E-mail eSignature Presentation Now
Make the most out of your eSignature workflows with airSlate SignNow
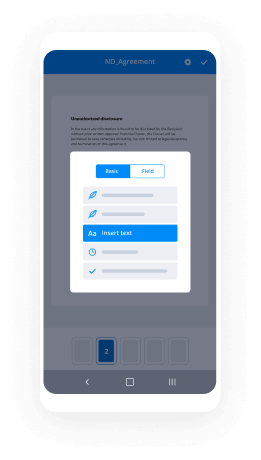
Extensive suite of eSignature tools
Robust integration and API capabilities
Advanced security and compliance
Various collaboration tools
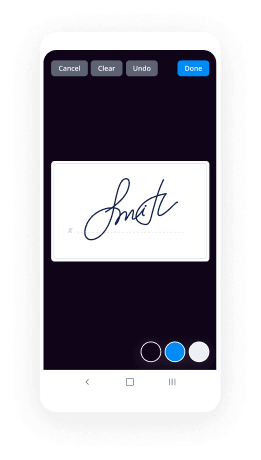
Enjoyable and stress-free signing experience
Extensive support
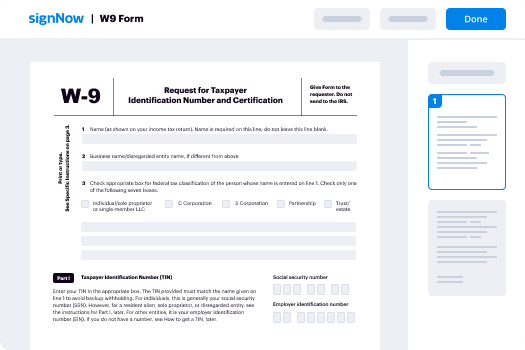
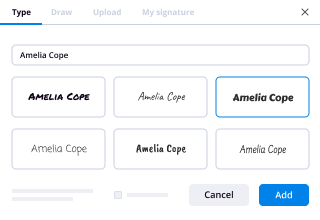
How To Use eSignature in ERP
Keep your eSignature workflows on track
Our user reviews speak for themselves






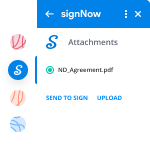
E-mail eSignature Presentation Now. Check out one of the most user-helpful experience with airSlate SignNow. Handle your entire document handling and sharing method electronically. Change from portable, document-dependent and erroneous workflows to computerized, electronic and flawless. It is possible to generate, produce and sign any paperwork on any device anywhere. Ensure that your important enterprise instances don't slide overboard.
Learn how to E-mail eSignature Presentation Now. Keep to the straightforward guide to get started:
- Design your airSlate SignNow profile in clicks or log on with the Facebook or Google accounts.
- Take pleasure in the 30-working day trial offer or pick a pricing strategy that's ideal for you.
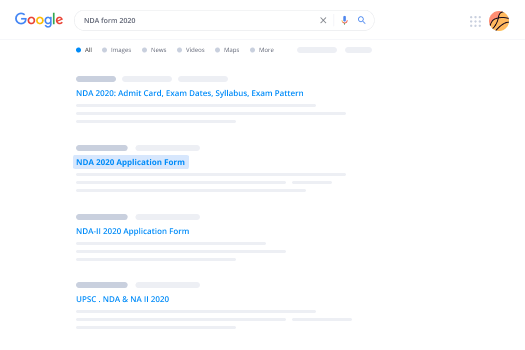
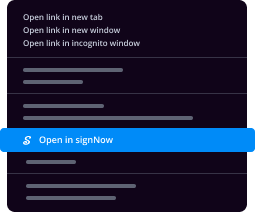
- Discover any authorized format, develop online fillable kinds and share them tightly.
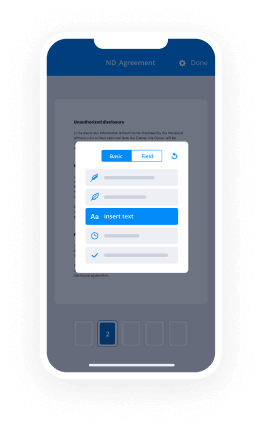
- Use innovative capabilities to E-mail eSignature Presentation Now.
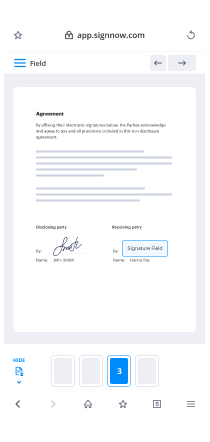
- Signal, customize putting your signature on get and collect in-man or woman signatures 10 times quicker.
- Set intelligent alerts and acquire notices at each and every step.
Shifting your jobs into airSlate SignNow is uncomplicated. What comes after is a simple approach to E-mail eSignature Presentation Now, along with tips and also hardwearing . colleagues and lovers for better alliance. Encourage your staff with the greatest resources to remain along with enterprise functions. Boost efficiency and scale your business more quickly.
How it works
Rate your experience
-
Best ROI. Our customers achieve an average 7x ROI within the first six months.
-
Scales with your use cases. From SMBs to mid-market, airSlate SignNow delivers results for businesses of all sizes.
-
Intuitive UI and API. Sign and send documents from your apps in minutes.
A smarter way to work: —how to industry sign banking integrate
FAQs
-
Is it possible for governments to eavesdrop a SSL communication? Why or why not?
Generally speaking, it depends on the government. But if we're talking about a well-funded state intelligence service, the answer is "probably, if they really want to."The easiest way for an intelligence service to do this is probably not by eavesdropping passively and then using supercomputers (or special circuits) to crack your encryption. Most experts believe that it's easier to perform a "man-in-the-middle" attack.Let's say you're traveling inside a police state and you want to connect to gmail.com so you can send your Gmail password and read your e-mail. How do you know you're really talking to gmail.com and not the evil government? Because the Web site presents a cryptographic certificate identifying itself as Google. (If you did send your password to the evil government, it would be game over. Ditto if they could read your email flying back.)But how do you know this certificate is legitimate? Because it bears the cryptographic imprimatur of a certificate authority (a company like VersignNow or their hundreds of competitors). How do you know the certificate authority is legitimate? Because its cryptographic imprimatur is stored in your Web browser (e.g., Internet Explorer) or operating system, and your Web browser trusts any of these hundreds of entities to signNow that Web sites are who they say they are.The problem is that your Web browser trusts hundreds of these certificate authorities, many resident in all kinds of nasty countries. It's like walking into a store to buy a diamond ring, and the store presents you with a signature from an "independent assayer" guaranteeing the purity and weight of the diamond. If you trust any of thousands of strangers to provide this certification, you can bet that the store could probably find somebody crooked to signNow whatever it wants.Now imagine the store is actually a well-funded nation-state and at least one of the hundreds of "independent assayers" is subject to its laws and not-so-nice tools of persuasion.Similarly, you should assume that several world governments can find at least one crooked certificate authority to signNow that they are gmail.com. You'll think you're talking to Google, but really you end up connecting to the government, which then impersonates you to talk to the real Gmail (and reads your e-mail before sending it back to you).One partial solution to this kind of problem (at least for e-mail) is to exchange cryptographic information DIRECTLY with the person you are corresponding when meeting up in real life, and then use that to encrypt and sign your e-mail, using a program like PGP or GPG. It is also possible to exchange this information through a third party who knows both of you personally, or through multiple third parties; this kind of scheme is known as a "Web of Trust." It has considerable limitations as well, but does have some advantages over the hierarchical X.509 public-key infrastructure that we use for TLS.
-
What digital tool, as a real estate agent, do you most use?
As an agent, we have access to the MLS, which the public only has limited access to. In my area the public can see exactly what Zillow can which is active listings. Our board does not disclose the sales price of closed prices, which makes services like Zillow pretty much worthless in my area. (Zillow may be useful in some areas, perhaps many, just not where I work).That said, my favorite and most useful tool, which is also available to the public, is the GIS (Government Information Service). Type in to Google: (Your county)(Your state) GIS [ie: Marion County Indiana GIS ] . While it isn’t available in every county of the country, you will find it in most major areas. It will give you access to the tax assessor records and often times the sales history of the property. The tax records will give you the details of site size, improvements, assessed values and depending on the county may or may not give you the annual taxes.Since real estate agents in some areas count the basement area when they list the size of the property, the GIS will allow me to figure out what is really there if I’m new to the area. For what I am looking for, there is a signNow difference between a stated 3,600 square foot house by the agent and 1,800 square foot above ground over a 1,800 square foot basement. - Lenders only count the above ground square footage as living area when making a loan.Hope this helps.
-
What is the best real estate technology?
A survey conducted by Coldwell Banker and CNET found that eighty-one percent of prospective home buyers were drawn to homes equipped with the latest in-home technology. Among those, thirty-five percent of people who preferred what is known as smart homes over traditional residences believed that such features solidified the property as “move-in ready.”Technology is also changing the field of home selling. Here are five ways that apps and other online features are making the life of a real estate agent easier.1. Broadcasting with Periscope and TwitterWhat better way to send out a massive blast than on Twitter? The social media site lets you keep it short but sweet as you tell followers that the home of their dreams has an upcoming open house session. You can also post pictures on Twitter that give potential buyers a better perspective of what they will see during their in-person tour of the property. Take the virtual showing a step further by using Periscope to share live footage of yourself walking through the house online. In past times, a substantial amount of money was necessary to promote property by way of commercials. Twitter and Periscope bring the perk to you for free so long as you have a smartphone or tablet when going live and taking pictures.2. Tracking with Glympse and WazeRunning twenty minutes behind used to be a deal breaker pre-Digital era. Not only did you inconvenience the client but you also provided a guess that was often inaccurate and led to more time wasted at the property. Traffic apps in the twenty-first century have made such estimating unnecessary.Waze is one app that provides navigation tips based on real-time traffic information. You can better coordinate appointments so that clients are not left waiting for several minutes and provide clearer updates when you are running late. Glympse also tracks traffic in real-time but takes things a step further by offering a link by which clients can track your whereabouts. Text or email the URL to prospective buyers and let them follow along as you make your way to the location.3. Meet Online with Reflector 2 and Join.meReal estate agents should consider investing in Reflector 2 instead of bringing their USB stick along to nail that next listing presentation. The app serves as a sort of projector by allowing you to cast all activity on your smartphone and tablet on a larger screen. The Reflector 2 works with nearly any device and does not require additional purchase outside of the app itself.Free Screen Sharing, Online Meetings & Web Conferencing is another app that has made buying a selling a home more convenient. Agents can hold brief meetings with clients without requiring them to come into the office. Sharing your computer screen is the best way to convey pertinent information to new homeowners. The recording and playback feature is particularly useful when you need to recall a client’s home preferences. They will be impressed with your attention to detail in finding a house with a built-in barbecue pit. You will know that such meticulousness is because of Free Screen Sharing, Online Meetings & Web Conferencing.4. Add Transparency and Rapidity with an Automated Mortgage Loan ProcessThe traditional method of the home loan process involved hours spent trying to secure financing. Leaving one paycheck stub or bank statement at home often meant holding off on the process until the client was able to furnish proof of such documentation. There was no transparency in the process, which meant that customers were entirely reliant on the expertise of the real estate agent.Technological advances have revolutionized the mortgage loan process. Automated processing now establishes criteria by which applicants are judged that makes applying simpler. Some financial institutions can pre-approve hopefuls in ten minutes. Individuals who go through the entire process may see their loans finalized in ten days instead of the average four-week period. Digital tools provide real-time updates so that even those who are not approved can move on to the next bank quickly instead of waiting for a rejection letter to arrive by way of snail mail.5. Agree from Home with E-signaturesIn past times, the thrill of closing quickly became inconvenient for buyers upon hearing that all approved owners would need to stop by the real estate agent’s office to sign final documents. Some individuals were forced to take a sick day from work just to make their mark on the paper. Such heartache is why the masses are thrilled to learn that e-signatures have the same weight as traditional marks on legal documents. A real estate agent can email paperwork that his clients can sign at their leisure and return electronically. It is even possible to solidify documents on a smartphone in some instances, which makes the home loan process that much more convenient.
-
Is the Donald Trump campaign sending unsolicited e-mail (SPAM)?
This story is developing quickly, and it looks like my 6/23 story on Daily Kos may have been the first to raise the allegation and evidence that Trump was sending SPAM (unsolicited e-mail, including to UK MPs).What is now known:1) Reports suggest that every MP in Iceland, as well as MPs in the UK, Denmark, Canada, and Australia received unsolicited e-mails from the Trump campaign. An unconfirmed report from an Australian MP on Twitter stated that ALL Australian MPs got the SPAM.2) UK MPs discussed the “intemperate SPAM” on the floor of the House of Commons, demanding that the unstoppable e-mails be blocked.3) Tons of people have complained about the Trump SPAM on Twitter (both receiving e-mails that they never signed up for and reports that unsubscribe requests have not been honored).4) Alexa stats from after the “first fundraising e-mail” and Return Path stats are consistent with an unsolicited e-mail campaign (high unsubscribe rate and lots of SPAM reports).5) Yahoo reported on campaign finance disclosures that suggest the Trump campaign is buying/renting e-mail lists of people that did not explicitly opt-in to Trump e-mails.6) Politico’s Ken Vogel confirmed via Twitter that “Trump campaign renting some scammy lists for fundraising emails: National Tea Party Alert, Liberty News Network, Endeavor Media Group, etc.”7) The Trump campaign was sued by two people, back in April, for sending unsolicited text message (SMS) SPAM.8) Some reports have questioned the authenticity of the foreign solicitation e-mails. Spoofing, etc. is a possibility; I certainly cannot speak for the foreign messages without seeing the headers. However, I, personally, received an unsolicited message from “Team Trump” that appears, superficially, to be linked to the RNC and an e-mail service provider. Other tweets link the mailings (not all unsolicited) to three additional e-mail service providers. The ESPs that appear to be involved are: Adestra-com, Geniusmailer-com, BlueHornet-com, and PsycloneContacts-net.9) The Associated Press is reporting that two “watchdog” groups have filed FEC complaints against the Trump campaign for soliciting foreign funds.10) Tweets have been posted linking some of the e-mail addresses sent to (one-time e-mails) or sender information to lists maintained by other GOP politicians, including: Rand Paul, Chris Christie, Ben Carson, Newt Gingrich, and Rick Santorum. Their involvement has not been independently confirmed nor have the tweets been verified.11) Donald Trump’s former campaign manager (and paid CNN pundit) Corey Lewandowski appears to have lied on air on CNN when asked about the e-mails to foreign MPs. He implied the e-mails were only sent to people who opted in to mailings and that people could opt-out. Both claims appear to be false.12) Josh Marshall at Talking Point Memo is reporting that some of the foreign e-mails seem to be coming from the Trump campaign while others seem to be coming from a pro-Trump Super PAC. He suggests it might be evidence of illegal coordination.13) Reports of Trump SPAM were still being posted to Twitter as of 7/3/2016.Experts Weigh InKen Magill of The Magill Report and Laura Atkins from e-mail delivery consultancy “Word to the Wise” have weighed in via blogs. Magill wrote that the simplest explanation is that Trump's list is not permission based while Atkins says "it certainly doesn't seem like it was even political style opt-in."Speculation1) From the number of users who claim to have been unable to unsubscribe, I believe that the campaign is not maintaining a global e-mail suppression list. As a result, unsubscribing from one send may not unsubscribe the user from other sends. It is also likely that sends are happening through multiple e-mail service providers or third-party senders and that suppression lists are not being shared between them.2) From the number of users complaining about receiving an excessive number of e-mails, it does not appear that the campaign was/is globally frequency capping the messages that are sent across the multiple lists and e-mail services providers.Full list of evidence and sources, with greater detail, in chronological order:I recently wrote a two-part article on Trump SPAM (the first article pre-dates the conservative reports), and posted them to the Daily Kos ( Did Donald Trump Raise $2 million from SPAM? , Trump Campaign SPAM Complaints Continue to Proliferate on Twitter ). Here are the facts:There are a lot of users taking to Twitter to complain about receiving Trump campaign e-mails without ever having signed up for his list.Shortly after his “first fundraising e-mail”, Alexa reported that ~20% of visits to the Trump2016 fundraising website were to the “unsubscribe” subdomain.Even with recent publicity, including allegations of a “tremendously high” SPAM complaint rate ( Trump Camp Still Not Asking for Donations in Emails ), there continue to be new reports of Trump campaign SPAM on Twitter.I signNowed out to e-mail delivery specialists Return Path on Twitter for a comment. Their reply (https://twitter.com/returnpath/s... ): “Based on the data, we surmise that Trump is likely buying lists, and he has a high spam complaint rate”.I think a fair question to ask would be whether the Trump campaign is knowingly sending SPAM. However, the data supports the SPAM allegations being leveled at the 2016 Donald Trump presidential campaign.UPDATE 6/26/2016 5:52PM ET: The Donald Trump campaign appears to have just sent another fundraising e-mail and prompted still more SPAM complaints on Twitter ( Another Fundraising E-mail and More Donald Trump Campaign SPAM Complaints on Twitter ). The number of complaints associated with this blast appear to be less than the campaign previously experienced. Maybe the campaign is trying to clean up its list (or maybe more of its messages are getting automatically filtered).UPDATE 6/26/2016 10:13PM ET: A lot more complaints have come in about the latest e-mail since my last update, so it looks like there are still a large volume of complaints for each message.UPDATE 6/27/2016: Finally, some media coverage reflecting what I have been saying for DAYS:Why Is Team Trump Asking Liberal Scottish Politicians for Donations?AP: "Trump may be buying email lists of people who don't want to hear from him” ( Trump emails: Can you spare $10 to help elect a billionaire? )UPDATE 6/27/2016: Yahoo just ran a detailed article on Donald Trump’s SPAM problem ( Donald Trump has a spam email problem ). Among the stats:Trump recipients marked 3.1% of those emails as spam; only .41% of Sanders messages and .02% of Clinton’s met the same fate. Three weeks earlier, Trump’s would-be readers were even less forgiving, marking 9.34% of his messages as spam.It also credits Trump with having a higher open rate than Clinton or Sanders, but I suspect some of those incremental “Opens” actually are from a larger number of people trying to unsubscribe.As I previously reported, the Alexa stats from shortly after the “first fundraising e-mail” showed ~20% of visits to an “unsubscribe” subdomain. If people open the message looking for an unsubscribe link, that could result in higher engagement/open rates.9.34% of messages marked as SPAM was INSANE! Even later, it was 3.1% for Trump as SPAM vs. 0.02% for Clinton while Clinton has a larger list.UPDATE 6/28/2016 8:22AM ET: According to the BBC (Brexit fallout, Labour turmoil and Cameron in Brussels - BBC News):Conservative MP Sir Roger Gale calls for Donald Trump campaign emails to be blocked on the House of Commons email system.Sir Roger raises a point of order to complain that many MPs have been "bombarded with emails from Team Trump on the behalf of someone called Donald Trump".While he is in "all in favour of free speech" he does not wish to be "subject to intemperate spam", adding that "efforts to have these deleted have failed".Speaker John Bercow replies that while "this is not a matter for the chair" he agrees it is "not acceptable to be bombarded with emails of which the content is offensive".Mr Bercow says he will contact the Parliamentary digital services to see if the messages can be blocked.UPDATE 6/28/2016 2:14PM ET: The news finally seems to be getting out:MPs 'bombarded' by spam emails from Donald TrumpUK Pols To Trump: Stop Wasting Our Time With Your Crappy Fundraising Emails!The last article states that a complaint has been filed with the FEC. None of the articles have mentioned that the SPAM has traveled beyond the UK to Australia. Two of the tweets I cited in one of my earlier articles were from Australian MPs who complained about receiving the solicitations.None of the articles have cited the Twitter reaction or suspicious Alexa stats cited in my earlier reports. Also, none have credited my earlier reports (including my article from 6/23 reflecting that “two British MPs” complained on Twitter about the SPAM).UPDATE 6/28/2016 7:34PM ET: Evidently Donald Trump sent SPAM to ALL Icelandic MPs as well ( Donald Trump Asking Icelandic MPs For Donations - The Reykjavik Grapevine ):Numerous members of the Icelandic parliament are both bemused and confused by an email, apparently received by all of then, asking for donations to the presidential campaign of Donald Trump.UPDATE 6/28/2016 9:16PM ET: Based on the campaign finance disclosures cited in the Yahoo report, Tweets from users who claim that one-time e-mails had fallen prey to the Trump SPAM campaign, and a conversation that I had with somebody who might be in a position to know, I strongly believe that Trump and/or the RNC is buying/renting lists and sending messages from the RNC/Trump without disclosing the source of the e-mail (the original list that the user signed up for) in the message itself. That may not be the only tactic being used, but I am convinced it is at least one of the tactics.From the number of users who claim to have been unable to unsubscribe, I also believe that the campaign is not maintaining a global e-mail suppression list. As a result, unsubscribing from one send may not unsubscribe the user from other sends. It is also possible/likely that sends are happening through multiple e-mail service providers or third-party senders and that suppression lists are not being shared between them.UPDATE 6/29/2016 8:18AM ET: Multiple reports have questioned the authenticity of the foreign messages ( Donald Trump is spamming foreign politicians asking for money , Britain: MPs object to ‘begging’ Trump emails ). I received an unsolicited fundraising message from “Team Trump” on June 21 tied to the domain GOPVictory365 | Landing Pages. It appears to be owned by the RNC. The message headers suggest the e-mail was sent from an Amazon IP and the domain’s nameservers were linked to an e-mail service provider that, from its website, appears to have deep GOP ties.UPDATE 6/29/2016 11:23AM ET: Multiple media outlets are now reporting on the foreign solicitation aspect of this story, but, still, no reports have thoroughly covered the SPAM aspect. Below are some more examples:Electoral fraud: Trump sends fundraiser emails to foreign politiciansUK Parliament members move forward to block Trump campaign emails due to 'offensive' contentDonald Trump Might Be Spamming Foreign Politicians For CashDenmark too: Trump Foreign Contributor/Derp UpdateUPDATE 6/29/2016 2:14PM ET: I have “liked” SCORES of Trump SPAM complaints on Twitter going back to the time of my first article. The problem of Trump SPAM appears to be widespread. If you browse my “likes” on Twitter ( Lenny Grover (@lennygrover) | Twitter ), you can view the tweets.UPDATE 6/29/2016 3:53PM ET: According to a new Associated Press report ( The Latest: Foreign officials say Trump appealing for funds ):Foreign officials are complaining that they're being "bombarded" by fundraising appeals from U.S. presidential candidate Donald Trump. And now, two watchdog groups are filing complaints against the Republican's campaign saying the practice breaks the law.[break]The complaint by watchdog groups Campaign Legal Center and Democracy 21 say the emails violated a federal law designed to prohibit foreign money in U.S. campaigns.UPDATE 6/29/2016 3:57PM ET: Tweets have been posted linking some of the e-mail addresses sent to (one-time e-mails) or sender information to lists maintained by other GOP politicians, including: Rand Paul, Chris Christie, Ben Carson, and Newt Gingrich. Their involvement has not been independently confirmed nor have the tweets been verified.Purely speculation on my part: I speculate that some GOP politicians, or conservative media outlets, who are not overtly supporting Trump may be covertly supporting the RNC/Trump e-mail campaign (and not want their information to be disclosed in the message that is sent to the list that they maintain).UPDATE 6/29/2016 8:04PM ET: Finally, the mainstream media is reporting on the FEC complaints:Trump fundraising emails overseas prompt complaints here and abroadComplaint filed about Donald Trump fundraising emailsBoth reports do not reflect the latest information in this post. Media outlets may be trying to confirm some of the information from Twitter that is still unverified. Also, there has been almost no reporting on deluge of domestic unsolicited e-mails and the difficulty people have had unsubscribing from Trump’s list.UPDATE 6/29/2016 9:17PM ET: Bloomberg joins the party:Trump Campaign Broke Law by Soliciting Foreign Donations, Groups AllegeUPDATE 6/29/2016 9:22PM ET: Now The Gaurdian:Trump campaign may have broken law by seeking foreign political donationsUPDATE 6/30/2016 10:54AM ET: A conversation I had on Twitter ( Lenny Grover on Twitter ), and the SPAM I personally received, links the mailing to at least three separate e-mail service providers: Adestra-com, Geniusmailer-com, and PsycloneContacts-net. Unconfirmed is that the campaign had been using NationBuilder and switched prior to the bulk e-mails being sent.UPDATE 6/30/2016 1:37PM ET: Evidently, Colbert mentioned Trump’s SPAM in his monologue ( The Late Show with Stephen Colbert Video - Trump Spams The United Kingdom - CBS.com ).UPDATE 6/30/2016 1:45PM ET: Another Tweet showing the sender signature suggests a fourth e-mail service provider is sending Trump SPAM (BlueHornet-com).UPDATE 6/30/2016 3:13PM ET: Josh Marshall at Talking Points Memo posted a very interesting article on the e-mail “blitz”:The Desperate and the Fail: Inside Trump's June Fundraising BlitzHe speculates that:At first, we thought he'd gotten the foreign politician emails from a crooked or stupid list broker. Having researched it a bit more, that seems less and less likely. It seems more like these were lists simply floating around the Trump Organization, tied to some earlier business venture, and someone in the campaign just decided to toss them in the hopper too. Admittedly, this seems like a preposterous theory. But all the conceivable explanations are equally preposterous. And yet one of them must be true since it definitely did happen.I published a long expose on Trump University on June 25th:Trump University Allegedly Pivoted from One Scheme to the NextSome facts from the article:In 2005, the most common SPAM title of the entire year, according to AOL, was about “Donald Trump”I found two e-mail messages from 2005 that were posted to online forums (and therefore preserved). An analysis of the content of the messages suggests one was likely sent by a notorious sender of SPAM, and both may have been sent by “affiliates” or “sub-affiliates” of Prosper Inc. (or related entities) to promote Trump University.I assumed, and Trump University president Michael Sexton’s deposition testimony suggests, that it was not directly involved with unauthorized promotion of Trump University by “affiliates” or “sub-affiliates” of Prosper sending copy that may differ from what it had approved via SPAM or other means.But, nevertheless, Josh Marshall’s present speculation is very interesting to me in that context…UPDATE 6/30/2016 4:19PM: The experts begin to weigh in:Laura Atkins from e-mail delivery consultancy “Word to the Wise” ( Trump's Fundraising Email - Bad Data Drives Delivery Problems ):it certainly doesn't seem like it was even political style opt-in.Ken Magill of The Magill Report ( The Magill Report ):A loose translation of the Occam’s-razor principle says the simplest answer is usually the right one. In this case, the simplest answer to the disparity in delivery rates between Trump and Clinton is Clinton is sending email to a permission-based list and Trump is not.UPDATE 6/30/2016 9:44PM: The Young Turks weigh in:Trump Illegally Fundraising From Foreign GovernmentsUPDATE 7/1/2016 2:52 AM: Thanks to great follow-up by Ken Vogel of Politico ( Kenneth P. Vogel on Twitter ), it is now even more likely that the Trump campaign sent unsolicited e-mail (SPAM). According to Vogel:Trump campaign renting some scammy lists for fundraising emails: National Tea Party Alert, Liberty News Network, Endeavor Media Group, etc.Endeavor Media Group owns Talon News and GOPUSA according to SourceWatch ( Endeavor Media Group, LLC ). GOPUSA currently has its e-mail list for rent through NextMark ( http://lists.nextmark.com/market... ). According to their data card, sending exclusive ads to the list costs only $8CPM and the list is clearly identified as “COMPILED LISTS”. The combination of the very low price and the compiled list designation makes it likely to not be a 100% opt-in list. If that is, in fact, the list that the Trump campaign rented from Endeavor Media Group, then they rented a list that was likely to contain at least some addresses that were not explicit opt-ins.UPDATE 7/1/2016 3:16PM: MPs in Canada have been getting the solicitations too:Canadian MPs ignore fundraising emails from Donald Trump | Toronto StarUPDATE 7/1/2016 10:29AM: I just posted another article on DailyKos (with evidence that people have been unable to unsubscribe from the mailings and that Corey Lewandowski lied on CNN about the list being opt-in/opt-out):Corey Lewandowski May Have LIED ON CNN About Trump Email SPAM (Not Opt-In, Some Claim Can't Opt Out)UPDATE 7/1/2016 12:32 PM: Josh Marshall at Talking Points Memo seems to be the journalist in hottest pursuit of the story. His latest article ( Welp, That's Weird. But of Course It Is ) suggests the foreign e-mails are coming from both the Trump campaign and a pro-Trump Super PAC. He suggests it might be evidence of illegal coordination (that both organizations are seeming sending to the same dirty list containing foreign politicians).UPDATE 7/3/2016 3:04AM: Cher’s verified Twitter account just posted Trump SPAM addressed to “Cherilyn” ( https://twitter.com/cher/status/... ). It has 196 retweets and 813 likes at this moment.UPDATE 7/3/2016 4:02AM: I just posted about Cher’s tweet:Cher Just Tweeted the SPAM She Received from Donald Trump to Her 3+ Million Followers
-
What is something interesting you learned in the past week?
I read somewhere on quora last week that if we perform a task for 21 days in a row daily, then that becomes an habit and we would do that involuntarily. I was skeptical about the theory and did some research online. I found that not many people believed in the 21 day theory and there were enough proof to suggest that more effort was required for forming a lifelong habit.I anyhow decided to try it. I decided to get up at 7 in the morning. For me, it was one of the most difficult thing as I am not a morning person and I am used to getting up late (sometimes at 9 or 10). I have since been getting up at 7 for a week and today I was surprised that I got up 5 minutes before the alarm rang.I also listed down some habits which I have been following since some years now. I found that some of them like watching random shows on TV and going through facebook feed was getting tiresome and was no longer enjoyable. These were habits which I had started somehow and it had become involuntary to the extent that as soon I came back home from office, I immediately switched on the TV or went online. These habits were no longer useful nor enjoyable. So, I have desisted myself from these habits during the week. It was difficult to fight the temptation to take the remote into hand but I have found some alternate activity to do in my leisure time. I have started reading on my favorite topics - psychology and philosophy. I have had more time to sleep and exercise after removing the time-wasting habits from my daily routine.During this process, I have found that small habits which we form over a period of time affect our lives to a large extent and a small change in our daily routine can make our lives more satisfying. Whether the 21 day habit theory is true or not, I now feel happy that during the last week, I have learnt the importance of good habits and have changed my habits for the better.
-
How do I become a GST practitioner?
In the GST regime, it is mandatory that before start helping one’s clients, one needs to register oneself as a GST Practitioner. In the present perspective, the process of GST migration has been in its full swing.There are numbers of businesses which are still oblivious regarding the appropriate procedure required for filing GST Returns and uploading invoices online. So they strictly require to contact/appoint an experienced, affordable and credible professional who can help them to deal with the new GST terms effectively.Sec. 48 of the CGST Act clearly mentions about the Conditions, Eligib...
-
Will the ransomware WannaCry do India more good than harm? Can we hope that this attack will instigate the people and government
Seeing this message ? Don’t despair, you are among more than 200,000 computers in 150 countries which have been affected.(Know more at: WannaCry ransomware: Everything you need to know, Why the WannaCry cyber attack is so bad, and so avoidable - Video)Although, it was initially reported that the impact on India will be HUGE. It is now being reported that the impact will be MINIMAL/ Sporadic.(Ref: WannaCry ransomware cyberattack fails to paralyse India; some businesses hit - Times of India)But, the caveat is that the impact may go under reported. Experts say that the rampant use of pirated software in India may leave Indian companies unable to report if they have been affected by the Wanna Cry cyber attack.(Ref: WannaCry ransomwares impact in India may go under-reported due to rampant use of pirate software)So yes, It may do more good than harm. We do hope that this attack will instigate the people and the gov of India to take major steps against internet piracy and to implement advanced computer networks and security measures. But it is up to each and every user and network administrator, to secure their own systems.It is incorrect to say that India was most affected because it is least protected. In fact, the impact was much lesser than expected. The government too tried to dispel rumors about banking telecom or aviation being hit by the outbreak. "There is no major impact in India unlike other countries. We are keeping a close watch. There have been isolated incidents in Kerala and Andhra Pradesh," Union information and technology minister Ravi Shankar Prasad said.Prasad said a Cyber Coordination Centre will start operating from next month to take precautions against such attacks in future. Besides, the cyber security arm of the Centre has asked banks, stock exchanges, and other vital institutions to safeguard their systems against the malware.The IT ministry has also signNowed out to agencies such as the RBI, NPCI and UIDAI, to warn them about the risks associated with WannaCry, and help to secure their systems, in order to make sure that digital payments in India are not affected.The Reserve Bank of India has notified all banks to operate their ATMs only after updating software systems to avoid being infected by ransomware. Automated teller machines are vulnerable to such malware attacks as they currently run on an older version of Microsoft's Windows XP, making the update highly necessary.There are a total of 2.2 lakh ATMs in India, of which many old ones run on Windows XP, for which Microsoft has officially ended support in 2014.IMPORTANT: If your PC has been infected, the following information will be of help:- (Source: Cyber Swachhta Kendra: Wannacry/ WannaCrypt Ransomware)The WannaCry ransom ware is writing itself into a random character folder in the 'ProgramData' folder with the file name of "tasksche.exe" or in 'C:\Windows\' folder with the file-name "mssecsvc.exe" and "tasksche.exe".Ransomware is granting full access to all files by using the command:Icacls . /grant Everyone:F /T /C /QUsing a batch script for operations:176641494574290.bathashes for WANNACRY ransomware:5bef35496fcbdbe841c82f4d1ab8b7c2775a0631fb8229b2aa3d7621427085ad7bf2b57f2a205768755c07f238fb32cc7f7ccaa16fb15eb1c7399d422f8363e88495400f199ac77853c53b5a3f278f3e84c82835a5d21bbcf75a61706d8ab54986721e64ffbd69aa6944b9672bcabb6d8dd63adb68ef053e044a5a2f46e0d2cdb0ad5902366f860f85b892867e5b1e87d6114ba5f10ad67a4131ab72531f02dadb349b97c37d22f5ea1d1841e3c89eb4e372d07207b4da75b3434584cd9f3450f529f4556a5126bba499c26d67892240Use endpoint protection/antivirus solutions to detect these files and remove the sameUsers and administrators are advised to take the following preventive measures to protect their computer networks from ransomware infection/ attacks:In order to prevent infection users and organizations are advised to apply patches to Windows systems as mentioned in Microsoft Security Bulletin MS17-010Microsoft Patch for Unsupported Versions such as Windows XP,Vista,Server 2003, Server 2008 etc. http://www.catalog.update.micros...To prevent data loss Users & Organisations are advised to take backup of Critical DataBlock SMB ports on Enterprise Edge/perimeter network devices [UDP 137, 138 and TCP 139, 445] or Disable SMBv1. https://support.microsoft.com/en...Apply following signatures/rules at IDS/IPSalert tcp $HOME_NET 445 -> any any (msg:"ET EXPLOIT Possible ETERNALBLUE MS17-010 Echo Response"; flow:from_server,established; content:"|00 00 00 31 ff|SMB|2b 00 00 00 00 98 07 c0|"; depth:16; fast_pattern; content:"|4a 6c 4a 6d 49 68 43 6c 42 73 72 00|"; distance:0; flowbits:isset,ETPRO.ETERNALBLUE; classtype:trojan-activity; sid:2024218; rev:2;)(http://docs.emergingthreats.net/bin/view/Main/2024218)alert smb any any -> $HOME_NET any (msg:"ET EXPLOIT Possible ETERNALBLUE MS17-010 Echo Request (set)"; flow:to_server,established; content:"|00 00 00 31 ff|SMB|2b 00 00 00 00 18 07 c0|"; depth:16; fast_pattern; content:"|4a 6c 4a 6d 49 68 43 6c 42 73 72 00|"; distance:0; flowbits:set,ETPRO.ETERNALBLUE; flowbits:noalert; classtype:trojan-activity; sid:2024220; rev:1;)alert smb $HOME_NET any -> any any (msg:"ET EXPLOIT Possible ETERNALBLUE MS17-010 Echo Response"; flow:from_server,established; content:"|00 00 00 31 ff|SMB|2b 00 00 00 00 98 07 c0|"; depth:16; fast_pattern; content:"|4a 6c 4a 6d 49 68 43 6c 42 73 72 00|"; distance:0; flowbits:isset,ETPRO.ETERNALBLUE; classtype:trojan-activity; sid:2024218; rev:1;)Yara:rule wannacry_1 : ransom{meta:author = "Joshua Cannell"description = "WannaCry Ransomware strings"weight = 100date = "2017-05-12"Strings:$s1 = "Ooops, your files have been encrypted!" wide ascii nocase$s2 = "Wanna Decryptor" wide ascii nocase$s3 = ".wcry" wide ascii nocase$s4 = "WANNACRY" wide ascii nocase$s5 = "WANACRY!" wide ascii nocase$s7 = "icacls . /grant Everyone:F /T /C /Q" wide ascii nocaseCondition:any of them}rule wannacry_2{meta:author = "Harold Ogden"description = "WannaCry Ransomware Strings"date = "2017-05-12"weight = 100strings:$string1 = "msg/m_bulgarian.wnry"$string2 = "msg/m_chinese (simplified).wnry"$string3 = "msg/m_chinese (traditional).wnry"$string4 = "msg/m_croatian.wnry"$string5 = "msg/m_czech.wnry"$string6 = "msg/m_danish.wnry"$string7 = "msg/m_dutch.wnry"$string8 = "msg/m_english.wnry"$string9 = "msg/m_filipino.wnry"$string10 = "msg/m_finnish.wnry"$string11 = "msg/m_french.wnry"$string12 = "msg/m_german.wnry"$string13 = "msg/m_greek.wnry"$string14 = "msg/m_indonesian.wnry"$string15 = "msg/m_italian.wnry"$string16 = "msg/m_japanese.wnry"$string17 = "msg/m_korean.wnry"$string18 = "msg/m_latvian.wnry"$string19 = "msg/m_norwegian.wnry"$string20 = "msg/m_polish.wnry"$string21 = "msg/m_portuguese.wnry"$string22 = "msg/m_romanian.wnry"$string23 = "msg/m_russian.wnry"$string24 = "msg/m_slovak.wnry"$string25 = "msg/m_spanish.wnry"$string26 = "msg/m_swedish.wnry"$string27 = "msg/m_turkish.wnry"$string28 = "msg/m_vietnamese.wnry"condition:any of ($string*)}Best practices to prevent ransomware attacks:Perform regular backups of all critical information to limit the impact of data or system loss and to help expedite the recovery process. Ideally, this data should be kept on a separate device, and backups should be stored offline.Establish a Sender Policy Framework (SPF),Domain Message Authentication Reporting and Conformance (DMARC), and DomainKeys Identified Mail (DKIM) for your domain, which is an email validation system designed to prevent spam by detecting email spoofing by which most of the ransomware samples successfully signNowes the corporate email boxes.Don't open attachments in unsolicited e-mails, even if they come from people in your contact list, and never click on a URL contained in an unsolicited e-mail, even if the link seems benign. In cases of genuine URLs close out the e-mail and go to the organization's website directly through browserRestrict execution of powershell /WSCRIPT in enterprise environment Ensure installation and use of the latest version (currently v5.0) of PowerShell, with enhanced logging enabled. script block logging, and transcription enabled. Send the associated logs to a centralized log repository for monitoring and analysis.Application whitelisting/Strict implementation of Software Restriction Policies (SRP) to block binaries running from %APPDATA%, %PROGRAMDATA% and %TEMP% paths. Ransomware sample drops and executes generally from these locations. Enforce application whitelisting on all endpoint workstations.Deploy web and email filters on the network. Configure these devices to scan for known bad domains, sources, and addresses; block these before receiving and downloading messages. Scan all emails, attachments, and downloads both on the host and at the mail gateway with a reputable antivirus solution.Disable macros in Microsoft Office products. Some Office products allow for the disabling of macros that originate from outside of an organization and can provide a hybrid approach when the organization depends on the legitimate use of macros. For Windows, specific settings can block macros originating from the Internet from running.Configure access controls including file, directory, and network share permissions with least privilege in mind. If a user only needs to read specific files, they should not have write access to those files, directories, or shares.Maintain updated Antivirus software on all systemsConsider installing Enhanced Mitigation Experience Toolkit, or similar host-level anti-exploitation tools.Block the attachments of file types, exe|pif|tmp|url|vb|vbe|scr|reg|cer|pst|cmd|com|bat|dll|dat|hlp|hta|js|wsfRegularly check the contents of backup files of databases for any unauthorized encrypted contents of data records or external elements, (backdoors /malicious scripts.)Keep the operating system third party applications (MS office, browsers, browser Plugins) up-to-date with the latest patches.Follow safe practices when browsing the web. Ensure the web browsers are secured enough with appropriate content controls.Network segmentation and segregation into security zones - help protect sensitive information and critical services. Separate administrative network from business processes with physical controls and Virtual Local Area Networks.Disable remote Desktop Connections, employ least-privileged accounts.Ensure integrity of the codes /scripts being used in database, authentication and sensitive systems, Check regularly for the integrity of the information stored in the databases.Restrict users' abilities (permissions) to install and run unwanted software applications.Enable personal firewalls on workstations.Implement strict External Device (USB drive) usage policy.Employ data-at-rest and data-in-transit encryption.Carry out vulnerability Assessment and Penetration Testing (VAPT) and information security audit of critical networks/systems, especially database servers from CERT-IN empaneled auditors. Repeat audits at regular intervals.Individuals or organizations are not encouraged to pay the ransom, as this does not guarantee files will be released. Report such instances of fraud to CERT-In and Law Enforcement agenciesGeneric Prevention Tools:Tool (NoMoreCry) to prevent Wannacry Ransomware by CCN-CERT:https://loreto.ccn-cert.cni.es/i...Sophos: http://Hitman.Prohttps://www.hitmanpro.com/en-us/...Bitdefender Anti-Crypto Vaccine and Anti-Ransomware (discontinued) https://labs.bitdefender.com/2016/03/combination-crypto-ransomware-vaccine-released/Malwarebytes Anti-Ransomware(formally Crypto Monitor)https://blog.malwarebytes.com/malwarebytes-news/2016/01/introducing-the-malwarebytes-anti-ransomware-beta/Trendmicro Ransomware Screen Unlocker tool:https://esupport.trendmicro.com/...Microsoft Enhanced mitigation and experience toolkit(EMET)https://www.microsoft.com/en-us/...Referenceshttps://technet.microsoft.com/li...http://www.catalog.update.micros...https://blogs.technet.microsoft....https://www.symantec.com/connect...https://securelist.com/blog/inci...https://securingtomorrow.mcafee....https://www.us-cert.gov/ncas/cur...http://blog.talosintelligence.co...https://www.trendmicro.com/vinfo...https://www.us-cert.gov/ncas/ale...http://blogs.quickheal.com/ms17-...http://blogs.quickheal.com/wanna...Wannacry/WannaCrypt Ransomware Presentation of CERT-In(PS: Thanks for reading/ upvotes. I write more here:- Jay Maan)
-
Why isn't the legal system willing to accept "I never received a notice," as a valid excuse? Why don't they simply mail the impo
When “I never received notice” isn’t a valid excuse, it is because too many people will, frankly, lie about this. People also make affirmative efforts to evade service. And sometimes people decide to just up and move without bothering to tell anyone. Shocking, I know.Thus, formal rules about service make it easy to determine whether service was done properly, and a party claiming lack of notice despite compliance with the rules will be required to prove the likelihood of actual lack of notice before the excuse will be even considered. On the other hand, if the party purportedly giving notice did not comply with the rules, the notice won’t be presumed to be valid without either an acknowledgment or waiver by the defendant.There are two different categories of notices—initial process and subsequent notice.For initial process, the court must obtain jurisdiction over the defendant. Traditionally this was done by personal service within the court’s territorial jurisdiction—the defendant needed to be “tagged.” This tagging was done by the sheriff (or a deputy), an agent of the court itself. If the defendant never showed up in the jurisdiction, the case could not proceed.¹More modern concepts of personal jurisdiction do not place as much emphasis on presence within the place; as any American law student will know, the case of International Shoe Co. v. State of Washington² established that personal jurisdiction could be asserted beyond a State’s boundaries if “minimum contacts” existed and “fair play” suggests that haling a foreign defendant to answer an in-state complaint would be reasonable.Of course, personal service by the state’s sheriff isn’t possible in such a case, and so most states do permit alternative forms of service as a matter of course (sometimes those alternative methods are available domestically as well). The exact requirements may vary by type of case and in any event will be spelled out in local rules of civil procedure; for proper advice you will want to consult a lawyer in the place where the action is. But generally, when initial process is involved, some form of service that leaves no doubt about the service, and the verification of some third party—the sheriff, the Post Office, a process server, &c—is required (the plaintiff in propria persona is not usually allowed to do initial personal service as they have as much motivation to lie about it as does the defendant). That might be personal service by a disinterested adult, another jurisdiction’s deputized sheriff, or service by certified mail.³ This means that someone is in a position to submit proof of the service to the court. (A defendant may also acknowledge service or waive⁴ any defects in service.)Now, for subsequent service, the rules tend to be a bit different. Once a party has been tagged and haled into court, they have a responsibility to themself and to the court to appear and present whatever defence they have to the action. Parties are, of course, entitled to notice of things that happen in the case—ex parte and sealed proceedings are extremely limited. But, at this point, because being party to a suit involves this responsibility, part of it is to keep the court and the other parties apprised of a proper address where notices may be served with a minimum of fuss (and to notify the court if that changes). Usually this is a mailing address and service is made by ordinary mail—which doesn’t require a signature and thus is less hassle for everyone—but in some cases service by e-mail, facsimile transmission, and the like may be agreed to (in the case of electronic case filing systems, e-mail service will likely be mandated as a condition of ECF use). Personal service is still permitted as a method of serving these subsequent papers, but not required. Again as to specific methods of service, you need to consult your local rules of procedure and the local attorney previously suggested.And so, a movant or the court will not be expected to make extraordinary efforts to provide “actual notice” of every single piece of paper by certified mail or personal service and give the defendant the opportunity to delay the case by evading service of motions. Neither will the court or other parties be required to chase a party around in the event of their moving and not leaving a forwarding address.⁵ Service to the “last known address” is almost universally sufficient. And the court won’t be impressed with “I didn’t get notices” when the lack of such notices is apparently the respondent’s own fault.N.B. This answer may be somewhat generalized for the United States; other legal régimes have their own ideas about notices.Notes:¹ A plaintiff unable to effect service could, of course, attempt to commence the action in another jurisdiction where the defendant could be found.² 326 U.S. 310 (1945). International Shoe is famous for the notion that an out-of-state defendant with “continuous and systematic contacts” to the state would nonetheless be susceptible to being sued there; the rule was further broadened by Burger King Corp. v. Rudzewicz, 471 U.S. 462 (1985), where even contacts that could not even be characterized as “minimum” with Florida were sufficient in the context of specifically making a comprehensive agreement to deal with a corporation legally resident in Florida.³ “Special service” or service not generally provided for by rule may be obtained by order of court only in the event that regular service cannot be obtained. Special service is usually publication. The purpose of special service is to allow the plaintiff to proceed with the action without having it stayed for an unreasonable period of time due to the absence of the defendant. The showing required for special service will vary by jurisdiction and possibly the facts of the case. And a defendant seeking to set aside a judgment obtained in this manner will have a much easier time of it than the defendant seeking to contest normal methods of service.⁴ As the primary purpose of service requirements is “notice to the defendant,” the mere fact that the defendant appears in the action suggests rather strongly that the defendant does in fact know about it. Consequently, a party seeking to challenge the validity of original service must do so at the outset and before making any substantive response to the complaint, otherwise the court will not hear such challenges and they will be deemed waived.⁵ We have this problem rather perennially in support court. I suspect it is a combination of general haplessness on the part of some of our obligors and deliberate efforts to evade our enforcement proceedings, but we get a lot of people who don’t show up at their contempt hearings because they “didn’t get notice.” The court issues bench warrants and most of the individuals are later arrested, and the failure of notice is not regarded as a defense by the court and in fact often leads to an additional contempt for failing to appear or to comply with the language in the support orders requiring parties to notify the court of address changes.
-
Is it unrealistic to try and become rich and successful through starting a business?
My Advice ,is try it here for FREE . At least if you fail , You are still at status QuoBusiness involve Real Money …Writing on Quora does not , trying out Online is one low risk business venture you can start offHave FunIn picking out a niche, see to it that you opt for one that you're interested in. As what you might have experienced, it's absolutely unhelpful to work with something that you loathe. It's rather difficult to convince customers to buy your product or service when you yourself don't have the heart to take interest in it.ChooseThe opening move to selecting a niche that's correct for you is to consider the issues and subject matter that you're most passionate about! By being passionate about a certain matter, you'll be motivated to learn more about it, teach other people about it, and work in it on a daily basis. Among the basic issues when it bears on failure in online business efforts is that a individual selects a niche that they think other people will be interested in, but they plainly have no interest in it themselves. Prevent this downfall right from the beginning - make certain whatever content you pick is that which you have a great interest in!While learning how to pick your niche, it's crucial to ensure that you've a great idea of your "target" audience. By discovering who's best suited as your audience, you'll be able to supply content that will meet the requirements that they have, and school them on items of their concern. It's equally crucial to guarantee that you're part of the audience that you're trying to draw in. This will guarantee that you cover every facet of your niche, and relate on a personal level with the other people that are in the same audience.Next apply the use of content that's uniquely yours. Exclusive material that you write, or have composed by ghost writers who produce professional SEO content, helps to demonstrate you as an authority in your niche. Ensure that your material can't be located anyplace else on the Net! This will immediately drive traffic to your site as you'll be providing visitors something fresh and unique. There are a lot of companies out there nowadays that may offer you unparalleled content.When you begin to put up material on your site, in article directories, or any additional location on the Net that's directly related to your niche, it's crucial to guarantee that you provide steady updates. This will keep your audience returning time and time again so that they might see the "newest" that you have to provide! This means provide fresh articles, keep your site maintained, and tailor your niche according to up to date trends.It's utterly imperative to see to it that you narrow the content down as much as conceivable. For instance, if you run a site on computer game cheat codes, you'll want to incorporate "computer game cheat codes" into your material, but your niche should be specialized to the type of computer game cheat codes that you provide. A good niche would be "The Sims Cheat Codes" - this will help interested Net users discover the material that they require fast!Its simple to learn how to pick your niche. The mystery to being successful is to pick a subject that you're passionate about, ascertain your audience, produce high quality, SEO content, update your material on a steady basis, and utilize keywords and keyword phrases that will reflect what your Net audience will look for.As an author, you've probably went through a lot of times when you just don't know what to write on. Maybe you've exhausted your common subjects and are looking for something different that will bring in the readers. This will give you hints for a few hot article topics. By applying these easy ideas, you'll be able to step-up your views, fascinate your audience, and ensure that your material brings in a constant stream of income.Write on an approaching holiday. General audiences are commonly interested in info concerning to the holidays. If the content is well written and furnishes info that is other than basic knowledge, you should see a good amount of views. These will fizzle out after the holiday has blown over, but will recover momentum, once the holiday approaches, once again.Research up to date events. If the matter is red-hot in the news, it will be red-hot to likely readers. Attempt to determine your own voice and present your data in a way that's unique to your audience.Write a report about pets. There are a lot of pet devotees around the world that like reading about their furry champions. Pet care is a great place to begin.Journal about our surroundings. Green is the up to date theme in news these days, and the chances are that it's here to stay. You are able to write about how persons may "green up" their lives, what fresh alternate fuels are being formulated, or how our environment is bearing upon wildlife. Any subject you decide to write on is likely to take in a powerful amount of readers.Tell individuals how to save income. This is among the most red-hot topics around, and it consistently pulls in viewers. The great thing about this subject is that there are perpetual ways to save revenue, so you should not have a problem making your material unique.Write on your passion. If you are profoundly interested in an issue, there is a great chance that other people are, as well.Do not forget to make your article original. Do not overexploit info that is vastly available over the Net. Pick out an easy yet unique title that will rank high on search engines, and draw in fresh readersAfter you've decided what niche to promote, you are able to then visit free affiliate sites which provide good-quality affiliate products. You must check that these have a great sales page with an elevated conversion rate. You are able to confirm this by getting hold of the creators of your chosen product. Make certain that your product fits with your niche. As well ask your self, if you were the consumer, would you purchase the product?A ProductIf you have been on the Net any length of time, then you know that affiliate marketing is an exceedingly lucrative way to bring forth income online. It's moderately simple, it may be done with little or no ad expenses, and an assortment of niches may be researched. Picking out the correct affiliate products to market is critical to your success. Abiding by these easy steps will assist you in making the most beneficial choices.Put together a list of affiliate products for each one of the niches that are of interest to you.Assess the commission structure of the affiliate plans on your list. Commissions commonly range from five percent to forty percent for palpable merchandise and up to seventy-five percent for digital merchandise.Have a look at the vendor's payment processes. The more reputable companies will pay you either via check or PayPal. A lot more will even pay you through an affiliate network, who will, in turn, compensate you by check or direct deposit to your chosen financial institution on behalf of the vendor.Have a look at the vendor's sales page. This is the page that will be looked at by visitors you refer to the parent company. A great sales page will be simple to read and simple to navigate when the buyer is prepared to make a purchase.Have a look at what the rivalry is marketing. Look up relevant keywords in your preferred search engine and check over the sponsored ads. In a lot of cases, these are advertisements are produced by other affiliates. If no one is promoting your chosen affiliate products or something like it, then there might be no demand for them in the current market.There are a lot of ways to market utilizing the Net. There's email marketing, PPC, banner advertising, utilizing videos, article promotion, doing SEO, blogging, and using social bookmarks, social networking and Web 2.0 properties. There's so much info out there, it may sometimes get overpowering. One way to figure matters out is to ask individuals who have become successful.Discover a discussion board that specializes in Internet marketing. These are sites where Internet marketers go to talk about the cutting-edge strategies, to determine what's working and what isn't, and to find reviews for the cutting-edge courses and software. Some that you might want to travel to are the Warrior Forum, Digital Point and IM4Newbies .The Warrior Forum is the oldest of the message boards and has been around since '96. Many superstars in the industry got their beginning here. It has the threads separated neatly into many different categories, like PPC, ad sense, article promotion, media buys, and so forth, so it's very simple to discover what you're seeking. The threads are well moderated and individuals here are commonly respectful and helpful to each other. This is an oddity in a lot of forums, where individuals tend to often be rather crude. So it's a huge plus that you are able to ask a question at the Warrior Forum without the dread of being called names. While the forum itself is free, there are frequently members offering cheap paid training courses of study called WSOs (Warrior Special Offers), and there's a lifetime upgrade for $37 as of 2010. This provides you access to a few members-only secret threads.Digital Point is likewise a good discussion board where individuals tend to be really helpful. It's organized in a great deal the same way as the Warrior Forum, while it hasn't been around as long, receiving its start in 2002. It's even so well regarded in the Internet marketing profession. It likewise has an area where you are able to outsource work that you don't wish to do yourself, like programming jobs, article authoring or site design.IM4Newbies, although much littler than either the Warrior Forum or Digital Point, is a dynamic community with about 70,000 members. It's a great place to get rolling for those completely fresh to Internet marketing as everything is set up for the fledglings, and they pay special attention to what they call their 101 classes, like Niche Marketing 101, Affiliate Marketing 101 and Net Business Management 101. It's likely less daunting to begin here too. As there are fewer threads, there's less of a data overload than what you may get at the other 2 forums.Make A Site Or BlogYou must produce your own site or blog, where you are able to put all your marketing techniques. If you want to maintain a site, be prepared to use a few bucks. Instead a quality hosting and a WordPress blog may guide you with the simple development of your page. The latter is truly helpful since you are able to join their site free of charge and you are able to be guided with whatever you desired to do with your page.Do It FreeIt is crucial to have an internet site if you have a business. Most internet sites commonly have multiple web pages that display info about the owner, product, service or contact. If you are merely setting out to have an internet presence with your business, it is a great idea to make a business web page. You are able to even begin a business web page free of charge.Look for a free web site hosting service online that lets you publish content. Some free of charge services that allow you to begin a web page fast are Blogger.com - Create a unique and beautiful blog. It’s easy and free., WordPress.com: Create a Free Website or Blog, Content Management System, Blog Software & Publishing Platform and weeby.com. Have a look through each of their choices and select the services that you like best. The advantage to these services is they are free of charge to use.Sign on for the service they're supplying. You need to make a username, a password and supply your e-mail address. After you sign on, you will have to pick out a title for your web site. Normally you are able to only register your site name under a sub domain name as you are hosting under their service. For instance, if you would like to produce a free of charge web page on WordPress.com: Create a Free Website or Blog and wish to title your pizza pie business http://greatpizzashop.com, your domain name will be WordPress.com.Pick out a template for your particular business type. You are able to pick from a lot of free templates. For instance, in Weebly you are able to select a design and choose from over thirty different templates. You are able to pick out the category themes ranging from instruction to marriages. You will prefer to pick "Business" for templates that have business conceptions.Produce material about your business and place a link to a product or service you are selling up on your freshly made web page.Push the publish button. Once you have a business template picked out, informational material and a product or service to sell, push the publish button. Individuals online will now be able to have a look at your business web page, which you made free of charge.Write write WriteWhen you get all set up, you must learn to enjoy writing since blogging is the chief way to communicate all the good things about your product with the buyers. Moreover, you are able to add an affiliate link in the resource box for your blog. When it's clicked, your reader will then be automatically redirected to the sales page. If you've your own product, then all you require is a simple webpage with an enlightening article about your product.AuthorAuthoring a great article that has relevant keywords to your niche included in it might be very confusing to a lot of online authors. On the other hand, if you wish to bring targeted traffic to your material or web pages, you need to include keywords in your material. This will give you a few great ideas on how to author an article that includes keywords to supercharge your article views or site visits.I keep reading associated articles that state to utilize the keyword tool supplied by Google; this is a great tip for web masters and authors. However, how many great keywords do you add to your material per length of article? Perhaps if we center on satisfying our readers with helpful info, the search engine top-ranking will come on its own. Shoving relevant words in articles is never advocated and it is looked at as "Black Hat" SEO or a spamming article. Attempt the steps here to write a good and helpful article that will be placed well from the words you pick to include in your articles or web pages.Perform research on Google trends. Discovering what data is searched for is a great idea when attempting to pick out a great article topic to write about. Monkey around with the Google tools and discover related keywords to include in your article(s).Prevent gorging your whole article with words that you're trying to get placed high for. This will just hurt your rankings. Author your article freely and aim the conversation or article info in a way to talk to your readers not the search engines.Include your primary keyword in your beginning and end paragraph. You are able to too include one in your main paragraphs as long as you're not wedging extra words into your content and articles. If you author a three hundred word article, attempt utilizing your key word around 3-4 times including one in your title.Author long and valuable info on your articles. Not only does Google like people friendly material, it likes to find well needed and valuable info to display in search engine results. The more valuable information, the more beneficial the ranking will be. Discover what individuals want to know about in your niche and explore the answersMarketing methodsIn increasing your sites traffic, you are able to quickly work at 3 kinds of easy methods: social marketing, forum marketing and article marketing.MarketOn social promoting, beginning building up your social network on Facebook and Twitter. Those are the two most well-situated to setup and most popular social web sites you will find currently. Begin establishing relationships with other people by becoming involved in a genuine and real discussion.In the discussion board marketing, you are able to begin by traveling to popular forums that accept topics touching on the problems or solutions that lead to your merchandise as the resolution. Go to Google and look for “discussion board”. Utilize different keyword phrase related to your niche. The method to link back to your web site is to utilize your signature to state a mighty advantage you are able to provide at your web site and post your website urlIn the meantime, you are able to post your articles to the leading article directories for the article promotion. The way I accomplish it is to re-purpose my own blog post. After my blog post is updated for a couple of days, I commonly submit that article to two primary article directories: http://ezinearticles.com and http://goarticles.com. Simply make certain you include a mighty beneficial statement in your resource box to link back to your web site. You need to incite the reader to come to your web site with that advantage you have listed.To produce a life long revenue in internet marketing business, you have to build up your own list. You might have heard it a lot of times that the revenue is in the list…and your relationship with that list as well.The ListIt does not take you long to learn to use a tool like Aweber to frame-up a potent system to build your list. The most beneficial tool is an auto responder like Email Marketing | AWeber to seize the e-mail addresses of people who come to your site. The wonderful thing about utilizing an auto responder system is you are able to author a series of e-mail sequences in advance prior to you getting your first subscriber that joins your list.It is referred to as “set it and forget it.” When the e-mail sequence is set up, you do not have to fret about it. A few internet marketers have set up the e-mail sequence to communicate with the subscriber base for a year or even longer.The primary goal is to utilize the e-mail sequence to establish trust with your subscriber base by giving helpful tips and tools that relate to your niche. Do not right away use a hard sell with anything in your beginning e-mail. You might utilize a strategy called “breath out, breath in”.That is to hand out useful info in your beginning e-mail, and then in the following e-mail you do a sales pitch to get the order in. And keep that cycle to get your subscriber base to read your e-mail and see your sales pitch or fresh info more naturally.Just like many of you, I at one time subjected myself in unrelentingly discovering ways to make money from home. I've constantly researched the net for tips and essentially steps on how I may begin my career online without necessarily leaving my job or overlooking the crucial events of my lifeI attempted to discover answers from net training programs just so I could simplify the seemingly complex techniques of the net world. Since I've forever believed in the construct of “teach a man to fish and you feed him for a lifetime”, I desired to share what I learned with you.I wish you to experience the success of net money-making and distinguish how you are able to produce income and have a Net lifestyle at the same time. Let’s begin now...
Trusted esignature solution— what our customers are saying
Get legally-binding signatures now!
Related searches to E mail eSignature Presentation Now
Frequently asked questions
How do i add an electronic signature to a word document?
How to make a pdf editable for esign?
How to sign pdf on box platform?
Get more for E mail eSignature Presentation Now
- How To Electronic signature South Dakota Plumbing PDF
- Help Me With Electronic signature South Dakota Plumbing PDF
- How Do I Electronic signature South Dakota Plumbing PDF
- How Can I Electronic signature South Dakota Plumbing PDF
- Can I Electronic signature South Dakota Plumbing PDF
- How To Electronic signature South Dakota Plumbing PDF
- How Do I Electronic signature South Dakota Plumbing PDF
- How Can I Electronic signature South Dakota Plumbing PDF
Find out other E mail eSignature Presentation Now
- Dc report of guardian form
- Florida equitable distribution worksheet form
- Florida equitable distribution worksheet 1996 form
- Florida board change address form
- Florida supreme court approved family law form 12903c2 answer to petition and counterpetition for dissolution of marriage with 10989987
- Motion for extension of time form
- Form 1 977 fact sheet printable
- Family law brochure fourteenth judicial circuit of bfloridab form
- Administration pasco form
- Expungement form for florida
- Divorce henry county form
- Iowa court rule 23 5 form 2
- Petition to probate will in solemn form chatham county ga chathamcourts
- Champaign county clerk form
- Illinois form statement
- Civil action cover sheet form
- Kansas condition of the ward form
- 102 divorce verified rule to show cause louisiana form
- Louisiana civil cover sheet form
- Divorce in louisiana form