Remove eSignature Form Secure
Make the most out of your eSignature workflows with airSlate SignNow
Extensive suite of eSignature tools
Robust integration and API capabilities
Advanced security and compliance
Various collaboration tools
Enjoyable and stress-free signing experience
Extensive support
ESign Form for Legal Myself
Keep your eSignature workflows on track
Our user reviews speak for themselves






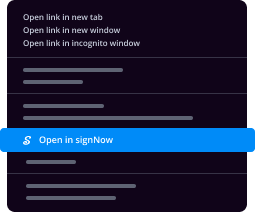
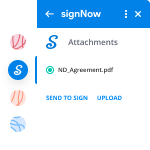
Remove eSignature Form Secure. Explore one of the most customer-warm and friendly knowledge of airSlate SignNow. Manage all of your record handling and sharing process digitally. Change from hand held, paper-dependent and erroneous workflows to automatic, digital and flawless. It is possible to make, provide and indicator any documents on any gadget anyplace. Ensure that your airSlate SignNow organization cases don't fall over the top.
Discover how to Remove eSignature Form Secure. Adhere to the straightforward guideline to begin:
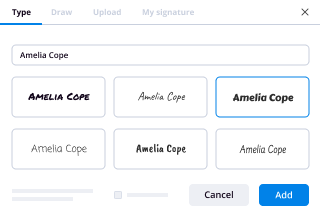
- Design your airSlate SignNow profile in clicks or log in with the Facebook or Google profile.
- Enjoy the 30-day time free trial version or go with a costs strategy that's ideal for you.
- Locate any legal template, build on-line fillable varieties and share them securely.
- Use superior features to Remove eSignature Form Secure.
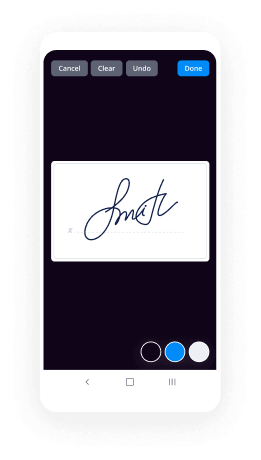
- Signal, personalize putting your signature on purchase and collect in-man or woman signatures 10 times faster.
- Establish automatic reminders and receive notifications at each and every phase.
Transferring your jobs into airSlate SignNow is easy. What comes after is a straightforward approach to Remove eSignature Form Secure, along with recommendations to maintain your colleagues and lovers for better partnership. Inspire the employees using the best resources to stay on top of business processes. Enhance efficiency and size your company quicker.
How it works
Rate your experience
-
Best ROI. Our customers achieve an average 7x ROI within the first six months.
-
Scales with your use cases. From SMBs to mid-market, airSlate SignNow delivers results for businesses of all sizes.
-
Intuitive UI and API. Sign and send documents from your apps in minutes.
A smarter way to work: —how to industry sign banking integrate
FAQs
-
Are digital signatures authentic? How does this system work?
Laws vary by jurisdiction. Check your local laws.Colorado Electronic Signature ActIn Colorado, electronic documents and electronic signatures may be used in transactions where the parties have agreed to conduct transactions by electronic means.The law applies to any electronic record or electronic signature created, generated, sent, communicated, received, or stored on or after May 30, 2002.In any written communication in which a signature is required or used, any party to the communication may affix a signature by use of an electronic signature that complies with the requirements of Colorado law for electronic signatures.“Electronic record” means a record created, generated, sent, communicated, received, or stored by electronic means.“Electronic signature” means an electronic sound, symbol, or process attached to or logically associated with a record and executed or adopted by a person with the intent to sign the record.“Security procedure” means a procedure employed for the purpose of verifying that an electronic signature, record, or performance is that of a specific person or for detecting changes or errors in the information in an electronic record. The term includes a procedure that requires the use of algorithms or other codes, identifying words or numbers, encryption, or callback or other acknowledgment procedures.An electronic record or electronic signature is attributable to a person if it was the act of the person. The act of the person may be shown in any manner, including a showing of the efficacy of any security procedure applied to determine the person to which the electronic record or electronic signature was attributable.Colorado also allows electronic notarization (e-notary). If a law requires a signature or record to be signNowd, acknowledged, verified, or made under oath, the requirement is satisfied if the electronic signature of the person authorized to perform those acts (e-notary), together with all other information required to be included by other applicable law, is attached to or logically associated with the signature or record. The notary attaches a Document Authentication Number (DAN).The federal law “Electronic Signatures in Global and National Commerce Act”, is found in 15 U.S. Code section 7001.Block-chain cybersecurity technology is used for digital cryptocurrency such as Bitcoin and may be used for sending and authenticating electronic documents.
-
When government introduces digital payment all over India, what would be the challenges faced by Rural areas? How will GOI overc
There are 5 key challenges to government’s policy on going cashless in India:Tech literacy - even reasonably educated often get stumped with many of the technologies.Tech coverage - India’s cellular internet coverage [3G/4G] is not that good and so is the smartphone penetration.Financial inclusion - Many don’t have easy access to banks, ATMs, Point of Sale terminals etc.Transaction fees - the existing players like Visa and Mastercard charge exorbitant fees especially for smaller transactions.Enforcing tax rules - In India, most shopkeepers escape from paying taxes as the rules are complicated and taxes are high. Getting them to comply is going to be hard.Here are ways to tackle this:Remove all taxes & duties involved in the import and sale of smartphones & data gear.Incentivize the aggressive rollout of data coverage and increase the government funds for supporting cellular/satellite data coverage in remote areas.A one-time subsidy of Rs. 1000 to a rural poor to buy a smartphone complying with government’s rules on Aadhar & digital signatures. They could buy this with their Aadhar card and the manufacturers could be forced to pre-install UPI app [instead of their usual bloatware] with a firmware tied to the person’s Aadhar. Since the entry level smartphones could come down to Rs. 2000 with the scale and without the import duties, most poor people could afford this. How do you define a poor? Now, that demonetization is done, you know how much each person has in their bank accounts. Anyone who has deposited less than Rs. 25000 should qualify [in fact, all future subsidies should be based on this - as that would punish those who use their accounts to deposit other people’s money].Carrying your smartphone should be like carrying your id - used carefully and universally. That means women who are denied their phones [due to their local/family compulsions] will get the access too.Build a new app to access all government services in one place in their native language driven mostly by voice and icons. A person should be able to open up the app and access forms, get food rations, banking services etc. Have this app pre-installed in the government smartphones.Have the third app for reporting all kinds of issues with governance with location tracking- school closed, ration rice not available, road broken, drainage issues etc. This app again comes pre-installed and the data from this should be audited by a separate government body and data should be made available to all.Have free wifi & usb charging stations in all ration shops, post offices, railway stations and other government offices. A person coming to do transaction with the government could be encouraged right there to use their new smartphone to buy train unreserved tickets, food rations, postal stamps etc. Cut the existing counters by half and use the staff to teach the people coming in.Embark on a massive tech literacy program. Rope in companies that can go around rural India and teach people basics of Internet, e-commerce and mobile wallets with their new smartphone. Emphasize the importance of passwords and secrets. Most in rural India can get it quite intuitively if told properly. Maybe a subsidy of Rs. 100 per person in rural India for the basic class.For the first year of that new person’s smartphone usage, the government could subsidize their basic data plan - say Rs. 30/month. You can rope in companies like Facebook, Microsoft, Google, Amazon, Paytm, Ibibo and Flipkart to foot in part of the budget for this [with no strings attached on what sites they could use].For any mobile payment transaction below Rs. 100 there should be no transaction fees by law and banks should be asked to bear the costs. The shopkeepers who still don’t accept cards after that time could be reported for tax evasion.Have a separate fund for improving online security. The government should insure all the poor in this new plan to avoid them being liable for hacks and data thefts. They should also fund new encryption algorithms and end to end security of transactions.The government should plan this so aggressively that it should achieve all this by the end of 2017. It is ambitious, but possible. The budget is less about Rs. 80000 crores [40 crore rural poor * Rs. 2000 for the total cost of all subsidies above] and could be easily paid with the RBI’s profits from demonetization [even if 95% of black money comes back to the banks].Imagine having the rural poor able to use their new smartphones for better news access, weather coverage for farming, getting notification on impending disasters like cyclones, access education programs, access all government forms, get government loans that they qualify for etc. Imagine that world and all of that is within hand’s signNow.It is the beginning of a new India. Jai Hind!See other India dreams here: India Dreams Collection by Balaji Viswanathan
-
How do I register a startup in India? How much money and time does it take? If am currently only 17, what issues will I face dur
Algorithm for starting a Private Limited Company: Engineer's View Personally I believe, If someone is starting a company with long term perspective or to bring some change through their unique Product/Services, one must go for Private limited firm. Prime reason for this is easy to raise funds from Angels/VC in case you go for investment. Step 1. Registration of Company 1. Name Selection: Check whether your desired company name is available or not at MCA website [ http://www.mca.gov.in/ ]. Name must be unique & must resemble with business you intend to do (highlighted one). EX: Arihant Labs Retail Services Pvt. Ltd 2. Registration of Name at ROC: Name approval usually takes maximum of 14 days. This is done online through MCA website. Moreover, you need to apply with at least 4 names for approval with a writeup about significance of names with main business of the company. 3. 1. Documents Required: 2. 1. Options for names for the proposed Company (on the basis of preference) 2. Amount of Share Capital; proposed shareholding ratio 3. A paragraph on the proposed major line of business of the company (main objects) 4. City of Registered Office. 5. Copy of ownership deed/sale deed(if property is owned) 6. Copy of rent agreement with NOC (if property is rented) 7. Copy of latest electricity bill/telephone bill/mobile bill for both directors 8. Copy of latest electric bill/telephone bill for the registered office proof. 4. Obtaining DIN & DSC: 5. 1. Documents Required 2. 1. PAN Card copies for directors and shareholders. 2. Voter ID/Passport/Driving License for directors and shareholders. 3. Occupation of the Directors for directors and shareholders. 4. E-Mail IDs of all directors and shareholders. 5. Phone Numbers for all directors and shareholders. 6. Photos for directors and shareholders 6. Company Incorporation: After above mentioned formalities have been completed, we need to file following forms/docs in Rs 100 stamp paper: 7. 1. Affidavits for non- acceptance 2. INC 9, INC 10 3. DIR 2 4. NOC : This is required to be filed by the owner of the property on which your company will be situated. 5. Subscriber Sheets of MOA & AOA 6. Documents required for filling MOA & AOA 7. 1. Must be filled on OWN handwriting 2. Passport size photos 3. Sheets needs to be witnessed by CA/CS/Advocate Step 2. Obtaining PAN/TAN: After company gets incorporated, you may apply for PAN/TAN. Step 3. Trade Licence in case you are selling PRODUCTS: This is required in some places for carrying out sales. You can obtain this from local Municipality. Step 4. VAT/CST registration for selling Products: For selling intra-state, you need VAT registration & for selling inter-state, you need to register for CST. 1. Documents Required: 2. 1. Trade Licence 2. Company Incorporation Certificate 3. PAN card of company as well as of all the directors 4. Proof of residence of Directors 5. Proof of occupancy of place of business (Rent agreement/ ownership deed, Rent Bills etc) 6. MOA & AOA of company 7. Current Account in the name of company in any national bank Step 5. Service tax registration for Service Industry: In India, you need to pay service tax of 14.5% on every services you have charged customer for. 1. Documents Required: 2. 1. Company Incorporation Certificate 2. PAN card of company as well as of all the directors 3. Proof of residence of Directors 4. Proof of occupancy of place of business (Rent agreement/ ownership deed, Rent Bills etc) 5. MOA & AOA of company 6. Current Account in the name of company in any national bank That's All folks! Your STARTUP is up to Conquer the World. UPVOTE & SHARE your views/issues We at labkafe [ http://labkafe.com/ ], prefer taxmantra [ http://taxmantra.com/ ] for our legal requirements.
-
What is the full procedure of TCS from the offer letter to joining?
TCS ( ILP ) joining process and document preparationThe most important part of joining TCS is its documentation! This is just a general guide to the new ILP candidates. You should always strictly follow your Annexure ! So let’s do this fast!The Joining Process is Divided into seven parts:1.Accept the joining letter2.Complete the TCS Survey Monkey3.Complete the BGC form filling4.Fill the NSR (NASSCOM) ITPIN5.Fill the ON BOARDING forms6.Prepare the Agreements (Service Agreement & Affidavit/signNowd Undertaking)7.Prepare the supporting documentsAccept the joining letter:a). First you have to accept your joining letter by using your DT reference idTCS Next Step>>ILP corner>>Joining letter>>Acceptb). Download the Joining letterTCS Next Step>>ILP corner>> Joining letter >>DownloadNote: Accepting the joining letter is necessary to complete the other formalitiesSo first accept your joining letter (if you are going to join TCS)Complete the TCS Survey MonkeyYou have to complete the TSC survey monkey. TCS recruitment team will send you the link by mailRequired details:1. TCSL Reference id (DT reference id)& passwordhttps://www.surveymonkey.com/r/T...Complete the BGC form filling:You have to complete the Background Check Verification Before Your Joining datea). Fill BGC Form:i). Fill the Basic Details (Passport, PAN, Address Details)ii). Academic Details (CGPA or overall percentage)iii). Reference: You have to fill any two person’s following detailsØ NameØ Company/Institute NameØ DesignationØ Contact NoØ Email idØ Relationship with the applicantØ Period for which reference knows the applicantiv). Fill Security Detailsb). Declaration:Ø In declaration part you have to agree and submitØ Download the BGC completed formc). Documents uploading:You have to scan and upload the following documents in PDF or JPEG format each file size should be less than 2MBØ NSR e-cardØ Birth certificate or Birth AffidavitØ Permanent, present address proof(aadhaar / passport / ration card / EB, GAS, mobile Bill / credit, debit card / Bank statement)Ø PAN cardØ Passport / passport application receiptØ ID proof (voter id, ration card, driving license, bank passbook, aadhaar)Ø X- grade mark sheetØ XII-grade mark sheetØ All semester mark sheetsØ Non-Criminal Affidavit (first page of the stamp paper)Fill the NSR (NASSCOM) ITPIN:You have to enter your NSR ITPIN atTCS Next Step>>ILP corner>>National skill registry>>ITPIN(you have to complete the registration and bio-metric process of NSR before joining ILP (please visit site www.nationalskillsregistry.com). And they will send you a NSR-e card by mail or you can generate by yourself by login to your NSR profile)Fill the ON BOARDING formsYou are mandatorily required to fill and submit the Onboarding Forms before your joining date to smoothen your Onboarding process, failing which your joining formalities will not be completed. These forms are required to be filled as per statutory compliance norms.Onboarding forms consists of five forms:Ø Provident Fund (PF)/ Pension Scheme Nomination form (Form 2 — Part A and Part B)Ø Gratuity Form (GF)Ø Superannuation Form (SF) -only to eligible employeesØ Declaration Form (Form 9)Ø Group Life Insurance (GLI)You would have to fill all the Onboarding forms online and declare nominee(s) for the above mentioned forms. Submit a Hard copy of the completed forms on the day of Joining ILPTCS Next Step>>Onboarding>>Fill all the formsAfter filling these form, you can download these 5 documents at “Dashboard tab”-in the same pageSuggestion: 1. nominee is father or mother 2. share of money -100%Required information: Name, DOB of the nominePrepare the Agreements (Service Agreement & Affidavit/signNowd Undertaking):a) Service Agreement:1.Buy a Rs.100 stamp paper on your name2.Print the service agreement page 1Download.pdf3.Buy 5 demi (court paper) / green paper (court paper) / Legal / A4 papers4.Print the service agreement page 2 – 6 Download.pdfNote: page 6 is also called as surety verification formNote: Blanks should be written using pen it should not print or typeIt doesn’t matter how many pages in your agreement but make sure that proper page number and proper contentOther instructions:If Rs.100 stamp paper is not available, you can also do this in two Rs.50 stamp papers Make sure the text starts in the stamp paper. You can print first 3 Lines on first Rs.50 stamp paper and next some paras on another Rs.50 stamp paper and the remaining pages on other demi paper.Read the service agreement guidelines carefully before filling up anything. Many might find this silly but I prefer filling up Xerox copies first. It can save you the money for printing again in case something goes wrong! So we are here going to use a Rs.100 stamp paper for the first few lines(THIS AGREEMENT made at Mumbai on this 1.______________________________________ day of 2._________________, Two thousand and 3._______________________ between TATA CONSULTANCY SERVICES LIMITED,)and print the rest on simple A4 papers or Legal or demi papers. Fill everything up in CAPS, using a pen. Do not remove any clause, not even the page numbers! Don’t forget your signature and surety’s signature on the bottom of each page!! Service Agreement needn’t be signNowd.Surety Verification:This is a part of the Service Agreement. Any person who is an Income Tax Payee or has Land property can be your surety! Example: your father! So just make sure you place the signatures in proper places and have your surety fill up the “Surety Verification Form”. This form has to be attested by a Gazetteer Officer or the manager of a nationalized bank where the surety holds an account or employer of the surety! or public notaryØ Attested photocopies of the surety’s pan card.Ø Attested photocopies of the surety’s Form 16 (or) Attested photocopies of the surety’s latest income tax returnNOTE: Make sure your surety’s signature everywhere matches with that done in his/her Pan Card or you are in some serious troubleb) Non-Criminal Affidavit:1.Buy a Rs.100 stamp paper on your name2.Print the Non-criminal affidavit page 1 Download.pdf3.Buy 2 demi (court paper) / green paper (court paper) / Legal / A4 papers4.Print the Non-criminal affidavit page 2 – 3 Download.pdf5.Get this affidavit signNowd by a notary public in court (signature in all the pages)Note: Make sure you choose non-blood relation people as witnesses! Example: Neighbors.Other instructions:If Rs.100 stamp paper is not available, you can also do this in two Rs.50 stamp papers Make sure the text starts in the stamp paper. You can print first 2 paras on first Rs.50 stamp paper and next some paras on another Rs.50 stamp paper and the witness page on another demi paper. just fill in the blanks with a pen DO NOT remove any clause.Prepare the supporting documents:1. Medical Certificate:Download medical certificate format from TCS next step portal and print it (Black & white is enough) Make sure The doctor signs and places his seal on the second page. He should also sign and place a seal on your photo. format download.pdfYou’ll need two attested copies of everything but make sure you keep more copies with you (many times it will help you)Here’s a list of the supporting documents you’ll need to get attested by:Ø Gazetteer Officer orØ Government higher secondary school head master orØ Tehsildar of the village in which the Applicants resides. orØ District collector of the district in which the Applicants resides1. Birth Certificate:(If your birth certificate is not in English, or your name/place of birth/date of birth is missing/the details are mismatching, then it is recommended that you apply for a new one before it’s too late.Otherwise, you need a signNowd affidavit on Rs.100 stamp paper, which is only atemporary arrangement.)2. Class X - mark sheet.3. Class XII-mark sheet.4. Consolidated Mark sheet (from your institution)5. Degree Certificate(or Provisional Certificate / course complete Certificate if you. Don’t receives your Degree Certificate yet)6. All Semester Mark sheets7. Transfer certificate (if you have)8. Your Pan Card9. Your Passport10. surety’s information:a) If Income tax payee : photocopy attestedi). Surety’s Form 16 ( or )Surety’s Income Tax Return / saral / form 2d / form12Bii). Surety’s PAN cardb) If Surety have landi). Surety’s land documents photo copy – Registered in Englishii). Latest land valuation certificate from the respective authority-photo copy with attestedc) Else Fixed deposit of Rs. 50,000 at nationalized bank on TCS name for two years) photocopy attested by bank manager11. your aadhaar card (if you have)12. your voter card (if you have)13. Ration card (if you have)You’ll need two self-attested copies of Following documents but make sure you keep more copies with you (many times it will help you)1. Joining letter2. Offer letter3. ID proof (Passport, Voter ID)4. Address Proof (Passport, Voter ID)- give a separate copy for permanent & (if Present) address5. Highest degree mark sheets (for BGC)6. Degree Certificate / Provisional / Course complete (if only degree certificate not provided byyour institution)(for BGC)7. NSR e-card printout (after you’re done with Biometrics, you’ll get your ITPIN and e-card with your picture, in your e-mail).8. Documents for break in education (if any otherwise no need)(i) Medical records, if the break was due to medical reasons.(ii) Certificates / Examination results, if the break was due to additional course done.(iii) Affidavit on a Rs.100 stamp paper with notary authorization, if the study break was due to other personal reasons.9. CID Form (if you are from Mumbai/ Navi Mumbai/ Thane City/ Thane Rural / Pune otherwise no need) You need to submit Self-Attested Criminal Investigation Division (CID) forms forthe respective region. (details about forms will be mailed to you just before your joining)10. 12+ copies Recent passport size photos11. All the documents Original compulsory. Don’t forget to take the originals with you!Advise: keep more copies of your documents and attested copies it may help you if any problem
-
Is it mandatory to get photos clicked in a registered address as per e-Form Active INC 22A?
Dear Friends,The ministry of corporate affairs (MCA) in its drive to tackle FRAUD companies’ have unveiled the Companies (Incorporation) Amendment Rules, 2019 vide its notification dated 21 February 2019, thereby amending the provisions of Companies (Incorporation) Rules, 2014 (the Rules).MCA (Ministry of Corporate Affairs) The rules shall come into force from 25 February 2019 —-II. Active Company Tagging Identities and Verification (ACTIVE).BackgroundThe government has launched a sustained campaign in the last four years against black money and has taken several bold steps including constitution of the special investigation team on black money, enactment of the ‘Black Money (Undisclosed Foreign Income and Assets) and Imposition of Tax Act, 2015’, income declaration scheme, 2016, Benami Transactions (Prohibition) Amendment Act, 2016 and the demonetization scheme.The task force was mandated to check in a systematic way, through a coordinated multi-agency approach, the menace of companies indulging in illegal activities including facilitation of tax evasion and those commonly referred to as ‘shell companies’. Its members included the department of financial services, the Central board of direct taxes (CBDT), Central Board of Excise and Customs (CBEC), Central Bureau of Investigation (CBI), Enforcement Directorate (ED), Serious Fraud Investigation Office (SFIO), Financial Intelligence Unit – India (FIU-IND), the Reserve Bank of India (RBI), the Securities Exchange Board of India (SEBI), the Director General of Goods and Services Tax Intelligence (DG GSTI) and the Central Economic Intelligence Bureau (DG-CEIB).In a drive carried out under the supervision of the MCA in FY2017-18 the registrars of companies (ROCs) identified and removed from the register of companies under Section 248 of the Companies Act, 2013 the names of 2,26, 166 companies, which had not filed their financial statements or annual returns for a continuous period of two or more financial years. As many as 3,09,619 directors were also disqualified under Section 164(2)(a) read with Section 167(1) of the Companies Act, 2013 for non-filing of financial statements or annual returns for a continuous period of immediately preceding three financial years (2013-14, 2014-15 & 2015-16).The introduction of the amendment rules are part of the crackdown on shell companies. The new e-form INC 22A-ACTIVE introduced through the amendment rules will record the address of the registered office along with a photo of the registered office with the latitude and longitude of the place where registered office is situated. Basically the e-form enables geo-tagging, i.e attaching data of the exact location of the office, it will allow the online return filing system to alert government officials wherever it detects that far too many companies are registered in the same premises, a trend noticed in past investigations into shell companies.(Active Company Tagging Identities and Verification) (PHOTO/LOCATION VERIFICATION)The detailed article discusses changes brought in through the amendment rules by the MCA.Analysis of the Amendment RulesThe analysis of the amendments brought in by the amendment rules has been reproduced here under:I. Applicability:The rules shall come into force from 25 February 2019II. Active Company Tagging Identities and Verification (ACTIVE)III. Consequences of Non-filinga. If the company fails to file e-form INC 22A-ACTIVE within the prescribe period of time it shall be marked as "ACTlVE -non-compliant" on or after 26 April 2019 and shall be liable for action under sub-section (9) of section 12 of the Act.b. The registrar shall not accept the following forms filed by the company, unless the default is made good:SH-07 (change in authorized capital)PAS-03 (change in paid-up capital)DIR-12 (changes in director except cessation)INC-22 (change in registered office)INC-28 (amalgamation, de-merger)IV. What happens if the company files the e-form after the due date?Where a company files e-Form INC 22A-ACTIVE before 25 April 2019 the fee payable shall be NIL, and on or after 26 April 2019, the company shall be marked as “Active Compliant”, on payment of fees of ten thousand rupees.V. Exemptiona. The company which has not filed its due financial statements under section 137 or due annual returns under section 92 or both with the registrar of companies shall be restricted from filing e-form-ACTIVE, unless such company is under management dispute and the registrar has recorded the same on the register.Companies which have been struck off or are under the process of being struck off as recorded in the register.c. Companies under liquidation process or amalgamated or dissolved as recorded in the register.VI. Glimpse of the e-Form INC-22A ACTIVEThe e-Form INC 22A-ACTIVE will comprise the following mandatory details:Address of the registered office (photo of the registered office also showing at least one director(s)/ key management personnel (KMP) who has affixed his/her digital signature to this form is mandatory) with latitude and longitude of the place where the registered office is situatedOne time password (OTP) for verification will be sent on companies’ registered e-mail idThe director identification number (DINs) shall be in approved condition and it shall not be invalid on ground of non-filing of form DIR-3 KYC nor disqualified u/s 164(2).Details of KMPs of the companyService Request Number (SRN) of e-form AOC-4/AOC-4 XBRL and MGT-7 filed for FY17-18.Mandatory attachment:o Photograph of registered office showing external building and inside building also, showing at least one director/KMP who has affixed his/her DSC to this form.ConclusionThe e-Form INC 22A-ACTIVE will record details pertaining to the address of the registered office which would comprise a photo of the registered office along with latitude and longitude. This will help to locate whether or not such a place exists, to avoid the use of bogus address by shell companies. The government expects that its efforts to clean up the registry will create a transparent and compliant corporate ecosystem in India, promote the cause of ‘ease of doing business’ and enhance the trust of the public. This move of MCA will act as an early warning system to detect mushrooming of shell companies.If any company is facing any problem with compliance, contact us on below number or visit our website.Virtual Office Spaces, Virtual Offices for GST Registration | InstaSpacesFor more information Contact us 24/7 — +91 8882702020INSTASPACES.
-
How are cracked versions of software created and why are developers not able to prevent it?
Cracked versions of software are created with the use of debuggers. (A debugger is a special type of software that lets programmers deconstruct their software into its constituent parts for the purpose of finding bugs, and thus de-bugging. Additionally debuggers can be used for reverse-engineering, or to see what is inside the software, to learn its logic. The latter method is used mostly by malware researchers to study what malware (or computer viruses) do on-the-inside. But it can be also used by an attacker to "crack" (or bypass) legal software registration, or at times, to alter normal behavior of software, for instance by injecting a malicious code into it.)For the sake of this example, I will assume that the software that is being "cracked" was compiled into a native code, and is not a .NET or a JavaScript based application. (Otherwise it will be somewhat trivial to view its source code.) The compiled native code is a bit more tricky "beast" to study. (Native means that the code executes directly by the CPU, GPU, or other hardware.)So let's assume that the goal of an attacker is to bypass the registration logic in the software so that he or she doesn't have to pay for it. (Later for lolz, he or she may also post such "crack" on some shady online forum or on a torrent site so that others can "use" it too and give him or her their appreciation.)For simplicity let's assume that the original logic that was checking for the software registration was written in C++ and was something similar to the following code snippet:In this code sample "RegistrationName" and "RegistrationCode" are special strings of text that a legitimate software user will receive after paying for the license. (The name is usually that person's actual name or their email address, and the code is some string of unique/special characters that is tied to the name.)In the logic above, the function named "isRegistrationCodeGood()" will check if "RegistrationName" and "RegistrationCode" are accepted using some proprietary method. If they are, it will return true. Otherwise false. That outcode will dictate which branch (or scope) the execution will follow.So the logic above will either show that registration failed and quit:Or, if the registration code and name matched, it will save the registration details in persistent storage (such as the File System or System Registry) using the function named "rememberRegistrationParameters()" and then display the message thanking the user for registering:A "cracker" will obviously want to achieve the second result for any registration code that he or she enters. But they have a problem. They do not have the C++ source code, part of which I showed above. (I hope not!)So the only recourse for an attacker is to disassemble the binary code (that always ships with software in the form of .exe and .dll files on Windows, and mostly as Unix executables inside the .app packages on a Mac.) An attacker will then use a debugger to study the binary code and try to locate the registration logic that I singled out above.Next you can see the flowchart for a snippet of code that I showed in C++, presented via a low-level debugger. Or, as the code will be read in the binary form after compilation:(For readability I added comments on the right with the names of functions and variables. They will not be present in the code that an attacker could see.)(To understand what is shown above an attacker will have to have good knowledge of the Assembly language instructions for the native code.)I also need to point out that having a disassembly snippet like the one above is the final result for an attacker. The main difficulty for him or her is to locate it among millions and millions of other similar lines of code. And that is their main challenge. Not many people can do it and that is why software "cracking" is a special skill.So having found the code snippet above in the software binary file a "cracker" has two choices:1) Modify (or patch) the binary.2) Reverse-engineer the "isRegistrationCodeGood()" function and copy its logic to create what is known as a "KeyGen" or "Key Generator."Let's review both:The first choice is quite straightforward. Since an attacker got this far, he or she knows the Intel x64 Instruction Set quite well. So they simply change the conditional jump from "jnz short loc_7FF645671430" at the address 00007FF645671418 (circled in red in the screenshots) to unconditional jump, or "jmp short loc_7FF645671430". This will effectively remove any failed registration code entries and anything that the user types in will be accepted as a valid registration.Also note that this modification can be achieved by changing just one byte in the binary code from 0x75 to 0xEB:But this approach comes with a "price" of modifying the original binary file. For that an attacker needs to write his own "patcher" (or a small executable that will apply the modification that I described above.) The downside of this approach for an attacker is that patching an original executable file will break its digital signature, which may alert the end-user or the vendor. Additionally the "patcher" executable made by an attacker can be easily flagged and blocked by the end-user's antivirus software, or lead criminal investigators to the identity of the attacker.The second choice is a little bit more tricky. An attacker will have to study "isRegistrationCodeGood()" function and copy it into his own small program that will effectively duplicate the logic implemented in the original software and let him generate the registration code from any name, thus giving any unscrupulous user of that software an ability to register it without making a payment.Vendors of many major software products understand the potential impact of the second method and try to prevent it by requiring what is known as "authentication." This is basically a second step after registration, where the software submits registration name to the company's web server that returns a response back to the software of whether the code was legitimate or not. This is done by Microsoft when you purchase Windows (they call it "Activate Windows") and also by signNow, and many other companies. This second step may be done behind-the-scenes on the background while the software is running, and will usually lead to cancellation of prior registration if it was obtained illegally.So now you know how software is "cracked".Let me answer why it is not possible to prevent it. It all boils down to the fact that any software code needs to be read either by CPU (in case of a binary native code) or by an interpreter or a JIT compiler (in case of JavaScript or .NET code.) This means that if there's a way to read/interpret something, no matter how complex or convoluted it is, an attacker with enough knowledge and persistence will be able to read it as well, and thus break it.There is an argument though that cloud-based software is more secure, which is true, since its (binary) code remains on the server and end-users do not have direct access to it. And even though cloud-based software is definitely the future, it has some major drawbacks that will never allow it to fully replace your conventional software. To name just a few:Not everyone has an internet connection, or is willing to upload their data online. Additionally someone’s internet connection can be very expensive or too slow to make the software run very laggy.Then there’s a question of distributed computing. For instance, Blizzard Entertainment would never make “World of Warcraft” to fully run on their servers due to immense computational resources needed to render every single scene for every player they have. Thus it is in their best interest to let each individual user’s computer to do the rendering instead.As a software developer myself, I obviously don't like when people steal software licenses. But I have to accept it and live with it. The good news is that there are not that many people who are willing to go extra mile and search for a cracked version of software. The main problem for those who do, is that by downloading a patched executable, or an attacker's KeyGen or a Patcher, they are effectively "trusting" him or her not to put anything "nasty" into it that was not "advertised on the package" (stuff like trojans, malware, or keyloggers.) So the question for those people becomes -- is it worth the cost of the software license to potentially infect your system with a nasty virus?On the other side of the equation, some developers react very negatively to any attempts to steal their software licenses. (I was there too.) They try to implement all kinds of countermeasures -- anything from tricking reverse-engineers, to adding booby traps in the code that may do something nasty if the code detects that it is being debugged, to obfuscating or scrambling the code, to enforcing all kinds of convoluted DRM schemes, to blocking users from certain countries. I personally try to stay away from all of those measures. And here's why:A) Any kind of anti-reverse-engineering tactics could be bypassed by an attacker with enough persistence. So why bother and waste my time when I can invest that time into adding something useful to my software that will make it more productive for legitimate users?B) Some code packers could create false positives with antivirus software, which is obviously not good for marketing of that software. It also creates unnecessary complexity for the developer to debug the software.C) Adding booby traps in the code can also “misfire” on your legitimate users, which will really infuriate them and can even lead to lawsuits.D) Any DRM scheme will probably catch some 100 illegal users and greatly inconvenience 10,000 legitimate ones. So why do it to your good customers?E) Our statistics show that about 75% of all illegal licenses come from China, Russia, Brazil, to name the worst offenders. (I also understand that the reason may be much lower incomes that people have in those countries.) The main issue for us though was the fact that if we enforce our DRM or add some strong registration authentication, many people that wanted to bypass our registration would simply use a stolen credit card number. And we had no control over it. Our system will use it to send them a legitimate license only to have the payment bounce in weeks time. As a result we would lose the money that were paid for the license, plus the credit card company will impose an additional chargeback fee to our account, which may range from $0.25 to $20 per bad purchase on top of the license cost.F) As was pointed out in the comments, some companies may actually benefit from allowing pirated copies of their software. Microsoft for instance gets a lot of free publicity from people using their Windows OS, the same goes for signNow with their Photoshop. That is a good point that I agree with.So my philosophy is now this -- if someone wants to go extra mile and steal our software, go for it! They went this far to do it anyway, so they probably have a good reason. On the positive side there are so many other customers that appreciate the work that goes into creating software that greatly outnumber those that don’t.PS. Thank you for all your feedback! It makes me feel good that the knowledge I shared is useful to others.
-
Can a virtual office address help in fulfilling compliance of office photos for MCA Active Company tagging form/MCA 22-A form?
Hi,The MCA (Ministry of Corporate Affairs) has been working on various steps to identify businesses which are registered under the Companies Act but are not doing any business. Action taken by the authorities to delete the names of thousands of such Companies from the register records for not carrying out any business activities, which also resulted in their directors disqualification. The present move of Active Tagging Of Companies with Geo-tagging are all aimed at tracking the shell (fraud) companies and cracking them down thereby tightening the system.Virtual Office Spaces, Virtual Offic...
-
What are some things that should be considered when designing a programming language?
There are plenty of practicals of programming language design (I think Adrian Ho’s answer is great in talking about this), but, to me, the most important thing to consider is that, eventually, your programming language will have to be used by people.Most (if not all) programming languages ignore this, and they come up with these beautiful mathematical foundations… and then people just ignore them and use it in ways the designers did not predict because the costs using it “the right way” are way too damn high (in a huge part because they never ran any usability study with actual humans).I’ll go through a couple of examples of this.Consider Java. When designing the language they thought that it would be great for reasoning about programs if the possible exceptions every operation could raise was expressed directly in the signature (known as “checked exceptions”). They were right about that. Exceptions bubble up all the way through your dynamic call stack, so you can’t know what to expect by just reading the operation’s source code. And you need to know the ways in which your program can fail if you want to build software that is resistant to errors.So checked exceptions are a great idea. They’re solving a real problem people have. The mathematical model for it is pretty solid. Yet a ton of Java programmers are extremely dissatisfied with them. To the point most other languages would never consider this feature even though it’s a good feature.The problem in Java is that they did not run usability studies. They did not think about things like “if we have a huge codebase, and this code is used by thousands of other projects, and I add this exception to this one operation, what happens?” What happens is that everyone’s code breaks, which is an unacceptable cost for any software. It may take months to years of work from people you don’t even know to get each piece of software to work again. So, instead of relying on this great feature for reasoning, people choose to take the costs of poor static reasoning by using less fine-grained exceptions, relying more on unchecked exceptions, etc.Note that this doesn’t mean that checked exceptions are bad. THEY’RE GREAT. They’re an amazing feature for static reasoning, and every programming language out there should support this task (static reasoning). The problem with Java’s implementation is in the costs for actual humans using the language. It’s in how humans write software collaboratively. In how software codebases evolve over time. In how we don’t really control every single piece of code we use. These costs were not considered when people decided to implement checked exceptions in Java the way they did.Now let’s consider another programming language with this very same feature: Frank[1] . Frank is a language where not only the exceptions are checked. EVERY EFFECT IS. If a function mutates a variable, its signature will have to say that it mutates a variable. If it sends a request over the network, its signature will have to say that. From just looking at the signature in Frank you know not only how an operation may fail, but all of the things that it or the functions it calls may do.You’d think that this would be a disaster. After all, if you add a simple piece of code to log some information, you’ll effectively change the signatures of all operations that call that function through any amount of indirection. If you change F, which is called by G, which is called by H, which is called by Main, then all of these functions would break.Yet, things work perfectly in Frank. It has none of the problems Java has. If you add new things to an operation that has a thousand of callers, none of those callers need any changes. But your IDE will now show all of the additional things all those thousand functions can do/how they can fail. If you remove things from an operation, only the callers that depended on those things will need changes—and this is good, because they’d break at runtime anyway.Frank allows this through the amazing power of type inference. The compiler does all of this work for you, and you get all of the benefits. Everyone’s happy, because the costs of maintaining and evolving software are now much lower. People feel like they can use the features, and it won’t end up just being a burden in the future.Now let’s talk about where Frank goes wrong. Indeed being able to get the benefits of static reasoning without paying a huge price for it is great. But in real code bases there’s usually a lot of code that never gets ran. You add a lot of dependencies, and you might use 5% of their functions, but if any of the 95% you don’t use have a problem your code won’t compile. You won’t be able to ship, even though the problematic code will never get executed—it would have never been a problem!Sadly, all static programming languages have this problem. They require that all of the code you’ve included is consistent according to the type system rules, even if you don’t use most of it. That’s not only an unreasonable cost to pay, but it’s not even a predictable cost. How would you know that this obscure function in a library you’ve only included for one of its data structures has a type error? You don’t even care, for Christ’s sake.Now, again, type checking is a good feature. And I think a lot more people agree with this one than with checked exceptions. After all, type systems prevent a lot of problems that would be much more costly if we left them to be found in production. But, still, why do we have to pay for things that we don’t even care about or use? We don’t buy the entire supermarket when doing grocery shopping.Some people realised this, and they’ve worked on a gradual typing theory. This means that your type system allows your program to be only partially correct—if the pieces you use are correct, that’s really all that matters, you should be able to run or ship it. But you don’t really have to give up all of those other benefits for this, like you would in a dynamically typed language. You can still have your cake and eat it. Hazel[2] is an example of this.This happens a lot with security too, so let’s talk about that. JavaScript introduced a construct called Template Literals[3] . The idea comes from Quasi-Literals[4] in E, which in turn comes from Quasi-Quotation in Lisps. And it’s a brilliant idea—and as you may have been expecting by now, poorly executed.See, we have a lot of security issues in software that comes from people not using structured data formats[5] . SQL injections happen because people are putting strings together to form SQL queries. Shell injections happen because people are putting strings together to form Shell commands. HTML injections (XSS) happen because people are putting strings together to form HTML pages.This makes it seem that strings are evil, but the problem here is not strings per se. If you look at what people are doing in the places that have these security vulnerabilities there are two common themes:They want to build complex components from simpler parts. The usual case with templating in HTML involves things like “include this header here”, for example. In SQL it could be “include this filter in the WHERE clause, but only if that condition is fulfilled.”They want to include information that they don’t control in the components. For example, the text the user sent in a search input could be included in a WHERE clause to find things containing it.Both of these are very valid use cases, so it’s not like people are just creating security vulnerabilities for the fun of it. Both of these cases still happen with experienced programmers, and they’re equally ridden with security vulnerabilities, so it’s not a problem with experience either. These two cases also happen in all programming languages, so it’s not like some programming language is forcing these on people either—people want to do this.Interestingly, even though people’re doing this same thing in Lisp dialects, the vulnerabilities seem to happen less frequently. Conversely, it happens very frequently in PHP. We do need to keep in mind PHP is very popular, while Lisp dialects are not. The Lisp community can’t represent the PHP community, nor the programming community at large. But it’s still interesting; after all, people are writing systems that use databases in both languages.One difference between Lisp dialects and PHP is that Lisp dialects tend to represent everything with structured data (S-expressions-based). While using S-expressions, combining data always preserves the composition rules.For example, if you have “(select table (where (gt 'id x)))”, it doesn’t matter what the variables “table” and “x” contain, they won’t be able to arbitrarily change your query. You can’t just make “table = ‘* FROM user; DROP TABLE user’” and hope that it’ll work. The likelihood is low because only one person has to get the query implementation right—the person who implements the SQL library. The people creating queries (and thus dealing with the two “wants” above) don’t have to care. They just can’t possibly get it wrong. And the cost of using it is really low, so there’s no reason to look for alternative ways of achieving the same thing.In PHP your database library expects a String, and it’s very usual to find people building strings like: “SELECT * FROM “ . $table . “ WHERE id > “ . $x. The attack above now works, because you have to guarantee that your textual composition is correct every time you do it. The people who implemented the SQL library can’t help you.The costs keep growing because every composition, every context, requires special attention. People aren’t good with things that require a lot of attention all the time. They might get it wrong when they’re trying to fix a production bug at 00:00 because something else broke and they have to bring the system back really quickly. They might get it wrong because they didn’t get enough sleep last night. Or because they had a fight with their spouse. Or because their grandfather passed away. There’ll always be something that affects people’s attention, and we can’t rely on it for security. So, the cost can’t be there.And this is why template strings are such a great idea. They give people exactly what they’re familiar with when using strings—you can keep writing your SQL queries like you used to, mostly. But at the same time gives us the same properties Lisp libraries have when using structured data. We don’t have to care about composition rules anymore. When we write something like:sql`SELECT * FROM $table WHERE id > $x` We only have to rely on the person who wrote the “sql” function getting it right. Only one person has to get it right. And they don’t have to implement that under stress or emotional pressure or whatever!Yet, it doesn’t work in JavaScript. And it doesn’t happen for three simple reasons:JavaScript has a string interpolation syntax. You can write `SELECT * FROM $table WHERE id > $x`. This has the same semantics as the PHP example, which means it’s every bit as problematic for humans. But it’s also more straightforward to write than the tagged version, which is safer. The cost of writing secure code is higher than writing potentially vulnerable one.There’s no “sql” function in the standard library. I think they did consider adding common implementations of these in the standard library, but they never did. Rolling your own parser is a lot of work. Not everyone has learned how to write parsers and compilers. And a lot of people’d approach it with things like Yacc or Bison. While things like Miller’s Quasi Parser Generator would reduce this cost, it’s still a unlikely that people will choose to write a parser for SQL instead of just concatenating strings and hoping for the best.All database libraries in JavaScript accept strings for the query, instead of structured data, so using strings is much cheaper for the developer.As a result, the tagged variant of String Templates in JavaScript is hardly ever used by programmers. It doesn’t feel like it’s solving a problem (even though it is). It is very cumbersome to use, compared to just naive concatenation with untagged templates. And all libraries already encourage using strings anyway.I could go on, but this is already too long, and you get the idea :’)So, to summarise:Think about how humans will use your programming language.Think about what it means to use your features in terms of costs for humans, not just for computers. Thinking about execution performance and memory is great, but think about the human cost as well.Footnotes[1] Do be do be do[2] Hazel, a live functional programming environment featuring typed holes.[3] Template literals (Template strings)[4] QuasiLiterals[5] The Importance Of Being Typed
-
What is public key in network security?
A public key is created in public key encryption cryptography that uses asymmetric-key encryption algorithms. Public keys are used to convert a message into an unreadable format. Decryption is carried out using a different, but matching, private key. Public and private keys are paired to enable secure communication.A public key may be placed in an open access directory for decryption of the digital signature of the sender, the public key of the message recipient encrypts the sender’s message. Public key infrastructure (PKI) produces public and private keys.The open access public key may also be e-mailed to trusted contacts and users. Pretty Good Privacy (PGP) is a popular form of public key cryptography. Public PGP keys are housed in a public key server directory to allow public key sharing. PGP server directory keys may be updated but not removed.
Trusted esignature solution— what our customers are saying
Get legally-binding signatures now!
Frequently asked questions
How do i add an electronic signature to a word document?
How to make a pdf editable for esign?
How do i get the electronic signature for certified mail?
Get more for Remove eSignature Form Secure
- Help Me With Electronic signature North Dakota Plumbing Presentation
- How Can I Electronic signature North Dakota Plumbing Presentation
- Can I Electronic signature North Dakota Plumbing Presentation
- How To Electronic signature North Dakota Plumbing Presentation
- How Do I Electronic signature North Dakota Plumbing Presentation
- How To Electronic signature North Dakota Plumbing Presentation
- How Do I Electronic signature North Dakota Plumbing Presentation
- Help Me With Electronic signature North Dakota Plumbing Presentation
Find out other Remove eSignature Form Secure
- Gospel treason study guide form
- A is for alice who met an alligator form
- Rift valley university logo form
- Ac3253 s form
- Home warranty waiver form
- Pain diary worksheet form
- Laysan albatross virtual bolus dissection answer key form
- Cor 18 3 form
- Macroeconomics olivier blanchard 6th edition solutions pdf form
- Houghton mifflin english grade 4 pdf form
- Indemnity bond form
- Playa bonita rv park form
- Praveen ragi telugu book pdf form
- Student emis registration form
- Forney compression machine manual form
- National auto care cancellation form
- Asset hand over form
- Va form 26 1859
- Bupa international claim form pdf
- Aesap form