reports that Kushner failed to disclose numerous meetings, including with Russian Amb. Sergei Kisylak. [8]May 11, 2017: Kushner files a first revision to his SF-86, and receives what is believed to be standard questioning from the FBI some time in mid-May.[9]“Third week of June, 2017” (exact date unknown) Marc Kasowitz, Trump’s personal attorney; and Alan Garten, chief legal officer for the Trump Organization, are informed of the existence of the emails, by Kushner’s attorneys (who had “discovered” the emails). [10]June 21, 2017: Kushner files his second revision to the SF-86. This discloses the Russian meeting to the FBI. [11]June 23, 2017: The FBI questions Kushner again over the second revision.[12] This is NOT standard.July 9–11: NY Times breaks the story of the Russian meeting, and the emails. After being contacted by the Times, Don Jr. chooses to release the emails via his twitter, before the Times can publish their story. During this time Don Jr.’s characterization of the meeting is first that it was about adoptions; then that it was about opposition research but they didn’t get any so it ended up being about adoptions; and finally admitting (with the release of the emails) that it was about the damaging information provided from the Russians, as explained clearly in the emails. At least one of these statements was drafted with the consultation of the White House legal team, and was “signed off” on by Trump himself. [13]July 12: Trump says “I only heard of it two or three days ago” (referring to the meeting). [14] In order for that to be true, it would require that two of Trump’s children, his campaign manager, his personal lawyer, the lawyers for his children, and the chief legal officer intentionally kept that information from Trump for at least two to three weeks (or in the case of Kushner/Jr./Manafort, for over a year.)So it begs the question — since Kushner knew of the meetings, had already disclosed them to the FBI (quietly, through the second SF-86 amendment, without trying to draw attention to it), and knew how damaging the information would be to their credibility on the Russia collusion question— why was Don Jr. allowed to make statements that Kushner and others knew weeks in advance were false?The answer is of course up to interpretation, but “what is possible” is that Kushner and Trump, knowing that the contents of the Russian meeting email would be going public sooner rather than later (since the media already had learned of the meeting), are attempting to set up Don Jr. to take the fall. By directing the media’s attention to Jr., who can be laughed off as an incompetent idiot who didn’t know what he was doing, Kushner buys more time for himself, taking some of the heat away from himself and his father-in-law, during the critical days ahead of the Trumpcare healthcare vote. Incidentally, Don Jr. makes for a great fall-guy, because even though he unofficially “advises” his father, he’s technically still an uncleared, private civilian who is subject to far fewer rules on disclosure, transparency, and honesty as Kushner is. And we know that the Trump organization places a high premium on protecting Kushner, who (along with Ivanka) is probably the single most influential person on Trump inside or outside the entire administration. [15]It’s also been speculated that the source of the leaks may not actually be Kushner, but could be Steve Bannon — who dislikes Kushner intensely and has been in a political power struggle with him since the transition.[16] If that’s true, then Jr. isn’t so much being “set up” so much as he’s “collateral damage.”Again, I think the most likely explanation is that Don Jr. is simply an incompetent idiot. But we know Jared Kushner, while he may not be “competent” in the traditional Washington sense, is not an idiot. He’s the one to keep an eye on here, not Don Jr.Footnotes[1] Trump Tower Russia meeting: At least eight people in the room[2] Kushner Omitted Meeting With Russians on Security Clearance Forms[3] Details revealed about Jared Kushner's security clearance forms[4] Details revealed about Jared Kushner's security clearance forms[5] Kushner’s lawyers say he mistakenly left meetings with the Russians off his security forms twice[6] https://nbib.opm.gov/record-prov...[7] People aren't buying Kushner's lawyers' explanation for security clearance form omissions[8] Kushner Omitted Meeting With Russians on Security Clearance Forms[9] Sources: Trump lawyers knew of Russia emails three weeks ago[10] Sources: Trump lawyers knew of Russia emails three weeks ago[11] Sources: Trump lawyers knew of Russia emails three weeks ago[12] Sources: Trump lawyers knew of Russia emails three weeks ago[13] Rancor at White House as Russia Story Refuses to Let the Page Turn[14] Trump says he learned ‘couple of days ago’ of son’s meeting with Russian lawyer[15] Did Jared leak the Donald Trump Jr meeting emails?[16] The Inside Story of the Kushner-Bannon Civil War
-
What is the best Contract Lifecycle Management system (from your experience)?
Like others in this thread, I agree that it depends on the specific features your industry/company demands. Hopefully one of the following tools will suit your needs.We did a huge crowd-sourcing of the best sales tools out there in different categories. This list of contract lifecycle managementt tools might do some service here. These should help you get your email workflows to be more efficient and easier to track throughout campaigns.The whole list of all 157 tools in different categories is here —-> Sales Tools: The Complete List (2017 Update) | Sales HackerHere are the ones we highligh...
-
Is the CashBean app an instant personal loan a scam or legit?
It is not a scam, It is legit but Just because it says you will get 60K instantly..that’s not true.The most they will give you at the very start is somewhere around 1000–4000 only.I tried it, my credit score is 793 and NO MISSING PAYMENT / Default EVER! Salary is 79,000 and No current Loan.Still, I got only 3500rs Limit on the first time. Which I didn’t use because it was a JOKE! I believe that paying a combination of interest, processing fee and all are too much for such a small amount.I was referred by a Friend.That same friend who’s credit score is 714 and 55,000rs Salary got only 2500rs Limit of Loan on the first try!...So basically, you can use them as an INSTANT LOAN option for future urgent need but for that, you will also have to keep using it and HELP THEM. Read it again HELP THEM! EARN a lot of money in that Processing Fee and HIGH INTEREST before they offer you something as big as 60K!in conclusion: install it if you are desperate for that instant 1000–2000 cash loan and FINE with the Interest and processing fees.Please note ALL THE APP LOAN are doing the same thing, they will offer you BIG LOAN in their Online Advertisements and Text Msg but in reality, no matter how good your credit score is.. YOU WILL START WITH VERY LOW!only to help them Earn PROFIT first..before they actually allow your that so call HIGH CREDIT!Still better than using Credit Card though.
-
What is the best HR program for a startup?
Kruze Consulting has worked with over 1000+ startups and has helped set up numerous HR infrastructure systems. HR is a not a luxury, but an essential component of any startup’s foundation. It doesn't matter how awesome your product is; poor hiring, an unproductive culture, and stagnant employees can sink the company in a hot minute. Below we've provided a suggested list of software, processes, and procedures to help startups navigate the HR landscape. Caveat: if you can afford to put the later stage processes in place sooner rather than later, you should do it!The Essentials: 0 - 7 EmployeesPayroll & Benefits, Gusto: simply the best.HR Management Platform, Zenefits: Still our #1 recommendation for managing employee offer letters and PTO. Its seamless.Communication, Slack: essential for office and remote workers alike.Employee Recognition, Bonusly: improve collaboration by allowing your employees to reward each other (via Slack)Harassment Training, ThinkHR: yes, you need this right from the start.Background Checks, Chekr: don’t get surprised. Do you due diligence and check for red flags with Chekr.Feedback, Google Forms Anonymous Suggestion Box: sometimes employees dont feel comfortable asking certain questions or notifiyng management about situations. This gives them a voice.Basic HR Advisory, Kruze Consulting: everyone has questions about which health care plans to pick, what other startups are doing, and best practices around hiring and firing. Kruze has all the templates and can help.The Growth Phase: 8 - 40 EmployeesNew Employee Orientation, Lessonly: when new employees start at Kruze, their first learning stop is Lessonly. Its critical for new hire orientations, as it documents all of our internal procedures and allows for bespoke lesson plans and custom video uploads. But here’s the kicker: it has quizzes at the end of each module so that we can hold folks accountable to the curriculum.Continuing Education, LinkedIn Learning (fka Lynda): Seth Godin rocked my world in a seminar about how we have learning all wrong: homework should be done at school, lectures should be done at home and performed by THE world expert. Why or why would you have your best excel jockey in the company teach everyone else when you can have the best Excel Guru in the world teach your team on LinkedIn Learning?401k Plans, Guideline/Gusto and ForUsAll: most Seed Stage startups don’t offer 401Ks, but after a Series A many management teams will start considering it. By Series B, you should definitely have a 401k in place.Employee Handbooks, Gusto: Gusto’s amazing DIY handbook tool is great backbone, but you’ll need an advisor to refine company specific policies and procedures that aligns with your company’s core value system.Robust Health Benefits, Zenefits or Gusto: make no mistake, if you want to hire top talent you now need to offer top benefits. Now is the time to up your Silver and Gold packages to Platinum. It’s also time to consider an FSA or HSA. Some cities, like SF, require that you spend a certain minimum on each employee’s benefits and report on that compliance (known as the SF Health Care Security Ordinance).Tuition Assistance Programs, Tuition.io: companies like Tuition.io are revolutionizing the way employers can help free their teammates from the shackles of student loan debt, driving loyalty and retention in the process.Commuter Benefits, Gusto: if you have a 20+ employees and are based in SF, you are required to provide up to $260/mo in pre-tax commuter benefits. Other jurisdictions have similar requirements. But even if you’re not in SF, its a best practice to provide this benefit for your team. Kruze can help you set up commuter benefits and maintain compliance.Intermediate HR Advisory, Kruze Consulting: How much should I be paying my new VP of Engineering? How much stock should I grant, and what type of ESOP should I offer? Kruze has the answers.Project Based Grading Systems, Kruze Consulting: one of the biggest complaints that we’ve heard from employees is that they’re not getting enough regular feedback so that they can improve their performance and get ahead in their career. Kruze has template frameworks to help you create project based grading systems. Think “Hey Jane, this project that you completed was a B+ because you forgot to do XYZ. You’re so close, and I’m sure we can get you up to A+ work on the next project.” The results we’ve seen after implementing these controls were immediate: on the subsequent projects, employees knew exactly how to improve and they did. A big win for management and employees alike.Performance Reviews, Lattice: quarterly or biannual performance reviews are important to your employees growth and the well being of the company. Biweekly 1:1 meetings should also be implemented and documented. Lattice organizes the review process in an easy to use online interface and Kruze can help you build the appropriate questions that management team should be asking of itself and its employees.Recruiting Management, Greenhouse and Google Hire: these amazing pieces of software helps you manage the recruiting process and collaborate with your team. Some of the most frustrating parts of the recruiting process is organizing resumes, coordinating schedules, and quantifying the interview process all in a timely manner. Greenhouse and Google Hire handles all of this.Event Planning, Blue Barley: allowing your team to bond outside of work is important. But finding and booking creative events can be difficult. This is where Blue Barley comes in.Recruiters: your time is best spent doing what you do best. Yes, recruiters are expensive but they cut the search process dramatically. Kruze has an extensive network of recruiting professionals that we can introduce you to depending on the role that you are looking to fill, including companies like Triplebyte and Avra.Gifts, Bouqs and Minibar: if your teammate has done something awesome, really reward them with flowers from Bouqs or booze from Minibar.Say Something Positive: words can go a long way. Make sure that your managers are routinely saying positive things to their teammates. There are plenty of apps out there that can help randomly remind them.Swag: you haven’t really made it until you have your startup’s logo emblazoned on a Patagonia. Sports Basement has the best pricing and service. For other bougie swag, see Clove & Twine. Business cards are going the way of the dinosaur, but if you must, use Moo.The Enterprise: 40+ EmployeesPEO (aka Professional Employer Organization): PEOs are companies like Justworks, Trinet, and Sequoia. They are “all-in-one” payroll and benefits providers that are able to provide more favorable benefits plans because they have a much larger group policy. Don’t be fooled though, their Service Cost is 10x+ the price of Gusto, and most the time any cost savings you got on the health plans is more than washed out on their monthly Service Costs. At least until you have scale. Kruze recommends that you consider a PEO once you’ve signNowed 40+ employees OR if you have employees in 5+ states. Before then, cost outweighs benefit. Our top picks are Sequoia and Justworks.In-house HR professional: Kruze recommends considering hiring a full time HR professional once you’ve signNowed 40+ employees. But if you’re planning on growing quickly, you might want to consider hiring your full time HR professional sooner than thatContinuing Education Programs: your best and brightest employees will be eager to advance their careers and knowledge base, and one of the best ways to do that is through continuing education. Kruze has a library of Continuing Education options and plans based on industry specific talents. One of our top picks in Continuing Education is Harrison Metal General Management.Mentorship Programs: careers may start with technical proficiency, but they blossom once soft skills are applied. Your employees likely have many other goals beyond just developing trade knowledge, like networking, sales, and better communication skills. Sometimes folks dont even know what they’re missing, but mentors can help guide them. The BestSelf.co journal is a fantastic resource that helps both mentors and employees stay accountable on their personal KPIs.
-
How can I implement an online payment gateway in an Android app using CCAvenue?
>Integration with CCAvenue is possible using their Mobile Integration Kit. They provide sample code for iOS and Android which can be downloaded from here:https://mars.ccavenue.com/downlo...They describe two ways of integrating with their payment gateway, seamless and non-seamless. Either way requires you to redirect the user to a web page to complete the payment process or acquire authorisation from the users bank. Once done CCAvenue can redirect the user to whatever URL you prefer. This could be a website, merchant server API or a custom URI like myapp:// where you could handle the response locally.Seamless means you have the opportunity to present the payment options natively and collect all required fields first, then submit this to CCAvenue.Non-Seamless means you just pass the amount and currency to CCAvenue and the billing and payment details are collected from the redirected page.Either way will you require you to handle integration with CCAvenue with a separate WebView Activity to which CCAvenue provide sample code for.First of all, you need to set up a CCAvenue account. Go to the Sign Up page, choose the Startup Pro plan and fill out your details. On creating your account, you will recieve an e-mail on your entered e-mail address to verify your e-mail. Once you verify your e-mail, you will recieve an activation e-mail which will give you your CCAvenue Account Login ID and you will be required to set your password. Set your account password and make sure you read the e-mails that you receive thoroughly.Login to CCAvenue M.A.R.S Panel (Dashboard). In the Settings > API keys tab , you would get the Merchant ID , Access Code as well as the Working Key. The working key is also named as the encryption key in the dashboard provided to your from CCAvenue. Copy these keys to a safe place for later use.To secure the data transmitted from mobile while initiating the transaction, CCAvenue has implemented a time-based RSA key pair value which needs to be fetched uniquely for every transaction. These files should be uploaded on your web server.To download these files, Login to CCAvenue Dashboard. Now go to Resources > Mobile Integration Kit. Further click on RSA & Response Handling. Download the PHP files from here. You can also use the JSP and ASP .NET files but make sure your web server supports these functionalities before you use them. PHP is supported by every web server so I am using PHP.You will find 4 files on unzipping your PHP download. These are: cacert.pem, ccavResponseHandler.php, Crypto.php and GetRSA.php. You will find 4 files on unzipping your PHP download. These are: cacert.pem, ccavResponseHandler.php, Crypto.php and GetRSA.php. Now follow the following steps:(a) Upload these 4 files on your web server.(b) In the GetRSA.php file, put your access code in the 4th line like this: 'access_code'=>"XXXXXXXXXXXXXXXXXX",(c) In the 20th line, you need to put the path where you have uploaded your cacert.pem file. For example: curl_setopt($ch, CURLOPT_CAINFO, $_SERVER['DOCUMENT_ROOT'].'/RSA/cacert.pem');(d) In the ccavResponseHandler.php file, put your working key in the 6th line like this: $workingKey='105B05A21AD102EBA62C051720CC3FA2';That's all for the server part.(Source :: Internet)Thanks.
-
What is the National Security Strategy of India?
Recently I participated in the “Prime Minister’s Silver Cup Essay Writing Competition 2017” which is one of the most prestigious essay writing competitions, being conducted by the SVP National Police Academy, Hyderabad for all the police officers from all departments, of all ages and ranks, across the entire country.The winner of the competition gets a Cash Prize, a Silver Cup and will be felicitated at the IPS Officers’ Passing Out Ceremony which is held at their Graduation Day in Hyderabad.The topic of that competition for this year was “National Security Strategy - From Cold War to Code War”. I shall be writing the essay here which I had submitted to the competition. I would lose the intellectual property rights for this essay to the Academy if I win the competition. If not, I would retain the rights to publish this essay anywhere I like. Since the results would come later this year, so writing it here wont be any problem. :P (Will delete this post, if by mistake, I get a prize :P)Anyways, here is the essay. The answer to this question. The national security strategy for India.“National Security Strategy : From Cold War to Code War”“Conflicting ideals are a virtue; they keep us on our toes, in a constant vigil” – AnonymousEons ago, when the earth was still uninhabited by the intriguing Homo sapiens, there existed a distant relative species of the contemporary cow, called the aurochs. This ancestral relative of the modern cattle was a highly ferocious and territorial animal, much unlike the present docile cow. The aurochs used to rule the lands of mid-Europe for centuries, and domesticating it was an unthinkable thought. But, a few centuries after the arrival of the humans, the ferocity of the aurochs was extinguished, the once undomesticable animal was domesticated, and the private parts of the aurochs were even squeezed by humans to extract nutritious milk. The aurochs was exploited, both physically and mentally, and was slowly transformed into the modern day humble cow. The aurochs, as we know it, is extinct, and now can be found only in the fossilized bones which are preserved in the museums, built by humans. There was no security for the aurochs. There was no strategy for the aurochs to save itself from the wrath of the humans. This is what happens when one does not have a viable security strategy against the threats of nature – Massacre and Extinction.In the last one century, our planet earth has witnessed major in-fighting amongst one of its species, the humans. The human beings have been fighting amongst themselves for millennia, but the last one hundred years had outdone all that. With the Great War of 1914 – 1918, the entire world witnessed enormous destruction, and it was thought that such destruction can never happen again. Then came the next Great War, aptly called the World War II, from 1939 till 1945, which again witnessed unprecedented destruction and loss of life. The dropping of the two nuclear bombs showed the capacity of the human intellect to destroy; to demolish; to devastate.The wreckage created by these two Wars taught a very valuable lesson to the human beings – Do not fight each other. But, this lesson was too short-lived, and we saw the rise of two super-powers, with conflicting ideas, ideals and ideologies, two countries that were competitive enough to start a race. A race to spread their ideology; A race to gain maximum number of members for their bloc; a race to build sophisticated arms; a race to explore space; a technological race; an ideological race; a hegemonic race – A race which paved the path for impending global destruction.For over five decades, the United States of America (USA) led the capitalist ideology bloc against the communist countries group, which was led by the Union of Soviet Socialist Republic (USSR) (Soviet Union) for unopposed global leadership, at the cost of each other. Soon after the famous Cuban crisis of 1962, the rise in the race for accumulation of dangerous arms shocked the entire world, as it shocked these two countries as well. To slow down this race and to ensure a strong control of arms proliferation, the two superpowers started holding bilateral conferences called the SALTs – Strategic Arms Limitation Talks, which paved way to treaties called the STARTs – Strategic Arms Reduction Treaties. Due to this self-realization on their abilities to destroy the world, due to these plans to put aside their ego and come to an agreement, due to these security strategies to avert mutual destruction, the entire planet has been saved. Even though the USSR disintegrated due to its internal crumbling issues later and ensured USA wins the Cold War Race, but these talks and treaties had sound security strategy to avert a full-blown War between the two blocs. This shows the importance of bilateral talks, strategic plans and the importance of peace for our own survival.The same can be said about the history of the security issues of independent India as well. Gifted by a long coastline, a longer land border with a myriad of interesting countries with interesting bilateral relationships, a rising economy, an increasing hegemony in the global international affairs, a nation that is abundant with resources and thrives with a diverse chaotic population which is divided by religion, region, language, caste, class, gender, race and what not, it is a miracle indeed that India still is a functioning vibrant democracy and has not been internally disintegrated or externally destroyed yet.With internal problems ranging from intense home-grown armed naxalism, an ideological and violent Maoism, the divisional insurgent movements in the North-East, an increasing number of cyber threats, a rising crime rate, a constant fear of cross-border religious fundamentalist terrorism, India does face a continuous variety of constant issues, simultaneously, which can be witnessed nowhere else in the world. No other country has such diverse internal cleavages amongst its own populace, no other country faces so many varied security issues at the same time and no other country has survived and thrived in such immense chaos, as does India.The most intense struggle is against our neighbouring brother, Pakistan, with whom we have already indulged in three and a half wars. Tensions seem to be never-ending and any improvements in peace talks are marred with disappointing incidents like the Uri attack or the Pathankot attack, which we retaliate again through surgical strikes and by bringing up the Indus Water Treaty and Balochistan issues. Construction of the Kishenganga, Ratle and Baglihar dams on the cross-border rivers are becoming an issue as well. But, the recent victory of India in the International Court of Justice gives us a moral advantage in the international scenario. To also ensure that a minimum deterrence is established, India came up with the Cold Start doctrine, which aims to destroy all important strategic locations in Pakistan, if instances of unwanted cross-border terrorism occur. Not just cross-border terrorism, but also border demarcation issues through the Sir Creek estuary and the Thalweg doctrine are major impediments in the bilateral relationship with Pakistan. To further establish deterrence, India has the Nuclear Triad - Ability to fire nuclear weapons through land, water and air. And at the same time, to build better friendship, India also undertakes Confidence Building Measures (CBMs) and has the ‘No-First Use’ nuclear attack policy. To analyse all these trends the Central Government had set up a Committee under Madhukar Gupta to understand ways and means of border protection, especially along the Indo-Pakistan border.Whereas, with China it is a totally different issue. With the rise of the Chinese economy, China wants to portray its hegemony in the Asian affairs, at the cost of the rise of India. It wants to coerce India into signing the One Belt One Road (OBOR) initiative; it wants to weaken India by making her have a trade deficit by dumping lots of Chinese goods into the market; it wants to ensure that India loses all its friends by subtly influencing their neighbours. China has started subverting the entire Pahadi (Northern Mountainous) region of Nepal, and now it has set its eyes on subverting the Madheshi Terai (Southern Plains) region. China is coercing Nepal into making the Government teach Chinese language in the schools and colleges of Nepal. It has also set up branches of the China Study Centre, China Cultural Centre, Buddhist Study Centre and Confucius Centre throughout the cities of Nepal to proliferate and spread the Chinese culture in the daily affairs of Nepal. It is also known that China controls a few-Nepal based newspapers and they get anti-India articles published in these newspapers, which the local Nepali citizens read and unknowingly get influenced by the Chinese propaganda. This subtle subversion is slowly and mildly influencing the entire Nepalese population to become pro-China and anti-India. These kind of mind games need to be countered by similar mind-games from the Indian side as well.The issue with Bangladesh is more complicated, mainly due to the infiltration of unregulated refugees and migrants into the north-eastern states which is changing the racial dynamics of these states, especially Assam. A large migrant Bangladeshi population is creating a Law & Order issue in the Assamese region mainly due to the xenophobia amongst the local populace, and the illegal settlement and citizenship registration of these Bangladeshi immigrants. The Myanmar border is stained with the stronghold of various drug cartels, due to the presence of the famous Golden Triangle, the world’s drug manufacturing horde. This is combined with the internal insurgency issues of the North-Eastern states, the violent Naga ethnic problem and an absence of economic development due to inaccessibility of the seven sister states with mainland India.Afghanistan is a friendly state, but is suffering from its own crumbling internal problems. India has ensured to maintain a cordial relationship with the Government, so that the rise of the Taliban can be monitored. India has helped Afghanistan in constructing the parliament building, dams and other essential infrastructure. India has hosted the Heart of Asia Conference of the Istanbul Process many times to gather international support for the Afghans. Overall, there are no border skirmishes with Afghanistan as India is respected by the people of this country. The same applies to the relationship with Bhutan as well, where mutual respect and understanding is the prevalent predominant norm, as propounded by the I.K. Gujral’s Doctrine of India helping its friendly neighbouring countries unilaterally, without expecting much in return. For every other strained border, including that of Sri Lanka, there are the Armed Forces which take care of the safety and security of the country.The effectiveness of the Armed Forces keeps increasing as the country faces and overcomes many of the violent incidents, which occur on a daily basis, in some or the other part of the country. The Ministry of Defence is in a constant vigil with its constituents, the Army, the Navy, the Air Force and the Indian Coast Guard ever committed to their duties. The Ministry of Home Affairs is the nodal controlling Ministry to a plethora of organizations including the Intelligence Bureau (IB) which takes care of internal intelligence collection and analyses, Border Security Force (BSF) at the Indo-Pakistan and Indo-Bangladesh border, Central Reserve Police Force (CRPF) to ensure anti-naxal operations, Assam Rifles (AR) at the Indo-Myanmar border, Central Industrial Security Force (CISF) to give security protection to vital installations and strategic industries, National Security Guard (NSG) to combat against terrorist activities, Sashastra Seema Bal (SSB) for the Indo-Nepal open border, Indo-Tibetan Border Police (ITBP) which takes care of the Indo-Chinese border, the Special Protection Group (SPG) gives protection to VIPs such as the Prime Minister, Central Bureau of Investigation (CBI) for investigating corruption charges and complicated cases of national importance, National Investigation Agency (NIA) which focuses on investigating terrorism related incidents and the Indian Police Service (IPS) personnel who head various State Police services. Research and Analysis Wing (R&AW), takes care of the external foreign intelligence collection and analyses, reports directly to the Prime Minister’s Office. Each of this organization has a specific task cut-out, which increases its specialization and specificity to handle these security issues with a focussed agenda. On top of these tasks, the Indian Government sometimes takes part in extraordinary exercises such as Operation Sankat Mochan where Indians were airlifted from South Sudan and Operation Raahat where Indians who were stuck in Yemen during their civil war were taken to safety. These new and upcoming challenges need a lot of presence of mind, training and an upgradation in the equipment used by the Armed Forces.Modernization of the Armed Forces has become a top priority for the Central Government after the establishment of the Vijay Kelkar Committee which focussed on the Defence Production and Acquisition of arms & ammunition from various foreign defence industries. As an aftermath to this committee, the Government also set up the Dhirendra Singh Committee for Defence Modernization which included recommendations like transfer of technology to ensure indigenous development and production of defence arms locally. This can be achieved with the help of the many Ordnance Factories established in the country under the overall technical supervision of the Defence Research and Development Organization (DRDO).Based on these recommendations, the Indian Army has recently announced the formation and formal establishment of the Army Design Bureau. It is aimed to act as an interface of the Indian Army that will provide high-tech defence products with the help of the collaboration between academics, various research organisations and the industry. This indigenous method will provide a better understanding of the Army’s requirements and would indigenise procurements and reduce the dependence on the massive imports. This will add an impetus to the ‘Make in India’ initiative of the Central Government.Even the Navy is getting an upgrade with the approval of “Project 75”, where a series of advanced Scorpene submarines are being built, along with the induction of new naval attack ships INS Khanderi, INS Kalvari and others to the Indian Navy. In the same way, French Rafale fighter jets are being procured and are being inducted to the Indian Air Force. These will be on the lines of the Russian Sukhoi, which has helped the Air Force in innumerable ways. The Committee set up under the Chairmanship of Naresh Chandra gave its recommendations on the ways and means to ensure effective Defence Management which called for a better collaboration between the various Armed Forces.This enhanced collaboration can already been seen in the annual inter-service military exercise called the Theatre Readiness Operational Exercise (TROPEX) involving the Army, the Navy, the Air Force and the Coast Guard which is designed to test the inter-operability and combat readiness of these Forces. Not just the TROPEX, but inter-national and inter-country military exercises are being organized annually to ensure inter-operability at a global scale, for example, the annual Malabar Trilateral Exercise between the naval forces of India, Japan and the United States. Even India and China have their own annual joint military exercise called Hand-in-Hand. This ensures an increased cooperation and mutual understanding of various countries, which may subtly increase friendship and strengthen the relationship.Such global initiatives are very common, especially in a post-Cold War era, most of the initiatives try to increase the collaboration between various countries, and many other initiatives try to control and restrict the proliferation of weapons. The Australia Group is one such initiative whose sole purpose is to reduce the usage of Chemical Weapons. The countries of this Group try to stop the trade in Chemical weapons and are pro-active in destroying the storage of chemical weapons in various countries. The Organization for the Prohibition of Chemical Weapons (OPCW), which won the 2013 Nobel Peace Prize works to prohibit the proliferation of chemical weapons and aims to destroy any stack held by any country.In the same way, another grouping by the name of Wassenar Agreement was created to monitor the trade and transport in conventional arms and weapons. The Hague Code of Conduct and the Missile Technology Control Regime (MTCR) works to control and monitor the production and trade of ballistic missiles made by the signatory countries. In a similar way, the Nuclear Suppliers Group (NSG) restricts the trade of nuclear fissile material in the global scenario. India’s security strategy presently is to become a part of these four Agreements to ensure that it equips itself with the latest technology to ward away and deter any forms of external and internal aggression. The joining of these four groups also would enhance India’s global hegemony which would further enable her to become a permanent member of the United Nations Security Council later.India has changed its international strategy considerably, from those days of neutrality and non-alignment when it started the Non-Aligned Movement at the Bandung Conference in 1955, to the current bilateral and multilateral agreements being made with all the strategically important countries. The Prime Minister also is exhibiting diminished interest in the outdated NAM principles, as he did not attend the summit this year. We can also see alignment with countries like USA, with the signing of the LEMOA agreement and an increasing procurement of arms from USA instead of Russia. USA also recently announced India as one of its Major Defence Partners for upgrading the bilateral relationship to the next level. India has also started signing important Agreements with conflicting countries like Israel, Saudi Arabia and Iran in these security matters. The careful balancing of the Indian foreign policy juggling between these three triangularly ideologically opposite countries is a modern day wonder indeed.If things seemed complicated in the international scenario, they are no less in the internal scenario as well. The State Police which takes care of the Law & Order situation, reduction of crime rate, management of prisons and other policing is facing a tough situation indeed. With the rising drug related problems, rapes, murders, thefts, corruption, bribery etc., the local citizenry is facing a lot of issues in their day-to-day problems which needs to be solved by their locally available policemen. A Committee was set up under Justice Malimath to suggest recommendations in revamping the Criminal Justice system. It reiterated the need for D. K. Basu Guidelines that are to be followed by the policemen to adhere to the Procedure of Arrest. The revamping of the existing police machinery to suit the needs of the current times is a must. With an enhanced citizen – police interactional interface, what needs is an upgradation in the maintenance of police records. This can be achieved through digitization of court records, police official documents and connecting the internal systems of all the police stations and courts with each other. An online interface and an ability to lodge FIRs online should also be encouraged. Utilizing the internet for establishing e-Governance will help the common man in approaching the police easier. The increase in the usage of internet through smartphones and laptops by today’s India is a testimony for this fact indeed.The increase in the interconnectivity of the entire world due to the explosive proliferation and penetration of the internet in the last two decades has brought a plethora of new security threats that need to be understood and neutralized soon. The Government had set up a Committee under A P Shah to understand the threats of the cyber world and ways to enhance the country’s cyber security. It also set up the Gulshan Rai Committee for Data Privacy which recommended ways to ensure that the data we generate and store is secure and safe. The inventions of new virtual digital crypto-currencies like the Bitcoin have also brought up new challenges in the cyber and financial sectors. The Bitcoins, which are unregulated, have the ability to disrupt the cyber space and disintegrate the financial world.The setting up of the Indian Computer Emergency Response Team (CERT-In) has been an excellent initiative to tackle the futuristic problems of the contemporary times. Especially at a time when our neighbouring countries are building armies of cyber warfare forces whose sole purpose is to attack the cyber networks of the vital installations of our country. With the help of CERT-In, the Central Government has also brought out initiatives like Cyber Swachata Kendra to help secure the cyberspace which is still at an early nascent stage. Now, the need of the time for the Indian Government is to build an army of IT specialists and cyber analysts who can both defend the country’s cyber infrastructure and if the need be, attack the enemy country’s online vital installations.The country anyways exports coding experts to the developed countries in the pretext of “brain drain”, whereas the Indian Government can hire the same computer specialists for managing her own cyber security. It is said that the Cold War was actually a war between the two blocs’ mathematicians, statisticians and coders whose work was to solve and break codes of the enemy country’s strategies and plans. From that Cold War, to the current Code War, the importance of this intelligentsia cannot be overemphasised. They have been the unsung heroes of those times, and they still will be the true heroes in these times.Along with conventional armies and conventional security strategies, India needs to learn to use unconventional means to win over the unconventional threats that she faces in the contemporary times in order to survive. Our country is a curious case where it has been successful in attracting all sorts of complications including terrorism, insurgency, Maoism, underworld gang wars, smuggling, theft, rapes, crime, border infiltration and every kind of possible issue that can be thought of. Our country has also created a viable organizational capacity to control each one of these intimidating activities.For over seven decades since Independence, the young country has gained experience in tackling each threat with its own focussed strategy, with its own viable plan and with its own appropriate ideation. Learning from the historic tale of the aurochs, in the current cluttered international context, and the more chaotic internal context, India has learnt to take good care of herself. Much unlike the fabled extinct aurochs, to ensure her own survival, India has constantly strived to have a viable National Security Strategy, right from those days of the Cold War, to these times of the Code War.
-
What does 'We the People' mean in the Constitution?
Q: What does ‘We the People’ mean in the Constitution?Full Preamble of the United States Constitution:We the People of the United States, in Order to form a more perfect Union, establish Justice, insure domestic tranquility, provide for the common defence, promote the general Welfare, and secure the Blessings of Liberty to ourselves and our Posterity, do ordain and establish this Constitution for the United States of America.Legally:It means The People are the signers of the Constitution.Literally:It is a more condensed form of writing this:We the People of the United States, in Order to fo...
-
How the changes in US immigration law affect the incoming International students?
The fact that Congress is not moving forward to raise the H-1B cap which is presently set at 85,000 while the number of H-1B petitions submitted increased from 172,000 in 2014 to 233,000 in 2015 makes it increasingly unlikely that International Students can secure H-1B status.However, for students with OPT who are in STEM occupations, if their employers have signed up for E-Verify, they can secure 17-month extensions of their OPT. This allow employers to obtain permanent residents for many of these students, bypassing the H-1B process.Please see
-
Is American history boring?
WARNING: This is a really long piece and I don’t blame you if you don’t want to read all of this. However, I would urge you to do so - I might tell you something you don’t know. However, for those who are in a rush, a tl;dr is upcoming. Also, some of the following may be considered insulting to Americans - to which I say, grow a pair and move on, but, for those who are incredibly sensitive, realise that this text is meant to inform, and not to offend.TL;DR: So, compared to other histories American history is goddamn boring, but mainly because the USA is quite a young country, only having been around for a couple of hundred years, whereas countries like Greece, Italy, Egypt, etc… have been around for thousands of years, and have a much richer history.Ordinarily, I would say that history is not a boring subject. It’s an exciting one, a thrilling tale of the paths our ancestors have taken, to get us to where we are now.However, in this case, I’m going to say yes, American history - by which I assume you mean the history of the United States - is incredibly boring.Let’s take a look at some facts, and compare it to several other histories.I’m gonna’ pick three unique histories and judge them against American history. My judged categories will be genesis - the beginning of - an outstanding event - a really cool event that took place during history - and a leader of each history. The leaders will be analysed and judged against the American leader as well.Let’s get to it.So, I’m gonna’ go with Roman history, Greek history, and - even though this’ll piss off pretty much every American reading this - British history. The reason I pick these is that they are quite well known as a general subject, but they are easy to compare to one another.The United States of America came around as a result of the American Revolution of 1783, although I do believe it started sometime in 1765. However, the only reason that the British lost - and I’ll even get pedantic about that - was because the Americans happened to have the French, the Spanish and the Dutch on their side. And, as it happens, these three were global powerhouses at the time. It seems so useful that the Americans seem to have amnesia whenever these three show up.Not to mention that the Americans didn’t even win, because America didn’t exist until after the Revolution. So the British beat the British. Well done, we beat ourselves - now, disloyal colonialists, please proceed to continue being the British rejects that you always will be.Now, I’m gonna’ state now that this birth in itself isn’t boring - a force of rebels assisted by three of the most powerful countries in the world, defeating another one of the most powerful countries in the world? Sounds like the plot for a movie - and like I said, on it’s own, it isn’t boring.But, compared to other histories, it is rather boring.Take Rome for example. I’m not even gonna’ cover the ‘first’ birth of Rome, since it is kinda shrouded in myths and legends. Instead, I’ll cover the birth of the Roman Empire, since this is also what I know the most about when it comes to Rome.For those who don’t know, this is a bust of Augustus Caesar - some of you may know him as Octavian. Regardless, he is responsible for the rise of the Roman Empire, out of the ashes of his father’s republic.There was a huge civil war that spanned across Southern Europe, Africa, and parts of Asia, between Marc Antony, Lepidus, and Octavian. Eventually, Lepidus was exiled, and Marc Antony poisoned himself alongside Cleopatra VII, leaving Octavian as the sole ruler of all of Rome’s territories.He restyled himself Augustus Caesar.If that isn’t cool, than I don’t know what is.What about Greece? They came out of the ashes of the Mycenaean civilisation, after losing their language. Instead of giving up, they stole the Phoenician language, and modified it to create their own language, becoming the seminal civilisation.Much, much more interesting than American history. Britain was occupied by the Romans, so I’m not gonna’ go into that one here.Now for the interesting event.My events to analyse are: the assassination of JFK; the Battle of Thermopylae, the Second Punic War, and the Battle of Britain.First of all, the assassination of JFK is not boring. It’s a brilliant mystery. I’ll give you that. But come on, it’s not very original - leaders have been assassinated throughout history, and certainly in more interesting ways.Now for the Battle of Thermopylae - this was an interesting event because it was a land stand against a powerful enemy. Even though the Greeks didn’t win, they managed to bring all of the warring city-states together and defend against a huge Persian army, led by none other than Leonidas.For the Romans, I chose the Second Punic War, because of the characters present during said war - for one, Scipio Africanus, who had several legendary exchanges with the Carthaginian general Hannibal Barca, who led his elephants over the Alps and into Italy.And for the British - the Battle of Britain, a pivotal moment during the Second World War, and perhaps the reason why Hitler lost the war on the Western Front. If it wasn’t for the Battle of Britain, I wouldn’t be sat here writing this very post in English.Now for the finale - historical figures. Up for analysis are:Theodore RooseveltJulius CaesarAlexander the GreatSir Winston ChurchillFirst of all, let’s start with Roosevelt. He was awesome - he took a goddamn bullet to the chest and then continued by making an hour long speech whilst the bullet sat mere inches away from his heart.Julius Caesar rebuilt Rome and was stabbed to death by his allies. Alexander the Great built an empire without losing a war, but the empire collapsed after his death, being shared between the Diadochi.Winston Churchill led the UK during the darkest days - WWII. For all his flaws, he was one hell of a man.So, after all that, I’m still gonna’ say that American history is boring, because everything’s been done before. It just isn’t original. xD
Trusted esignature solution— what our customers are saying
Get legally-binding signatures now!
Related searches to Submit eSign Presentation Secure
Frequently asked questions
How do i add an electronic signature to a word document?
How to annotate and sign pdf?
Get more for Submit eSign Presentation Secure
- How Can I Electronic signature Colorado Plumbing PPT
- How To Electronic signature Colorado Plumbing PPT
- How Can I Electronic signature Colorado Plumbing PPT
- How Do I Electronic signature Colorado Plumbing PPT
- Help Me With Electronic signature Colorado Plumbing PPT
- Can I Electronic signature Colorado Plumbing PPT
- How Can I Electronic signature Colorado Plumbing PPT
- Can I Electronic signature Colorado Plumbing PPT
Find out other Submit eSign Presentation Secure
- Power attorney children form
- Newly divorced individuals package wisconsin form
- Wi statutory form
- Contractors forms package wisconsin
- Power of attorney for sale of motor vehicle wisconsin form
- Wi statutory 497431228 form
- Wedding planning or consultant package wisconsin form
- Hunting forms package wisconsin
- Identity theft recovery package wisconsin form
- Statutory power of attorney for health care wisconsin form
- Revocation of statutory power of attorney for health care wisconsin form
- Aging parent package wisconsin form
- Sale of a business package wisconsin form
- Legal documents for the guardian of a minor package wisconsin form
- New state resident 497431237 form
- Commercial property sales package wisconsin form
- General partnership package wisconsin form
- Wisconsin declaration form
- Contract for deed package wisconsin form
- Wi will form