Create Electronic signature Presentation Mobile
Make the most out of your eSignature workflows with airSlate SignNow
Extensive suite of eSignature tools
Robust integration and API capabilities
Advanced security and compliance
Various collaboration tools
Enjoyable and stress-free signing experience
Extensive support
How To Implement eSignature in CMS
Keep your eSignature workflows on track
Our user reviews speak for themselves






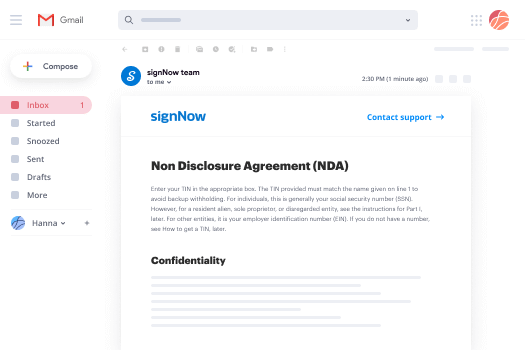
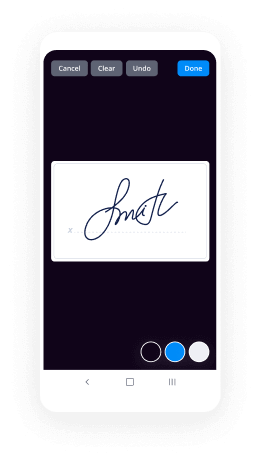
Create Electronic signature Presentation Mobile. Check out by far the most user-pleasant knowledge about airSlate SignNow. Manage your entire document processing and expressing system electronically. Go from hand held, paper-structured and erroneous workflows to automatic, computerized and flawless. You can actually produce, supply and sign any documents on any gadget anyplace. Ensure your essential company cases don't slip over the top.
Discover how to Create Electronic signature Presentation Mobile. Keep to the basic information to start:
- Design your airSlate SignNow accounts in clicks or log in with your Facebook or Google profile.
- Benefit from the 30-time free trial version or go with a prices program that's perfect for you.
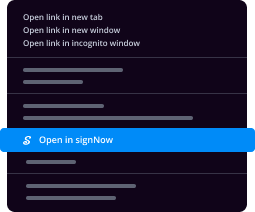
- Find any authorized template, develop on-line fillable forms and talk about them tightly.
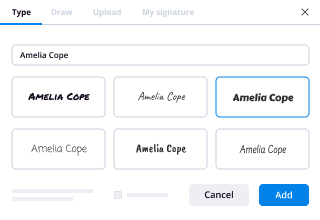
- Use innovative characteristics to Create Electronic signature Presentation Mobile.
- Indication, modify signing order and acquire in-individual signatures 10 times more quickly.
- Set automated alerts and obtain notices at every stage.
Relocating your tasks into airSlate SignNow is easy. What follows is a straightforward procedure to Create Electronic signature Presentation Mobile, along with tips to keep your colleagues and partners for greater partnership. Encourage the employees using the greatest instruments to stay on the top of enterprise operations. Enhance efficiency and scale your organization faster.
How it works
Rate your experience
-
Best ROI. Our customers achieve an average 7x ROI within the first six months.
-
Scales with your use cases. From SMBs to mid-market, airSlate SignNow delivers results for businesses of all sizes.
-
Intuitive UI and API. Sign and send documents from your apps in minutes.
A smarter way to work: —how to industry sign banking integrate
FAQs
-
What is the new instantaneous payment system being used at Target?
This is a great question! I have some direct and indirect knowledge of this program. The way Target has crafted the retail transaction experience I think portends to the direction I believe a vast majority of retail experiences will migrate to. I will digress with a bit of background.Target And TechnologyTarget has always been on the leading edge of technology on front end systems and back end systems. Most of the technology is not seen and operating in the background. For example, the POS and Inventory management software is so well tuned, that it does an incredible job in predicting demand for a particular item up to the not only the day, hour or minute, but to the second.They also have a great deal of foresight in branding most customer facing technology in the store's iconic color of Red. And look to the finest detail on how to improve the entire check out experience. Not just optimized for speed (see Walmart) but optimized for the best possible experience. This is one of the largest forces driving the company's adoption of technology and perhaps the high wisdom that is seen in the way they deploy this technology. There is a great deal of study in retail psychology that most of us are not aware of that plays out when you are completing a purchase. You and I want to get through the checkout line in a very efficient manner. We want the experience to be fast, but perhaps not too fast. The 10 feet that surrounds a checkout line has some of the highest profitability for most retailers and we as consumers love this little area. So Target thought very long and hard about the entire process and signNowed out to a number of industry experts over the last 15 years to help craft the best possible experience we see today.Electronic Signatures. Swipe And Sign Before The Final Barcode ScanTarget was one of the first national retailers to embrace electronic signature pads instead of signing a paper receipt. They did this not so much for how it allowed the company to not need to manage and store the customer's signed receipts, that was important, but more so on how much faster the check out process was conducted. The new technology allowed for a new concept in retail, the early presentation and authorization of the transaction, prior to the final barcode scan. It allows the customer to swipe their Payment Card and sign the receipt all before the last product was bagged. Target was one of the first retailers to implement this very new experience. It sure seems simple and logical today, but it was anything but that when the ideas were being hashed out.Over the years. Target has experimented with a number of customer facing systems from IBM, Verifone and Hypercom. The most recent standardization is with a customized version of the Hypercom Optimum L4150 High-Performance Multi-Lane Payment and Advertising Terminal.Hypercom L4150How Does Target Speed Up Payment Card Acceptance?There are many parts that go into creating the very speedy Payment Card experience at most Target stores. As mentioned above the customized L4150 is the point of interaction and allowed for much of the changes we see in the checkout experience. But there is a lot going on in the background. The L4150 is connected to the POS system usually and IBM SurePOS 500 or 700 and routed through custom software that is connected to the Payment Card Authorization systems. All of this tech has been optimized by and for Target. The process starts when the customer swipes the Payment card and this can be the moment the first item is scanned by the cashier. Once the card is swiped there is an immediate request for a signature. When the last item is scanned the system completes the transaction and prints the last lines of the receipt and this can be as fast as 2 seconds. If one waits to the end of the last scan to swipe the credit card and the transaction is below $50 there will be no prompt for a signature and this is equally as fast. A Pleasant Surprise The entire process is designed to be highly efficient and very simple for the consumer to translate. It comes as a pleasant surprise to just about all of us, even when when have experienced the process before. It is in stark contrast to most Payment Card transaction experiences. This well thought out process is combined with one of the fastest Payment Card Authorization network connections, at a major retailer, using M-Dex ((Merchant Direct Exchange) established by Visa to process at 1mb+ speeds for very large retailers (500,000+ transaction/month). The entire backend is driven by a 5mb-25mb connection to the Target's VPN (Virtual Private Network) using Microsoft's Virtualization solution— Hyper-V. The system is run on Dell R710 servers for the hosts running Hyper-V and Dell MD1000 storage units. There are 15,000 virtual guests running on more than 3,600 Hyper-V hosts across the entire store network. This supports updates to more than 300,000 endpoints across the network, including servers, virtual machines, mobile devices, PCs, and POS registers. Target, with about 1,768 stores, usually has no IT personnel on-site and has found the Hyper-V virtualization allows a vast majority of issues to be solved at the data center and not locally. Microsoft has a great case study of some aspects of Target’s backend technology with the use of the Hyper-V product here: Microsoft Case Study: Microsoft Services - Target Corporation.This system shows a rather huge commitment to technology and a desire to create the most optimal consumer experience. To see how the same set of circumstances is translated with other national retailers, visit Walmart or Kmart and judge the experience. In Walmart's case, they have a profound, "If it was not invented here, it is not relevant" attitude with its study of the retail experience, and one can surmise if this translates to a richer experience for its customers. By contrast, Target is more than willing to continue to test and experiment and to signNow outside of the company for experts that have studied these processes. I personally think Target is the best example one can find in balancing all important aspects and crafts into one of the top 5 best retail experiences and I feel strongly that wise retailers can gain great insights by studying Target and the way they see its customers.
-
What industries must use electronic signature software?
Any industry involving a large amount of paperwork make use electronic signatures. In other words, all industries make use of electronic signatures because all of them have piles of paperwork to handle. Some examples of such industries include financial, life science, healthcare and pharmaceutical industries.Industries such as the pharmaceutical industry, have a number of licenses and other paperwork that they have to handle and keep track of. It can be a tedious task to perform such cumbersome paper processes. Therefore, e-signatures can facilitate an organisation in keeping a track of all this paperwork, by signing electronically.Healthcare industries usually involve time-sensitive documents, which need to be urgently completed. But, it can take days in case of the traditional wet ink paper signatures for the documents to signNow the signer and back, if the parties are geographically scattered. But with electronic signatures, that is not the case. Geographical barriers do not play a role. Documents which earlier needed days to be completed, can now be signed and sent back within minutes, in the click of a button. Furthermore, it takes a long time to bring assets under management. The time taken by the signing process, if wet ink paper signatures are used, may even further delay the process. But by using electronic signatures, the whole process can speed up.Apart from these, there are many paper prone industries which require huge amount of paperwork and with the use of electronic signatures they can make their everyday processes smoother and more efficient.
-
What specific task(s) could a lawyer (or legal professional, e.g. paralegal) get done using mobile technology available today or
Lawyers can run their entire practices using mobile technology. There is nothing that cannot be done from out of the office. What is required?I will tell you what I use for my consulting business as opposed to for my law firm. But the concepts are the same.1. Laptop and/or tablet. Generally a full laptop will be needed to do most work. I have both.2. SECURE Internet connection. I bring mine with me. I do not trust public networks.3. SECURE cloud based practice management system in which is contained every piece of data for every single client. Also allows for time tracking and billing. I use Clio4. If 3 does not include documents, a separate SECURE document storage and management system. I use SpiderOak5. Smart Phone with calendar and contacts that sync with the same data from the office. Android phone.6. Tracking and ability to wipe any mobile device that might be lost or stolen. Various products.7. Appropriate software, I use Office 365. Gives me the full Office Suite along with what I need to sync everything to everything else.8. If a litigator, potentially specialized litigation and presentation software. Powerpoint and AppleTV9. PDF creation software with signing ability, signNow or similar10. Lexis or Westlaw My law firm has Lexis. Specific tasks that lawyers can perform with the setup I gave you?1. Communicating with clients and other lawyers2. Drafting and editing documents3. Reviewing documents4. Filing documents with the court5. Conference calls by video or audio6. Marketing - blog posts, social media, answering questions on sites such as this7. Tracking time8. Creating bills9. Sending bills10. Checking and entering calendar information11. Create and organize court or seminar presentations12. Sign new clients13. Showing presentations in court or at seminars14. Legal researchAnything I can do inside my office, I can do outside my office. Except, of course, sit in a conference room with my co-workers. I also don't have a portable printer, but I use Acrobat and other tools that allow for electronic signatures on my iPad or touch screen laptop as well as marking up documents electronically.
-
What are some great free online tools for entrepreneurs?
There’s quite a lot out there, depending on what you’re looking for :)Some free online tools (in no particular order):Dropbox. Save and share everything.Evernote. Best note app ever.FreePik. Find thousands of free images.SurveyMonkey. Create surveys to gauge customer feedback.Rapportive. Useful tool for Gmail that allows you to see other people’s social media profiles.Trello. Project management made simple.Slack. Work communication simplified.AdCat. Allows you to use a single picture to get perfect-sized, up-to-date ad images for Facebook, Instagram, and Twitter. Free.Easel.ly. Great infographic generator for creating attractive content. Engaging content is vital for attracting audiences.Google Analytics. See who’s coming to your site and from where, among many many other awesome functions.Sidekick. Awesome email tool that tracks when emails are opened — super useful for proper follow-ups.Hotjar. Recordings of users on your website. Amazing to understand user behavior, which drives marketing strategies.Hootsuite. For social media management in one easy to use dashboard.Leadin by Hubspot. For lead management.Ahrefs. Powerful SEO tool.Later. Instagram consistently shows amazing engagement with users. This tool manages scheduling for you.Crowdfire. Great tool to figure out who to follow on social media for optimal engagement.BuzzSumo. Analyze what content performs best.Social Rank. Allows you to see which are your most valuable followers.UberSuggest. Free keyword suggesting tool.LinkMiner. Free tool for the link building strategy.JustsignNowOut. Finds journalists interested in covering you.Keyword.io. Free keyword research tool for SEO.MailChimp. To run automated email campaigns.Optimizely. A/B testing to optimize your website.Google Trends. Shows how often a particular search-term is entered.TweetDeck. Owned by Twitter, it makes discovering content easily digestible and allows you to find the topics and people you want.Title Maker. Content idea generator.Explore. Get to know what’s trending.Engage Master. Convert visitors to customers.Startup Bootstrap. Website building templates.Submit.co. Get press for your startup.SumoMe. Tool set to grow your website traffic.Quip. View documents on any device.Atomic Squirrel. Startup checklist.There’s tons more out there depending on what you are looking for specifically. I’m happy to update and reorganize if you need more :)Disclosure: I’m working on AdCat.
-
Which are the best companies for outsourcing software product development?
Many outsourcing companies get their talents from the top outsourcing destinations, mostly from Asia. One of which is the Philippines, a consistent lead outsourcing destination for years. Once dubbed as the “BPO Capital of the World”, the Philippines is home to a large pool of IT professionals.This is the reason why I set up my software development company. I believe the availability of highly skilled tech talents in the Philippines is a solution to the IT shortage in the UK and the US. I have met wonderful and simply talented people at my company Cloud Employee.Cloud Employee offers developers adept in several technologies. Check our services for a full list. The cheap labor the country offers equates to a more cost-efficient service price. Cloud Employee makes it possible to save up to 65%. Don’t believe me? Check our pricing.Aside from the available talent, what makes Cloud Employee stand out from the rest is the flexible hiring process and free trial. We let our clients be in full control of selecting which developer passes their standards. Of course, we make sure that the selection is in line with or exceeding their requirements. Clients also get a free trial to test the developers and to also have a glimpse of how we work at Cloud Employee. Know more about how we work.I’m proud to share that Cloud Employee has served several tech startups, SMEs, and even large IT firms in the UK, the US, and Australia. See what our past and current clients say about Cloud Employee.While you’re getting to know us, here are some helpful reads from our blog:7 Reasons Why You Should Bootstrap Your BusinessPH Remains Top Outsourcing Provider Despite Rising CompetitionTrump’s H-1B Reforms and What They Mean for Tech CompaniesCloud Employee Offers Alternative in the Midst of UK Hiring CrisisWhat To Expect From Big Tech Brands This 2018
-
How does the Coin universal credit card work?
A Dynamically Changing Electronic Payment Card Called CoinKanishk Parashar CEO of Coin [1] developed a $50 (currently) .84 mm card that stores eight payment methods that uses a dynamic programable magnetic strip that simulates the magnetic strip of a legacy payment card. The Coin app stores an unlimited number of payment card data in an encrypted manner that can be loaded into one of the Coin card memory locations. The Coin card is a Bluetooth Low Energy (BLE) device and is designed to communicate between the Coin card and Coin mobile app and has about a two year battery life.Part of the payment card magnetic strip 3 track data is read in to the Coin app by way of a very familiar device that resembles the Square card reader. The cardholder swipes the card and then takes a picture of the card as a visual clue to the card that is being used. At this point the image is not used to decode the card numbers and in most cases the card numbers are unreadable. However the image may serve as a confirmation of the information found on the 3 track data received by the card swipe. There has been rumors of a license from one of the companies that has perfected the decoding of credit card images.Once the payment card(s) are recorded they can then be deployed to the Coin card via Bluetooth. The Coin card has a three line LCD display that is controlled by an integrated button that scrolls through the cards that are currently present on the Coin card. The large center line of the LCD display shows a four character display that the cardholder selects as a memorable name for a particular payment card. The nine character lower LCD line displays the first eight digits of the payment card. The top line displays the sequential number of the cards stored in the device.Coin uses 128-bit SSL to the server and 256-bit encryption on the Coin card itself.The Coin TechnologyCoin is based on Sparkfun’s Arduino Pro Mini [2] running an Amtel ATmega328 [3] MCU operating at 8MHz and external resonator with an added Bluetooth Low Energy bridge, antenna, 3 line LCD screen, a magnetic strip simulator, mechanical low profile button and coin battery. Arduino [3] is based around an open-source single-board micro controllers with software that consists of a standard programming language compiler and a boot loader that executes on the micro controller. It is a useful platform for hobbyists and rapid development and prototyping. Prototype of the original Coin card, the magnetic strip simulator is the silver foil strip at top and the copper coil induction loop at the center.Block diagram of the Sparkfun’s Arduino Pro Mini board.Early Coin Arduino Pro Mini based circuit board pin out plansCoin At The MerchantThe card holder would select the method of payment by pressing the integrated button on the Coin card until the correct simulated payment card is selected. They would present the card to the merchant and Coin would generate via the internal coil a magnetic signal that simulates the same data that was read by the payment card reader and the three tracks of data. The induction coil actully drains battery quite rapidly and thus is only activated when a sufficient megnetic field is detected at the payment card terminal.If all goes to plan the legacy or new iOS/Android payment card processing solutions should register a positive transaction.An added benefit is the Coin card is electronically leashed to the smartphone via Bluetooth and will signal the app when it detects a distance separation. Thus one would be reminded to collect the card and even find the card. Coin And The Practical And Pragmatic MerchantThus far all of this sounds quite compelling and frankly very useful for most of us. However most merchants will be very skeptical about accepting what is clearly not a Visa, MasterCard, Discover or American Express card. They also would be very challenged by the rules and guidelines that all of the payment card issuers and payment card processors present to the merchant for detecting payment card fraud in the US with cards that have magnetic strips.Standard issue Visa branded merchant security features flyer. Standard issue MasterCard branded merchant security features flyer. Standard issue American Express branded merchant security features flyer. As old fashioned as this may sound the legacy payment card has a number of very clear security elements. These elements although seeming trivial, they are really quite important and useful:The payment card logoThe hologramThe raised numbers and raised card holder nameThe signature panelThe cardholder’s signatureThe reprinting of the payment card number and the CVV2 number in the signature panelThe expiration dateThus far Coin card does not have any of these security features. This may have an impact on acceptance at some merchants. All merchants agree to examine each payment card for these minimum security features. If the payment card companies can demonstrate that these features were not examined, they could hold the merchant, even though they swiped the card, 100% fully liable for any repudiation by the cardholder that results as a chargeback. This means the merchant could face losing the full amount of the transaction plus a penalty fee that can be from $25 to hundreds of dollars. They can reject acceptance of the card and in some circumstance retain the card under the Code 10 procedure. The Code 10 merchant procedure is a process for a card that is considered suspect:CALL FOR A CODE 10 AUTHORIZATIONCall your authorization center immediately and ask for a "Code 10" if:You believe you have a counterfeit or altered card.The transaction is suspicious.The account number is listed on the warning bulletin.The signatures don't match.You become suspicious for any other reason.You will be asked a series of "yes" or "no" questions. Hold the card while the operator gives you instructions.I would not suggest using this method to pay a $500 bar tab at a Texas Country Western saloon at 2 am until this type of system is rather mainstream. Hass and the boys may not like your “funny card”.Official Rulings And New TechnologiesThus far none of the payment card companies have presented an official ruling on systems like Coin card and may or may not endorse them. Time will tell. Unofficially it is my assessment that they are watching this closely and do not want to injure innovation but at the same time want to protect cardholders and merchants.Both MasterCard and Visa have experimented in this space before, not exactly Coin but moving in this direction. There are a number of patents that surround some of the methods used:All of the payment card companies will require merchants to have payment card terminals that can accept EMV and/or wireless EMV (NFC) by the end of 2014 or the merchant will risk full chargback liability. There will also be lower rates in the future for merchants that have deployed these upgrades. Thus over the next ten years we will see the magnetic strip being slowly deemphasized. This leaves this whole concept in a bit of a limbo. I can say that I personally will invest in just about all of these devices because I think they have merit. I have purchased a Coin card as well as competing systems.Quora has a resident expert on these types of systems and the challenges they face, Chris Bartenstein of Stratos (company). I am rather certain his practical and pragmatic insights on developing systems like Coin would be quite valuable.It is also important to understand that Apple will be entering into this space in a very unique manner.I Support Innovation And The Solving Of Real ProblemsI want to make it very clear, I think that Coin has created a very compelling product and I think they are at the correct price point and they really solve at least a short term problem. It is clear by the first three hours, sell out that there is a great deal of early adopter interest. It is my hope that great and innovative ideas flourish in payments. _____[1] Coin[2] Arduino Pro Mini 328 - 3.3V/8MHz[3] ATmega328[4] Arduino
-
What are the current topics for a paper presentation by an ECE student?
List of all Technical topics (ECE) in recent trend is given below :A Digital Speech Effects SynthesizerAdvanced Queue Management TechniquesAgent Mediated E-commerceAircarsAircraft GPS TrackingAmbiophonicsAn Electric BicycleLogin application in java using model view controller(mvc) and MySQL databaseAnatomy and working of search enginesAndroid a smart phone operating system by googleAnti-hiv using nano robotsApache hadoop introductionApplication of microcontroller in vehicle monitoring and security systemAqua communication using modemArtificial intelligence on expert systemsAn iPhone application for visualizing pollution mapsAnalysis of Minimum Energy Performance Standards (MEPS) for Domestic Electrical appliancesAnalysis on Performance of Freeware ToolsAndroid Operating SystemAnimatronicsAntenna Analysis Using Wavelet RepresentationsAnti-Jamming wireless systemsApplication of Genetic Algorithms in Network routingApplication of LED for Domestic ApplicationsApplications of Graph Theory to Metabolic PathwaysApplications of Soft Computing in Medical Image AnalysisApplications of speech recognitionApproximate string matching for Music retrievalARQ Schemes for Wireless Data CommunicationsArtificial EyeArtificial immune system.Artificial intelligence for speech recognitionAspects of Database Security and Program SecurityAttacks on Smart CardsAugmented RealityAuthentication and securing the systemsAutomated Network Address AssignmentAutomated Software Testing of ApplicationsAutomatic Device Driver Synthesis From Device SpecificationsAutomatic sound-based user grouping for real time online forumsAutomatic Video Surveillance SystemsAutonomic ComputingAutomatic Conveyor for Industrial AutomationAttendance Monitoring Intelligent ClassroomAn Automatic Mobile Recharge StationBidirectional Power Control for hybrid vehiclesBiomolecular ComputersBiometrics IRIS techniqueBio sensors (photonics)BiochipsBio-Medical Instrumentation and Signal analysisBiometric SecurityBiometric TechnologyBiometrics Based AuthenticationBio-Molecular ComputingBionic eye possible path toward artificial retinaUltrasonic Based Distance Measurement SystemWireless Advanced Flight Systems Aircraft Monitoring SystemBlade ServersBlue GeneBlue sat Communications ProtocolBlue-sat Radio Switching CircuitBluetooth Based Smart Sensor NetworksBrain computer interfaceBiomass gasifier for thermal and electrical applicationsBittorrent a revolution in p2p technologyBlue brainBlue eyes technologyBrain controlled car for disabled using artificial intelligenceBrain gateBrain port deviceBrain Finger Print TechnologyBrian Gate TechnologyBroadband via satellite to Rural AreasCapability Maturity Model Programming (CMM)Capacity of Ad-hoc Wireless NetworksVehicle Speed Sensing and Smoke Detecting SystemIntelligent Fire Sprinkler SystemCapturing packets in secured networksCarbon nano tube electronicsCDMA Wireless Data TransmitterCellular CommunicationsCellular Digital Packet DataCellular Neural NetworkCellular technologies and securityCarbon nanotubesChallenges in mobile ad hoc networks (manets)Cloud computingCloud computing concepts and designCensoring private information from network packet tracesChannel Allocation Algorithms for Mobile TelephonyGSM based Advanced Wireless Earthquake Alarm System for early warningIntelligent Wireless Talking Bus StopChannel Coding and Decoding for Mobile CommunicationsChannel Estimation in MIMO SystemsCharacterization of Piezoelectric ElementsChess AlgorithmChoreographyAqua communication using modemCircuit and safety analysis systemClassification, Clustering and Application in Intrusion Detection SystemClassification, Clustering and their Application for Damage Detection in MechanicalClustering Enterprise JavaCoding in high noise environmentsCold fusionCollaborative Mobile EnvironmentsCombined Input Output Queued SwitchesCompact peripheral component interconnect (CPCI)Compliers and its workingCompression and distribution of volumetric data setsComputational Geometry in Drug DesignComputational Intelligence and LinguisticsComputational neuroscienceComputational PhotographyComputer ForensicsComputer Viruses(Malwares, Trojons, Spywares)Computerized Paper Evaluation using Neural NetworkConcurrent Programming and Parallel distributed O.S.Condition Monitoring of Power System EquipmentConditional Access SystemContent Management Systems(WordPress, Joomla, Drupal etc)Continuously variable transmission (CVT)Control & Signal Processing Techniques in Financial EngineeringControl and Optimization Methods in Communication NetworksControl of a 3-d overhead craneControl of heterogeneous networksControl System Wireless InterfaceControlled multimedia recording environment for lectures and 3D.Controller design for a helicopter modelCooperative Adaptive Cruise ControlCross Platform Component Object ModelCrusoe ProcessorCryogenic ProcessorCryptography and N/W securityCryptovirologyCSS and DeCSSCT scanningCyber terrorismDeploying a wireless sensor network on an active volcanoDigital jewelryData Mining for Condition Monitoring of Power System EquipmentData mining through Active LearningDynamic Car Parking Negotiation and Guidance Using An Agent-Based PlatformGSM Real Time Street Light Control SystemsData over Cable System (DOCSIS)Data Pre ProcessingData Security in Local Network using Distributed FirewallsData ware hosuing & miningDatagram Congestion Control Protocol (DCCP)Dataset Query algorithms in Streaming MiningDelay-Tolerant NetworksDense wavelength division multiplexingDesign and development of a programmable alarm systemDesign of a wireless sensor board for measuring air pollutionDesign of Amplifier for recording of Nerve SignalsDesign of an all Electric Steering WheelDesign of diamond-based Photonics devicesDesign of IC Amplifiers for touch SensorsDesign of Low Density Parity Check CodesDetermination of efficiency of the Permanent Magnet MotorsDeveloping a own server systemDevelopment and Control of Humanoid robotDevelopment of a Broadband Tunable Fiber LaserDevelopment of a New Sensor for Detecting Partial Discharge Induced PressureDevelopment of a wind-turbine simulatorDevelopment of new sensors for online monitoring of partial dischargesDigit recognition using neural networkDigital Audio BroadcastingDigital Audio Effects Control by AccelerometryDigital Camera Calibration and Inversion for Stereo iCinemaDigital Neurons for Digital BrainsDigital Signal Processing and their applicationsDigital silhouettesDigital theatre systemDirect to home television (DTH)Direct Torque and Flux Control of IPMSMDistance learning systemsDomain name servers [DNS]Driving Optical Network EvolutionDual Energy X-ray AbsorptiometryDynamic Cache Management TechniqueDynamic Memory Allocation(malloc, calloc, NEW etc)Dynamic resource allocation in Grid ComputingDynamic source routing protocolDynamic Virtual Private NetworkEarth Simulator- Fastest SupercomputerEffects of large scale integration of PV systems on the distribution networkEfficiency / Comparative study of routing schemes in event based systemsElectromagnetic Applications for Mobile and Satellite CommunicationsElectromagnetic launching systemElectromagnetic processor fabricationElectronic nose & its applicationElliptical Curve Cryptography(ECC)Embedded Configurable Operating systemEmbedded system in automobilesEmbedded systems and VLSI an architectural approach to reduce leakage energy in memoryEmbedded web server for remote accessEmbryonics approach towards integrated circuitsEmergency Health Care SystemEmerging trends in robotics using neural networksE-MINE: A novel web mining approachEncrypted Hard disksEncrypted Text chat Using BluetoothEncryption Decryption MethodsEnergy-efficiency and Layer Integration in Wireless NetworksEnterprise SecurityEqualization of room acoustics for audio reproductionEthernet Passive Optical NetworkE-Toll tax fixingEvolution Of Embedded SystemeXtensible Bindings Language (XBL )Electronic waste (e-waste)Embedded web server for industrial automationEyegaze systemFuel saver systemGoogle autonomous carFeatures of Qualcomm Snapdragon processorGuarding distribution automation system against cyber attacksFace detection technologyFacility Layout Design using Genetic AlgorithmFalls detection using accelerometry and barometric pressureFast Convergence Algorithms for Active Noise Controlling VehiclesFault Tolerance in Virtual Machine EnvironmentsFault tolerant Routing in Mobile Ad-Hoc NetworkFerroelectric RAMFine Grained DataBase SecurityFine-grained Access Control in DatabasesFingerprint recognition system by neural networksFinite Element Interface (FEI)Flexible CRT DisplaysFluorescent Multilayer Disc (FMD)Fluorescent Multilayer Optical Data StorageForecasting Wind PowerFractal image compressionFractal robotsFree Space Laser Communicationsfully digital class-D amplifiersFully Integrated Amp-Meter for Electrical SimulatorsFunctional Magnetic Resonance ImagingFuture of the internetFuture Programming Techniques and ConceptsFuzzified Computer-Automated Crane Control SystemFuzzy Logic Control for complex systemsGaming interfaces applied to videoconferencingGeneral Packet Radio Service (GPRS)Generic visual perception processorGeographic information systemGeometric Invariants in Biological MoleculesGIS tools for web applicationsGlobal positioning response systemGSM Digital Security Systems for PrinterVoice Operated Intelligent Fire Extinguisher VehicleGlobal Positioning SystemGlobal System for Mobile Communication (GSM)Google Android- Mobile OS from GoogleGrasshopper Operating SystemGroupware TechnologyGSM Security And EncryptionHandfree driving [auto]Hardware EDAC for Harsh EnvironmentsHardware implementation of background image modelingHAVI: Home Audio Video InteroperabilityHawk Eye – A Technology in sportsHigh Altitude Aeronautical PlatformsHigh Performance ClustersHigh Performance ComputingHigh Performance DSP ArchitecturesHigh Speed Circuits for optical InterconnectHigh Speed Data in Mobile NetworksHigh speed LANs or InternetHolographic Data StorageHolographic MemoryHolographic Versatile DiscHolt-Winters technique for Financial ForecastingHomeRF and Bluetooth: A wireless data communications revolutionHot Spot TechnologyHyper thread imaxHyper thread technologyHyper Transport TechnologyHow does a search engine work ??How does google search engine work ??How to create a website using wordpressHuman computer interaction & its futureDesign of a color Sensing System for Textile IndustriesGSM based Path Planning for Blind Person Using UltrasonicImage retrieval using compact binary signaturesVehicle Monitoring and Security SystemImbricate cryptographyImplementation of hamming codeIntroduction to microcontrollersIntroduction to AirfoilIntrusion detection and avoidance systemIC Amplifier Design for Touch SensorsImage transmission over WiMax SystemsImage WatermarkingImplantable on-chip Power SuppliesImproving TCP performance over mobile ad hoc networksIndustrial Applications using Neural NetworksInformation Extraction from structured & Semi-structured dataInformation Extraction modes & techniquesInfrared Remote ControlInnovative Application Development using J2EE ArchitectureIntegrated Circuit Design for Biomedical ApplicationsIntegrated Optical Chip DesignIntegrated Voice and Data transfer & handlingIntegrating Structural Design and Formal Methods in Real Time System DesignIntegrating Wind Power into the Electricity gridIntegration of Parallel Database in a Service Oriented ArchitectureIntegration of wind and solar energy in smart mini gridIntel centrino mobile technologyIntelligent calling bellIntelligent navigation systemIntelligent Patient Monitoring SystemIntelligent RAM : IRAMIntelligent Software AgentsInteractive Voice Response SystemInternet Access via Cable TV NetworkInternet architecture and routingInternet Protocol duplicate address detection and adaptationIntrusion Detection SystemInvestigation into solar thermal/coal driven power stationsInvestigation of the real-time implementation of learning controllersIP spoofingIP re-director featuresiOS 8 featuresIPODSIris ScanningiSCSI: The future of Network StorageISO Loop magnetic couplersJava Cryptography Architecture (JCA)Java Messaging Service (JMS)Enterprise Messaging Service (EMS)Advantages of EMS over JMSJava BeansJIRO Java-based technologyLaser Power SupplyJmeter toolGEMS tool for EMSLess characterization of ferromagnetic material for non-sinusoidal excitationLight emitting polymersLoad balancing and Fault tolerant serversLight Interception Image AnalysisLight TreeLightning Protection Using LFAMLiquid Crystal on Silicon Display (LCOS)Location estimation and trajectory prediction for PCS networksLong baseline motion estimationLotus Notes/DominoLow power filter design for mobile communicationLow Power UART Design for Serial Data CommunicationLow-Power Microelectronics for Biomedical ImplantsLow-Power Oscillator for ImplantsMagnetic Random Access MemoryManaging Data In Multimedia ConferencingMango- new mobile from MicrosoftMicro chip production using extreme uv lithographyMicrosoft NetMeetingMigration from GSM network to GPRSMining the Web: Searching, Integration and DiscoveryMobile Virtual Reality ServiceMobility Modeling and trajectory prediction for next generation PCS networksModeling of current spread through electrode geometries in implantable hearing deviceModeling of wind turbine system for an Interior Permanent magnet generatorMoletronics- an invisible technologyPower generation through Thermoelectric generatorsMulti Protocol Label SwitchingMulti user Scheduling for MIMO broadcastingMultiple clients communicationMultiple Domain OrientationMultisensor Fusion and IntegrationNeuro chipsParasitic computingPassword paradigmsPolymer memory a new way of using plastic as secondary storageProgrammable logic devices (PLD)Navigation of Mobile Wheeled RobotsNerve Signal Measurement Electronics for Biomedical ImplantsNetwork Attached Storage (NAS)Non Volatile Static RAMOptical coherence tomographyOptical to electrical converter for optical interconnectOptimization of Ad Hoc Wireless Sensor NetworksOptimization of Protocol Stack for wireless networksOracle RDBMSOutdoor High Voltage InsulatorsOvonic Unified MemoryPersonal Satellite assistant SystemsPH Control Technique using Fuzzy LogicPhone Busy IndicatorPivot Vector Space Approach in Audio-Video MixingPlastic chips & electronicsPluggable Authentication Modules (PAM)POF Tunable Fiber LaserPOP Plaster Of ParisPower Efficiency and Security in Smart HomesProactive Anomaly DetectionPrototype System Design for TelemedicinePublic Key Encryption and Digital SignatureQoS in Cellular Networks Based on MPTQoS in Networking using active NetworksQOS in software server FirewallsQuad-Core ProcessorsRadio Frequency Identification (RFID)Real time communication in wireless sensor networksReal Time Operating Systems on Embedded ICsReal Time Speech TranslationReal Time Systems with Linux/RTAIReliable and Fault Tolerant Routing on Mobile Ad Hoc NetworkRenovating the Address Resolution Protocol (ARP)Revolutions in the Operating System and ServersRobotic SurgeryRoom Equalization for Audio ReproductionRuby on Rails [RoR]Radio frequency identification technologyRapid prototypingSecured webportal for online shoppingSecuring underwater wireless communication networksSecurity analysis of micropayment systemSecurity aspects in mobile ad hoc network (manets)Security requirements in wireless sensor networksSemantic webSensitive skinSnake robot the future of agile motionSoftware defined radio(sdr)Spwm technique for multilevel inverterStorage area network(SAN)SwitchgrassSystem on chipSALT (Speech Application Language Tags)Sand Box TechnologySecurity of Open-Source SoftwareSecurity On Wireless LAN Adaptive cruise controlSecurity threats in the World Wide WebSensor fusion for video surveillanceSensors on 3D DigitizationSession Initiation Protocol (SIP)Shallow water Acoustic NetworksShort Message Service (SMS)Significance of real-time transport Protocol in VOIPSimulating Quantum CryptographySimulation of low-power converter for electromagnetic vibration driven generatorSingle photon emission computed tomographySmart camera for traffic surveillanceSmart Cameras in Embedded SystemsSmart FabricsSnickometer A toolSocket ProgrammingSoftware advances in wireless communication(Cognitive Radio, Dynamic spectrum Access etc. )Software Testing & Quality AssuranceSpace MouseSpace RoboticsSpectrum Sharing in Cognitive Radio NetworksSpeech Enhancement for Cochlear ImplantsSpeech Enhancement for Mobile ApplicationsSpeech transmission over WiMax systemsSpeed Detection of moving vehicle using speed camerasSPINS -Security Protocol For Sensor NetworkSplit Range SynchronizationStealth VirusSurface-conduction Electron-emitter Display (SED)Swarm intelligence & traffic SafetySynchronous Optical NetworkingSynthetic Aperture Radar SystemSystems Control for Tactical Missile GuidanceTesting methods (Stress, Black-Box, White-Box, Performance Testing etc )The Architecture of a Moletronics ComputerThe Tiger SHARC processorThermal infrared imaging technologyThought Translation Device (TTD)Time Shared O.S.Tracking and Positioning of Mobiles in TelecommunicationTrends in Compiler ConstructionThree-dimensional password for more secure authenticationUltrasonic motorWearable biosensorsWeb-miningTraffic Light Control SystemMulti-Channel Infra Red Remote ControlMagic lightsZigbee Based Wireless Sensor Network for Sewerage MonitoringWireless integrated network sensorsUbiquitous NetworkingUltra Low-Power Microphone Pre-AmplifierUltra Low-Power Radio Receiver for Biomedical ApplicationsUltrasonic detector for monitoring partial dischargeUltra-Wideband CommunicationUMA (Unlicensed Mobile Access )Vector – LDPC Codes for 3G Fading ChannelsVirtual SurgeryWideband Spectrum Sensing for Cognitive Radio SystemsWireless Computer Communications Using Sound WavesLink available for getting details about some topic. You can search internet for getting details about the remaining topics.Hope this helps you :)
Trusted esignature solution— what our customers are saying
Get legally-binding signatures now!
Related searches to Create Electronic signature Presentation Mobile
Frequently asked questions
How do i add an electronic signature to a word document?
How to create an electronic signature in paint?
Ptcas what is better electronic signature or document?
Get more for Create Electronic signature Presentation Mobile
- How Do I Electronic signature Pennsylvania Police Form
- How Can I Electronic signature Pennsylvania Police Form
- Help Me With Electronic signature Pennsylvania Police Form
- How Can I Electronic signature Pennsylvania Police Form
- Can I Electronic signature Pennsylvania Police Form
- Can I Electronic signature Pennsylvania Police Form
- How To Electronic signature Pennsylvania Police PPT
- How Do I Electronic signature Pennsylvania Police PPT
Find out other Create Electronic signature Presentation Mobile
- Renew registration ny form
- California emissions hang tag form
- Islamabad driving license verification form
- Sker vatten intyg mall form
- Additional insured endorsement form fillable
- The infectious diseases act chapter 137 form
- Soc 453 form
- Petty cash log form
- Astm d4832 pdf form
- Victim impact panel arkansas form
- Ct 3m4m form
- American linear units form
- Molst form
- Inheritance gizmo answer key form
- Transamerica wellness claim form
- Verb worksheets for grade 3 form
- Financial disclosure form 201678
- Vmou defaulter form
- Wells fargo direct deposit form
- Ch robinson carrier setup form