Remove eSignature Presentation Later
Make the most out of your eSignature workflows with airSlate SignNow
Extensive suite of eSignature tools
Robust integration and API capabilities
Advanced security and compliance
Various collaboration tools
Enjoyable and stress-free signing experience
Extensive support
How To Use eSignature in ERP
Keep your eSignature workflows on track
Our user reviews speak for themselves






Remove eSignature Presentation Later. Explore by far the most consumer-warm and friendly exposure to airSlate SignNow. Handle all of your record digesting and expressing method electronically. Range from portable, papers-based and erroneous workflows to computerized, electronic digital and perfect. It is simple to create, produce and signal any documents on any product anyplace. Make sure that your crucial enterprise situations don't move overboard.
Learn how to Remove eSignature Presentation Later. Keep to the straightforward information to begin:
- Design your airSlate SignNow account in click throughs or sign in along with your Facebook or Google accounts.
- Enjoy the 30-working day trial offer or pick a pricing plan that's perfect for you.
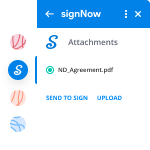
- Discover any authorized web template, build on the web fillable types and talk about them tightly.
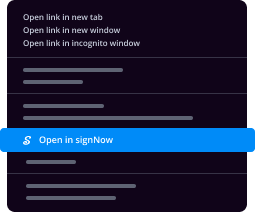
- Use sophisticated features to Remove eSignature Presentation Later.
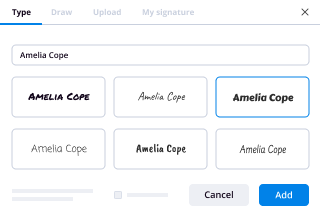
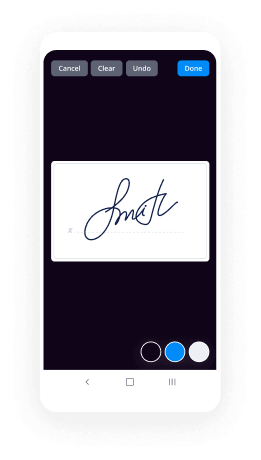
- Indicator, personalize putting your signature on purchase and gather in-individual signatures ten times more quickly.
- Establish automatic reminders and receive notifications at each and every phase.
Shifting your tasks into airSlate SignNow is uncomplicated. What adheres to is a simple procedure to Remove eSignature Presentation Later, in addition to recommendations to maintain your peers and partners for greater partnership. Inspire your workers using the finest resources to keep in addition to enterprise functions. Enhance output and size your company more quickly.
How it works
Rate your experience
-
Best ROI. Our customers achieve an average 7x ROI within the first six months.
-
Scales with your use cases. From SMBs to mid-market, airSlate SignNow delivers results for businesses of all sizes.
-
Intuitive UI and API. Sign and send documents from your apps in minutes.
A smarter way to work: —how to industry sign banking integrate
FAQs
-
How stealthy is a Arleigh Burke destroyer?
Thanks for the ATA! I served on 2 Burke Class DDGs.Burke Class DDGs employ several RCS or ‘Radar Cross Section’ reduction methods.First and foremost is that the hull and more especially the superstructure employ shaping techniques to present angles that will bounce or scatter radar return.Placement of equipment on deck is limited or able to be hidden/enclosed. The mast is angled, enclosed and made of aluminum. The 5 inch gun has been modified on later ships to include a reduced RCS turret.Equipment that cannot be placed elsewhere or hidden has special covers made of radar absorbent material. Similarly parts of the superstructure and any infrastructure that cannot be angled use RAM tile. Any of the RAM areas as well as identified hot spots are coated with special RAM paint. For instance the exhaust pipes are painted with a paint similar to what was used on the F117. Later ships removed the exhaust pipes altogether. Collectively these systems are called PCMS or Passive Counter Measures System.The result is a RCS that is about 70 percent smaller than the ships actual size depending up the platform trying to detect it.Aside from RCS reduction an area that is as important is ‘Emissions Control’. You can hide from radar completely and it will not help a bit if your electronic signature gives you away. The Burke Class excels at controlling emissions. Phased Array SPY-1 radars have a virtuous ability to control emissions by being able to digitally dial its echo, meaning the radar doesnt just use max energy all the time like an easily visible spotlight shooting up into a night sky. Burke can turn its radar off altogether and rely on its own electronic sniffing ECM sensors or through Cooperative Engagement and Tactical Databanks use other platforms sensors to get a picture. For example an E-2D Hawkeye is airborne, it can link with the Burke and now the Burke can see what it sees. Burke can even launch weapons using another platforms sensor picture.
-
How are cracked versions of software created and why are developers not able to prevent it?
Cracked versions of software are created with the use of debuggers. (A debugger is a special type of software that lets programmers deconstruct their software into its constituent parts for the purpose of finding bugs, and thus de-bugging. Additionally debuggers can be used for reverse-engineering, or to see what is inside the software, to learn its logic. The latter method is used mostly by malware researchers to study what malware (or computer viruses) do on-the-inside. But it can be also used by an attacker to "crack" (or bypass) legal software registration, or at times, to alter normal behavior of software, for instance by injecting a malicious code into it.)For the sake of this example, I will assume that the software that is being "cracked" was compiled into a native code, and is not a .NET or a JavaScript based application. (Otherwise it will be somewhat trivial to view its source code.) The compiled native code is a bit more tricky "beast" to study. (Native means that the code executes directly by the CPU, GPU, or other hardware.)So let's assume that the goal of an attacker is to bypass the registration logic in the software so that he or she doesn't have to pay for it. (Later for lolz, he or she may also post such "crack" on some shady online forum or on a torrent site so that others can "use" it too and give him or her their appreciation.)For simplicity let's assume that the original logic that was checking for the software registration was written in C++ and was something similar to the following code snippet:In this code sample "RegistrationName" and "RegistrationCode" are special strings of text that a legitimate software user will receive after paying for the license. (The name is usually that person's actual name or their email address, and the code is some string of unique/special characters that is tied to the name.)In the logic above, the function named "isRegistrationCodeGood()" will check if "RegistrationName" and "RegistrationCode" are accepted using some proprietary method. If they are, it will return true. Otherwise false. That outcode will dictate which branch (or scope) the execution will follow.So the logic above will either show that registration failed and quit:Or, if the registration code and name matched, it will save the registration details in persistent storage (such as the File System or System Registry) using the function named "rememberRegistrationParameters()" and then display the message thanking the user for registering:A "cracker" will obviously want to achieve the second result for any registration code that he or she enters. But they have a problem. They do not have the C++ source code, part of which I showed above. (I hope not!)So the only recourse for an attacker is to disassemble the binary code (that always ships with software in the form of .exe and .dll files on Windows, and mostly as Unix executables inside the .app packages on a Mac.) An attacker will then use a debugger to study the binary code and try to locate the registration logic that I singled out above.Next you can see the flowchart for a snippet of code that I showed in C++, presented via a low-level debugger. Or, as the code will be read in the binary form after compilation:(For readability I added comments on the right with the names of functions and variables. They will not be present in the code that an attacker could see.)(To understand what is shown above an attacker will have to have good knowledge of the Assembly language instructions for the native code.)I also need to point out that having a disassembly snippet like the one above is the final result for an attacker. The main difficulty for him or her is to locate it among millions and millions of other similar lines of code. And that is their main challenge. Not many people can do it and that is why software "cracking" is a special skill.So having found the code snippet above in the software binary file a "cracker" has two choices:1) Modify (or patch) the binary.2) Reverse-engineer the "isRegistrationCodeGood()" function and copy its logic to create what is known as a "KeyGen" or "Key Generator."Let's review both:The first choice is quite straightforward. Since an attacker got this far, he or she knows the Intel x64 Instruction Set quite well. So they simply change the conditional jump from "jnz short loc_7FF645671430" at the address 00007FF645671418 (circled in red in the screenshots) to unconditional jump, or "jmp short loc_7FF645671430". This will effectively remove any failed registration code entries and anything that the user types in will be accepted as a valid registration.Also note that this modification can be achieved by changing just one byte in the binary code from 0x75 to 0xEB:But this approach comes with a "price" of modifying the original binary file. For that an attacker needs to write his own "patcher" (or a small executable that will apply the modification that I described above.) The downside of this approach for an attacker is that patching an original executable file will break its digital signature, which may alert the end-user or the vendor. Additionally the "patcher" executable made by an attacker can be easily flagged and blocked by the end-user's antivirus software, or lead criminal investigators to the identity of the attacker.The second choice is a little bit more tricky. An attacker will have to study "isRegistrationCodeGood()" function and copy it into his own small program that will effectively duplicate the logic implemented in the original software and let him generate the registration code from any name, thus giving any unscrupulous user of that software an ability to register it without making a payment.Vendors of many major software products understand the potential impact of the second method and try to prevent it by requiring what is known as "authentication." This is basically a second step after registration, where the software submits registration name to the company's web server that returns a response back to the software of whether the code was legitimate or not. This is done by Microsoft when you purchase Windows (they call it "Activate Windows") and also by signNow, and many other companies. This second step may be done behind-the-scenes on the background while the software is running, and will usually lead to cancellation of prior registration if it was obtained illegally.So now you know how software is "cracked".Let me answer why it is not possible to prevent it. It all boils down to the fact that any software code needs to be read either by CPU (in case of a binary native code) or by an interpreter or a JIT compiler (in case of JavaScript or .NET code.) This means that if there's a way to read/interpret something, no matter how complex or convoluted it is, an attacker with enough knowledge and persistence will be able to read it as well, and thus break it.There is an argument though that cloud-based software is more secure, which is true, since its (binary) code remains on the server and end-users do not have direct access to it. And even though cloud-based software is definitely the future, it has some major drawbacks that will never allow it to fully replace your conventional software. To name just a few:Not everyone has an internet connection, or is willing to upload their data online. Additionally someone’s internet connection can be very expensive or too slow to make the software run very laggy.Then there’s a question of distributed computing. For instance, Blizzard Entertainment would never make “World of Warcraft” to fully run on their servers due to immense computational resources needed to render every single scene for every player they have. Thus it is in their best interest to let each individual user’s computer to do the rendering instead.As a software developer myself, I obviously don't like when people steal software licenses. But I have to accept it and live with it. The good news is that there are not that many people who are willing to go extra mile and search for a cracked version of software. The main problem for those who do, is that by downloading a patched executable, or an attacker's KeyGen or a Patcher, they are effectively "trusting" him or her not to put anything "nasty" into it that was not "advertised on the package" (stuff like trojans, malware, or keyloggers.) So the question for those people becomes -- is it worth the cost of the software license to potentially infect your system with a nasty virus?On the other side of the equation, some developers react very negatively to any attempts to steal their software licenses. (I was there too.) They try to implement all kinds of countermeasures -- anything from tricking reverse-engineers, to adding booby traps in the code that may do something nasty if the code detects that it is being debugged, to obfuscating or scrambling the code, to enforcing all kinds of convoluted DRM schemes, to blocking users from certain countries. I personally try to stay away from all of those measures. And here's why:A) Any kind of anti-reverse-engineering tactics could be bypassed by an attacker with enough persistence. So why bother and waste my time when I can invest that time into adding something useful to my software that will make it more productive for legitimate users?B) Some code packers could create false positives with antivirus software, which is obviously not good for marketing of that software. It also creates unnecessary complexity for the developer to debug the software.C) Adding booby traps in the code can also “misfire” on your legitimate users, which will really infuriate them and can even lead to lawsuits.D) Any DRM scheme will probably catch some 100 illegal users and greatly inconvenience 10,000 legitimate ones. So why do it to your good customers?E) Our statistics show that about 75% of all illegal licenses come from China, Russia, Brazil, to name the worst offenders. (I also understand that the reason may be much lower incomes that people have in those countries.) The main issue for us though was the fact that if we enforce our DRM or add some strong registration authentication, many people that wanted to bypass our registration would simply use a stolen credit card number. And we had no control over it. Our system will use it to send them a legitimate license only to have the payment bounce in weeks time. As a result we would lose the money that were paid for the license, plus the credit card company will impose an additional chargeback fee to our account, which may range from $0.25 to $20 per bad purchase on top of the license cost.F) As was pointed out in the comments, some companies may actually benefit from allowing pirated copies of their software. Microsoft for instance gets a lot of free publicity from people using their Windows OS, the same goes for signNow with their Photoshop. That is a good point that I agree with.So my philosophy is now this -- if someone wants to go extra mile and steal our software, go for it! They went this far to do it anyway, so they probably have a good reason. On the positive side there are so many other customers that appreciate the work that goes into creating software that greatly outnumber those that don’t.PS. Thank you for all your feedback! It makes me feel good that the knowledge I shared is useful to others.
-
What do pro-choicers think of third-trimester abortions?
First, the child has a “head and limbs and everything” much, much earlier than the third trimester.So if the criteria is that a fetus with “a head and limbs and everything” should not be aborted, the period of time when abortion is okay would have to be before 8 or 9 weeks or even earlier, depending on your perception of what constitutes a “head and limbs”. The little buds and the little webbed looking hands are seen by 8 weeks, along with the large (seemingly) misshapen head that will envelope the amazing human brain.I personally believe that the fetus is not conscious until around the 24th week of pregnancy. (I came up with this general time frame from reading about neurology, consciousness, and fetal development; a complex topic that I won’t detail here.) I don’t believe the fetus feels pain when aborted before about the 22nd week. Although it is heart-wrenching to watch images of the fetus (reflexively) attempting to escape abortionist tools. They jerk and pull away, as all living things seek to preserve their lives.However, as I said elsewhere, that to me being unconscious does not mean a living being does not have rights. I recently had surgery and was unconscious for the procedure. I could have been terminated and not felt it or known about it, but that wouldn’t have made it morally right.Very few abortions are done in the third trimester. Few doctors will do them. When they do occur it is often because the fetus is so seriously deformed and would not survive the birth process anyway. (But since your question is about having a head and limbs, we needn’t stick to the last trimester in our discussion.)Abortion is not legal throughout all three trimesters in most states. Many states have limits of between 20 to 24 weeks, some even earlier. But even at 12 weeks, yes, there is a very human-looking being with a little head, arms and legs and visible, although still ambiguous, genitals.I don’t know what “pro-choice” people think about very late abortions. Some may have an arbitrary timeline in their own mind as towhen the baby is too human to deprive of its life, and others follow the “gospel of choice”. The gospel of choice is that any and all rights an unborn person has are null and void because the rights of the mother trump them. Once the infant is born and takes a breath, then and only then can humanity be ascribed to them. Here is an interesting video in which a (former) fetus speaks of surviving an abortion attempt:I must say, I am suspicious of your claim to be pro-choice. Forgive me if I am incorrect in my suspicions. Frequently, posters on this forum will pose as pro-choice and ask innocent questions meant to provoke the discussion on Quora. It is futile to try to dissuade most pro-choicers with these ethics questions.Of interest, there are many former pro-choice warriors who have struggled with the issue and have jumped the fence. Notable is Dr. Bernard Nathanson, the abortionist who may have done more than anyone else to make abortion legal as one of the key figures in the work of the National Association for the Repeal of Abortion Laws. (NARAL) . His turnaround was so radical that he went from an atheist to a Catholic and spent his remaining years fighting abortion. I have not been able to find online recently his breathless deathbed plea for unborn life, but this obituary provides his perspective. B. N. Nathanson, 84, Dies; Changed Sides on AbortionOther well-known figures include the “Roe” of “Roe versus Wade”’ Norma McCorvey, who changed her mind and spent decades as a prolife activist Norma McCorvey on becoming pro-life (1998) - CNN Videoand Abby Johnson, the former director of a Planned Parenthood. AbortionWorkerOf course, these mind-changes have no effect on discussion with true-believing pro-choice people; such people are seen only as turncoats. If the “gospel of choice” community responds at all, it is usually in the form of attack or attempts to discredit those who have jumped the fence. For those who have a grain of doubt in their position, who are troubled by the fetal attempt to squirm away from a sharp tool, then perhaps the reasons these pro-choice icons became turncoats may be interesting. But they will not interest those who have no doubts.I will provide here links to two videos showing fetal life. One is a miscarriage, and the other is labelled as an abortion. I don’t believe the moving fetus is an abortion, despite the claims of the person who posted it. The medical personnel are speaking a language I don’t understand, but you can hear tones of sadness as they discuss the little fetus, and further the fetus is not damaged in anyway, so likely this is footage of a natural miscarriage. This is graphic, but not gory, it is merely a fetus moving a little bit as it dies because it cannot live outside the womb. This fetus is too young to try to breathe or have any pain or consciousness. I am estimating that it was born early in the second trimester. If you are sensitive, it may be too alarming to watch. I am sorry about the banner “Abortion is Murder” and so on. but this is the only video that shows the miscarriage of a fetus of this age that I can find. I don’t think all the “murder” talk and the accusations help the discussion. Anyway, this is not a third trimester baby by any stretch of the imagination. It is likely 14 to 16 weeks and yes, there is a head and legs.I want to also add that I don’t think that reversing the Supreme Court decision regarding the right of women to terminate their pregnancies will help anything at this point.I am more interested in being free to talk about human life with those who have doubts and to explore addressing the cultural effects of the legalization of abortion. For instance, there are movements such as Feminists for Life and other secular prolife movements who offer a different perspective from the religious dissenters and the “gospel of choice” movement. secularprolifeYes, the Supreme Court has spoken. But no law has been enacted that prevents thoughtful people from re-examining and conversing about the disquieting questions that the theme of abortion gives rise to.
-
What are the career options after graduating with a Bachelor's in physics?
There are actually Three things you can do after you ‘earn’ your Bachelor degree in Physics :Continue your studiesGet a Job , orGive a JobAllow me to explain each in detail -Continue your studies :-> Here you have several Options:a) Pursue Masters from IIT by cracking IITJAM or from any other university on Physics and earn a PHd later on. You can also do Integrated PHd by applying and getting a good rank in JEST , TIFR , IISER etc.b) Pursue your Masters from any IIT (or from any other University) and then pursue MTech by cracking GATE. After MTech you can get placed in some PSUs or some reputed MNCs. Many prefer higher studies though (like PHd after Mtech). (P.S - IIT Kharagpur provides Integrated Mtech-PHd for Computer Science and Data Analytics after qualifying in GATE)c) Give an entrance test conducted by few universities for Btech and get into some good Engineering Colleges. (Ex : Jadavpur University in Kolkata conducts an entrance test for students of BSc(Hons) Physics. Qualified Candidates enter into 2nd year of BTech. Likewise Calcutta University provides Btech in Radiophysics.)d) Do Bachelors in Education(BEd) for a Teaching Job.e) MSc on other subjects like Biophysics, RadioPhysics, Geophysics, Instrumentation etc. Ex - MScTech in Geophysics from ISM Dhanbad (Note : the degree mention MScTech not MTech; Both are different).f) Other Masters programme in other disciplines if you want to do it like MCA, MBA, MA, LLB etc. (Being interested in Defence Services, personally I would have preferred Masters from Institute of Defence Studies in Pune and PHd later on— a path very few know or like to tread .)g) If you have a Gap in years after your BSc Physics and possess the thought that you will be unable to share the class with the younger generation, feel free to pursue distance learning through IGNOU. You can pursue your masters on other subjects via IGNOU or sit for an entrance examination for MSc. Physics (distance learning) which by the way IGNOU conducts in collaboration with Indian Institute of Astrophysics (forms available in the month of september).h) You can also pursue higher studies from Foreign universities. Of course you have to crack the competitive exams related for that purpose.2. Get a Job :→ You can Apply for Various entrance examinations for Banks(RBI Grade B, SBI PO, IBPS etc), Railways( ASM, Goods Guard, JE, RPF SI etc) , PSUs or State Units(AAI ATC, Electricity Executives, Forest Guard etc), Armed Forces(AFCAT, CDSE, Coast Guard(only interview) ), Civil Services(UPSC CSE, State CSE, IFoS) and Central/State Police Services( SSC CAPF, UPSC CAPF, SSC CGL etc). Crack these Examinations and earn a respectable service with the Central or State Governments or Banking Sector or PSUs.(PS : If you have completed MSc Physics then you can apply in Indian Navy as an Officer or else not. Indian Navy does not recruit candidates having just BSc in Physics. You either should have BTech or do MSc Physics- the condition valid even in UPSC CDSE recruitment)→ If you want a job in your core field(subject), there are exams like ISRO Scientific Assistant, SSC IMD Scientific Assistant, BHAVINI Scientific Assistant, NCPOR Scientific Assistant(which do not conduct any exam but only Personal Interview), NPCIL Scientific Assistant etc. which too are Govt Organisations that requires Bachelor’s in Physics as a qualification.(PS- If you complete MSc in Physics however you can apply for a relatively higher position in similar organisations for the post of Scientific Officer - Some institutes like BARC donot recruit candidates having a degree less than that of MSc.)You know the craze for Government Jobs, Don’t you? Some Jobs are indeed Earned. :)→ However You can always find a Job in the Corporate Sector. Ex: TCS, WIPRO etc.So, All the very Best if getting a Job is your sole Aim.P.S - Build and Develop Skills via sites(also Android App) like Udemy, Coursera, edX, Skillshare, Codecademy etc. Trust me sometimes recruiters will be much interested if they learn that you have invested some quality time in having knowledge which can give you an edge over other candidates. Also makes your Resume look quite attractive. Moreover guess what, most courses are totally free of Cost. After Completing the Course if you wish to have the valid Certificate with a signature and stamp from reputed universities, you can pay them a certain fee. Totally ok if you dont pay as those digital certificates will not hold much value over regular courses;but do keep in mind the skill you learn can make you top notch over others.Personally I prefer to pay as a token of appreciation. Doesn’t seem much(approx 3k INR & sometimes even only 600 INR) if you consider the fact that the knowledge you receive is immense and magnificent.3. Give a Job :→ Well you know what I am going to say. The Word that became the centre of attention lately in India- ‘Entrepreneurship’.Take risks, try out new ways, give people a source of Income, earn Fortunes and build your own Empire. And the thing is you don’t even need a Bsc or Physics to be a great entrepreneur. You don’t need to work for anyone, You can always work for yourself.But yes to be brutally honest- as lovely as the situation might seem- you will most likely Fail in this venture. Dont get me wrong but what I am saying here is the ‘Reality’. However I haven’t seen or met Entrepreneurs who didnot fail and yet achieved big.Who knows You might become the next Zuckerburg or the next Elon Musk - which by the way if you dont know, Mr. Musk has done his Bachelors in Physics. ;)These are the three things which I feel you can do. The Interest and the Will rests on you and you alone. I hope I was able to remove all your doubts. Still if you have one, feel free to comment.By the way, Upvotes are Welcome. Thank you for the 177 upvotes. Means a lot.All the Best for your future.(>_<) ♡Edit- Thank you Quorans for my first 500 upvotes.
-
What caused the 1500 degree fires under the WTC rubble that burned for months after their collapses?
Edit. By the way, I just watched the “Impossible Builds” episode on the Scorpion Tower. It has an external array of support columns without internal ones. That’s the same general plan as the WTC. This means it should be subject to the same failure mode if a plane filled with fuel crashes into it. End of edit.The towers fell because the fires from paper and jet fuel were enough to make the cross braces slump not melt. I’ve seen that in neighborhood fires much less intense. So if this is about needed to melt steel for the towers to fall it’s a troll question.Scan your local news source for large local fires. This might be large apartment buildings totally destroyed by fire, medium sized stores or warehouses, even churches. Look where the sky is visible through the roof. What you’ll see is slumped steel beams. In a tower designed like the WTC that’s how the failure happened. Floor joint beams slumped to the point they separated from the exterior support columns. Once a fall started the momentum was enough to cause floors not yet burning to fail and fall.Once down there were vast amounts of combustibles plus lots of insulating material plus vast amounts of heat of kinetic energy from the fall plus the fact that it was well compressed enough to keep the air flow limited. That’s a perfect scenario for a fire that burns for a very long time and that stays at a temperature that low.Hotter and the heat melts more material, plugging the outgoing air flow. Cooler and the lack of heat opens cracks, increasing the outgoing airflow. Thus the underground fire was constantly limited by the outgoing airflow not by the incoming airflow. That’s why the fire was so cold.Being cold compared to a fire with a plentiful outgoing air flow, there was plenty of fuel to last for months. The duration of the fire was from the huge amount of combustibles combined with the limited outgoing airflow.
-
What are the valid facts in the NGT v/s Art of Living case?
This is height of hypocracy and believing themselves to be above law .What is the difference between ShriShri Ravishankar from the so called DABANGS of Bihar and UP who flout law openly and brazenly.Please do not start with comparison proving difference between the two.He is a renowned man with million of followers this hypocracy and behaviour puts him in a wrong colour and picture.If people like him are so brazen in not sticking to their commitments what kind of message does his act convey in general masses and his followers in particular.This is the difference between as real sadhu and teacher and a pseudo sadhu and teacher.The real teacher leads by example and put a very correct picture of himself to his followers.he is not a teacher and there is no difference between the people who indulge in crime but brazen it out and he who with his WCF raped the flood plains of Yamuna, promised to pay the nominal fine imposed by NGT on the eve of the festival and got approval on condition that the fine will be paid after the festival but has since refused to stick to his commitment.He is trying to be a states man by writing to ISIS and they joked about his naivety by sending him a picture of beheaded man.There are some question which should be asked :A. How does he know ISIS.B. Why did he corrosponded with them.C. Who or whose behalf did he write this letter.D. Did GOI appointed him as incoluter with ISIS .E. What is his standing among Arabs and supporters of ISIS .F. Is he looking for a active political role with GOI.G. Should not NIA question him on his relationships inside ISIS high command?H. On relationship with person to whom the letter was addressed?.I . If he wrote directly to Bagdadi and Bagdadi replied to him then it really becomes a case for thorough investigation by intelligence agencies across the globe because there is no intelligence available on Bagdai, his movements, and his place of stay and his permanent postal address.I. He should voluntarily cooperate with intelligence agencies and share details of Bagdadi it may help in eliminating Bagdadi.
-
If there is one thing this world is missing, what is it?
Origin of the Elements Approximately 73% of the mass of the visible universe is in the form of hydrogen. Helium makes up about 25% of the mass, and everything else represents only 2%. While the abundance of these more massive ("heavy", A > 4) elements seems quite low, it is important to remember that most of the atoms in our bodies and Earth are a part of this small portion of the matter of the universe. The low-mass elements, hydrogen and helium, were produced in the hot, dense conditions of the birth of the universe itself. The birth, life, and death of a star is described in terms of nuclear reactions. The chemical elements that make up the matter we observe throughout the universe were created in these reactions. Approximately 15 billion years ago the universe began as an extremely hot and dense region of radiant energy, the Big Bang. Immediately after its formation, it began to expand and cool. The radiant energy produced quark-antiquarks and electron-positrons, and other particle-antiparticle pairs. However, as the particles and antiparticles collided in the high energy gas, they would annihilate back into electromagnetic energy. As the universe expanded the average energy of the radiation became smaller. Particle creation and annihilation continued until the temperature cooled enough that pair creation became no longer energetically possible. One of the signatures of the Big Bang that persists today is the long-wavelength radiation that fills the universe. This is radiation left over from the original explosion. The present temperature of this "background" radiation is 2.7 K. (The temperature, T, of a gas or plasma and average particle kinetic energy, E, are related by the Boltzmann constant, k = 1.38 x 10-23J/K, in the equation E = kT.) Figure 10.1 shows the temperature at various stages in the time evolution of the universe from the quark-gluon plasma to the present time. At first quarks and electrons had only a fleeting existence as a plasma because the annihilation removed them as fast as they were created. As the universe cooled, the quarks condensed into nucleons. This process was similar to the way steam condenses to liquid droplets as water vapor cools. Further expansion and cooling allowed the neutrons and some of the protons to fuse to helium nuclei. The 73% hydrogen and 25% helium abundances that exists throughout the universe today comes from that condensation period during the first three minutes. The 2% of nuclei more massive than helium present in the universe today were created later in stars. The nuclear reactions that formed 4He from neutrons and protons were radiative capture reactions. Free neutrons and protons fused to deuterium (d or 2H) with the excess energy emitted as a 2.2 MeV gamma ray, n + p Æ d + g. These deuterons could then capture another neutron or free proton to form tritium (3H) or 3He, d + n Æ 3H + g and d + p Æ 3He + g. Finally, 4He was produced by the reactions: d+ d Æ 4He + g, 3He + n Æ 4He + g and 3H + p Æ 4He + g. Substantial quantities of nuclei more massive than 4He were not made in the Big Bang because the densities and energies of the particles were not great enough to initiate further nuclear reactions. It took hundreds of thousands of years of further cooling until the average energies of nuclei and electrons were low enough to form stable hydrogen and helium atoms. After about a billion years, clouds of cold atomic hydrogen and helium gas began to be drawn together under the influence of their mutual gravitational forces. The clouds warmed as they contracted to higher densities. When the temperature of the hydrogen gas signNowed a few million kelvin, nuclear reactions began in the cores of these protostars. Now more massive elements began to be formed in the cores of the very massive stars.
-
What are the differences between Western classical music and Indian classical music? What’s the difference in their evolution?
Western classical music can be generalized as an extensive study of harmonies (multiple tones played simultaneously) and the feelings they evoke.Indian classical music can be generalized as an extensive study of note sequences and the feelings they evoke.Both explore two different dimensions of music.A western classical song written for an orchestra will typically consist of a hundred different instruments / voices playing different note sequences. Here, it is not the parts that are important, but the whole - how good these note sequences sound together. Hence we arrive at the idea of harmonies and chords, dissonance and consonance. Harmonic complexity is extensively studied. These are the concepts explored in western music theory.Essentially, it comes down to figuring out “do these notes sound good when played together?”. It’s about creating a co-ordinated piece that has to be played exactly as notated, with precise timing by every performer. The beauty here lies in the unity of all the parts, evoking different feelings.An Indian classical song is more free-flowing and meditative. Each song has a broad structure / template laid out, but the performer is free to (and is expected to) improvise over it. Songs are rarely notated, and notations for the same song can vary from one another.Here, there is no concept of harmony; there is always only one note playing at a time. The core ideas studied in music theory are different combinations and sequences of notes, and their phrasings (called raagas / raags). There is so much depth explored here that musicians can usually sing each raaga for an hour.These differences are probably rooted in how these forms of music originated. Music in ancient India was a means to signNow the gods. It was a way to express devotion, love and gratitude to them. Therefore, its nature became very meditative. You rarely ever see songs that express emotions about romantic love, sexuality or the complexity of human relationships. In western music, a variety of these emotions and feelings are explored in depth, because it evolved through a need to express them.This is also the reason that a good part of western music involves modulation. Songs sung to a lover are to be sung softly, songs sung in anger have to be sung harshly, and so on (taking some clichéd examples). A lot of emphasis is given, both to instrumentalists and singers, on how each note should sound. In Indian classical music, the only thing important is what note is being played / sung (and the transitions between them).Both forms of music explore entirely different dimensions of music, and are beautiful in their own way. :)
Trusted esignature solution— what our customers are saying
Get legally-binding signatures now!
Related searches to Remove eSignature Presentation Later
Frequently asked questions
How do i add an electronic signature to a word document?
How to make a pdf editable for esign?
How to track electronic signature for us mail?
Get more for Remove eSignature Presentation Later
- Help Me With Electronic signature North Dakota Plumbing Presentation
- How Do I Electronic signature North Dakota Plumbing Presentation
- Help Me With Electronic signature North Dakota Plumbing Presentation
- How Can I Electronic signature North Dakota Plumbing Presentation
- Can I Electronic signature North Dakota Plumbing Presentation
- How Can I Electronic signature North Dakota Plumbing Presentation
- How To Electronic signature North Dakota Plumbing Presentation
- How To Electronic signature North Dakota Plumbing Presentation
Find out other Remove eSignature Presentation Later
- Participant agreement d6 night market village of form
- Inheritance account agreement piper jaffray form
- Atto di assenso form
- Animal ampampamp veterinary sciences internship learning contract form
- Evidence forms
- Bottle agreement form
- Lettre avis form
- Conformation entry form united kennel club ukc
- Cat history form
- 0327729000 form
- Retail stores liquor stores and wholesale operations texas form
- Kofc rsvp program form
- A mighty flier form
- Scouters training award form
- Activity faith church students lock in which includes among other things basketball dodge ball volleyball swimming walking form
- Customer service information sheet csis puget sound energy
- Catalog table of contents american granby inc form
- Antrag auf arbeitslosenentschdigung arbeitswiss form
- Certified inspection form
- Written compositions example form