Remove eSignature Document Computer
Make the most out of your eSignature workflows with airSlate SignNow
Extensive suite of eSignature tools
Robust integration and API capabilities
Advanced security and compliance
Various collaboration tools
Enjoyable and stress-free signing experience
Extensive support
How To Remove Sign Document
Keep your eSignature workflows on track
Our user reviews speak for themselves






Remove eSignature Document Computer. Discover by far the most end user-helpful experience with airSlate SignNow. Control your entire record digesting and sharing process electronically. Range from hand-held, document-based and erroneous workflows to programmed, digital and perfect. You can easily generate, deliver and sign any documents on any system everywhere. Ensure that your airSlate SignNow organization circumstances don't slip over the top.
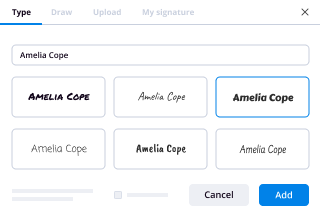
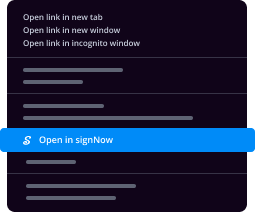
See how to Remove eSignature Document Computer. Stick to the simple manual to get started:
- Make your airSlate SignNow bank account in click throughs or log on with your Facebook or Google accounts.
- Benefit from the 30-day time trial offer or go with a prices prepare that's perfect for you.
- Discover any legal format, construct on the internet fillable forms and share them securely.
- Use sophisticated characteristics to Remove eSignature Document Computer.
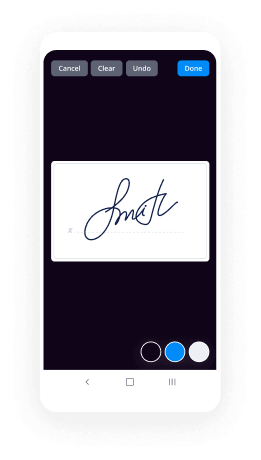
- Sign, individualize signing order and acquire in-individual signatures 10 times speedier.
- Set up intelligent reminders and receive notices at each step.
Shifting your jobs into airSlate SignNow is straightforward. What adheres to is a simple method to Remove eSignature Document Computer, in addition to ideas to keep your fellow workers and companions for far better alliance. Empower your workers using the finest resources to stay on top of company operations. Enhance productiveness and scale your small business quicker.
How it works
Rate your experience
-
Best ROI. Our customers achieve an average 7x ROI within the first six months.
-
Scales with your use cases. From SMBs to mid-market, airSlate SignNow delivers results for businesses of all sizes.
-
Intuitive UI and API. Sign and send documents from your apps in minutes.
A smarter way to work: —how to industry sign banking integrate
FAQs
-
If you sign an e-filed document with a character that changes your name, would it no longer be legally binding?
This might become a question for the trier of fact, were the matter to somehow make it into court (on an action for bsignNow or a declaratory judgment).There’s no particular formality required of a legal signature—any mark that is intended as a signature is a signature. You can sign a document with an “X” or your initials or the words “I got this,” and theoretically it’s just as binding as a perfect cursive script of your name.The custom that signatures are handwritten is based on a traditional method of authentication—if the signature is handwritten in the maker’s usual handwriting, that is actually a fact that helps prove it’s a signature. If the signature is something other than that, it’s good practice to have witnesses also subscribe—in the event of a dispute the witnesses could be asked to testify that yes, they saw the maker sign the instrument and they themselves signed to attests that fact.“E-signing” obviously removes the “handwritten” aspect of the signature, but it doesn’t change the nature of the signature—the “electronic” signature is still a signature if made with the intent of being one.It’s possible that the computer routine that captures the “e-signature” would reject the “signature” if the character were changed. That’s happened to me already when I made a typo in the little box for it. But that’s a matter of programming, not law.The long and the short of it is this is that the variation would be considered in light of the totality of the evidence. It would likely be considered inconsequential by a court considering the issue as long as corroborating evidence such as a consistent IP address and time of submission make it seem more likely than not that the person who typed the name into the box was the same person who was supposed to be signing. Conversely to challenge the signature on this basis, you’d likely need more than just a minor variation in form but the possibility of a plausible explanation involving impersonation or fraud.
-
How can I determine if I am being snooped on my PC? How can I inspect the network packets leaving my laptop for snooping activit
I love John's answer, it's blunt and to the point, and it's the right answer. Take action on a layer that people using electrons can't; block the view of the camera lens that you are concerned about. I'd also suggest turning off your microphone, and unloading the driver that handles that peripheral in your operating system, if you don't use it. Nowadays, most people do though, so think wisely about what part of your computer was necessary for you to purchase it. Now to my answer:The answer depends on your proficiency with Information Technology, specifically your understanding of Operating System, Application, and Network concepts and commercial and Open Source products. The short answer is, "it depends."The long answer is that if you have a record of activity that existed prior to your suspicions (we call that a baseline), you can compare what existed before to what exists now in access, security, and application logs. You can compare baseline network traffic patterns with current patterns.Another method you can use is to look at the files that have been changed, accessed, or created since you became suspicious. There are a lot of potential events related to this activity, and you should understand which events are related to normal activity and which events are not.You should determine what level of security controls you currently have in your IT environment, including detective controls such as IDS, corrective controls such as backups of your data and applications (or entire computer), and preventative controls such as Anti-virus and password complexity and variance among the services you have signed up for (NEVER REUSE PASSWORDS).Now, if you want to get into the weeds and start staring at every single packet of data that transits your home (or corporate) network environment, you'd better have some good tools. There are some great tools that are freely available, including:SnortWiresharkSecurity OnionSuricata…and the list goes on an on. My advice is only use a tool that you know how to use, and either pay for someone else to use advanced tools they understand, or learn how to use them yourself. Don't freak out over results from a tool you have never used before, investigate how it occurred, and determine it's significance.Hope this helps!-Jason
-
How do I register a startup in India? How much money and time does it take? If am currently only 17, what issues will I face dur
Algorithm for starting a Private Limited Company: Engineer's View Personally I believe, If someone is starting a company with long term perspective or to bring some change through their unique Product/Services, one must go for Private limited firm. Prime reason for this is easy to raise funds from Angels/VC in case you go for investment. Step 1. Registration of Company 1. Name Selection: Check whether your desired company name is available or not at MCA website [ http://www.mca.gov.in/ ]. Name must be unique & must resemble with business you intend to do (highlighted one). EX: Arihant Labs Retail Services Pvt. Ltd 2. Registration of Name at ROC: Name approval usually takes maximum of 14 days. This is done online through MCA website. Moreover, you need to apply with at least 4 names for approval with a writeup about significance of names with main business of the company. 3. 1. Documents Required: 2. 1. Options for names for the proposed Company (on the basis of preference) 2. Amount of Share Capital; proposed shareholding ratio 3. A paragraph on the proposed major line of business of the company (main objects) 4. City of Registered Office. 5. Copy of ownership deed/sale deed(if property is owned) 6. Copy of rent agreement with NOC (if property is rented) 7. Copy of latest electricity bill/telephone bill/mobile bill for both directors 8. Copy of latest electric bill/telephone bill for the registered office proof. 4. Obtaining DIN & DSC: 5. 1. Documents Required 2. 1. PAN Card copies for directors and shareholders. 2. Voter ID/Passport/Driving License for directors and shareholders. 3. Occupation of the Directors for directors and shareholders. 4. E-Mail IDs of all directors and shareholders. 5. Phone Numbers for all directors and shareholders. 6. Photos for directors and shareholders 6. Company Incorporation: After above mentioned formalities have been completed, we need to file following forms/docs in Rs 100 stamp paper: 7. 1. Affidavits for non- acceptance 2. INC 9, INC 10 3. DIR 2 4. NOC : This is required to be filed by the owner of the property on which your company will be situated. 5. Subscriber Sheets of MOA & AOA 6. Documents required for filling MOA & AOA 7. 1. Must be filled on OWN handwriting 2. Passport size photos 3. Sheets needs to be witnessed by CA/CS/Advocate Step 2. Obtaining PAN/TAN: After company gets incorporated, you may apply for PAN/TAN. Step 3. Trade Licence in case you are selling PRODUCTS: This is required in some places for carrying out sales. You can obtain this from local Municipality. Step 4. VAT/CST registration for selling Products: For selling intra-state, you need VAT registration & for selling inter-state, you need to register for CST. 1. Documents Required: 2. 1. Trade Licence 2. Company Incorporation Certificate 3. PAN card of company as well as of all the directors 4. Proof of residence of Directors 5. Proof of occupancy of place of business (Rent agreement/ ownership deed, Rent Bills etc) 6. MOA & AOA of company 7. Current Account in the name of company in any national bank Step 5. Service tax registration for Service Industry: In India, you need to pay service tax of 14.5% on every services you have charged customer for. 1. Documents Required: 2. 1. Company Incorporation Certificate 2. PAN card of company as well as of all the directors 3. Proof of residence of Directors 4. Proof of occupancy of place of business (Rent agreement/ ownership deed, Rent Bills etc) 5. MOA & AOA of company 6. Current Account in the name of company in any national bank That's All folks! Your STARTUP is up to Conquer the World. UPVOTE & SHARE your views/issues We at labkafe [ http://labkafe.com/ ], prefer taxmantra [ http://taxmantra.com/ ] for our legal requirements.
-
As a computer science student, what can I learn right now in just 10 minutes that could be useful for the rest of my life?
Have you ever felt that something(like taking backup of files, deleting old files etc.) should automatically happen when you connect your pen-drive to your system?Let us take an example, Suppose your teacher wants you to copy your assignments into his pendrive in front of him. The pen drive contains your final examination paper. You want your ubuntu system to automatically copy all the data from that pen drive to your hard disk automatically in the background (without even opening a copy dialogue). Here is how to do it on ubuntu:1] First let us write a simple shell script which we want to execute whenever a pen drive is connected to our system. Let us write a simple script which copies all data from the connected device to your home directory.First open a new fileemacs $HOME/script.shand add following lines to that file.#!/bin/bash sudo mkdir -p /tmp/test sudo mkdir -p $HOME/device_data sudo mount /dev/sdb1 /tmp/test sudo cp -r /tmp/test/* $HOME/device_data/ sudo umount /tmp/test Save and close the file.This script essentially creates a new directory named "device_data" inside your home folder and copies all the data from the pen drive into device_data directory.(Note: You can write ANYHTING into this script, so use it wisely :P)Now let us make this script executable.sudo chmod +x $HOME/script.sh As this script needs sudo permissions, we need to make it sudo runnable. To do this add the name of the script into sudoers file.Open sudoers file.sudo visudo -f /etc/sudoers Now after the 25th line (%sudo…) add this line
ALL=(ALL) NOPASSWD: /home/ /script.sh So now this script will run with sudo rights but will not ask for password! :)2]Now we need to tell our system to follow OUR rules (i.e execute our script) whenever a pendrive is connected. For this we need to create our own "udev rules" file. This file should be created in '/etc/udev/rules.d' directory.cd /etc/udev/rules.d Open a new file (with sudo rights):sudo emacs 91-myrules.rules Make sure the file name starts with "91". This gives your rules priority over other rules.Now add these lines into that fileACTION=="add", ATTRS{idVendor}=="****", ATTRS{idProduct}=="****", RUN+="/paht/to/your/script.sh" Make sure you enter proper path into RUN variable.Done!!Now plug any pendrive into your system and test this!Note: 1] When you connect your external drive this script will be run and your system won’t be able to use it unless this script execution is complete! So have some patience! :p 2] This answer is written for educational purposes only! Do not misuse it.Thanks Mehak Sharma for promoting the answer! -
Since many schools have stopped teaching cursive, will signatures not be used in the future?
The people who are deciding educational curriculum are short sighted enough to think so. But it’s not just about writing one’s name. Not knowing cursive means they cant read it either. Which means they won’t be able to read historic documents. Future generations will be unable to access the original Declaration if Independence and US Constitution and Bill of Rights because they are in ‘cursive’. It’s like returning to the middle ages when the Catholic clergy were the only ones literate enough to read the Christian bible. The masses had to rely on them to tell them what was in the bible. And now the future masses are going to have to rely on the literate minority once again.Its a huge step backward socially and intellectually, isn’t it?Because future generations will in majority be beholden to the minority if their homeschooled and private schooled peers who are still being taught to do cursive. The argument is that writing isn’t necessary because everyone types now.But what happens if the electric grid goes down? What happens if electronics are sabotaged or cease to work?Typing is impossible and no one can write. The world is in trouble.
-
Has there ever been a clear scientific link between tobacco and cancer? If so, then what is it?
How do scientists or doctors demonstrate that A causes B?The ideal experiment would be to take a large sample of healthy people, randomly assign half to use tobacco and half to abstain, then track the results a few decades later to find out whether the tobacco-using group had higher cancer rates than the control group. This is a randomized controlled trial, the gold standard in evidence-based medicine[1]. For ethical reasons, this is clearly unfeasible.We cando this experiment on non-human animals (animal experiments).do this experiment on human cells in a dish (in vitro experiments).study cancer rates in people who do and do not smoke, and in people who are and are not exposed to smokers; typically, a non-smoking spouse (cohort studies).If smoking caused cancer, we might also look for a dose-response relationship between risk and amount/duration of smoking, and a reduction of risk after cessation.study smoking rates in people with and without cancer (case-control studies).Each experiment or study alone may be subject to imperfect sampling or experimental variability, which is why it is so important to control for possible confounding factors like age, income, race, and geographic location, as well as to combine all of these studies into large meta-analyses.Therefore, “a clear scientific link” is not nearly as useful or definitive as what currently exists: a large body of multiple clear scientific links all pointing to the same conclusion.Each of these aspects of the scientific link between tobacco and cancer have been rather exhaustively studied — here are very thorough IARC monographs providing a collection of many, many studies in humans and animals concerning smoking and secondhand smoke,[2] as well as smokeless tobacco[3]and other tobacco products[4]. Here is just one table of studies:What happens when politics and money get involved? Learning about the history of tobacco “science” has made me both more skeptical of individual scientists and more confident in the scientific community as a whole. An industry can’t buy everyone, and scientists are motivated by more than money. The facts will come out in a society that supports science.As evidence mounted, tobacco companies had to restrict their emphasis to varying nuances of “causation” and criticizing individual studies, eventually producing such interesting documents as this internal memo from Philip Morris in 2000.In case you do not find the scientific studies convincing, consider the fact that even the tobacco industry admits the overwhelming consensus causally linking tobacco and cancer.[5]Their current focus is no longer on denying the link between tobacco and cancer, but on searching for “the responsible agents in smoking [and] their mechanism of action”. They would, of course, like to sell tobacco products with those agents removed, and/or suggest that “gaps in the scientific knowledge” mean that these modified tobacco products should not be regulated. (Let’s see what happens to e-cigarette users in the next few years).Focusing on the specific chemicals involved will be much more complex because so many compounds, and so many known carcinogens, are found in tobacco products, even the smokeless ones. Particularly abundant are some of the tobacco-specific nitrosamines, NNN and NNK, which are known group 1 carcinogens[6]. Setting the tobacco on fire generates even more, different carcinogens.Some interesting new computational techniques use DNA sequencing to analyze mutational signatures of different carcinogens. This involves taking cancer patient samples and analyzing all of the somatic mutations in the cancer genome. It turns out that different causes of mutation produce different “signature” mutation profiles of DNA bases. Tobacco smoke is associated with cysteine to adenine mutations, with some to guanine and thymine, a complex signature resulting from the additive effects of multiple carcinogens[7].This is what would be expected from what has been shown in human studies: tobacco smoke causes mutations in DNA, some of which can give rise to cancer.Footnotes[1] Evidence-based medicine - Wikipedia[2] IARC Monographs- Monographs available in PDF format[3] http://monographs.iarc.fr/ENG/Mo...[4] http://monographs.iarc.fr/ENG/Mo...[5] Industry Documents Library[6] http://monographs.iarc.fr/ENG/Mo...[7] Mutation signatures of carcinogen exposure: genome-wide detection and new opportunities for cancer prevention
-
What are the cyber security laws that everyone must know?
According to Information Technology Act 2000(IT Act 2000) and its Amendment here are some of the list of law :OFFENCES:65. Tampering with computer source documents.Whoever knowingly or intentionally conceals, destroys or alters or intentionally or knowingly causes another to conceal, destroy, or alter any computer Source code used for a computer, computer programme, computer system or computer network, when the computer source code is required to be kept or maintained by law for the time being in force, shall be punishable with imprisonment up to three years, or with fine which may extend up to two lakh rupees, or with both.Explanation.–For the purposes of this section, “computer source code” means the listing of programmes, computer commands, design and layout and programme analysis of computer resource in any form.66. Computer related offences.–If any person, dishonestly or fraudulently, does any act referred to in section 43, he shall be punishable with imprisonment for a term which may extend to three years or with fine which may extend to five lakh rupees or with both.Explanation.–For the purposes of this section,–(a) the word “dishonestly” shall have the meaning assigned to it in section 24 of the Indian Penal Code (45 of 1860)(b) the word “fraudulently” shall have the meaning assigned to it in section 25 of the Indian Penal Code (45 of 1860).66A. Punishment for sending offensive messages through communication service, etc.–Any person who sends, by means of a computer resource or a communication device,–(a) any information that is grossly offensive or has menacing character; or(b) any information which he knows to be false, but for the purpose of causing annoyance, inconvenience, danger, obstruction, insult, injury, criminal intimidation, enmity, hatred or ill will, persistently by making use of such computer resource or a communication device;(c) any electronic mail or electronic mail message for the purpose of causing annoyance or inconvenience or to deceive or to mislead the addressee or recipient about the origin of such messages,shall be punishable with imprisonment for a term which may extend to three years and with fine.Explanation.–For the purpose of this section, terms “electronic mail” and “electronic mail message”means a message or information created or transmitted or received on a computer, computer system,computer resource or communication device including attachments in text, images, audio, video and anyother electronic record, which may be transmitted with the message.66B. Punishment for dishonestly receiving stolen computer resource or communication device.–Whoever dishonestly received or retains any stolen computer resource or communication device knowingor having reason to believe the same to be stolen computer resource or communication device,shall be punished with imprisonment of either description for a term which may extend to three years or with fine which may extend to rupees one lakh or with both.66C. Punishment for identity theft.–Whoever, fraudulently or dishonestly make use of theelectronic signature, password or any other unique identification feature of any other person,shall be punished with imprisonment of either description for a term which may extend to three years andshall also be liable to fine which may extend to rupees one lakh.66D. Punishment for cheating by personation by using computer resource.–Whoever, by meansof any communication device or computer resource cheats by personating, shall be punished withimprisonment of either description for a term which may extend to three years and shall also be liable tofine which may extend to one lakh rupees.66E. Punishment for violation of privacy.–Whoever, intentionally or knowingly captures, publishesor transmits the image of a private area of any person without his or her consent, under circumstancesviolating the privacy of that person, shall be punished with imprisonment which may extend to three yearsor with fine not exceeding two lakh rupees, or with both.Explanation.–For the purposes of this section–(a) “transmit” means to electronically send a visual image with the intent that it be viewed by a person or persons;(b) “capture”, with respect to an image, means to videotape, photograph, film or record by any means;(c) “private area” means the naked or undergarment clad genitals, public area, buttocks or female breast:(d) “publishes” means reproduction in the printed or electronic form and making it available for public;(e) “under circumstances violating privacy” means circumstances in which a person can have a reasonable expectation that–(i) he or she could disrobe in privacy, without being concerned that an image of his private area was being captured; or(ii) any part of his or her private area would not be visible to the public, regardless of whetherthat person is in a public or private place.67. Punishment for publishing or transmitting obscene material in electronic form.–Whoever publishes or transmits or causes to be published or transmitted in the electronic form, any material whichis lascivious or appeals to the prurient interest or if its effect is such as to tend to deprave and corruptpersons who are likely, having regard to all relevant circumstances, to read, see or hear the matter contained or embodied in it, shall be punished on first conviction with imprisonment of either descriptionfor a term which may extend to three years and with fine which may extend to five lakh rupees and in theevent of second or subsequent conviction with imprisonment of either description for a term which mayextend to five years and also with fine which may extend to ten lakh rupees.67A. Punishment for publishing or transmitting of material containing sexually explicit act, etc., in electronic form.–Whoever publishes or transmits or causes to be published or transmitted in theelectronic form any material which contains sexually explicit act or conduct shall be punished on firstconviction with imprisonment of either description for a term which may extend to five years and withfine which may extend to ten lakh rupees and in the event of second or subsequent conviction withimprisonment of either description for a term which may extend to seven years and also with fine whichmay extend to ten lakh rupees.67B. Punishment for publishing or transmitting of material depicting children in sexually explicit act, etc., in electronic form.–Whoever,–(a) publishes or transmits or causes to be published or transmitted material in any electronic formwhich depicts children engaged in sexually explicit act or conduct; or(b) creates text or digital images, collects, seeks, browses, downloads, advertises, promotes,exchanges or distributes material in any electronic form depicting children in obscene or indecent or sexually explicit manner;or(c) cultivates, entices or induces children to online relationship with one or more children for and on sexually explicit act or in a manner that may offend a reasonable adult on the computer resource;or(d) facilitates abusing children online, or(e) records in any electronic form own abuse or that of others pertaining to sexually explicit actwith children,shall be punished on first conviction with imprisonment of either description for a term which may extendto five years and with fine which may extend to ten lakh rupees and in the event of second or subsequentconviction with imprisonment of either description for a term which may extend to seven years and also with fine which may extend to ten lakh rupees:Provided that provisions of section 67, section 67A and this section does not extend to any book,pamphlet, paper, writing, drawing, painting representation or figure in electronic form–(i) the publication of which is proved to be justified as being for the public good on theground that such book, pamphlet, paper, writing, drawing, painting representation or figure is theinterest of science, literature, art or learning or other objects of general concern; or(ii) which is kept or used for bonafide heritage or religious purposes.Explanation–For the purposes of this section, “children” means a person who has not completedthe age of 18 years.80. Power of police officer and other officers to enter, search, etc.–(1) Notwithstanding anythingcontained in the Code of Criminal Procedure, 1973 (2 of 1974), any police officer, not below the rank of a1[Inspector], or any other officer of the Central Government or a State Government authorised by theCentral Government in this behalf may enter any public place and search and arrest without warrant anyperson found therein who is reasonably suspected of having committed or of committing or of beingabout to commit any offence under this Act.Explanation.–For the purposes of this sub-section, the expression “public place” includes any publicconveyance, any hotel, any shop or any other place intended for use by, or accessible to the public.(2) Where any person is arrested under sub-section (1) by an officer other than a police officer, suchofficer shall, without unnecessary delay, take or send the person arrested before a magistrate havingjurisdiction in the case or before the officer-in-charge of a police station.(3) The provisions of the Code of Criminal Procedure, 1973 (2 of 1974) shall, subject to theprovisions of this section, apply, so far as may be, in relation to any entry, search or arrest, made underthis section.85. Offences by companies.–(1) Where a person committing a contravention of any of the provisionsof this Act or of any rule, direction or order made there under is a company, every person who, at the timethe contravention was committed, was in charge of, and was responsible to, the company for the conductof business of the company as well as the company, shall be guilty of the contravention and shall be liableto be proceeded against and punished accordingly:Provided that nothing contained in this sub-section shall render any such person liable to punishmentif he proves that the contravention took place without his knowledge or that he exercised all due diligenceto prevent such contravention.(2) Not with standing anything contained in sub-section (1), where a contravention of any of the provisions of this Act or of any rule, direction or order made thereunder has been committed by acompany and it is proved that the contravention has taken place with the consent or connivance of, or isattributable to any neglect on the part of, any director, manager, secretary or other officer of the company,
Trusted esignature solution— what our customers are saying
Get legally-binding signatures now!
Related searches to Remove eSignature Document Computer
Frequently asked questions
How do i add an electronic signature to a word document?
How to esign a filable pdf file?
Who can sign documents for a company?
Get more for Remove eSignature Document Computer
- Can I Electronic signature Kansas Real Estate PPT
- How Do I Electronic signature Kansas Real Estate PPT
- How Can I Electronic signature Kansas Real Estate PPT
- Help Me With Electronic signature Kansas Real Estate PPT
- Can I Electronic signature Kansas Real Estate PPT
- How To Electronic signature Kansas Real Estate PPT
- How To Electronic signature Kansas Real Estate PPT
- How Do I Electronic signature Kansas Real Estate PPT
Find out other Remove eSignature Document Computer
- Ansi tpi inspection forms
- Annual learning plan alp form
- Tata aig claim form 40915436
- Certificate of liability insurance ampamp form
- Sutton bank hsa form
- Fcps calendar form
- Vtg59 form
- 48830 ngoe form
- Import permit application ministry of agriculture of barbados form
- Utah contractor license form
- Histocompatibility lab testing requisition form university of utah healthcare utah
- Ldss 4281 form
- Illinois statutory short form power of attorney for property mwrdrf
- Cincinnati bar association notary form
- California department of education child development division form cd 9605
- App 003 fillable form
- Anf 2d dgft form
- Ftc sem 17b 2 109 foreign national request for access alertconference form
- Slavery and sectionalism worksheet answers form
- Modbus over serial line specification and implementation guide v1 02 form