Sign Form for Administrative Myself
Make the most out of your eSignature workflows with airSlate SignNow
Extensive suite of eSignature tools
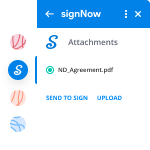
Discover the easiest way to Sign Form for Administrative Myself with our powerful tools that go beyond eSignature. Sign documents and collect data, signatures, and payments from other parties from a single solution.
Robust integration and API capabilities
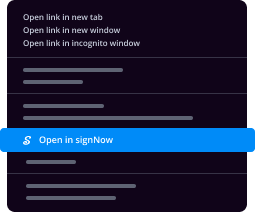
Enable the airSlate SignNow API and supercharge your workspace systems with eSignature tools. Streamline data routing and record updates with out-of-the-box integrations.
Advanced security and compliance
Set up your eSignature workflows while staying compliant with major eSignature, data protection, and eCommerce laws. Use airSlate SignNow to make every interaction with a document secure and compliant.
Various collaboration tools
Make communication and interaction within your team more transparent and effective. Accomplish more with minimal efforts on your side and add value to the business.
Enjoyable and stress-free signing experience
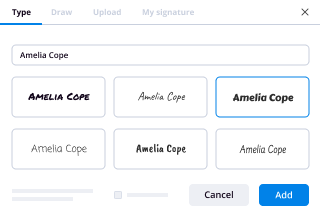
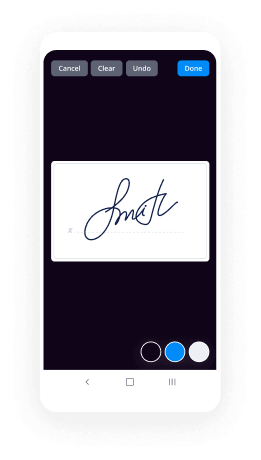
Delight your partners and employees with a straightforward way of signing documents. Make document approval flexible and precise.
Extensive support
Explore a range of video tutorials and guides on how to Sign Form for Administrative Myself. Get all the help you need from our dedicated support team.
How Can I Sign Presentation for Administrative
Keep your eSignature workflows on track
Make the signing process more streamlined and uniform
Take control of every aspect of the document execution process. eSign, send out for signature, manage, route, and save your documents in a single secure solution.
Add and collect signatures from anywhere
Let your customers and your team stay connected even when offline. Access airSlate SignNow to Sign Form for Administrative Myself from any platform or device: your laptop, mobile phone, or tablet.
Ensure error-free results with reusable templates
Templatize frequently used documents to save time and reduce the risk of common errors when sending out copies for signing.
Stay compliant and secure when eSigning
Use airSlate SignNow to Sign Form for Administrative Myself and ensure the integrity and security of your data at every step of the document execution cycle.
Enjoy the ease of setup and onboarding process
Have your eSignature workflow up and running in minutes. Take advantage of numerous detailed guides and tutorials, or contact our dedicated support team to make the most out of the airSlate SignNow functionality.
Benefit from integrations and API for maximum efficiency
Integrate with a rich selection of productivity and data storage tools. Create a more encrypted and seamless signing experience with the airSlate SignNow API.
Collect signatures
24x
faster
Reduce costs by
$30
per document
Save up to
40h
per employee / month
Our user reviews speak for themselves






-
Best ROI. Our customers achieve an average 7x ROI within the first six months.
-
Scales with your use cases. From SMBs to mid-market, airSlate SignNow delivers results for businesses of all sizes.
-
Intuitive UI and API. Sign and send documents from your apps in minutes.
A smarter way to work: —how to industry sign banking integrate
FAQs
-
What is your most unpopular opinion about the American education system?
I don’t like the sports environment in schools anymore. I think it’s really toxic and abusive.Once a year, a high school student will die from playing football in the US. Students are hit with life-altering injuries. Students are prepared to play sports and leave school without any other life skills in case it doesn’t work out. Football and baseball teams in my hometown are toxic environments that encourage sexual deviancy, drug use, and general asinine behavior.I think it’s stupid after awhile. The chance of a student making it to the professional leagues is extremely low, yet students are encouraged to work super hard to the point of injury for someone else’s paycheck. College athletes aren’t even compensated for their work, and they bring in massive revenues to the school. Imagine being hit as hard as these players do, 40 times for four years (not counting practice and scrimmages), then 48 times for four more years (not counting practices, playoffs, or scrimmages) without pay. It’s ludicrous, and just because a handful of NFL players make 20 million a year, doesn’t mean everyone does.I like sports a lot, I really do. However, the biggest turnoff for me about it all is how much athletes are manipulated in high school and college, and for baseball players the Minor Leagues where they’re paid about $5,000 a year. I would like to see less obsession and glorification over football, personally, even though I love the sport, it’s an extremely toxic environment and I don’t like how it affects our kids and woefully fails to prepare them for life after their 30’s.Written in five minutes.
-
What is the most honest thing you said in an interview which resulted in you not getting the job? How often does honesty backfir
What is the most honest thing you said in an interview due to which you didn't get the job? Seeing my financial situation, my room mate referred me to his friends. Who are linked with a consultancy firm.Later after few process I was sent to a BPO interview...That whole process of preparing, luring, and boring interview process made me feel worst...All candidates were tense, except me and few others who are best suited (not me).The coordinator gave few tips on how to get job in that company. It's like the question paper is out before the exam. The problem is that we've to say few lies to them to impress the recruiter.What all the questions they ask and how to respond. I lost ...
-
What’s the best thing you have ever said in an interview?
This happened approximately 4 years ago. At that time I was in college. And it was the dreaded placement season which we fear the most but is eventually the thing we all work our ass off to perform our best.I had already sat in 10–12 companies,getting screened out at various stages & somehow managing to signNow interview stage in only 2–3 of them. It was time when I might have started to go in my nutshell to avoid the feeling that will push me to doubt myself & eventually make the matters worse.Moreover seeing my friends get placed just added to the pressure a whole new level.Each day we woul...
-
Why do schools punish someone in a fight who is defending themself? Are people really expected to let themselves get beaten and
Yes, they are.And since bullies are very good at attacking when no one is looking, it is often the victim who is punished and the bully walks.It is this fear of getting in trouble that made my son not fight back against a bully for almost 2 years, from spring of 2nd grade to the beginning of 4th. Then that kid decided to sit with my kids on the bus. My daughter had to sit in the front seat because it had a seat belt which reminded her to stay seated. My son was assigned to sit with her to “help with her.” Ok, he was there to keep him away from the bullies in the back of the bus.Then the biggest bully decided to sit with them and the bus driver let him. Because there is nothing suspicious about a known bully wanting to sit with a younger child and his favorite target? He had already deliberately broken a pair of my son’s glasses. A couple of days later while the bus was loading and the driver was not watching them, he threw a punch at my daughter.Now some would say my kids should have just run away, right? There is no where to run on a bus, the bully was always by the aisle with my kids trapped against the wall, and my daughter was seat-belted in. My son blocked his first punch, blocked his second punch, then grabbed his hair, pulled him to the floor and sat on him. Problem solved.The bus driver declared an emergency, called the transportation office, and completely freaked out the principal who thought he had a dead kid. My son was given a “bus ticket” and kicked off the bus for a week. I was supposed to sign the ticket so he could give it to the driver to get back on.I did not.Instead, I wrote a letter to the transportation department outlining every time my kids had been attacked, harmed, broken glasses, etc. on the bus. It was a long list. And listing all punishments meted out. None. The next time the bully tried to sit with my kids, my son blocked the seat and pointed to the back of the bus. That was the last time my son was bothered on the bus, and it also solved most of the play ground bullying. Because they now knew that he would defend himself. Fortunately, the principal did take the time to figure out what had actually happened and the incident did not harm the good relationship we had with him.A couple of years later a boy ripped my daughter’s glasses of her face and refused to give them back. This attack fits the definition of assault under state law. He literally mugged her. My daughter, of course, retrieved her property. In doing so she used a phrase that was not deemed school appropriate.At least a dozen kids saw the whole thing. Not one of them tried to help her. Not one of them tried to tell the driver what was happening. I know at least a dozen watched it happen, because about a dozen kids did complain to the bus driver and their parents about my daughter’s language. A dozen nice, church-going kids from nice church going families decided that an assault was not worth mentioning, but the language of the victim was the problem. That is what we are teaching our kids these days, apparently.And of the dozen or so parents not one inquired as to the well-being of the victim. Not one was worried that the little girl who had been attacked had been hurt. Instead they called the school to complain that my daughter had used a swear word on the bus. The principal called me in for a chat and I told her what had happened. After a short discussion she decided to be extremely generous in not punishing my daughter as she had been “provoked.” More likely, she did not want the school district personnel involved (again) because she was not supposed to be involved with anything to do with my daughter (long story). I suggested that it might be a good idea to talk to the boy involved and explain to him that it is not ok to attack other students. She said that that would not be necessary. The principal did not think that it was necessary to tell a child that it is not ok to attack and rob other children.That is what “zero tolerance” can do. It can mean “bullies rule and don’t you dare fight back.” Good in theory, but not always so good in practice. In the first case, every child on that bus learned not to attack my children. In the second every child on that bus learned that attacking, assaulting, robbing, is ok, but don’t you dare “swear”, even while defending yourself. Pretty messed up priorities in my opinion.
-
If a Democrat wins the presidency next election, couldn’t they just reverse most of what Trump has done like he has with Obama?
Yup.Turns out Mr. Pen and Phone wasn’t as effective as he thought.That’s what happens when your entire legacy is built on executive orders. Sandcastles swept away with the tide. That’s why presidents don’t make law. Congress does.That’s why DACA was rolled back.That’s why we pulled out of the Paris Climate Agreement.That’s why Obamacare is coming undone.That’s why a bleep-ton of Federal Regulations on businesses have been cancelled.That’s why the Iran deal is under siege.That’s why the Mexico City policy was rescinded.That’s why the Dear Colleague Memorandum on Title IX was repealed.That’s why we may now get to bring back elephants shot in Zimbabwe and the other place I’m too lazy to look up.All Executive Orders or EOs in a certain capacity.All sandcastles.And now all dead or on death’s doorstep.The good news for Democrats and anti-Republicans is that the same thing will happen when the next Dem comes into the White House.Goodbye Border Wall.Hello Obamacare 2.0.Welcome back to Paris, Mr. President.Not even The Wall can keep the tide away from his EO sandcastles, even if he tinted them with gold.You what lasts for the test of time?Law.Law passed by your congressmen in the House and the Senate, that have enough of a majority and public support to break past the deadlock, the gerrymandering, the scheming and plotting. Laws that go past petty partisanship that are vital for the security of the nation and her people.You can debate whether or not the laws you want should be above partisan politics, whether that be guns, abortion, climate change, illegals, or trigger warnings, but the fact remains that for each issue, neither side has the vast majority to sweep in and inact those laws.Why?Because you’ve become convinced that only the president can change things. Only the president and his EOs can change the country.Trump has not only shattered that illusion, but he took “a big beautiful dump on it. Believe me.”Stop looking to the White House for your vision, and turn it back on your Congressman. They’re supposed to listen to you, to represent you, to be your voice under the Capitol Dome.Call them. Tweet them. Facebook them. Harass and harangue them until they listen to you, and if they refuse, then why the hell are you voting for them?Turn that House of Cards in on itself.The president is the chief executive. He doesn’t make the law. He enforces it.You’re barking up the wrong tree.Edit:So I just want to clarify a few things instead repeating myself in the comments:ACA:Obamacare was and is signed legislation. I apologize for not being clear.This is why Trump can’t do anything to remove it, at least without Republican support, but they’re completely split between repeal/replace or downright repeal.There are however, suspicious EOs applied to Obamacare that some would argue exceed the law.Now normally, Congress would take a look and try and edits the kinks.But by the time the problems of Obamacare arose, Obama’s lost the House and his super majority Senate. Which meant the kinks and majors issue could not be resolved through legislation. Hence EOs.Opinion | How the Obama administration’s executive actions sabotaged ObamacareKeep in mind, this is the Washington Post, the same Post that still has “Democracy Dies in Darkness” in the header after the election of Trump, so you know that this is serious, even for the Lefties.If Trump can’t get a repeal through Congress, he’s just going to take Obama’s EO bandaids off and watch it bleed to death until the budget itself requires a repeal.Title IX:This is the specific item that Betsy Devos wants to remove.Dear Colleague Letter from Assistant Secretary for Civil Rights Russlynn Ali. -- PrintableThis was sent out in 2011 by the Obama Administration that basically removed the “beyond reasonable doubt” part of rape accusations.Please pay special attention to page 2 on that bleeping 1 in 5 rape statistic that has been debunked so many times I’m wondering if Obama either had a brain fart when he wrote that or if he was just pandering to his feminist base.Refer to page 4 and 5 about the action taken: “if the school knows or reasonably knows… Title IX requires the school to take immediate action to eliminate the harassment, prevent its recurrence, and address its effects.”No proof required. After all a woman would never lie. I could have sworn I heard something called “…beyond a reasonable doubt…”And my favorite part: “if the complainant requests confidentially… the school should take all reasonable steps to investigate and respond to the complaint consistent with the request to confidentiality…”That’s right, whoever heard of the right to face your accuser? A sexist probably.Utterly disgusting.Which is why it would never pass in Congress.Title IX was in place since the 70s, which basically reiterates the 1964 Civil Rights Act in gendered form for institutions that take federal tax dollars. That is these institutions can’t discriminate nor prohibit based on sex and everything that goes into it.Here’s the law: Title IX and Sex Discrimination.No where in signed Law does it state that these institutions should “listen and believe?” Hence the EO (or really a Dear Colleague).Because apparently, one in five, sorry, now it’s one in four women in colleges are being sexually assaulted or worse… raped.And gosh darn it, we’re just not doing enough to stop it. And if it wasn’t for those evil sexist Republicans and their archaic principles of Innocent until Proven Guilty, we can start punishing these animals… I mean men… I mean rapists… I mean sexual assaulters… I mean…Oh wait, what’s this…Campus Sexual Assault Researchers: Setting the Record Straight on '1-in-5'And this…The Many Problems With Campus Sexual Assault SurveysYet another leftist site calling out the statistic when their base has so much to gain.Are 1 in 5 Women Raped at College?Yes, I know Prager is Conservative-leaning and this offers motive to dispute, but they present the facts clearly and cite sources as well as add on other consequences to this statistic that other outlets fail to mention.I’ll also add this video by a YouTuber named Sargon of Akkad who analyzes everything about Mattress Girl and how Obama’s memo regarding Title IX affected this:Its fifty minutes long, so I understand if ya’ll don’t have the time, but look at the like/dislike ratio. That amount of universal support shows that Sargon attempted to remain as objectionable as possible and present nothing but the facts regarding how Obama’s Title IX ruined a man’s life.This is what Trump and Devos want to remove, and I fully support it. An EO (pseudo-EO really) that can and is abused by opportunistic man-hating feminists.Thank you all again for you’re upvotes and comments. I really do appreciate the feedback.
-
I need a signature from a professor I have never met in order to be accepted into engineering grad school. How do I ask for his
It’s not clear from your question whether this is a professor with some administrative responsibility over your academics, (e.g. - a department head in your major) or someone who has decision-making authority over the acceptance into grad school.In either case - If the signature is appropriate, the polite way is to ask in person or by phone and following up with a written request letter or email. (See below)It’s best to have the letter written and in front of you with all of the relevant information when you ask. You can always send it if you are unable to ask in person.Note - In some cases, emailing a scanned document might be reasonable, but if email is the preferred method, confirm via an immediate follow up call or email that that format works for them.It should include:Your name and current contact information with any supporting reference materials.Includes copies of transcripts or student i.d. numbers if they are signing off on course completion.What the purpose of the request is (e.g., grad school program).What the reason is that you are asking them specifically.If they are a backup for a professor that does know you, this is where you explain the reason that that person is not feasible and provide any information you have (email or phone) that would allow them to follow up with that person.What/where you need them to sign - CLEARLY INDICATED.Who the specific recipent(s) will be.WHEN IT IS REQUESTED TO BE SENT OR AVAILABLE BY**What you are requesting that they do with the signed form.If you are asking them to forward it, a fully addressed and postage-paid envelope.**In addition to making it clear in your request letter, place a post-it on the envelope with “Please mail by…” on it, and specify a date at least 4–7 days before the due date to allow for mistakes or administrative delay in mail signNowing it’s recipient.Time permitting — It is always preferable to arrange to pick up signed documents in person and forward them yourself, after verifying that they are complete and correct.If you need a separate signed copy for yourself, you can request that they send it to you in a separate (provided) envelop or retain it for pickup.If the person has agreed verbally or via email to complete the form and follow any other requested steps, it is completely acceptable to follow up on the early shipping or pick-up date to verify that they have completed and/or forwarded it as requested.Most people appreciate this reminder, especially if something that they have promised has not been processed. Note that the 4–7 day “grace period” leaves time to rectify this, if needed.Important note - When requesting ANY sort of reference or document completion, it is NEVER appropriate to act as if your own late or last-minute request is a reason for someone to deviate from their standard practices.At most, you might say, “I was not given adequate time myself for the following reasons, but I would appreciate it very much if you could….. Is that possible?”They are only responsible to you for what they have agreed to obligate themselves to, not what you are obligated to do to meet your aims and ends.Remember - “Lack of preparedness on your part does NOT constitute an emergency on my part.”
-
Atheists, what is the worst insult you’ve received (related specifically to your atheism)?
Atheists, what is the worst insult you’ve received (related specifically to your atheism)?Like many, it was right here from a purveyor of love and Christian Kindness. Buckle up, buttercup, because we’re going for a ride down memory lane.The setup;I’d written an award-worthy answer to “Why do many atheists think that Christians hate them?” which, in retrospect, I could have answered more easily by just saying “because 99.793% of all they do supports that thesis.” but I didn’t. Short answers go to Collapseland, so I expanded on the theme.So, a loving Christian offered this in the comments;That, in itself, isn’t so bad. He does refer to atheists as Meaningless Garbage, but like recognizes like. It’s to set the scene for what was to come because Mr. Numb***s F***wit started to mash a little harder on the Hate Throttle;A couple minutes ago I started trying to go through the second in Gimp and highlight all the stuff he’d like me to lay at his doorstep under the instructions of Matthew 7:12…but the more I highlighted the more I realized that essentially it’s all hatred under the guise of some numb***s f***wit just being a f***wit of the numb***s variety. Were I to pinpoint the insults with yellow highlighting, it’d just look like a puppy full of Mellow Yellow pissed all over it.So, yeah. Worst (best?) insult I’ve gotten was to be repeatedly called an excrement eater and more by a grumpy theist. What was his issue? Dunno. Might’ve been a Big Bad Wolf-Modernized situation; at some point in the past, he was approached by a Big Bad Atheist. Scurrying to cover, he felt she could not effect him. But the Big Bad Atheist…She huffed…And she puffed…And she blew the guy’s boyfriend?Dunno. Not my circus, not my monkeys. I don’t have the authorization to euthanize or the patience to dig deeper to find the root cause, so I just nod, smile, and laugh inwardly at the baked-in hilarity of him not understanding, among other things, that he is the epitome of the Hateful Christian. Insults sting in proportion to the value you place on the insulting party…and I could fart all month and still not give a shit what that bloviating theist says.The funniest part for me was the overwhelming lack of any theists to step up and say “Hey asshole, calm down the rhetoric here, you’re making us look like we actually are. Not good for the advertising side, so knock it off.” That, I find hilarious.Not only that, but if I were to uncork the phrase “excrement eater” toward a theist on this site…Quora moderation would contact Belarus (always use an intermediary, it’s just good practices) who would contact Russia. Russia would rotate one of their warhead satellites, which they have; I saw Space Cowboys and it’s a great flick. Quora has a copy of my ID because some jerkhead tried to get me banned for Name Vio, so they have my home address and they’d have forwarded those GPS coordinates with the request. So Russia would just rotate that nuke warhead so it’s pointed right at me, slap a post-it with “BNBR, noob” on the working end of it, and let ’er rip from 200 miles up. I would be no more. Little bit of goo, little bit of eww, and a shit-ton of posts written by the famed “Quora User”…if those posts even survived in my absence.This is a fun site. Or…at least it could be. It’s really an excellent study in human psychology; why would a guy like me give hundreds of hours to generate content for a site that’s giving me nothing in return, that consistently holds some of its contributors to a lesser standard than I am bound to? I do not know, but here I am anyways. Here we are…If anybody figures out why, pass it on. At this point, at least for me, it’s like a poker game; it’s deep into the game and I have so much invested to the pot that it’s very difficult to stomach the idea of folding and leaving the game, even though I can see clearly that there’s no victory to be had, no gain to be made for me. Still, the chips I have invested have got me mentally handcuffed; I realize there’s no point to staying in the hand, but the sheer volume of all my 1,860+24 chips has me feeling like I’ve invested too much to just fold. Many a good poker player has lost everything including cab fare home because of the same psychological tendency; the more you put in the pot, the harder it becomes to fold ’em and say “Well played, until we meet again.”And would you look at that, 1,861 chips…
-
What's the most petty/funny way you've seen a business/person comply with a law or take advantage of its loophole?
The Department of Transportation/Federal Motor Carrier Safety Administration requires companies that have big trucks, especially those that drive interstate, to keep files on their drivers. These are called DQ (Driver Qualification) files and consist of an application for employment, a driver’s record (which you’ve checked over), negative pre-employment and random drug and alcohol testing reports, and copies of their valid commercial DLs and health cards (i.e., Medical Examiner’s Certificates).A state trooper had gotten angry with us for some reason, so he referred us for an audit, which did occur in a limited form. Basically, it was limited to collating mechanic’s repair reports with driver’s need-repairs reports and looking over the DQ files. It turns out that the auditor liked us; he seemed to have a genuine affinity for our little trucking operation, and so he performed a very limited audit, which we passed, with only a couple of infractions noted.If I remember there were two infractions, both of which being easy to fix.One was that he noted the owner/President of the company did not have an application for employment.—I took the owner a job application. He wrote in his name and information. For job wanted, he put boss.For references, he listed me, myself, and I (three references). How long had these people known him? He put down his age.For salary requested, he wrote as much as I can get. Signed it, dated it.I filed it away, and I guess he was hired over 30 years after he started the company.
-
How do you protect your computer from being hacked?
Disclaimer: I am not a certified cybersecurity professional like my colleague Brendon Taylor.I am however, like many who work in the IT industry, de facto help desk and tech support for family, friends and relatives when they are having problems with their PCs, laptops and devices. Think of this answer a community service announcement to lessen your home tech support pain and improve the cybersecurity and safety of your loved ones.No doubt you have fielded a call from a relative asking something like: “My computer’s acting weird” or worse: “I’m getting messages on my machine and can’t login — what’s bitcoin and why do I have to pay to unlock my computer?”That’s when you get that sinking feeling that your weekend just got busier, and wish that you had spent a little more time beforehand educating them on some cybersecurity basics. As they say, an ounce of prevention is worth a pound of cure.Outlined below are the top twelve tips you can share (or implement yourself) to better prepare before you get that call, to make everyone’s lives just a little safer online.Work out what to protect. The starting point is to work out your digital footprint — i.e. what data you have, where it is, who has access to it, and what you want to protect. Take an inventory of all of your sensitive material so you can start to consolidate your data — it’s a good time to do a virtual spring clean too. You may often be surprised what information you have sprawled on USBs, external hard drives, mobile devices, in the cloud, on camera SD cards, in printer/scanner memory, on your PC or laptop.Backup regularly. Sooner or later, something’s going to go wrong, whether malicious or user error, that will destroy data. You need to assume that this is inevitable and get a simple, effective backup solution in place that runs frequently. If you are using a physical external device, ensure that you disconnect it after backing up or it may be just as vulnerable to data loss. It doesn’t hurt to check that the backups are working periodically too — goodness knows there have been enough professional system admins who have gone to restore from a backup only to find them corrupted or incomplete.Update regularly. Patching or updating your operating system, applications and (if you are confident) firmware is essential to reduce the number of vulnerabilities that can be used to access your device. Just like the weakest link in a chain, all it takes is a single chink in your system armour to gain a foothold. Whilst not a panacea, it certainly reduces the attack surface of vulnerabilities. Refer back to point #2 above though, sometimes your updates may not apply correctly and there are times a home techie will need to restore to a prior state if the patch you just applied didn’t work as expected.Use antivirus/anti-malware and keep signatures up to date. Whilst having an antivirus solution is not the silver bullet that some users assume them to be, they do at least provide a level of protection. Keep the signatures up to date and run scans regularly, particularly on specific files before opening them or if you notice any unusual behaviour on your system. And consider using ad blockers with your browsers too.Use strong (and unique) passwords for each key system. Better yet, use a password manager like LastPass, Dashlane or 1Password. Re-using the same password is a bad idea — if someone discovers it, they could use your password to login in to your social media, work systems or banking information so it is better to keep them separate. And please, please, don’t use the top worst passwords that are prone to reuse. Find something unique, and not too short — every extra character adds to the effort required to brute force it. And it goes without saying, don’t put passwords on a sticky note or in your wallet.Use encryption. This is a broad recommendation, but what is important here is wherever you can, secure your information so that it is harder to access or intercept. Encrypt your hard drive with something like BitLocker, your external drives and USBs so if you drop them they aren’t easily accessible, look for the lock sign (SSL) for web sites, and check the encryption settings on the apps you use. Consider using Virtual Private Networks (VPNs) for more secure communication where appropriate.Always click with caution. Whether you are opening an attachment in an email or downloading and installing an app, you need to do some form of checking or verification if you think that something feels dodgy. It goes without saying, don’t run pirated software or apps from suspect web sites. With shortened web addresses it can be tricky to see what you are clicking through to. You can check these shortened URLs by using a site like CheckShortURL.com or Sucuri, or if you want to get really fancy, check out Cisco’s Talos IP and Domain Reputation Center. Calling the original sender of an email or business can be a useful alternative method of verification.Be careful what information you share and check your privacy settings. With social media privacy standards evolving regularly, it is important to check your settings to understand if you are sharing public information you didn’t mean to, such as location data, personal information like date of birth, or photos that weren’t intended for the public domain. A quick google search on your name or email address may surface information available to the public, and whether it represents you appropriately. If not, look to remove it from public view. While you are at it, be sure to check the HaveIBeenPwned website by Troy Hunt to see if your account information may have been leaked through a variety of data bsignNowes. If your account shows up, it is highly recommended that you change your passwords immediately.Watch the Wi-Fi. At home, it is important to ensure that you have taken the basic steps to secure your Wi-Fi, including: changing the default network name and password, hiding the signal from public view, updating the encryption level to the highest available and ensuring that you check periodically that there are no unknown devices attached. In public, you should approach any public Wi-Fi network with extreme caution as you don’t know who is intercepting the traffic that you are passing and where it is going. If you need any reinforcement of this, check out this article from CSO on why you should never connect to public Wi-Fi.Consider multi factor authentication. Having a second method set up to verify who you are beyond the initial system password is worth the effort for more sensitive data. There’s a useful paper from the Australian Cyber Security Centre on multi factor authentication if you want to read more.Don’t forget physical security. Devices are prone to theft or tampering, so make sure that you don’t leave them unlocked or out in the open as visible temptation for thieves. And of course, the more mobile the device, the more likely you are to lose it — looking at the 2018 Uber Lost & Found Index the number one device lost is the mobile phone. So make sure it has a passcode on it and set up the ability to find it or wipe it remotely if possible. And finally, when you are disposing of old devices, make sure you are thoroughly wiping all of the data off it.Keep informed. Technology is constantly changing, as are privacy standards and vulnerabilities that can be exploited, both through systems and more sophisticated scam techniques. Follow or subscribe to useful trusted sources of security information, such as Stay Smart Online and Scamwatch in Australia. For more advanced reading around cybersecurity or those who like listening to podcasts, check out the following: Brian Krebs, Brian Johnson — 7 Minute Security podcasts, Sans.Org Information Security Resources, Security Week or Dark Reading.I’m sure most of these cybersecurity basics apply equally well in start-ups, small business and enterprise, it is just the scale and complexity of the challenge that requires additional governance and broader controls fit for your industry. And like the old adage “charity begins at home”, so too should cybersecurity, because these habits translate into our schools, our institutions, and our businesses. These days the line between home and work are becoming more and more blurry, so being safer at home can reduce your business risk too — not to mention saving you time on the weekends not having to deal with as many unexpected tech support issues at home!Other useful resources:NSA’s Best Practices for Keeping Your Home Network SecureMicrosoft Top Tips for Internet Safety at HomeStaySmartOnline — Protect Your StuffATO Top Cybersecurity Tips for IndividualsCybersecurity While Travelling Tip CardACSC Protect: Essential Eight ExplainedReport a Cybercrime — Australian Cybercrime Online Reporting Network
Trusted esignature solution— what our customers are saying
be ready to get more
Get legally-binding signatures now!
Related searches to Sign Form for Administrative Myself
Frequently asked questions
How do i add an electronic signature to a word document?
When a client enters information (such as a password) into the online form on , the information is encrypted so the client cannot see it. An authorized representative for the client, called a "Doe Representative," must enter the information into the "Signature" field to complete the signature.
How to create an electronic signature pic?
it/PV4eVY — Donald Trump Jr.'s Lawyer (@mandy_cooper13)
Trump Jr. also sent the email after news broke that former acting Attorney General Sally Yates had alerted the White House that Flynn might have lied about discussing sanctions with then-Russian ambassador Sergey Kislyak.
The White House, which initially said that Trump didn't know any details about Flynn until he learned about it later — then said that the president only found out about them through media reports — has faced questions about why Trump's son was seeking to establish communications with the Russian government in the first place.
In a series of tweets, Trump Jr. denied that he and others had received the emails, and called the Times story "a COMPLETE and TOTAL FABRICATION" of his meeting. He said the Times' "fictional account" was "100% made up."
This morning's NY Times Magazine cover: "How Vladimir Putin Created Donald Trump." — Donald Trump Jr. (@DonaldJTrumpJr)
Flynn's resignation Monday came the same day that he was interviewed by FBI agents about the meeting — as part of Robert Mueller's probe of Russia's meddling in the US presidential election.
What is the proper way to desiginate an electronic signature in the federal court system in ms?
I am aware of the court's rules on electronic signatures and it seems that the answer, for the current time, is the same as it is for the private party in the case. If you have any insight or comments on this please don't hesitate to contact:
David R. Littman
Box 688
Tucson, AZ 85712
Phone: 520-548-9000
e-mail: djlittman@
This article was originally published in the Spring 2011 issue of
More From
Get more for Sign Form for Administrative Myself
- Help Me With Electronic signature Alaska Courts PDF
- How Do I Electronic signature Alaska Courts PDF
- How To Electronic signature Alaska Courts PDF
- Help Me With Electronic signature Alaska Courts PDF
- How Can I Electronic signature Alaska Courts PDF
- Help Me With Electronic signature Alaska Courts PDF
- How Can I Electronic signature Alaska Courts PDF
- Can I Electronic signature Alaska Courts PDF
Find out other Sign Form for Administrative Myself
- Cobra forms
- Training agreement contract form
- Health information form
- Notice subpoena form
- Nonexempt form
- Agreement addendum form
- Exempt form
- Family medical leave form
- Training checklist form
- Employee warning document form
- Reciprocal contract form
- Employee handbook form
- Permission form
- Employee new hire form
- Agreement disclose form
- Personal guaranty of another persons agreement to pay consultant form
- Consulting and marketing agreement wireless communications form
- Complaint to terminate lease form
- Notice creditors form
- Reaffirmation agreement motion and order form