Request eSignature Form Myself
Make the most out of your eSignature workflows with airSlate SignNow
Extensive suite of eSignature tools
Robust integration and API capabilities
Advanced security and compliance
Various collaboration tools
Enjoyable and stress-free signing experience
Extensive support
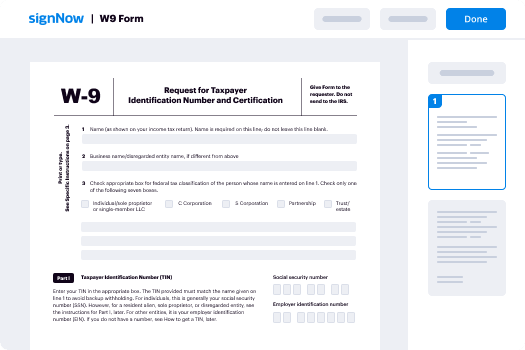
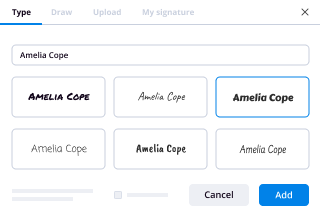
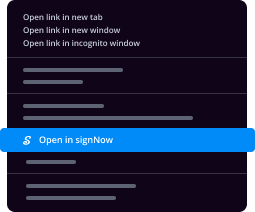
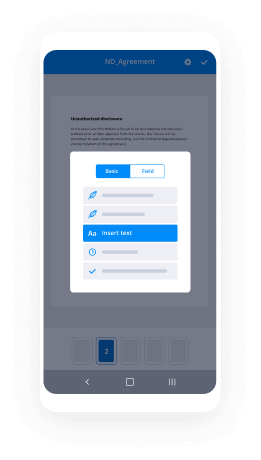
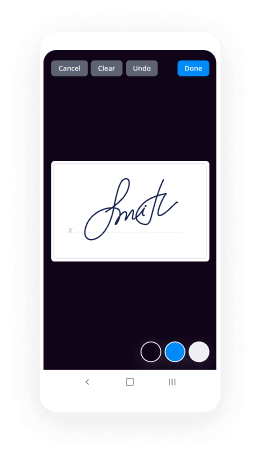
How To Add Sign in eSignPay
Keep your eSignature workflows on track
Our user reviews speak for themselves






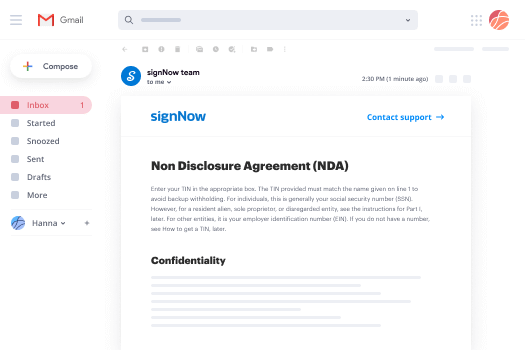
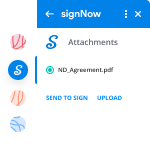
Request eSignature Form Myself. Investigate probably the most consumer-warm and friendly knowledge of airSlate SignNow. Deal with your complete document handling and expressing program electronically. Move from hand held, document-structured and erroneous workflows to computerized, electronic and flawless. You can easily make, produce and signal any paperwork on any device everywhere. Ensure that your essential enterprise instances don't fall overboard.
Discover how to Request eSignature Form Myself. Keep to the simple manual to begin:
- Create your airSlate SignNow account in click throughs or log in with the Facebook or Google accounts.
- Enjoy the 30-working day free trial or select a pricing strategy that's perfect for you.
- Get any lawful design, create on the web fillable kinds and share them firmly.
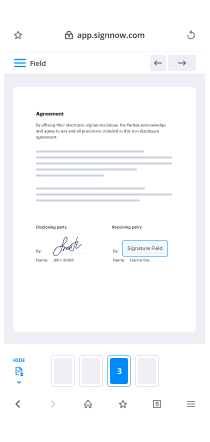
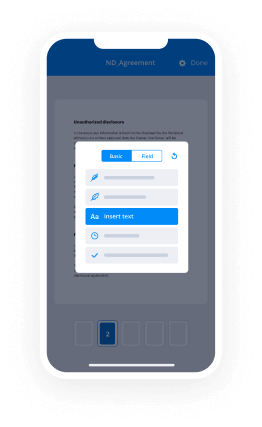
- Use advanced capabilities to Request eSignature Form Myself.
- Sign, personalize putting your signature on order and acquire in-particular person signatures ten times faster.
- Established automatic reminders and acquire notices at every phase.
Relocating your activities into airSlate SignNow is uncomplicated. What comes after is an easy process to Request eSignature Form Myself, along with suggestions to keep your fellow workers and associates for far better cooperation. Empower your workers together with the best instruments to keep in addition to business operations. Increase productiveness and scale your organization more quickly.
How it works
Rate your experience
-
Best ROI. Our customers achieve an average 7x ROI within the first six months.
-
Scales with your use cases. From SMBs to mid-market, airSlate SignNow delivers results for businesses of all sizes.
-
Intuitive UI and API. Sign and send documents from your apps in minutes.
A smarter way to work: —how to industry sign banking integrate
FAQs
-
What’s the rudest customer service experience you have ever had?
So we had been with a certain national bank for about 12 years. We had issues with them off and on, but it wasn't enough to make us want to go through the hassle of finding a new one.Then 2016 happened.It was a chaotic but exciting time for my family. We sold our house and upgraded just a few miles away. Naturally, we were excited but had a long list of things to update. Included on that list was the bank information.We walked into the local bank branch to change our address about a week before we moved. No harm; no foul. It was easy enough.Most of our banking is done online, so it wouldn't be shocking not to receive statements to our new address. I started to realize though that some letters to new address were just addressed to my husband and not myself. Odd, but it's not alarming yet.My debit card expired in December of that year, and around late October I received an email indicating that a new debit card had been mailed to me. Sweet!Only it didn't come. We waited. And waited. And waited. We would call, only to be told that it could take a few weeks.No new debit card for me. Meanwhile, my husband had already received his.Going online, we realized that they had the old address for me still listed. Once again, we trudged down to the post office to get it changed.Side note: Why wasn't mail being forwarded? Good question. Our city postal service struggled with that regardless of our efforts. Different story.Anyway, the next week it was - again - going to be sent to me. And again, no new debit card. It was sent to my old one.This went back and forth for weeks. For some reason, they would not update my address. Usually they would just cancel the debit card that had been sent to the wrong address, but in mid-December they actually canceled my working card, too. Oops.Finally we signNowed an agreement with a supervisor that a new card would be overnighted to one of the few branches open on Christmas Eve. It should be in their mailbox by 11 AM, which would leave us time to still head out of town for the holiday.We made our way down to the branch. It wasn't really close to us, but I really needed a working debit card. We went into the branch, which was located within a grocery store.Two people were working.One other person was in line. One teller was on the phone.When we signNowed to the counter, we explained our situation. We were hopeful that this would solve our issues. Unfortunately, it went south. Fast.The first teller flat out told us to get to the back of the line (by now there were a few other people) because she was busy with other customers. We looked around - she was busy with US. We are customers with a healthy bank account, so...how were we not CUSTOMERS?We asked for clarification. All we wanted was her to check the mailbox for an overnighted envelope with my debit card in it. Mind you, I had no working card.She started yelling, saying she couldn't leave her customers and to - again - get to the back of the line. We calmly explained that we were customers, too. At some point she would have to assist us. We just needed her to check her mailbox. Please. Please. Please.I was almost crying at that point. This entire situation has been a mess despite doing everything we could on our end.That set her off. By now, we had both tellers screaming at us to get out of their bank....all because we wanted her to check the mailbox. For my debit card. Which their bank continuously failed to send to the correct address.I wish I were kidding. If I could get the video footage of it, I would.We immediately placed a call to the bank's call center to at least get it noted what was going on. The supervisor, though at first defensive of the tellers, quickly admitted that they both acted inappropriately. We were even given a credit of like $50 for our trouble. (Weee!)He overnighted ANOTHER new card to my parent's address, which thankfully came on Dec. 26.He also FINALLY updated my address in their system. He had no idea why no one else had been able to update it.Flash forward to March. It was payday, and I had tried to buy a Groupon for something like bowling for the family. My card was declined -- interesting. It also happened at the same time that other people were tweeting that they weren’t able to use their debit cards either. There must be a national outage, right?Wrong.My boss frantically contacted me to ask if everything was okay - my paycheck had not gone through.Naturally, we called to find out that the bank had terminated our relationship. They claim that they sent us a letter in January, but we never received anything like it (though I don't know if I should blame them or our postal service for that one).Why did they terminate our relationship, you ask?Easy: we were in violation of "misconduct" with the tellers who apparently reported us as being belligerent. We may have raised our voices slightly, but it was THEY who yelled at US. I’m not exaggerating here. I’ve never had two grown women yell at customers like those two tellers.No one wants to work on Christmas Eve, but come one now!There was no appeal. It was a done deal - they didn't really care about our side of the story.It turned out in the end because we love our new bank, but dang - it was one of the worst experiences we had ever gone through with bad customer service that went on to actually hurt us beyond the incident.Funny enough, the bank still sends me emails asking me to open a new checking account.
-
As a startup founder of three years our legal housekeeping is a bit of mess, how can I best setup a system to organize and track
As a startup founder of three years myself, I can relate to how legal housekeeping can be messy. Once a year, I have our own lawyers go through and do an audit of all of our legal paperwork (which costs a couple thousand dollars to be extremely thorough, but it’s worth it). Luckily, there are now many ways to easily manage and track all of your legal, financial, and HR documents via third-party sites that specialize in these management proceedings. I wrote a blog post about this awhile back titled “5 Ways to Save Time Dealing With Documents” which highlights certain sites that can be very beneficial depending on what paperwork you’d like to track or manage. They are as follows:1. GroupDocsGroupDocs is a new, comprehensive online service for document creation and management. It has multiple features, including a viewer for reading documents in your browser, an electronic signature service, an online document converter, a document assembly service, a feature for comparing different versions of a document, and an annotation feature. An individual plan is $10 per month for limited storage and 500 documents, while a group plan for up to 9 people is $19 per user per month. Based on the number of features and pricing, GroupDoc is a good-value purchase for a small business. As you’ll see below, GroupDocs can be cheaper than a service that offers only one such feature.2. signNowWhen you’re closing a deal and need to get documents signed, the last thing you need is a slow turnaround due to fax machine problems or the postal service. The solution is to use an electronic signature service such as signNow, which is one of the most popular e-signature companies in the world. This service allows you to email your documents to the person whose signature you need. Next, the recipient undergoes a simply e-signing process, and then signNow alerts you when the process is completed. Finally, signNow electronically stores the documents, which are accessible at any time. As a result, you can easily track the progress of the signature process and create an audit trail of your documents. The “Professional” plan is recommended for sole proprietors and freelancers, and costs $180 per year ($15 per month) for up to 50 requested signatures per month. The “Workgroup” plan is geared towards teams and businesses, and it costs $240 per user per year ($20 per month per user), for unlimited requested signatures.3. signNowsignNow is another e-signature service. Similar to signNow, signNow allows you to upload a PDF file, MS Word file or web application document. Next, you can edit the document, such as by adding initials boxes or tabs, and then email them out for signatures. Once recipients e-sign the document, signNow notifies you and archives the document. signNow offers low rates for these services: a 1-person annual plan with unlimited document sending costs $11 per month. An annual plan for 10 senders with unlimited document sending costs only $39 per month.4. ExariExari is a document assembly and contract management service that assists in automating high-volume business documents, such as sales agreements or NDAs. First, the document assembly service allows authors to create automated document templates. No technical knowledge is required; most authors are business analysts and lawyers. Authors have a variety of options for customizing documents, such as fill-in-the-blank fields, optional clauses, and dynamic updating of topic headings. They also can add questions that the end user must answer. Once you send out the document, the user answers the questionnaire, and Exari uses that data to customize the document. Next, the contract management feature allows you to store and track both the templates and the signed documents. Pricing is based on the size and scope of your planned implementation, so visit their website for more information.5. FillanyPDFIt’s a hassle having to print out PDF forms in order to complete them. Fortunately, FillanyPDF is a service that allows you to edit, fill out and send any PDFs, while entirely online. This “Fill & Sign” plan costs $5 per month, or $50 per year. If you subscribe to the “Professional” plan, you can also create fillable PDFs using your own documents. With this service, any PDF, JPG or GIF file becomes fillable when you upload it to the site. You can modify a form using white-out, redaction and drawing tools. Then, you can email a link to your users, who can fill out and e-sign your form on the website. FillanyPDF also allows you to track who filled out your forms, and no downloads are necessary to access these services. The “Professional” plan costs $49 per month, or $490 per year.Switching firms can be a hassle. As a former startup attorney, I have a bit of advice about finding the right attorney for your business: it’s best to focus on the specific attorney you’ll be working with. He or she should have a solid understanding of the ins and outs of your business industry, a deep knowledge of the legal issues your startup may face, and previous work experience with startups to ensure a quality and efficient work product. This is absolutely key when matching our startup clients at UpCounsel to attorneys on our platform who can perform their legal work and hash out their legal projects in a timely manner. We also allow clients to store any and all of their legal documents directly on UpCounsel so they don’t have to go searching in alternative places for the correct paperwork. It’s proven to be a free and lightweight way to store legal documents that our clients love. Here's what it looks like:As I’ve mentioned, it’s more important to find the right attorney as opposed to the right law firm. And seeing as you’re a startup, our own startup clients typically save an average of 50-60% on their legal work, since the attorneys don't include overhead fees (a.k.a. the fees included for doing business with the firm itself) in their invoices.Hope this gives you a deeper look into what other sites and services are out there. If you have any questions or would like more information on how best to handle your legal housekeeping/ attorney matters, feel free to signNow out to me directly. As a former startup attorney at Latham & Watkins, I’d be happy to give you some guidance.
-
What are some rare unknown facts about Chhatrapati Shivaji?
|| जय भवानी जय शिवाजी ||Shivaji Maharaj was the founder of the Maratha kingdom. Born on 1627 AD at Shivneri near Pune, Shivaji went on to become a Maratha hero who gave the Moslem invaders a tough time. His father Shahaji Raje Bhosale was in the army of Bijapur Sultan and he grew up under the care of his mother Jijabai and Dadaji Kondadev, his guardian.He Built a Powerful Naval ArmyShivaji Maharaj at a very early stage realized the importance of Naval force. He not only protected the Konkan coast from the pirates but also made sure it remained independent from foreign invaders including the Dutch, Portuguese and the English. What’s more, he also built naval forts at Jaigad, Vijaydurg, Singhudurg and other places. He also had four different kinds of warships including Manjuhasm Pals, Gurabs and Gallibats.It was Shivaji who formed a Professional Army of MarathasBefore Shivaji came in force, there was no proper Maratha army. It was Shivaji Maharaj who formed a formal army where several soldiers were paid throughout the year for their services. The Maratha army was divided into several units and each unit had 25 soldiers. The 25 soldiers reported to Havaldar who then reported to Jumladar. Both Hindus and Muslims were appointed in the army without any discrimination.At the age of 15, Shivaji Acquired Forts by BribingWhen Shivaji was only 15 he bribed Inayat Khan, a Bijapuri commander to hand him the fort of Torna. Next, Shivaji also got the possession of Kondana fort after bribing an Adilshahi commander. Besides, the commander of Chakan fort became a Shivaji loyalist. Seeing Shivaji as a threat, Mohammed Adilshah imprisoned his father Shahaji Raje. Later Shahiji was conditionally released.The Combat with the Mighty Afzal KhanShivaji is known for his combat with the Adilsahahi general Afzhal Khan. Both of them were supposed to meet carrying only a sword with just one follower. Shivaji speculated that Afzhal Khan would attack him so he wore armor beneath his dress. Different accounts narrate different stories as to who initiated the first attack/ However, it is interesting to see how a small man both in built and size could easily defeat and kill the huge general Afzal Khan in a combat.Shivaji Maintained Peaceful Relations with MughalsShivaji maintained peaceful relations with the Mughals. In fact, Shivaji even offered his assistance to Aurangzeb for capturing Bijapur. In return he was guaranteed formal right to the forts and villages which were under his possession. However, things started deteriorating when Shivaji’s officer raided areas near Mughal Territory of Ahmednagar and later in Junnar. Soon, even the Mughals retaliated by raiding Shivaji’s territory.Shivaji Had to Fight with His Half Brother VenkojiAll the negotiations made by Shivaji with his half brother Venkoji failed and this is the reason why the two brother fought each other in 1677. However, Shivaji defeated Venkoji and took most of his possessions. Later, Venkoji’s wife Dipa Bai made new negotiations with Chhatrapati Shivaji Maharaj and even convinced her husband to stay away from Moslem advisors.
-
What kind of e-mails irritate professors the most?
Many. Those rejection letters (we get plenty of those) and collaborators not honoring their commitments to common projects are particularly bad. However, I get the feeling you’re referring to student-initiated emails. I agree with Joshua Gross’ list. Other than that, here are a few types of those I find irritating.Disrespectful, juvenile, text-message-like, titleless emails. Your email must have some basic structure, including hello, your name and course, and a question/comment. At the end, say goodbye. Also, mind the style a little. I’m really not your mate. If you don’t include a title I won’t respond.Emails that ask about something that is clearly stated on the syllabus. If you do this, (i) I’ll simply email “that information is in the syllabus” and (ii) you will look careless and unengaged. Don’t be that person.Emails that are excruciatingly long. Please, don’t do this to me. I’m sure whatever you’r trying to say could be synthesized in four sentences.Emails sent from private accounts (gmail, yahoo, hotmail…). Because of legal reasons, communications with students are best kept on the university’s server. You have an institutional email. Please, use it. This applies to my own students and students from my university, particularly when submitting assignments and discussing grades and other sensitive educational issues. If you're emailing me because you want to apply to our graduate program, and you do this from a gmail account that's completely fine.Emails asking about the homework. I’m not your secretary nor your father. Don’t ask about the homework because I will not respond to your email and bring this issue to everybody’s attention next time we meet in class.Emails that are too personal and explain issues that should be presented face to face, during office hours. Life happens. I know. Leave the deep stuff for face to face conversations if possible, and only bring them up if you think I really must know. I’m happy to listen, but I’m a linguist, not a psychologist. I can tell you who to contact if you need help.Emails that come after the final grades have been posted (asking for extra credit opportunities). Once the grades have been rolled up, they’re official. No, you can’t read a book and submit a synthesis for one extra credit now. It’s December 18th!Emails from parents on behalf of their children (who are my students). One word: FERPA. In other words, “Sorry, I can’t discuss any of this with you, helicopter mother of a 22 year old”.Emails asking about something I have announced on Blackboard/CANVAS. This is quite self-explanatory. Like the message I sent on Blackboard/CANVAS.Now, having said that, I understand you are a student. You’re learning. Part of that learning includes email interactions. I won’t be offended by your email, even though it might frustrate me a bit. I’m actually glad to point you in the right direction.
-
What is the format of the RTI reply?
Sample ApplicationDate :To,The Public Information Officer,Centre for Cultural Resources and TrainingPlot No. 15A, Sector – 7, DwarkaNew Delhi - 110075Sub:-Request for information under RTI ActDear Sir,I ______________________________ Son/ Daughter / Wife of ____________________ resident of______________________________________________________________ Telephone No. (withSTD Code) / Mobile No. – (______) __________________ wish to seek information, under the RTI Act, 2005 from Centre for Cultural Resources and Training, New Delhi. I, hereby, declare that I am a Citizen of India and information sought in this application will be used in the best of the Public Interest. I further assure you that, I shall not allow/ cause to use / Pass / share / display / or circulate the information received in any case and under any circumstances, with any person or in any manner which would be detrimental to the Unity / Sovereignty or against the Interest of India.1. The information needed is in the form of ___________ Documents / Clarification.(Plz. Tick whichever applicable)2. The Information sought pertains to your head office CCRT, New Delhi / CCRT Regional CentreHyderabad / CCRT Regional Centre Udaipur.(Plz. Tick whichever applicable)3. The Required Information is for the period - ___________ to ______________.4. The information sought is related to -------- Myself / Third Party(Plz. Tick whichever applicable)5. The particular / details of Information / Documents asked for is given below:-________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________6. I have deposited the required RTI Fee amount of Rs. 10/- (Rupees Ten Only) towards application fee through Cash (Receipt enclosed) / Demand Draft / Banker’s Cheque / Indian Postal Order (Strike Out Whichever not Applicable) favouring ‘Centre for Cultural Resources and Training, New Delhi’ Payable at ___________ (the place where application is deposited). Further, I also undertake to pay any additional fees/charges (if applicable) as prescribed under the RTI Act.Kindly provide the information as soon as possible & within time frame as stipulated under RTI Act, 2005.(Name and Signature of the Applicant)Address:- ______________________________Tel. No. (office):- _______________________ (Res.):- _______________________E-mail Address, if any _________________________
-
How do the police build a criminal case against you?
Since I was a2a, how a case is built is dependent upon the type of crime (fraud, drug trafficking, money laundering, violence, etc.). Discovery of fraud generally involves a report of suspicious activity, a victim’s report, or review of records. Fraud investigations are primarily conducted through collection of pertinent financial records, identifying those involved and their documented activities. Fraud commonly involves a convoluted manipulation of circumstances that requires extensive knowledge of law and applicable regulations.Drug trafficking and associated money laundering generally involve informant information, with the informant commonly being someone arrested for an observed drug violation who turns on their confederates in order to limit their own punishment. That process could lead to an undercover operation and/or involve extensive surveillance of suspects, identification of drug and money stash locations, trash collection at identified locations, and collection of sufficient information to establish probable cause for a search warrant (http://www.quora.com/What-constitutes-probable-cause-for-a-police-officer-to-be-able-to-search-a-car-without-a-warrant/answer/Dan-Robb-2). The search warrant could lead to recovery of evidence, identification of suspects, and seizure of illegal substances or large quantities of currency for which there is no viable explanation.Investigations of crimes against persons are commonly initiated based on a report of what is claimed to be criminal behavior by a witness. The next common step involves interviews indicating where evidence may reside or where other witnesses may be located. Such information is evaluated and corroborated if possible; in that not even all eyewitness testimony is reliable (Robb, 2011). Crime scenes are identified and search is initiated, based either on immediate probable cause or through search warrants. Evidence is collected if possible, then processed for possible identification of suspects (e.g., DNA and/or fingerprints identifiable from data bases of prior offenders, or for comparison with future suspects), and indicators of events are theorized (e.g., accidental versus criminal actions).If no suspects are identifiable, or even if there are possible suspects, how the crime was committed may provide clues linking that crime to a past suspect or past crimes, even without physical evidence with regard to a suspect; or, if a serious crime, investigation may involve more extensive evaluation in a criminal profiling process:Modus Operandi and SignatureD. RobbCMRJ531In 1838, Sir Frederick Roe, a magistrate in London, argued for the employment of specialized police officers to detect crimes (as cited in Dilnot, 1927). The successes of the privately employed Bow Street Runners were cited as an example of the historical presence of recognizing modus operandi, and what could be interpreted as recognition of the value of criminal profiling.Sir Peter Laurie, a City magnate, was positive that the Metropolitan Police could not supersede the runners. ... "These men have been thief catchers all their lives, and know almost every thief in London, and of what he is capable. ... If you take them to a house, and show them that a robbery has been committed, they will tell you directly, by inspection, whether it has been done by an old or by an inexperienced thief." (as cited in Dilnot, 1927, p. 53)Holmes and Holmes (2002), in my opinion, do not adequately address the concepts of Modus Operandi (MO) and Signature. Therefore, further information is provided here. MO is not a new concept. Dilnot stated that "'Modus operandi' is obviously as old as detective work itself" (1927, p. 212). Dilnot did not comment of the exact origins of the position of detective, but he did say that detectives were employed by the Metropolitan Police, under the British Home Secretary, prior to 1845. The daguerreotype photographic process was patented in Europe in 1840, and,had come to America soon afterwards. ... None was more enthusiastic for this medium than Alan Pinkerton. Within a few years he had built up an impressive Rogues Gallery of mugshots and circulated copies of photographs to lawmen all over the country, together with detailed descriptions of physical features, dress, habits, mental characteristics, criminal specialties and mode of operation. (Mackay, 2007, p. 93)Pinkerton (1819-1884), a Scotch immigrant barrel maker and former Deputy Sheriff, headed the de facto national investigative agency (albeit private) in the U.S. during the pre- and post-Civil War era. The emergence of this private agency was apparently due the emergence of interstate commerce (i.e., railroads); the lack legal jurisdiction outside of the city, count, or state; an aversion to central governmental control; parochial thinking; and governmental financial considerations. In 1861, Pinkerton sent a letter to President Lincoln:I have in my Force from Sixteen to Eighteen persons on whose Courage, Skill and Devotion to their country I can rely. If they with myself at the head can be of service in the way of obtaining information of the movements of Traitors, or Safely conveying your letters or dispatches, on that class of Secret Service which is the most dangerous, I am at your command. (as cited in Mackay, 2007, p. 107)Fosdick (1915/1969), a former New York City Commissioner of Accounts, conducted one of the first cross-cultural studies of policing during 1913 and 1914. He was complimentary of the German system of criminal investigation, particularly with regard to the scholarly efforts of Dr. Hans Gross, an academic and criminal justice practitioner. Many European police agencies employed relatively sophisticated criminal classification and referencing systems, to the extent that in some countries, all foreigners were required to record their travels with the local police or face legal sanction. The use of dactyloscopy (fingerprinting) began for Scotland Yard in 1901, after use by English officials in India. And, classification of offenders according to method of operation (MO) by Scotland Yard was begun officially in 1896. However, at the request of London authorities in 1888, Dr. Thomas Bond was apparently cognizant of the concept based on his assessment of the crimes attributed to Jack the Ripper, based on his statement thatall five murders were no doubt committed by the same hand. … All the circumstances surrounding the murders lead me to form the opinion that the women must have been lying down when murdered. …In each case the mutilation was implicated by a person who had no scientific nor anatomical knowledge. …A man subject to periodical attacks of Homicidal and Erotic mania. The murderer in external appearance is quite likely to be a quiet inoffensive looking man, probably middle-aged and neatly and respectfully dressed. He would be solitary and eccentric in his habits, also he is most likely to be a man without regular occupation, but with a small income or pension. (as cited in Kocsis, 2006, p. 4)MO was at that time primarily used for burglary and theft crimes. Fosdick related:What is probably the most ambitious plan of crime classification by methods has been initiated in ... England. ... The so-called "M.O." or Modus Operandi system devised by Major L. W. Atcherley, Chief Constable of the West Riding of Yorkshire Constabulary.His system is more than an index for a single department. It is a cooperative arrangement by which habitual or traveling criminals can be traced from community to community by a comparison of their methods of work. (1915/1969, p. 344)Atcherley's system included 10 categories, and the tenth is somewhat consistent with the concept of signature:1—Classword; kind of property attacked, whether dwelling house, lodging house, hotel, etc.2—Entry; the actual point of entry, front window, back window, etc.3—Means; whether with implements or tools, such as a ladder, jimmy, etc.4—Object; kind of property taken.5—Time; not only time of day or night, but whether church time, market day, during meal hours, etc.6—Style; whether criminal to obtain entrance describes himself as mechanic, canvasser, agent, etc.7—Tale; any disclosure as to his alleged business or errand which the criminal may make.8—Pals; whether crime was committed with confederates, etc.9—Transport; whether bicycle or other vehicle was used in connection with crime.10—Trademark; whether criminal committed any unusual act in connection with crime, such as poisoning a dog, changing his clothes, leaving a note for the owner, etc. (Fosdick, 1915/1969, p. 346)MO and Signature are similar and may be easily confused, one for the other. MO involves those behaviors necessary for the successful commission of a crime; incorporating three elements: 1) success of the crime; 2) protection of identity; and, 3) successful escape (Gee & Belofastov, 2007).Signature is an aspect of a crime that fulfills an emotional need, which is not necessarily conscious. Signature could involve intentional crime scene configuration or taking of souvenirs, and generally remains consistent, due to the emotional element; or, may be as elemental as words used or the order in which acts are committed (Holmes & Holmes, 2002). Although, some variations of Signature can be expected, based on the recognition that each independent crime is subject to numerous influences (e.g., unexpected interruption, time constraints, physical limitations) (Douglas, Burgess, Burgess, & Ressler, 1992; Douglas & Olshaker, 1995; Turvey, 2001).Douglas et al. indicated that “signature does not always show up in every crime because of contingencies that might arise, such as interruptions or an unexpected victim response” (1992, p. 261). Turvey (2001) referred to this concept as the “X-factor,” unexpected events at the crime scene that may eliminate MO and Signature.MO is more affected by evolution and refinement, in response to environmental stimuli. For example, if one gets too close to being caught, one will probably improve their methods in the future. Or, as in the “DC Sniper” case, the press commented upon the fact that the shooter had targeted only adults, which was of course followed by the shooting of a young boy. And then, press statements highlighted the lack of demands by the DC Sniper, followed by demands from these spree killers for a large sum of money.Douglas and Olshaker (Douglas being a retired Federal Bureau of Investigation profiler) provided the following discussion of MO vs. Signature, and staging versus posing:The differences between MO and signature can be subtle. … (A) robber … made …captives undress, posed them in sexual positions, and took photographs…. That’s his signature. It was not necessary or helpful to the commission of a bank robbery.” Another robber forced disrobing “so the witnesses would be so preoccupied … that they … couldn’t make a positive ID. … This was MO. (1995, pp. 253-255)In a serial murder case, the defendant’s lawyer “was trying to show that it was unlikely these crimes were all committed by the same individual because so many details of the modus operandi varied. I made it clear that regardless of the MO, the common denominator in each of the murders was physical, sexual, and emotional torture. … So, though the methods of torture varied—the MO, if you will—the signature was the pleasure he received out of inflicting the pain” (Douglas & Olshaker, 1995, p. 255).Staging is an element of MO and involves placement or manipulation of a crime scene to mislead investigators, “such as when a rapist tries to make his intrusion look like a routine burglary” (Douglas & Olshaker, p. 256). Posing, (also) an element of signature, is infrequent and involves “treating the victim like a prop to leave a specific message. … These are crimes of anger, crimes of power(,) … it is the thrill of … beating the system” (p. 256).The Signature is sometimes referred to as a “calling card” or trademark of the offender, such as by Douglas et al. (1992). However, stating that the Signature is a calling card is inappropriate in my opinion. Such a label leads to the inference that it is an intentional act on the part of the perpetrator to mark the crime as his own; this may not be the case, since the perpetrator may not be conscious of the significance of the act and oblivious to how the evidence of his behavior will appear. Turvey (2001) also disagreed with such a label because crimes and the resulting crime scenes are inherently chaotic with numerous variables; therefore, a precise match of Signature and MO is unlikely. In addition, Turvey noted that interpretation of evidence may be faulty due to misinterpretation or destruction of evidence (intentional or accidental), leading to faulty conclusions.Signature and MO may be difficult to differentiate, and may even be indistinguishable in a crime scene. However, the concepts must be separated and the characteristics of each must be articulated.CR531 Criminal ProfilingD. L. RobbProfessor Comments Week 1Very few people would argue against the idea that the ways in which we present and maintain ourselves, our homes, and our workspaces reflect some very important aspects of our personalities. Certainly, from our studies in the humanities, archeology and anthropology, we know that even in the absence of a written history, the depictions of art, music, clothing, household artifacts, and architecture developed and left behind by a long-dead society can still clearly tell us a great deal about the beliefs, attitudes and lifestyles of its inhabitants. Similarly, it is the contention of practitioners of Criminal Profiling, that the actual commission of crimes may also reflect key personality and lifestyle characteristics of those who committed the crimes.The commission of a crime requires that the offender make a series of choices, decisions, responses, and reactions. The resulting dynamics of the crime, as revealed through crime scene investigation, will then necessarily reflect the intelligence, competence, composure, experience, needs, wants, fantasies, motivation, and many other key characteristics of the offender’s personality. This has probably been obvious to those charged with finding and apprehending offenders from the outset of such positions. …Profiling is rooted in the belief that an offender’s thinking directs the offender’s behavior. If the crime scene reveals to us the offender’s behavior, we should be able to examine the scene to make some assumptions about the offender’s thinking. “Elementary,” as Sherlock might say, probably not. Profiling is a complex function that requires investigative experience and insights gained from years of exposure to various crimes, individuals, and personality types.Criminal profiling is a criminological/sociological, psychological, biosociological, and forensic analysis process that attempts to make investigative sense of apparent crime scene dynamics, in order to gain an understanding of behavior, motivation characteristics of offenders, and personality. Profilers analyze the totality of the known crime circumstances, make inferences of offender behavior from that analysis, and create a profile of the offender based on inferences of the offender's behavior (what would appear to be inferences based on inferences).Profiling is, in fact, a form of retroclassification, or classification that works backward. Profilers recognize crime scene dynamics that are associated to criminal personality types who commit similar offences. Typically we classify a known entity into a discrete category, based on presenting characteristics that translate into criteria for assignment to that category. (Douglas, Burgess, Burgess, & Ressler, 2006, p. 97)In this course, you will be prompted to examine the research on criminal profiling. We will try to make sense of these acts of violence, which so often confront us in our contemporary life, and cull out of the acts, some comprehensible threads that will permit us to find similarities amongst offenders’ personalities and to formulate a rationale for the differences between them, as well. However, as we continue our inquiries into the field, we will discover that, as in almost all studies of human behavior, the discipline is filled with contradictory theories, opposing beliefs about the best way to study and construct criminal profiles, and many social, legal, and ethical issues that must be considered.References:Dilnot, G. (1927). The story of Scotland Yard. New York: Houghton Mifflin.Douglas, J. E., Burgess, A. W., Burgess, A. G., & Ressler, R. K. (Eds.). (2006). Crime classification manual: A standard system for investigating and classifying violent crimes (2nd ed.). San Francisco: Josey-Bass.ReferencesDilnot, G. (1927). The story of Scotland Yard. New York: Houghton Mifflin.Douglas, J. E., Burgess, A. W., Burgess, A. G., & Ressler, R. K. (1992). Crime classification manual: A standard system for investigating and classifying violent crimes. San Francisco: Josey-Bass.Douglas, J., & Olshaker, M. (1995). Mind hunter: Inside the FBI’s elite crime unit. New York: Pocket Books.Fosdick, R. B. (1969). European police systems. Montclair, NJ: Patterson Smith. (Original work published 1915)Gee, D., & Belofastov, A. (2007). Profiling sexual fantasy: Fantasy in sexual offending and the implications for criminal profiling. In R. N. Kocsis (ed.). Criminal profiling: International theory, research, and practice. Totowa, NJ: Humana Press.Holmes, R. M., & Holmes, S. T. (2002). Profiling violent crimes: An investigative tool (3rd ed.). Thousand Oaks, CA: Sage Publications.Kocsis, R. N. (2006). Criminal profiling: Principles and practice. Totowa, NJ: Humana Press.Mackay, J. (2007). Allan Pinkerton: The first private eye. Edison, NJ: Castle Books.Turvey, B. E. (2001). Criminal profiling: An introduction to behavioral evidence analysis (2nd ed.). San Diego, CA: Elsevier Academic Press.Once sufficient evidence is collected and corroborated to the extent thought necessary by investigators, the case is presented to prosecutors who assess the evidence with regard to the necessity for proving the allegation beyond a reasonable doubt in court. Additional investigation may be requested, prosecution may be declined, or accepted for prosecution.Reference:Robb, D. L. (2011, November). Eyewitness identification in photographic lineups: A case study. Presented at the Texas Association for Investigative Hypnosis Training Conference, November 2011. Retrieved from: https://www.academia.edu/2662993...
-
What is the history of criminal justice as an academic discipline?
The course of study that became criminal justice grew out of criminology, a subset of sociology. Criminology is the study of the roots and causes of crime. Criminal justice takes in considerably more ground, but usually includes at least one criminology course. People often start the course thinking they want to understand how the criminal mind works, and they are usually more confused when they're done than before they started. In the 1950s and 1960s, there were a few "police science" departments and courses at U.S. colleges, mostly for people who were already cops and wanted college degrees to get a leg up on promotions. Some substituted for police academies, as many law enforcement agencies had no formal training program until the 1960s or 1970s. At most police departments, new hires were placed with a more experienced officer to "learn the ropes" until they were thought to be competent enough to patrol on their own. This training period ranged from a day or two to a year.The man who was the assistant chief at the agency where I worked was hired the year I was born (1953). When he retired, he wrote an article for the department newsletter that described what it was like to be hired then. You put in your application, and when an opening occurred, the chief of police went through the pile and pulled out what he thought were the most promising candidates. Having someone inside the department recommend you to him was huge. If you didn't have a local personal reference he trusted, you had little chance of being hired. The chief called you in, talked to you for a while, and if he liked what he saw, hired you on the spot. It was more or less expected you would already have a gun, but if you didn't there was a rusty .38 Special revolver that the department could loan you until you bought your own. They sent you down to the pistol range to make sure you could hit the wall without shooting off your foot, and told you to be back at 4:00 PM for the evening shift. If you didn't have the money for a uniform, you patrolled in your Sunday church suit, badge pinned onto your jacket, and often with your gun stuffed in your waistband. Given the number of local regulars who always wanted to try out the new guy for a little sport, just making it back to the station at the end of watch without any open wounds was a mark of passage. But, I digress. In the mid-1960s, following several years of civil unrest growing out of the civil rights movement and incidents like the Watts Riots, Congress got the idea that law enforcement needed to become more professional. Huge pots of money were created to fund the Law Enforcement Assistance Administration (LEAA) and the Law Enforcement Education Program (LEEP). The former funded equipment, training, buildings and other goodies; the latter paid for cops' college educations. Cops could go to college for free. Because nothing motivates institutions of higher learning more than money, campuses across the country created degree programs in justice administration, police science, police administration, and other euphemisms, most of which came to be known as criminal justice programs. Because there weren't a lot of academics with relevant degrees in these fields, many of the "professors" were working cops with either vocational teaching certificates (usually requiring only a high school diploma and work experience), or bachelor's and a few master's degrees. It wasn't entirely unknown to have Cop A sitting in a class taught by Cop B on Monday, and then for Cop B to be in Cop A's class on Wednesday. Some of these programs were properly rigorous, but others were old boy's clubs where papers were recycled, and the class sessions little more than War Story 101. The police administrators I worked under came up through this system, and they tended to be woefully uninformed and incompetent. This is, unfortunately, still the case. Criminal justice programs have become the Phys Ed of the new millennium. Up until the 1970s or so, physical education majors (most of whom were collegiate athletes) took classes in Theory of Basketball and Team Organization that had little substance, but allowed them to stay eligible to play their sport. Gradually these programs were infiltrated by more rigorous courses in anatomy and physiology, kinesiology, nutrition, and so on, and the muscleheads were forced out. Many of them flocked to criminal justice, which is considerably less demanding than other disciplines.If this sounds cynical, it comes from eight years of teaching criminal justice courses at colleges in five states. I tried to make my courses more rigorous, and was mostly castigated for doing so. The colleges where I worked were far more interested in having students matriculate and then re-enroll in courses for as long as possible, seeking out that elusive Full-Time Equivalent (FTE) student statistic. If the courses were too hard, they gravitated to another professor or another school where they didn't have to work so hard. There were a few students who truly wanted to learn and made the job worthwhile, but most of them were there because they didn't know what else to do, or it kept them eligible to play sports. The situation has been made worse by the proliferation of online courses and for-profit colleges. Online courses make it easy to cheat and recycle papers, and the people teaching them are usually part-timers, paid on a per student/course basis. They don't care enough to make the effort to root out the people who aren't really doing the work. The for-profits are often not regionally accredited, which means the credits and degrees they grant won't be recognized by legitimate colleges and many employers. They charge huge fees (paid for with student loans they help the student apply for), do a lot of hand-holding, promise students who have no prayer of ever working in this field that employers will be competing to hire them upon graduation, and ensure that everyone passes and all their students are above average.It's a discouraging situation, and while I deplore it, I'm also happy I'm not having to fight that battle anymore.
-
How am I supposed to get a birth certificate without a picture ID, when I need a birth certificate to get a picture ID, and I ne
Get a form to fill out from the County Clerks Office it is an application for a birth certificatr and get at least two blank affidavits to be completed by people who personally know if the date and tine if your birth. The doctor or hospital where you were born us listed on a birth certificate, date time of birth, your full name at birth, your mother's full maiden name and date of birth and your father's full name and date of birth. The birth county and state. All if this is asked on the application for your birth certificate. A medical dictor with a copy if your driver's license can help you if they personally know you as a patient they have seen by completing an affidavit and submitting it on your behalf, your apartment nanager can also provude you wuth an affidavit. Both probavly have copies of your address and identification if your an established patient abd renter. A close relative can complete ab affidavit as well but must include a copy of ‘their’state issued identification with their affidavit. They must have enough knowledge if your birth to vouch for when and where and time you were born as well as county and state of your birth and name if your birth facility. Misr school officials and employers are also in a position to vouch for you with signed and signNowd affidavits. bearing their signature and form of identification they have on file fir you.Hope you can get this taken care if right away. I found myself in the same position when my purse was stolen 10 years ago.I went to an organization with a black and white copy of my state issued photo identification ob file and asked that they make a copy if it for me. I was able to get a hard copy of my photo ID by having the driver's license number and a number that ran the length of the DL card. I then used the replacement photo copy of my DL to get my Birth Certificate. I used my lease copy and a utility bill to verify my address too. Anyone with a copy of that state issued photo ID will be able to complete an affidavit.Thanks for requesting my answer to your questionMay God ve with you 0:) B..
Trusted esignature solution— what our customers are saying
Get legally-binding signatures now!
Related searches to Request eSignature Form Myself
Frequently asked questions
How do i add an electronic signature to a word document?
How to esign a filable pdf file?
No matter where you're from sign pdf?
Get more for Request eSignature Form Myself
- Can I Electronic signature New Mexico Plumbing Presentation
- How Can I Electronic signature New Mexico Plumbing Form
- How To Electronic signature New Mexico Plumbing Presentation
- How Do I Electronic signature New Mexico Plumbing Presentation
- Can I Electronic signature New Mexico Plumbing Form
- Help Me With Electronic signature New Mexico Plumbing Presentation
- How Can I Electronic signature New Mexico Plumbing Presentation
- How To Electronic signature New Mexico Plumbing Form
Find out other Request eSignature Form Myself
- Weevil cide applicators manual form
- A practical english handbook for bachelor students ujaz feec vutbr form
- Non solicitation form oando
- Ged transcripts 225944136 form
- Global school of open learning form
- Techlog software manual pdf form
- Mc2000 handicare as puls norge form
- Pte ail vic edu au in pte reading form
- State of nevada petition for summary administration form
- Duplin county inspections 47344415 form
- Substation checklist form
- 92900a form
- Pennsylvania quitclaim deed from husband and wife to an individual form
- Pre kindergarten assessment rubric 2nd nine weeks form
- Rimowa repair policy form
- Inventory agreement template form
- Colombian birth certificate template form
- Amendment complaint riverside form
- Alitalia modulo di segnalazione form
- Online form filling for scholarship for ipcc