Validate eSignature Presentation Later
Make the most out of your eSignature workflows with airSlate SignNow
Extensive suite of eSignature tools
Robust integration and API capabilities
Advanced security and compliance
Various collaboration tools
Enjoyable and stress-free signing experience
Extensive support
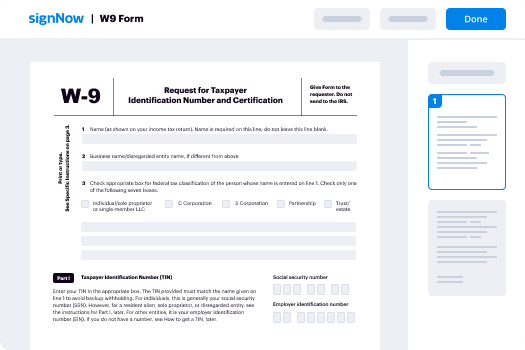
How Do I Implement eSignature in CMS
Keep your eSignature workflows on track
Our user reviews speak for themselves






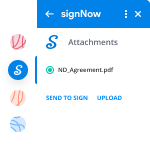
Validate eSignature Presentation Later. Investigate probably the most consumer-helpful knowledge about airSlate SignNow. Handle your complete papers digesting and expressing system electronically. Go from portable, papers-structured and erroneous workflows to computerized, digital and flawless. It is simple to produce, deliver and indication any paperwork on any device anywhere. Be sure that your crucial business cases don't fall over the top.
Find out how to Validate eSignature Presentation Later. Adhere to the straightforward guideline to get going:
- Make your airSlate SignNow accounts in clicks or log in along with your Facebook or Google profile.
- Take advantage of the 30-day time trial offer or go with a prices strategy that's great for you.
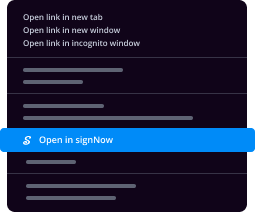
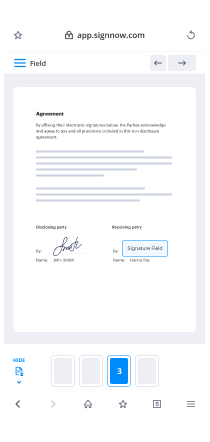
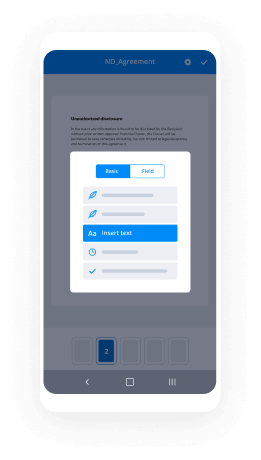
- Discover any lawful template, create on the web fillable types and talk about them safely.
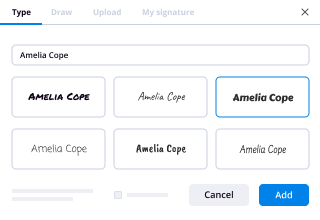
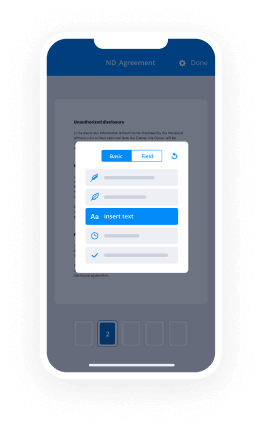
- Use advanced characteristics to Validate eSignature Presentation Later.
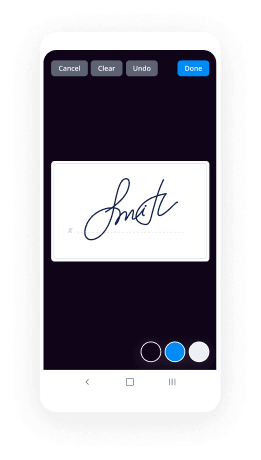
- Sign, personalize signing get and acquire in-person signatures 10 times more quickly.
- Set up auto alerts and receive notifications at each stage.
Shifting your duties into airSlate SignNow is simple. What practices is a straightforward method to Validate eSignature Presentation Later, as well as suggestions to help keep your peers and lovers for greater collaboration. Inspire your staff using the very best instruments to stay on top of business processes. Increase productiveness and scale your organization faster.
How it works
Rate your experience
-
Best ROI. Our customers achieve an average 7x ROI within the first six months.
-
Scales with your use cases. From SMBs to mid-market, airSlate SignNow delivers results for businesses of all sizes.
-
Intuitive UI and API. Sign and send documents from your apps in minutes.
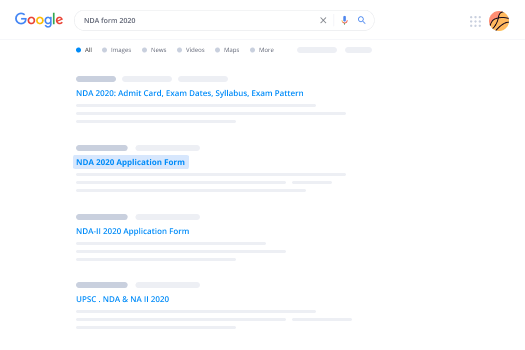
A smarter way to work: —how to industry sign banking integrate
FAQs
-
How are cracked versions of software created and why are developers not able to prevent it?
Cracked versions of software are created with the use of debuggers. (A debugger is a special type of software that lets programmers deconstruct their software into its constituent parts for the purpose of finding bugs, and thus de-bugging. Additionally debuggers can be used for reverse-engineering, or to see what is inside the software, to learn its logic. The latter method is used mostly by malware researchers to study what malware (or computer viruses) do on-the-inside. But it can be also used by an attacker to "crack" (or bypass) legal software registration, or at times, to alter normal behavior of software, for instance by injecting a malicious code into it.)For the sake of this example, I will assume that the software that is being "cracked" was compiled into a native code, and is not a .NET or a JavaScript based application. (Otherwise it will be somewhat trivial to view its source code.) The compiled native code is a bit more tricky "beast" to study. (Native means that the code executes directly by the CPU, GPU, or other hardware.)So let's assume that the goal of an attacker is to bypass the registration logic in the software so that he or she doesn't have to pay for it. (Later for lolz, he or she may also post such "crack" on some shady online forum or on a torrent site so that others can "use" it too and give him or her their appreciation.)For simplicity let's assume that the original logic that was checking for the software registration was written in C++ and was something similar to the following code snippet:In this code sample "RegistrationName" and "RegistrationCode" are special strings of text that a legitimate software user will receive after paying for the license. (The name is usually that person's actual name or their email address, and the code is some string of unique/special characters that is tied to the name.)In the logic above, the function named "isRegistrationCodeGood()" will check if "RegistrationName" and "RegistrationCode" are accepted using some proprietary method. If they are, it will return true. Otherwise false. That outcode will dictate which branch (or scope) the execution will follow.So the logic above will either show that registration failed and quit:Or, if the registration code and name matched, it will save the registration details in persistent storage (such as the File System or System Registry) using the function named "rememberRegistrationParameters()" and then display the message thanking the user for registering:A "cracker" will obviously want to achieve the second result for any registration code that he or she enters. But they have a problem. They do not have the C++ source code, part of which I showed above. (I hope not!)So the only recourse for an attacker is to disassemble the binary code (that always ships with software in the form of .exe and .dll files on Windows, and mostly as Unix executables inside the .app packages on a Mac.) An attacker will then use a debugger to study the binary code and try to locate the registration logic that I singled out above.Next you can see the flowchart for a snippet of code that I showed in C++, presented via a low-level debugger. Or, as the code will be read in the binary form after compilation:(For readability I added comments on the right with the names of functions and variables. They will not be present in the code that an attacker could see.)(To understand what is shown above an attacker will have to have good knowledge of the Assembly language instructions for the native code.)I also need to point out that having a disassembly snippet like the one above is the final result for an attacker. The main difficulty for him or her is to locate it among millions and millions of other similar lines of code. And that is their main challenge. Not many people can do it and that is why software "cracking" is a special skill.So having found the code snippet above in the software binary file a "cracker" has two choices:1) Modify (or patch) the binary.2) Reverse-engineer the "isRegistrationCodeGood()" function and copy its logic to create what is known as a "KeyGen" or "Key Generator."Let's review both:The first choice is quite straightforward. Since an attacker got this far, he or she knows the Intel x64 Instruction Set quite well. So they simply change the conditional jump from "jnz short loc_7FF645671430" at the address 00007FF645671418 (circled in red in the screenshots) to unconditional jump, or "jmp short loc_7FF645671430". This will effectively remove any failed registration code entries and anything that the user types in will be accepted as a valid registration.Also note that this modification can be achieved by changing just one byte in the binary code from 0x75 to 0xEB:But this approach comes with a "price" of modifying the original binary file. For that an attacker needs to write his own "patcher" (or a small executable that will apply the modification that I described above.) The downside of this approach for an attacker is that patching an original executable file will break its digital signature, which may alert the end-user or the vendor. Additionally the "patcher" executable made by an attacker can be easily flagged and blocked by the end-user's antivirus software, or lead criminal investigators to the identity of the attacker.The second choice is a little bit more tricky. An attacker will have to study "isRegistrationCodeGood()" function and copy it into his own small program that will effectively duplicate the logic implemented in the original software and let him generate the registration code from any name, thus giving any unscrupulous user of that software an ability to register it without making a payment.Vendors of many major software products understand the potential impact of the second method and try to prevent it by requiring what is known as "authentication." This is basically a second step after registration, where the software submits registration name to the company's web server that returns a response back to the software of whether the code was legitimate or not. This is done by Microsoft when you purchase Windows (they call it "Activate Windows") and also by signNow, and many other companies. This second step may be done behind-the-scenes on the background while the software is running, and will usually lead to cancellation of prior registration if it was obtained illegally.So now you know how software is "cracked".Let me answer why it is not possible to prevent it. It all boils down to the fact that any software code needs to be read either by CPU (in case of a binary native code) or by an interpreter or a JIT compiler (in case of JavaScript or .NET code.) This means that if there's a way to read/interpret something, no matter how complex or convoluted it is, an attacker with enough knowledge and persistence will be able to read it as well, and thus break it.There is an argument though that cloud-based software is more secure, which is true, since its (binary) code remains on the server and end-users do not have direct access to it. And even though cloud-based software is definitely the future, it has some major drawbacks that will never allow it to fully replace your conventional software. To name just a few:Not everyone has an internet connection, or is willing to upload their data online. Additionally someone’s internet connection can be very expensive or too slow to make the software run very laggy.Then there’s a question of distributed computing. For instance, Blizzard Entertainment would never make “World of Warcraft” to fully run on their servers due to immense computational resources needed to render every single scene for every player they have. Thus it is in their best interest to let each individual user’s computer to do the rendering instead.As a software developer myself, I obviously don't like when people steal software licenses. But I have to accept it and live with it. The good news is that there are not that many people who are willing to go extra mile and search for a cracked version of software. The main problem for those who do, is that by downloading a patched executable, or an attacker's KeyGen or a Patcher, they are effectively "trusting" him or her not to put anything "nasty" into it that was not "advertised on the package" (stuff like trojans, malware, or keyloggers.) So the question for those people becomes -- is it worth the cost of the software license to potentially infect your system with a nasty virus?On the other side of the equation, some developers react very negatively to any attempts to steal their software licenses. (I was there too.) They try to implement all kinds of countermeasures -- anything from tricking reverse-engineers, to adding booby traps in the code that may do something nasty if the code detects that it is being debugged, to obfuscating or scrambling the code, to enforcing all kinds of convoluted DRM schemes, to blocking users from certain countries. I personally try to stay away from all of those measures. And here's why:A) Any kind of anti-reverse-engineering tactics could be bypassed by an attacker with enough persistence. So why bother and waste my time when I can invest that time into adding something useful to my software that will make it more productive for legitimate users?B) Some code packers could create false positives with antivirus software, which is obviously not good for marketing of that software. It also creates unnecessary complexity for the developer to debug the software.C) Adding booby traps in the code can also “misfire” on your legitimate users, which will really infuriate them and can even lead to lawsuits.D) Any DRM scheme will probably catch some 100 illegal users and greatly inconvenience 10,000 legitimate ones. So why do it to your good customers?E) Our statistics show that about 75% of all illegal licenses come from China, Russia, Brazil, to name the worst offenders. (I also understand that the reason may be much lower incomes that people have in those countries.) The main issue for us though was the fact that if we enforce our DRM or add some strong registration authentication, many people that wanted to bypass our registration would simply use a stolen credit card number. And we had no control over it. Our system will use it to send them a legitimate license only to have the payment bounce in weeks time. As a result we would lose the money that were paid for the license, plus the credit card company will impose an additional chargeback fee to our account, which may range from $0.25 to $20 per bad purchase on top of the license cost.F) As was pointed out in the comments, some companies may actually benefit from allowing pirated copies of their software. Microsoft for instance gets a lot of free publicity from people using their Windows OS, the same goes for signNow with their Photoshop. That is a good point that I agree with.So my philosophy is now this -- if someone wants to go extra mile and steal our software, go for it! They went this far to do it anyway, so they probably have a good reason. On the positive side there are so many other customers that appreciate the work that goes into creating software that greatly outnumber those that don’t.PS. Thank you for all your feedback! It makes me feel good that the knowledge I shared is useful to others.
-
Sadness again descended where a hero (Lt Col Niranjan) sacrificed his life for nation at Pathankot. Where are those voices now?
I belong to the armed forces fraternity, by virtue of which I get to hear directly from the men most affected by such incidents.I wouldn't want to add much myself, but I have a couple of forwarded messages which I believe really need to be shared. There are some pressing issues within the Armed Forces family, but since they have been raised to never question authority, they continue to suffer silently.Just give the following text some thought, they raise very valid questions and I wish the media and our general public paid attention to such details :"Touching message posted by a course mate of Lt.col Niranjan, who died while diffusing a bomb at Pathankot... R.I.P Lt Col Niranjan EK. My Coursemate, my Sutta Pal, Barrack-Type and Punishment-Type. Wish I could turn back the clock for you, Moron! I would have ensured that instead of CDSE you would have cleared your Civil Services Exam. Your daughter would have had a father to watch her grow up. Your wife would have had a husband to grow old with. And you would never had had to fight to get a decent pension (Not that you would have needed one - everyone knows the price of a Babu's signature). I wish that you had not been a warrior, a leader of men and a guardian of an ungrateful nation. I wish you had been a pen-pushing Babu who charged you just for doing his job. I wish that you had not been an Officer And A Gentleman earning a hardship allowance of Rs.32000 in Siachen. Instead you should have been a blood-sucking Babu earning Rs.72000 HARDSHIP ALLOWANCE for enjoying the salubrious climes of Shillong or Guwahati. Or I wish that you had been a Corporate Honcho, who earns thrice your salary for doing one-fourth of what you do. I wish that you had been an AAM AADMI for whom nothing matters beyond the next increment,the next mobile phone or the next vehicle that he is going to buy. I wish that you had been anything except what you chose to become - A Real Man, A Professional Soldier, A Leader Of Men, A True Son Of This Ungrateful Nation, Sworn to protect it at all cost. I Wish...I Wish... But You Are No Longer There.... So I can only pray that in your next life, you decide to do something worthwhile. Something... Anything.... Just Don't Repeat The Mistakes You Made In This One.. R.I.P Brother... We'll Meet In The Afterlife! "Another one which deserves some attention, it makes us question what the Police and other forces are doing while Army men die, they same army men who take up the job of the NDRF and others when Floods hit Kashmir or Tamil Nadu (to even rescuing kids stuck in borewells). :"Lt Col EK Niranjan of Engineers lost his life leaving a young wife & 18 months old daughter while combating terrorists in pathankot.he was seriously wounded in the action & later succumbed to the injurieswhy did he die ?for whom did he die ?the two big & unpleasant questionsit is the nexus of punjab police, politicians & drug syndicates which is ruling present punjaban suv of SP rank punjab police officer is highjacked while he himself was inside it & punjab police cannot locate the vehicle with blue beacon on it for next 24 hourswhen the SP himself reports to police within an hour of highjack & confirms it was indeed a militant activity, his report is brushed asidethe CM, Deputy CM & home minister are not aware till the militants actually attack the airforce basewhy?Because all three ie politicians, police & drug mafia are busy ferrying lethal drug consignments & counting money.An alert was issued after about 12 hours in the late evening of 01 january when the dead body of innova taxi driver was locatedCM, Deputy CM & home minister still remained silent.It is an eye opener for all of us in which direction the once prosperous state punjab is heading with the nexus of the trio.Lt Col E K Niranjan has made the supreme sacrifice while saving his brothers in airforce station at pathankot because his own countryman consisting of politicians, police & drug mafia of punjab have failed him, betrayed him & eventually murdered him.RIP brother, you could attain the selfless martyrdom for the selfish countrymen, we pray for you & your bereaved family. These terrorists came to the airbase using the SP pathankot's official car. The SP is alive. The driver is dead. All very convenient.That SP was accidentally moving around the place where the terrorists hijacked him with his car at mid night. He was thrown out of the car and the driver died. Very convincing.No one in the media is asking the right questions.What stops the media from saying what I said? Why not ask IG, gurdaspur? Why not ask DGP, Punjab? This question is not connected with the operations going on. In any case, army cannot answer this question. The question is, how did the SP escape? Why did he not fight the terrorists and die? Is his life more precious? What about his oath to the constitution of India? Why should the armed forces be the only guys to take their oath seriously and keep dying for the country? Are the IPS officers exempted from their own oath to protect India? These are serious questions which every citizen of India should be asking. Are armed forces supposed to die so that corrupt police officers can live?Genuine food for thought.. "PS: Above messages are as received via whatsapp. Similar concerns keep coming up in the armed forces often, and hence I decided to put then out in the open to the general public. I would not want to name those who sent these, since they still firmly respect their values as defence officers.
-
Why isn't the legal system willing to accept "I never received a notice," as a valid excuse? Why don't they simply mail the impo
When “I never received notice” isn’t a valid excuse, it is because too many people will, frankly, lie about this. People also make affirmative efforts to evade service. And sometimes people decide to just up and move without bothering to tell anyone. Shocking, I know.Thus, formal rules about service make it easy to determine whether service was done properly, and a party claiming lack of notice despite compliance with the rules will be required to prove the likelihood of actual lack of notice before the excuse will be even considered. On the other hand, if the party purportedly giving notice did not comply with the rules, the notice won’t be presumed to be valid without either an acknowledgment or waiver by the defendant.There are two different categories of notices—initial process and subsequent notice.For initial process, the court must obtain jurisdiction over the defendant. Traditionally this was done by personal service within the court’s territorial jurisdiction—the defendant needed to be “tagged.” This tagging was done by the sheriff (or a deputy), an agent of the court itself. If the defendant never showed up in the jurisdiction, the case could not proceed.¹More modern concepts of personal jurisdiction do not place as much emphasis on presence within the place; as any American law student will know, the case of International Shoe Co. v. State of Washington² established that personal jurisdiction could be asserted beyond a State’s boundaries if “minimum contacts” existed and “fair play” suggests that haling a foreign defendant to answer an in-state complaint would be reasonable.Of course, personal service by the state’s sheriff isn’t possible in such a case, and so most states do permit alternative forms of service as a matter of course (sometimes those alternative methods are available domestically as well). The exact requirements may vary by type of case and in any event will be spelled out in local rules of civil procedure; for proper advice you will want to consult a lawyer in the place where the action is. But generally, when initial process is involved, some form of service that leaves no doubt about the service, and the verification of some third party—the sheriff, the Post Office, a process server, &c—is required (the plaintiff in propria persona is not usually allowed to do initial personal service as they have as much motivation to lie about it as does the defendant). That might be personal service by a disinterested adult, another jurisdiction’s deputized sheriff, or service by certified mail.³ This means that someone is in a position to submit proof of the service to the court. (A defendant may also acknowledge service or waive⁴ any defects in service.)Now, for subsequent service, the rules tend to be a bit different. Once a party has been tagged and haled into court, they have a responsibility to themself and to the court to appear and present whatever defence they have to the action. Parties are, of course, entitled to notice of things that happen in the case—ex parte and sealed proceedings are extremely limited. But, at this point, because being party to a suit involves this responsibility, part of it is to keep the court and the other parties apprised of a proper address where notices may be served with a minimum of fuss (and to notify the court if that changes). Usually this is a mailing address and service is made by ordinary mail—which doesn’t require a signature and thus is less hassle for everyone—but in some cases service by e-mail, facsimile transmission, and the like may be agreed to (in the case of electronic case filing systems, e-mail service will likely be mandated as a condition of ECF use). Personal service is still permitted as a method of serving these subsequent papers, but not required. Again as to specific methods of service, you need to consult your local rules of procedure and the local attorney previously suggested.And so, a movant or the court will not be expected to make extraordinary efforts to provide “actual notice” of every single piece of paper by certified mail or personal service and give the defendant the opportunity to delay the case by evading service of motions. Neither will the court or other parties be required to chase a party around in the event of their moving and not leaving a forwarding address.⁵ Service to the “last known address” is almost universally sufficient. And the court won’t be impressed with “I didn’t get notices” when the lack of such notices is apparently the respondent’s own fault.N.B. This answer may be somewhat generalized for the United States; other legal régimes have their own ideas about notices.Notes:¹ A plaintiff unable to effect service could, of course, attempt to commence the action in another jurisdiction where the defendant could be found.² 326 U.S. 310 (1945). International Shoe is famous for the notion that an out-of-state defendant with “continuous and systematic contacts” to the state would nonetheless be susceptible to being sued there; the rule was further broadened by Burger King Corp. v. Rudzewicz, 471 U.S. 462 (1985), where even contacts that could not even be characterized as “minimum” with Florida were sufficient in the context of specifically making a comprehensive agreement to deal with a corporation legally resident in Florida.³ “Special service” or service not generally provided for by rule may be obtained by order of court only in the event that regular service cannot be obtained. Special service is usually publication. The purpose of special service is to allow the plaintiff to proceed with the action without having it stayed for an unreasonable period of time due to the absence of the defendant. The showing required for special service will vary by jurisdiction and possibly the facts of the case. And a defendant seeking to set aside a judgment obtained in this manner will have a much easier time of it than the defendant seeking to contest normal methods of service.⁴ As the primary purpose of service requirements is “notice to the defendant,” the mere fact that the defendant appears in the action suggests rather strongly that the defendant does in fact know about it. Consequently, a party seeking to challenge the validity of original service must do so at the outset and before making any substantive response to the complaint, otherwise the court will not hear such challenges and they will be deemed waived.⁵ We have this problem rather perennially in support court. I suspect it is a combination of general haplessness on the part of some of our obligors and deliberate efforts to evade our enforcement proceedings, but we get a lot of people who don’t show up at their contempt hearings because they “didn’t get notice.” The court issues bench warrants and most of the individuals are later arrested, and the failure of notice is not regarded as a defense by the court and in fact often leads to an additional contempt for failing to appear or to comply with the language in the support orders requiring parties to notify the court of address changes.
-
What are the career options after graduating with a Bachelor's in physics?
There are actually Three things you can do after you ‘earn’ your Bachelor degree in Physics :Continue your studiesGet a Job , orGive a JobAllow me to explain each in detail -Continue your studies :-> Here you have several Options:a) Pursue Masters from IIT by cracking IITJAM or from any other university on Physics and earn a PHd later on. You can also do Integrated PHd by applying and getting a good rank in JEST , TIFR , IISER etc.b) Pursue your Masters from any IIT (or from any other University) and then pursue MTech by cracking GATE. After MTech you can get placed in some PSUs or some reputed MNCs. Many prefer higher studies though (like PHd after Mtech). (P.S - IIT Kharagpur provides Integrated Mtech-PHd for Computer Science and Data Analytics after qualifying in GATE)c) Give an entrance test conducted by few universities for Btech and get into some good Engineering Colleges. (Ex : Jadavpur University in Kolkata conducts an entrance test for students of BSc(Hons) Physics. Qualified Candidates enter into 2nd year of BTech. Likewise Calcutta University provides Btech in Radiophysics.)d) Do Bachelors in Education(BEd) for a Teaching Job.e) MSc on other subjects like Biophysics, RadioPhysics, Geophysics, Instrumentation etc. Ex - MScTech in Geophysics from ISM Dhanbad (Note : the degree mention MScTech not MTech; Both are different).f) Other Masters programme in other disciplines if you want to do it like MCA, MBA, MA, LLB etc. (Being interested in Defence Services, personally I would have preferred Masters from Institute of Defence Studies in Pune and PHd later on— a path very few know or like to tread .)g) If you have a Gap in years after your BSc Physics and possess the thought that you will be unable to share the class with the younger generation, feel free to pursue distance learning through IGNOU. You can pursue your masters on other subjects via IGNOU or sit for an entrance examination for MSc. Physics (distance learning) which by the way IGNOU conducts in collaboration with Indian Institute of Astrophysics (forms available in the month of september).h) You can also pursue higher studies from Foreign universities. Of course you have to crack the competitive exams related for that purpose.2. Get a Job :→ You can Apply for Various entrance examinations for Banks(RBI Grade B, SBI PO, IBPS etc), Railways( ASM, Goods Guard, JE, RPF SI etc) , PSUs or State Units(AAI ATC, Electricity Executives, Forest Guard etc), Armed Forces(AFCAT, CDSE, Coast Guard(only interview) ), Civil Services(UPSC CSE, State CSE, IFoS) and Central/State Police Services( SSC CAPF, UPSC CAPF, SSC CGL etc). Crack these Examinations and earn a respectable service with the Central or State Governments or Banking Sector or PSUs.(PS : If you have completed MSc Physics then you can apply in Indian Navy as an Officer or else not. Indian Navy does not recruit candidates having just BSc in Physics. You either should have BTech or do MSc Physics- the condition valid even in UPSC CDSE recruitment)→ If you want a job in your core field(subject), there are exams like ISRO Scientific Assistant, SSC IMD Scientific Assistant, BHAVINI Scientific Assistant, NCPOR Scientific Assistant(which do not conduct any exam but only Personal Interview), NPCIL Scientific Assistant etc. which too are Govt Organisations that requires Bachelor’s in Physics as a qualification.(PS- If you complete MSc in Physics however you can apply for a relatively higher position in similar organisations for the post of Scientific Officer - Some institutes like BARC donot recruit candidates having a degree less than that of MSc.)You know the craze for Government Jobs, Don’t you? Some Jobs are indeed Earned. :)→ However You can always find a Job in the Corporate Sector. Ex: TCS, WIPRO etc.So, All the very Best if getting a Job is your sole Aim.P.S - Build and Develop Skills via sites(also Android App) like Udemy, Coursera, edX, Skillshare, Codecademy etc. Trust me sometimes recruiters will be much interested if they learn that you have invested some quality time in having knowledge which can give you an edge over other candidates. Also makes your Resume look quite attractive. Moreover guess what, most courses are totally free of Cost. After Completing the Course if you wish to have the valid Certificate with a signature and stamp from reputed universities, you can pay them a certain fee. Totally ok if you dont pay as those digital certificates will not hold much value over regular courses;but do keep in mind the skill you learn can make you top notch over others.Personally I prefer to pay as a token of appreciation. Doesn’t seem much(approx 3k INR & sometimes even only 600 INR) if you consider the fact that the knowledge you receive is immense and magnificent.3. Give a Job :→ Well you know what I am going to say. The Word that became the centre of attention lately in India- ‘Entrepreneurship’.Take risks, try out new ways, give people a source of Income, earn Fortunes and build your own Empire. And the thing is you don’t even need a Bsc or Physics to be a great entrepreneur. You don’t need to work for anyone, You can always work for yourself.But yes to be brutally honest- as lovely as the situation might seem- you will most likely Fail in this venture. Dont get me wrong but what I am saying here is the ‘Reality’. However I haven’t seen or met Entrepreneurs who didnot fail and yet achieved big.Who knows You might become the next Zuckerburg or the next Elon Musk - which by the way if you dont know, Mr. Musk has done his Bachelors in Physics. ;)These are the three things which I feel you can do. The Interest and the Will rests on you and you alone. I hope I was able to remove all your doubts. Still if you have one, feel free to comment.By the way, Upvotes are Welcome. Thank you for the 177 upvotes. Means a lot.All the Best for your future.(>_<) ♡Edit- Thank you Quorans for my first 500 upvotes.
-
How do I register a Pvt. Ltd. company?
Steps to Register Private Limited Company:-Step 1. Digital Signature Certificate(DSC) RequiredThe first and foremost step to start the registration process is to have directors & shareholders Digital Signature Certificate. Digital Signature are nothing but a USB drive(DSC token) which contains the encrypted digital signature of a person.It is same as a person is signing with a pen on a paper and with digital signature, a person can sign a document on Computer.Step 2. Directors Identification Number(DIN)Directors Identification Number(DIN) are mandatory for every person, who wishes to become a director in any company. PAN card is mandatory to have a DIN number. Director Identification Number is a unique code which has lifetime validity.Documents required for DIN ApplicationPAN CardAdhar CardElectricity BillPhone billMobile BillBank StatementNote: There can be Maximum 15 Directors in a Private Limited Company which can be received by giving Notice to ROCStep 3. Name ReservationAfter having DIN number. Name Reservation Application can be filed through Form INC-1 and Name will be reserved by the DIN numbers of the Directors. Following points should be considered while making the application for Name Reservation.The name should not be similar to any existing company or LLP name.The name should not be similar to any Registered Intellectual Property.In the event of winding-up of a company, the name of such entity will not be available for use for the next 2 years. However, if company winds up by the court order, then the name of such entity will not be available for use for the next 20 years.Step 4. Drafting of Memorandum of Association(MOA) and Article of Association(AOA)Memorandum of Association: It is the constitution of a company. It is a document, which among other things, defines the areas within which the company can act. It states the objects for which the company has been formed. Articles of Association: It contains the rules and regulations relating to the internal management of a company. It serves as a binding contract between the company and its members. Once the company name is approved by the ROC, the subsequent step is to draft the MoA and AoA. The subscribers need to determine their name, address, and occupation in their own particular handwriting and sign the subscription pages of MoA and AoA.Step 5. Certificate of IncorporationAfter the submission and completion of all the necessary documents, the registrar of the company shall retain and register the memorandum and articles. After the registration of the Memorandum of a company, the registrar shall signNow that the company is incorporated. The digitally signed "certificate of incorporation" then will be emailed to the directors.
Trusted esignature solution— what our customers are saying
Get legally-binding signatures now!
Related searches to Validate eSignature Presentation Later
Frequently asked questions
How do i add an electronic signature to a word document?
How to make a pdf editable for esign?
How do i sign into my e-mail account with my new password?
Get more for Validate eSignature Presentation Later
- Help Me With Electronic signature Rhode Island Plumbing Word
- How Can I Electronic signature Rhode Island Plumbing PDF
- Can I Electronic signature Rhode Island Plumbing Word
- Can I Electronic signature Rhode Island Plumbing PDF
- How To Electronic signature Rhode Island Plumbing PDF
- How Can I Electronic signature Rhode Island Plumbing Word
- How Do I Electronic signature Rhode Island Plumbing PDF
- Help Me With Electronic signature Rhode Island Plumbing PDF
Find out other Validate eSignature Presentation Later
- Texas warranty deed search form
- Gift deed texas form
- Condominium bylaws form
- Independent contractor agreement form
- Medicaid long term care application form
- Limited liability company 481371178 form
- Court ordered mediation texas form
- Acknowledgment paternity form
- Escrow form 481371181
- Mechanics lien form pdf
- Grandparent rights form
- Complaint builder form
- Breach contract form
- Llp form
- Encroachment form
- Quash writ form
- Storage agreement form
- Easement form
- Agreement sales form
- Testamentary trustee form